
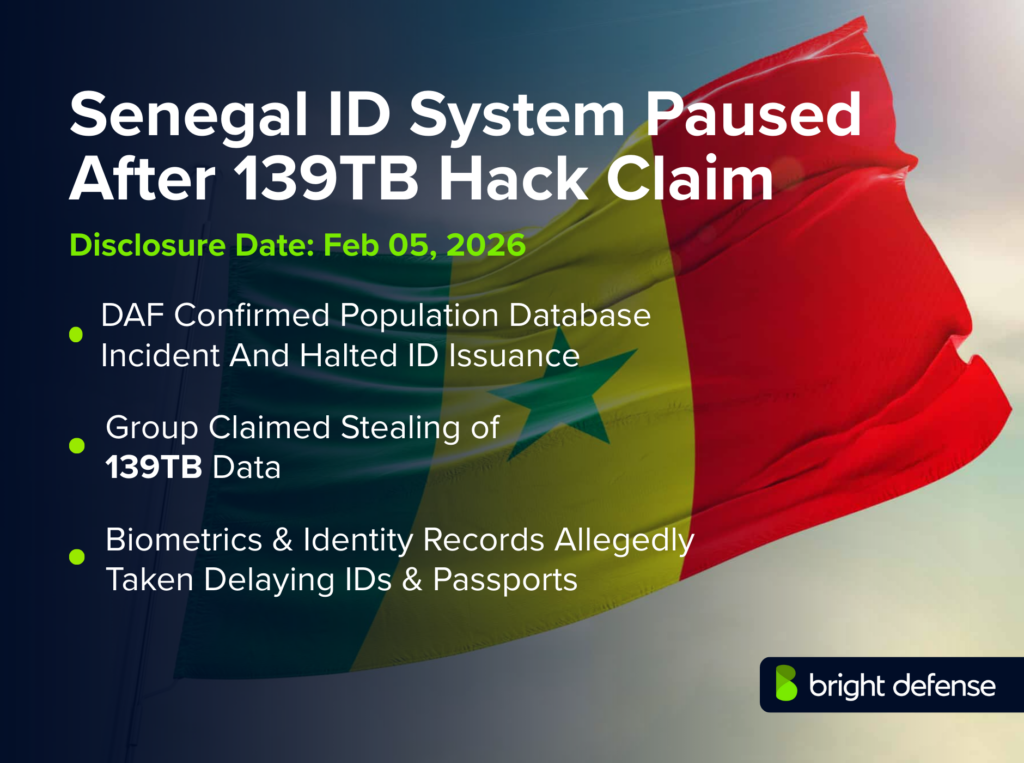
Senegal ID System Breach – 139TB Hack Claim
Senegal temporarily suspended national identity card production after a cyber incident hit the Directorate of File Automation, while a ransomware group claimed it stole up to 139TB of highly sensitive citizen data.
What Happened in the Breach
Senegal’s Directorate of File Automation, known as the DAF, announced an “incident” in its information system and said the national ID card production service was “momentarily” suspended, with technical teams tasked with restoring operations and an investigation opened.
The disruption followed criminal claims from a ransomware operation calling itself the Green Blood Group, with public reporting describing competing figures for the alleged theft, including an unverified claim of 139TB and a separate claim of 139GB.
Timeline: From First Access To Latest Update
- January 19, 2026: A leaked email cited in reporting said attackers compromised 2 DAF servers on this date and stole “card personalization” data, with the message attributed to an executive at IRIS Corporation Berhad, a Malaysian supplier tied to Senegal’s digital ID card program
- January 20, 2026: Reporting cited the same IRIS-linked email as warning Senegalese officials and describing immediate containment steps such as cutting network connections and password changes
- January 22, 2026: The IRIS-linked email cited in reporting described plans for a technical visit to Dakar to support further investigation and corrective actions
- February 5, 2026: The DAF announced the temporary suspension of national ID card production, said an investigation was opened, and told the public that personal data remained intact
- February 5, 2026: Reporting said the Green Blood Group published proof on the dark web and claimed possession of the DAF’s database totaling 139TB, while Senegalese authorities did not confirm the size
- February 6, 2026: Local reporting said Senegal Numérique SA, a state digital infrastructure entity, was also compromised around the same time, though Senegalese authorities have not issued a consolidated technical accounting for the second claim
- February 9, 2026: Reporting said the cyber incident forced the temporary suspension of DAF operations tied to national ID cards, passports, and biometric services, with a senior police official saying restoration work was underway and that citizen data integrity remained intact
- February 12, 2026: Trade press reporting stated the Green Blood Group referenced 139TB on its leak site but referenced 139GB elsewhere, leaving the true volume unverified in public records
What Data Or Systems Were Affected
The DAF functions as a core identity-services body, with public reporting describing it as responsible for the biometric population register and the issuance of identity documents such as national ID cards and passports.
The Green Blood Group’s claims described theft covering citizen database records, biometric data, and immigration-related files, while the DAF’s public communications said no leak or alteration of personal data was recorded and that citizen data remained intact.
Who Was Responsible (Confirmed Vs Alleged)
Senegalese authorities have not publicly attributed the intrusion to a named actor in the official DAF communications carried by state and national outlets.
The Green Blood Group claimed responsibility in dark web postings cited in multiple reports, and reporting also described the group as a newly emerged ransomware operation with limited publicly verified background.
How The Attack Worked
Public sources have not provided a confirmed initial access vector, and the DAF has not published a technical incident report describing intrusion path, privilege escalation, or exfiltration mechanics.
Reporting tied the earliest concrete technical clue to the leaked IRIS-linked email, which described the compromise of 2 DAF servers on January 19, 2026 and the theft of ID card personalization data, but that description has not been corroborated in a detailed public forensic summary from Senegalese authorities.
Impact and Risks for Customers
The direct public-facing impact was service availability, since the DAF said national ID card production was suspended across Senegal until technical teams restore operations, with no restart date listed in the official DAF statements carried by APS and RTS.
The larger risk centers on potential identity fraud and targeted scams if stolen datasets contain biometric or civil status attributes, with reporting emphasizing that the 139TB volume remains unverified and that official communications disputed any confirmed data leak at the time of publication.
Company Response And Customer Remediation
The DAF said competent technical services took steps to restore service as quickly as possible and that an investigation was opened to determine cause and responsibility.
Reporting said IRIS Corporation Berhad actions described in the leaked email included cutting off a server connection, changing a password, and shutting network links to foreign missions and other offices, which implies a containment posture even though Senegalese authorities have not released a full post-incident control summary.
Government, Law Enforcement, And Regulator Actions
APS reported that the DAF communiqué was signed by Commissioner Ibrahima Dieng and that an investigation was opened, with the DAF framing the event as an incident inside its system rather than a confirmed national database leak.
Reporting also cited a senior police official saying restoration efforts were underway and that citizen data integrity remained intact, while national reporting continued to flag uncertainty over the breach scope and the attackers’ claimed data volume.
Financial, Legal, And Business Impact
Public sources reviewed did not provide a confirmed ransom amount, a verified data-exfiltration volume, or a quantified cost estimate for response, service disruption, or reissuance of identity documents.
Local reporting tied the incident to broader scrutiny of state digital infrastructure, including separate claims of compromise involving Senegal Numérique SA and discussion of IRIS’s role in national ID modernization, but official statements have not validated those related claims in a single authoritative report.
What Remains Unclear About the Breach
The total volume of data potentially accessed remains unverified in public reporting, with claims spanning 139TB and 139GB, and with official DAF communications stating that citizen personal data remained intact and that no leak was recorded.
The incident start time, detection time, containment milestones, and restoration timeline remain only partially documented publicly, with official statements confirming a service halt but not providing a dated technical chronology beyond the suspension announcement.
Why This Incident Matters
A disruption to national identity issuance creates broad downstream friction for banking, telecom onboarding, travel, public benefits, and civil administration, since the DAF plays a central role in biometric register operations and identity document production.
The incident also follows earlier Senegal government cyber disruptions reported in recent years, which increases urgency for tighter protection of identity infrastructure even when official messaging disputes the attackers’ leak claims.
Bright Defense: Reducing National ID and Biometric System Breach Risk
Bright Defense can reduce the likelihood and blast radius of incidents like this through penetration testing that targets identity-service attack paths such as privileged access abuse, directory service compromise, segmentation gaps around population register systems, and high-risk administrative workflows connected to card personalization and issuance. Continuous compliance can keep evidence and control operation current across access reviews, logging, incident response readiness, backup integrity, and third-party risk controls that often matter most after a ransomware claim.
Sources
- APS — Piratage informatique : la DAF annonce la suspension provisoire de la production de cartes nationales d’identité (February 5, 2026)
https://aps.sn/piratage-informatique-la-daf-annonce-la-suspension-provisoire-de-la-production-de-cartes-nationales-didentite/ - RTS — Incident technique à la DAF : l’institution rassure sur la sécurité des données, une enquête ouverte (February 5, 2026)
https://www.rts.sn/actualite/detail/a-la-une/incident-technique-a-la-daf-linstitution-rassure-sur-la-securite-des-donnees-une-enquete-ouverte - The Record — Senegal confirms breach of national ID card department after ransomware claims (February 9, 2026)
https://therecord.media/senegal-breach-national-id-agency - Dark Reading — Senegalese Data Breaches Expose Lack of Security Maturity (February 12, 2026)
https://www.darkreading.com/cyberattacks-data-breaches/hackers-breach-senegal-national-biometric-database - Biometric Update — Senegal data breach disrupts national ID issuance (February 10, 2026)
https://www.biometricupdate.com/202602/senegal-data-breach-disrupts-national-id-issuance - INCYBER News — A leak may have compromised the sensitive data of Senegal’s entire population (February 6, 2026)
https://incyber.org/en/article/a-leak-may-have-compromised-the-sensitive-data-of-senegals-entire-population/ - AllAfrica, republished from RFI — Sénégal: Le DAF, un département du ministère de l’Intérieur, touché par une cyberattaque (February 7, 2026)
https://fr.allafrica.com/stories/202602070072.html - Seneweb — After the Daf: SENUM SA, guardian of state data, hacked (February 6, 2026)
https://www.seneweb.com/en/news/Technologie/apres-la-daf-senum-sa-gardienne-des-donnees-de-letat-piratee-1_n_482615.html - The Gambia Journal — Senegal’s File Automation Directorate Hit by Cyberattack, Hackers Claim 139TB Data Breach (February 5, 2026)
https://gambiaj.com/senegals-file-automation-directorate-hit-by-cyberattack-hackers-claim-139tb-data-breach/
Get In Touch



