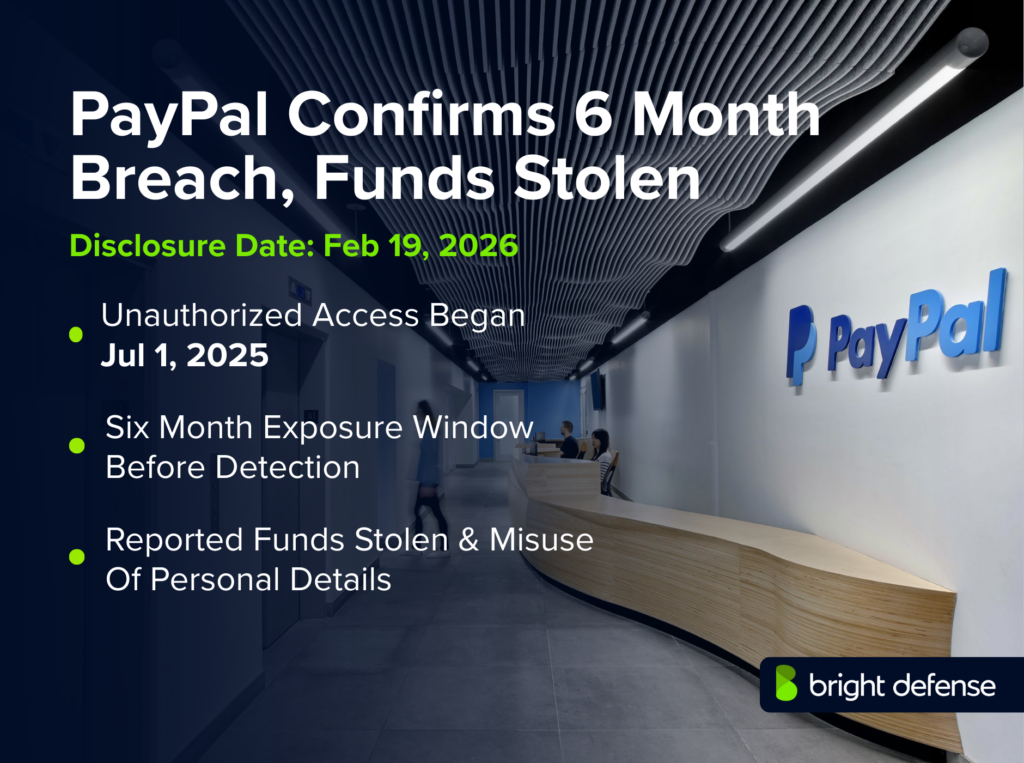
PayPal Breach Exposed Data for 6 Months, Funds Stolen
What Happened in the Breach
PayPal confirmed that a software error in its PayPal Working Capital (PPWC) loan application led to a data exposure that lasted nearly six months.
According to PayPal’s breach notice filed with Massachusetts authorities, the error in the PPWC application exposed personal data to unauthorized individuals between July 1 2025 and December 13 2025. PayPal detected the issue on December 12 2025 and rolled back the faulty code the next day.
The company emphasized that its core systems were not compromised and said only a small number of customers, around 100, were potentially affected.
Nevertheless, exposed data included names, email addresses, phone numbers, business addresses, Social Security numbers and dates of birth.
PayPal found that some victims experienced unauthorized transactions, prompting the firm to refund affected accounts and reset passwords. The breach underscores how a single coding error can expose sensitive data even when the underlying infrastructure is secure.
Timeline: From First Access To Latest Update
- July 1 2025: A change to the PPWC loan application inadvertently introduced a bug that exposed customer data. The exposure continued undetected for months.
- July 1 – December 13 2025: Personal information—names, contact details and Social Security numbers—remained accessible to unauthorized parties.
- December 12 2025: PayPal discovered unauthorized access during an internal investigation. It determined that the bug had been active for more than five months.
- December 13 2025: PayPal rolled back the problematic code, blocking further access to the exposed data.
- February 10 2026: The company sent breach-notification letters to affected customers. The letters explained what information was involved, described the remediation steps taken, and offered complimentary credit monitoring.
- February 20 2026: BleepingComputer reported on the incident, citing PayPal’s notifications and statements. On the same day The Register and other outlets confirmed that about 100 customers were notified.
- February 21 – 22 2026: Additional reports from TechRepublic, Cybernews and Techzine gave further details on the nature of the bug and the data exposed. PayPal reiterated that it had not delayed disclosure for law‑enforcement reasons and that the core system had not been breached.
- Latest confirmed update: As of February 22 2026, no regulators have announced investigations or fines related to the PPWC incident. PayPal continues to offer two years of free credit monitoring and identity‑restoration services to the affected users. No arrests or lawsuits have been reported.
What Data Or Systems Were Affected
The bug in the PPWC application exposed sensitive personally identifiable information (PII). PayPal’s breach notice states that the compromised data may have included each customer’s name, email address, phone number, business address, Social Security number and date of birth. Reports confirm that approximately 100 customers were affected, although the exact number has not been publicly disclosed.
The exposure did not involve PayPal’s main payment platform or other systems; the firm insists that the broader infrastructure remained secure. However, because the data set included unique identifiers such as Social Security numbers and dates of birth, the risk of identity theft and fraudulent account activity is significant. A few customers experienced unauthorized transactions, which PayPal refunded.
Who Was Responsible (Confirmed Vs Alleged)
PayPal attributes the incident to an internal coding error rather than an external hack. The company says a software modification in the PPWC loan application inadvertently exposed data to unauthorized individuals. There is no evidence that threat actors breached PayPal’s core systems; instead, the vulnerability allowed unknown individuals to access data that was unintentionally exposed.
Because the flaw resulted from a configuration error and not a deliberate intrusion, no specific attacker has been identified. Nevertheless, individuals who discovered the exposure were able to view and potentially misuse the data; some used it to carry out fraudulent transactions. Law‑enforcement agencies have not announced any arrests or identified suspects.
How The Attack Worked
The incident was rooted in business‑logic failure rather than a classic hack. PayPal’s PPWC platform serves small businesses seeking fast access to financing.
A code change introduced on July 1 2025 inadvertently made certain fields in the application interface publicly accessible.
This misconfiguration exposed PII to any party who interacted with the application, even though no authentication bypass or network intrusion occurred.
As soon as PayPal detected the error on December 12 2025, it reversed the faulty code and blocked further access the next day.
The error effectively left sensitive customer files “on a table in the public lobby,” as one analyst put it; unauthorized individuals could scrape the data because it was made visible by the flawed code.
There is no indication that passwords or cryptographic keys were compromised, but the presence of Social Security numbers and birthdates raises the potential for identity‑theft schemes.
Impact and Risks for Customers
Although the breach affected only around 100 customers, the exposed data included high‑value identifiers. Social Security numbers, dates of birth and full contact information can be used to commit identity theft, open fraudulent credit lines or launch targeted phishing attacks.
Cybersecurity experts interviewed by Cybernews warn that the longer attackers stay undetected, the greater the risk of credential exposure. Even with a limited victim pool, the sensitivity of the data raises the likelihood of synthetic identity fraud and highly targeted social‑engineering campaigns.
PayPal acknowledged that unauthorized transactions occurred on a small number of accounts; these transactions were refunded, but they demonstrate how quickly exposed data can be exploited. Victims must remain vigilant by monitoring credit reports, reviewing account activity and enrolling in the offered credit‑monitoring service.
Because PPWC serves small businesses, the breach disproportionately impacts entrepreneurs and sole proprietors whose personal information is tied to their business accounts.
Company Response and Customer Remediation
PayPal responded quickly after identifying the issue. Within one day of discovering the bug, the company rolled back the code change responsible for the exposure and terminated unauthorized access.
It reset passwords for all impacted accounts and required users to create new credentials upon their next login. Affected customers were offered two years of complimentary three‑bureau credit monitoring and identity‑restoration services through Equifax, with enrollment required by June 30 2026.
PayPal issued refunds to those who experienced fraudulent transactions and provided detailed guidance on securing accounts, including using unique passwords, monitoring for suspicious activity and being cautious of phishing emails.
The company emphasized that it had not delayed notification due to any law‑enforcement investigation. It reminded users that PayPal will never ask for passwords or one‑time codes via phone or email.
Government, Law Enforcement, and Regulator Actions
At the time of writing, no regulatory fines or law‑enforcement actions have been announced in connection with this incident. PayPal complied with state‑level data‑breach notification laws by sending letters dated February 10 2026 to affected customers.
The Massachusetts notice publicly filed by the Attorney General’s Office details the cause of the breach, the dates of exposure and PayPal’s remediation steps.
There is no evidence that law‑enforcement agencies were investigating an external hack, and PayPal claims that it did not delay disclosure for investigative reasons. Regulators in other states have not publicly commented.
However, PayPal’s earlier security incidents have drawn regulatory attention; in January 2025, New York’s Department of Financial Services fined the company $2 million for failing to meet cybersecurity requirements related to a 2022 credential‑stuffing attack. The recurrence of security issues may lead to increased scrutiny of PayPal’s compliance practices.
Financial, Legal, and Business Impact
Financially, the PPWC breach is modest compared with large‑scale cyberattacks, but the costs are not negligible. PayPal has refunded fraudulent transactions and is paying for two years of credit monitoring and identity restoration services for each affected customer, expenses that can reach hundreds of dollars per person.
The breach also exposes PayPal to reputational risk; as a major fintech platform, even a small incident can erode trust among merchants and users. Industry analysts note that the event follows a series of security lapses—most notably the December 2022 credential‑stuffing attack that compromised 35,000 accounts. Repeated incidents may prompt investors and regulators to demand stronger internal controls.
While no lawsuits have been announced yet, affected customers could pursue legal action if identity theft or fraud occurs. PayPal may also face inquiries from data‑protection regulators, especially because the breach involved Social Security numbers, which are subject to strict legal protections.
What Remains Unclear About the Incident
Several aspects of the PPWC data exposure remain uncertain. PayPal has not publicly disclosed the exact number of affected customers; sources such as The Register and BleepingComputer report that roughly 100 people were notified, while the official letters refer only to a “small number”.
The company has not explained precisely how the coding error made data accessible, beyond stating that it was an application‑level bug.
It is also unclear whether any organized threat actor actively exploited the vulnerability or whether the unauthorized transactions were opportunistic.
PayPal has not indicated whether the exposed data was sold on dark‑web markets or how it monitored potential downstream misuse.
The duration of undetected exposure, almost 165 days, raises questions about the effectiveness of PayPal’s change‑management and monitoring processes.
Regulators have not announced investigations, so the incident’s legal ramifications are still unknown. More information may emerge if affected customers file complaints or if authorities investigate the code‑review process that allowed the bug to persist.
Why This Incident Matters
This breach is significant despite its limited scale because it illustrates how software errors can expose sensitive data over extended periods. PayPal’s PPWC platform handles financing for small businesses, making the exposed data particularly valuable to criminals. The incident highlights the importance of rigorous code review, continuous monitoring and robust change‑management practices in financial applications.
It also shows that personal identifiers such as Social Security numbers can be exposed even when the main system is secure. Cybersecurity experts warn that long‑lasting exposures increase the risk of identity theft, synthetic fraud and highly targeted social‑engineering attacks.
The event follows earlier PayPal security lapses, suggesting systemic challenges in the company’s security culture. The combination of prolonged exposure, sensitive data and repeat incidents is likely to attract regulatory scrutiny and underscores the need for continuous improvement in fintech security.
How Bright Defense Could Prevent Similar Incidents
Bright Defense could have limited the PPWC data exposure through continuous testing, monitoring, and secure development controls. Ongoing penetration testing and integrated code analysis can detect business-logic flaws and risky code changes before or soon after release.
Continuous compliance checks and real-time monitoring can flag policy violations and unusual data access, which goes to show how early detection reduces exposure time.
Audit logs support fast root-cause review and regulatory reporting, while secure development training helps engineers apply proper access controls. This approach could have caught the faulty PPWC update before months of customer data remained exposed.
Sources
- BleepingComputer — “PayPal discloses data breach that exposed user info for 6 months” (February 20 2026). https://www.bleepingcomputer.com/news/security/paypal-discloses-data-breach-exposing-users-personal-information/
- Massachusetts Attorney General — “Notice of Data Breach” (February 10 2026).https://www.mass.gov/doc/2026-240-paypal-inc/download
- The Register — “PayPal app code error leaked personal info and a ‘few’ unauthorized transactions” (February 20 2026). https://www.theregister.com/2026/02/20/paypal_app_code_error_leak/
- TechRepublic — “PayPal Flaw Exposed Email Addresses, Social Security Numbers for 6 Months” (February 20 2026).https://www.techrepublic.com/article/news-paypal-working-capital-data-exposure-2025/
- Cybernews — “PayPal breach went undetected for six months, exposing Social Security numbers” (February 20 2026). https://cybernews.com/security/paypal-six-month-breach-ssn-working-capital-app/
- Techzine — “PayPal leaked sensitive data for six months due to software error” (February 20 2026). https://www.techzine.eu/news/security/138969/paypal-leaked-sensitive-data-for-six-months-due-to-software-error/
- Cyber Press — “PayPal Data Breach – Customers Names, SSNs, and Dates of Birth Exposed” (February 20 2026). https://cyberpress.org/paypal-data-breach/ly%20six%20months
- BleepingComputer — “Earlier PayPal credential stuffing breach compromised 35,000 accounts” (January 2023). https://www.bleepingcomputer.com/news/security/paypal-discloses-data-breach-exposing-users-personal-information/
Get In Touch