
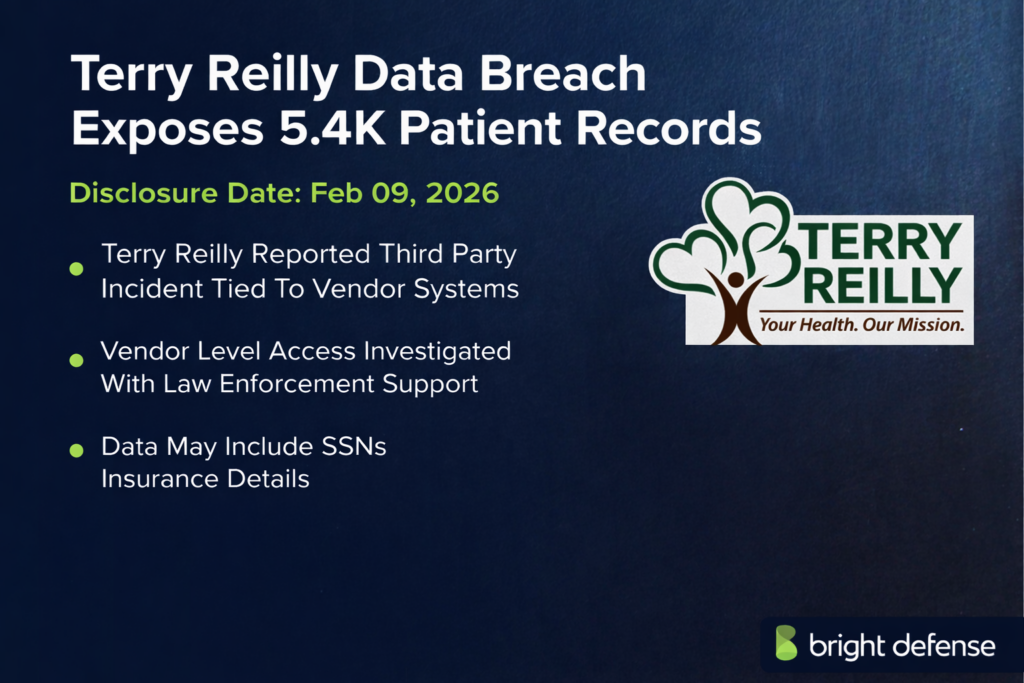
Terry Reilly Data Breach Exposes 5.4K Patient Records
What Happened in the Breach
Community Health Clinics Inc., doing business as Terry Reilly Health Services (TRHS) in Nampa, Idaho, disclosed February 9 2026 that a security incident at its billing vendor risked exposing the personally identifiable information of about 5,421 patients.
According to TRHS, the breach did not originate on its own systems; instead, it stemmed from a compromise at TriZetto Provider Solutions (TPS), a Missouri‑based insurance‑eligibility clearinghouse subcontracted by OCHIN, the electronic health‑record provider used by TRHS.
TRHS said the unauthorized access to TPS may have exposed patients’ names, addresses, dates of birth, Social Security numbers, health insurance member numbers, insurance company names, provider names, dependent details and other demographic or clinical information.
Financial account or payment card details were not included. The Idaho clinic stressed that it learned of the incident through its vendor and took immediate steps to notify affected patients, offer credit monitoring and cooperate with investigators.
Timeline: From First Access To Latest Update
- Nov 2024–Oct 2, 2025: An unknown actor accessed historical eligibility reports in a TriZetto web portal for about 11 months; TriZetto detected activity on Oct 2, secured the portal, hired Mandiant, and stopped the access.
- Oct–Nov 2025: TriZetto reviewed the system and found exposed data in reports included identifiers and health plan details such as names, addresses, DOBs, SSNs, member or Medicare numbers, insurer names, and demographics; financial data was not involved.
- Dec 10, 2025: Oregon health agencies said TriZetto notified them; Deschutes, La Pine, and Best Care began notifying about 1,300, 1,200, and 1,650 clients and offered identity protection.
- Jan 15, 2026: A HIPAA Journal update said TriZetto began client breach notices, offered to manage regulatory notices, and provided credit monitoring and identity restoration; one client was told over 700,000 people were likely impacted.
- Feb 9, 2026: Terry Reilly Health Services posted a notice and began mailing letters with Kroll enrollment codes; KIVI said letters would arrive within about a week with details on impacted data.
- Feb 9–Feb 12, 2026: Media and law firms highlighted the breach; reported counts ranged around 5,000, with one listing 5,421, and free credit monitoring was noted for affected patients.
- Feb 18, 2026: Schubert Jonckheer & Kolbe said it was investigating TriZetto over alleged notification delays tied to access from Nov 2024 to Oct 2, 2025, with some notices reaching people in Dec 2025.
- Feb 19, 2026 onward: Class-action investigations and regulatory attention continued; TriZetto had not publicly confirmed the exact number of affected TRHS patients, and tracking continued through covered-entity reporting.
What Data Or Systems Were Affected
The breach occurred in a TriZetto web portal used by healthcare providers to verify patient insurance eligibility. Forensic investigators determined that the threat actor accessed historical eligibility transaction reports containing both personally identifiable information (PII) and protected health information (PHI) of patients.
According to TriZetto’s investigation, the compromised data included names, addresses, dates of birth, Social Security numbers, health insurance member numbers or Medicare beneficiary numbers, insurance company names, information about the primary insured or beneficiary and other demographic health information.
These reports did not hold financial account data or payment card details. In the case of Terry Reilly Health Services, the clinic disclosed that the exposed information might include patient names, addresses, birth dates, Social Security numbers, health insurance member numbers, insurer names, provider names, dependent information and other health or insurance‑related details. The clinic confirmed that no financial account or payment card information was involved.
Who Was Responsible (Confirmed Vs Alleged)
TriZetto Provider Solutions, a Missouri‑based revenue‑management service owned by Cognizant, was the vendor whose systems were breached. The unauthorized actor has not been publicly identified, and investigators have not confirmed whether the intrusion was part of a broader campaign.
TriZetto engaged the cybersecurity firm Mandiant to investigate and eradicate the threat. At present, there is no publicly available evidence linking the incident to a specific cybercrime group, nor has any ransomware gang taken credit.
Some law firms have alleged that TriZetto delayed notifying affected entities until December 2025 or later, despite evidence that the breach began in November 2024. TriZetto has not commented publicly on those allegations. For Terry Reilly Health Services, there is no indication the clinic was at fault; it was a downstream victim of its vendor’s security lapse.
How The Attack Worked
Investigators believe the breach resulted from an unauthorized third party obtaining credentials to TriZetto’s insurance‑eligibility web portal. The intruder accessed stored eligibility transaction reports—documents used by healthcare providers to verify insurance coverage—beginning around November 2024.
TriZetto detected suspicious activity almost eleven months later on October 2 2025. After detection, TriZetto shut down external access to the portal, engaged Mandiant to perform a forensic investigation and implemented additional security controls.
The breach exploited the long dwell time; during that period, the threat actor had access to sensitive demographic and insurance data from multiple healthcare providers. There is no evidence that malware or ransomware was deployed in this incident. The breach appears to have been a credential compromise that allowed data exfiltration rather than direct system takeover.
Impact and Risks for Customers
For patients of Terry Reilly Health Services and other affected providers, the exposure of Social Security numbers, dates of birth, addresses and insurance identifiers creates a heightened risk of identity theft and medical fraud. Criminals could use the stolen data to open fraudulent accounts, file fraudulent insurance claims or impersonate patients to obtain medical services.
Even without financial information, the combination of PII and PHI is highly sensitive and can be sold on darknet marketplaces.
The HIPAA Journal noted that the compromised dataset potentially covers more than 700,000 individuals across at least 26 healthcare providers. Claim Depot reported that 5,421 Terry Reilly patients were affected, although this number has not been confirmed by TriZetto or TRHS.
Local reports emphasised that the exposed data includes dependent information and provider names, increasing the risk of targeted phishing and insurance fraud. No evidence has emerged of misuse of the TRHS patient data to date, but identity‑theft schemes often have a long tail.
Company Response And Customer Remediation
Upon learning of the breach, TriZetto secured the compromised portal, engaged Mandiant and law enforcement, and said it eliminated the threat actor from its environment. The company offered to handle notification and regulatory reporting on behalf of its healthcare clients and committed to providing complimentary credit monitoring, fraud consultation and identity‑theft restoration services for affected individuals.
For the Terry Reilly incident, TRHS posted a detailed notice on its website and began mailing notification letters to potentially impacted patients on February 9 2026. Each letter contained a specific membership number that allowed patients to enroll in Kroll’s identity‑protection program, which includes credit monitoring, fraud consultation and identity‑theft restoration services for at least one year. TRHS advised patients to call the Kroll helpline and to monitor their credit reports and insurance statements for suspicious activity.
KIVI reported that the letters would explain what information may have been affected and include instructions for enrolling in the free services. Law firms investigating the incident are encouraging patients to review the breach notice and enroll in the offered credit monitoring. There is no indication that either TriZetto or TRHS is offering monetary compensation beyond identity‑protection services at this time.
Government, Law Enforcement, And Regulator Actions
TriZetto notified the U.S. Department of Health and Human Services Office for Civil Rights (HHS OCR) about the breach and offered to file notifications on behalf of its clients.
The clinic’s notice indicates that law enforcement and cybersecurity specialists were alerted once the incident was discovered. The breach is under investigation by state attorneys general and class‑action law firms.
Schubert Jonckheer & Kolbe LLP and Strauss Borrelli PLLC announced investigations into whether TriZetto violated data‑breach notification laws by waiting several months to inform affected entities. Claim Depot noted that TRHS reported the incident to the HHS OCR on January 15 2026. Regulatory actions remain ongoing, and no enforcement fines had been announced at the time of publication.
Financial, Legal, And Business Impact
TriZetto’s breach has broad implications for healthcare providers across the United States. The HIPAA Journal reported that the incident may have exposed records for more than 700,000 individuals.
Entities such as Deschutes County Health Services, La Pine Community Health Center and Best Care estimated that between 1,200 and 1,650 of their patients were affected, while TRHS identified about 5,421 potentially impacted patients. Each affected organization must offer credit‑monitoring services and may face costs related to notification, legal counsel and potential class‑action litigation.
TriZetto faces reputational damage and potential liability for failing to detect and report the breach promptly; law firms have suggested that delayed notification might violate state and federal laws. However, as of February 2026, there is no evidence that the breach led to direct financial losses for patients or that unauthorized medical billing has occurred.
TRHS continues to operate normally but may experience increased scrutiny of its vendor‑risk management practices. Some healthcare clients, such as Deschutes County agencies, have chosen to send their own notifications rather than rely on TriZetto’s timeline, reflecting the erosion of trust.
What Remains Unclear About the Idaho Clinic Breach
- Investigators have not publicly identified the threat actor.
- The method used to obtain access credentials remains unclear.
- TriZetto has not disclosed the client specific affected counts, including TRHS.
- The notification timeline remains disputed, with reports pointing to December 2025 and other accounts citing December 10, 2025.
- Public reporting has not confirmed data sales or misuse on underground forums.
- Investigations by state attorneys general and the HHS OCR remain ongoing.
- Fines, corrective actions, or settlement terms have not been announced.
- The long term impact on TRHS reputation and patient trust depends on communication transparency and the effectiveness of identity protection services.
Why This Incident Matters
This breach underscores the systemic risks posed by third‑party vendors in the healthcare sector. Although Terry Reilly Health Services did not suffer an internal systems compromise, its patients’ sensitive information became vulnerable because a subcontractor of its electronic health‑record provider failed to detect unauthorized access for nearly a year.
The incident highlights how personal and medical data can be compromised through supply‑chain relationships and how long dwell times can occur in vendor environments. By exposing Social Security numbers, dates of birth, insurance identifiers and health details, the TriZetto breach creates fertile ground for identity theft, medical fraud and targeted scams.
The event also illustrates the challenges of timely breach notification and the need for healthcare organizations to monitor vendor security practices. With more than 700,000 individuals potentially affected and at least 5,421 patients at a single Idaho clinic facing identity‑theft risks, the episode serves as a stark reminder that even small healthcare providers must demand rigorous security and rapid incident reporting from their third‑party partners.
Bright Defense: Strengthening Defenses Through Pen Tests and Continuous Compliance
Bright Defense provides proactive controls that could have reduced the TriZetto incident’s impact. Vendor portal penetration testing can find weak authentication, misconfigurations, and excessive access before attackers act. Simulated credential compromise and data exfiltration testing can measure detection and containment speed.
Continuous compliance monitoring keeps third party systems aligned with HIPAA and NIST SP 800-53 while automated audits flag deviations quickly. Vendor risk management improves due diligence, contract security terms, and breach notification timelines. For healthcare groups like Terry Reilly, Bright Defense provides fast anomaly alerts, clear remediation steps, and support for regulator and patient communications.
Sources
- Terry Reilly Health Services — Data Security Incident – Februrary 9 2026 notice (February 9, 2026)
https://www.trhs.org/notices - KIVI News — Terry Reilly says some patients’ personal health details may have been exposed (February 10, 2026)
https://www.kivitv.com/news/local-news/terry-reilly-says-some-patients-personal-health-details-may-have-been-exposed - HIPAA Journal — TriZetto Provider Solutions Issues Data Breach Notifications to HIPAA Covered Entities (January 15, 2026)
https://www.hipaajournal.com/trizetto-provider-solutions-data-breach/ - Deschutes County Health Services — Contractor data breach impacts health information of thousands in Central Oregon (January 29, 2026)
https://www.deschutes.org/health/page/contractor-data-breach-impacts-health-information-thousands-central-oregon - Schubert Jonckheer & Kolbe LLP via PR Newswire — Privacy Alert: TriZetto Provider Solutions Under Investigation for Data Breach of Over 700,000 Patient Records (February 18, 2026)
https://www.prnewswire.com/news-releases/privacy-alert-trizetto-provider-solutions-under-investigation-for-data-breach-of-over-700-000-patient-records-302691109.html - Strauss Borrelli PLLC — Terry Reilly Health Services Data Breach Investigation (February 12, 2026)
https://straussborrelli.com/2026/02/12/terry-reilly-health-services-data-breach-investigation/ - Claim Depot — Terry Reilly Health Services Data Breach: 5,421 Affected (February 12, 2026)
https://www.claimdepot.com/data-breach/terry-reilly-health-services-2026 - BeyondMachines — Terry Reilly Health Services Reports Data Breach Caused by Third Party Compromise (February 10, 2026)
https://beyondmachines.net/event_details/terry-reilly-health-services-reports-data-breach-stemming-from-trizetto-vendor-compromise-f-9-f-m-y
Get In Touch



