Updated:
March 17, 2026
What is Compliance Monitoring? Why is it Important?
Non-compliance already carries major financial consequences. Global fines for non-compliance reached $14 billion in 2024, and the global average cost of a data breach was $4.4 million in 2025. For smaller firms, the fallout can be severe. Research cited by the Council of Insurance Agents & Brokers says 60% of small businesses cannot withstand the six months following a cyberattack.
In 2026, compliance is no longer just about preparing for an annual audit. Regulators are focusing less on one-off compliance artifacts and more on whether privacy and cybersecurity programs operate coherently and at scale across jurisdictions.
With regulatory demands expanding across states and sectors, companies face fines, operational strain, and reputational damage if they fall short. Morgan Lewis notes that developments in 2025 materially increased the documentation, assessment, and governance burden on organizations operating across multiple jurisdictions.
Compliance monitoring tools support a more proactive approach. NIST says continuous monitoring provides visibility into organizational assets, awareness of threats and vulnerabilities, and visibility into the effectiveness of deployed security controls. It also provides the information needed to respond to risk in a timely manner.
That ongoing visibility helps organizations stay closer to their regulatory obligations, reduce the chance of costly failures, and make compliance part of day-to-day operations rather than a once-a-year exercise.
In this article, we will cover:
- The shift from periodic to continuous compliance monitoring
- Key components of an effective monitoring system including automated checks, real-time alerts, and customizable dashboards
- Challenges in implementing compliance monitoring systems and how to overcome them
- Best practices for maintaining continuous compliance
What is Compliance Monitoring?
Compliance monitoring is the ongoing process of checking that an organization follows laws, regulations, policies, and standards. It helps detect issues early and supports corrective action before they become serious problems.

At its core, compliance monitoring involves regular checks that help detect and address compliance gaps in real time. Unlike traditional approaches that rely on annual reviews or external audits, it connects daily operations with compliance requirements so issues can be corrected quickly and the risk of violations stays lower.
This integration allows for immediate adjustments, reducing the risk of compliance breaches.
The Importance of Compliance Monitoring
Compliance monitoring matters because compliance rarely breaks in a single moment. It weakens over time as controls drift, systems change, employees leave or change roles, and processes that passed an audit months earlier fall out of alignment. Monitoring helps organizations catch those gaps early and correct them before they become audit findings, contract delays, or regulatory issues.
Here are 5 key factors that make compliance monitoring crucial right now:

1. Compliance Is No Longer Static
Most companies still think about compliance in snapshots: a SOC 2 audit, an annual risk review, or a point-in-time certification. That mindset no longer matches reality. In PwC’s Global Compliance Survey 2025, 85% of respondents said compliance requirements had become more complex over the past three years, and 77% said that complexity had negatively affected their company in growth-related areas. When requirements shift this quickly, a once-a-year check cannot keep up.
Monitoring turns compliance into a living process. Instead of asking whether the company was compliant last year, teams can see whether controls are still operating today under current conditions.
2. Small Gaps Create Large Costs
Most compliance failures do not start with major incidents. They start with small issues that go unnoticed: an access review that stops happening, a vendor that never gets reassessed, or logging that quietly breaks after a system update. The financial impact of letting those gaps grow is well documented.
IBM’s 2025 Cost of a Data Breach Report found that the global average breach cost was $4.44 million, while the average cost in the United States reached $10.22 million. PwC’s Global Compliance Survey 2025 also found that 77% of organizations reported negative business impact from rising compliance complexity. Monitoring exists to catch those gaps early, before they turn into expensive problems.
3. Auditors Expect Ongoing Evidence
Audit expectations have changed, even if audit schedules have not. SOC 2 Type 2 audits require evidence that controls operated effectively over a defined review period, not just at audit time, and that review window typically spans 3 to 12 months. A-LIGN’s State of Compliance 2026 found that 97% of organizations now conduct at least two audits per year, and 74% of enterprise organizations conduct four or more. That level of scrutiny makes manual, last-minute evidence collection unreliable.
Compliance monitoring makes this easier. Drata notes that SOC 2 Type 2 audits require proof that controls operate effectively over time, and that continuous monitoring and automated evidence collection reduce manual work and audit prep time. When controls are tracked continuously, evidence already exists when auditors ask for it, and teams spend less time scrambling to assemble support at the end of the cycle.
4. Monitoring Protects Revenue, Not Just Risk
Compliance failures do not only create regulatory exposure; they disrupt growth. In PwC’s Global Compliance Survey 2025, 49% of organizations said planned new products and services would require compliance support, 44% said the same for deals and corporate transactions, 43% for entering new markets, and 41% for new business models. Elsewhere in the same survey, 77% said rising compliance complexity had already negatively affected their company in five or more business areas tied to growth.
Monitoring reduces those disruptions. NIST says continuous monitoring gives organizations visibility into assets, threats, vulnerabilities, and the effectiveness of deployed controls, along with the information needed to respond to risk in a timely manner. When compliance status stays visible, teams can move faster with reviews, audits, and due diligence instead of reacting at the last minute.
5. Continuous Oversight Is Becoming the Norm
The shift toward monitoring is no longer theoretical. Industry data shows it is already underway. RegScale’s 2026 State of Continuous Controls Monitoring report, based on a survey of 253 InfoSec leaders, found that 95% of organizations have implemented some level of GRC automation, but only 28% continuously monitor security controls in real time, while 72% still rely on periodic assessments. That gap shows both how quickly continuous oversight is gaining ground and how much room remains between intent and execution.
Compliance monitoring is not about adding overhead. It is about replacing reactive work with ongoing visibility. In the same report, 83% of organizations said manual compliance work causes moderate or major delays, and 85% said resource constraints had forced them to delay or eliminate legacy GRC activities. Organizations that monitor continuously spend less time reacting to surprises and more time operating with clarity.
The Shift from Periodic to Continuous Compliance
The shift from periodic compliance checks to continuous monitoring reflects a major change in how organizations manage regulatory obligations. Periodic reviews still serve a purpose, but they often treat compliance as a point-in-time task rather than an everyday discipline. Continuous monitoring moves away from that episodic model by embedding compliance into daily operations and giving teams ongoing visibility into controls, vulnerabilities, threats, and policy adherence so they can respond faster when gaps appear. NIST defines continuous monitoring as maintaining ongoing awareness of security, vulnerabilities, and threats to support risk-based decisions, PwC’s Global Compliance Survey 2025 found that 85% of organizations said compliance requirements had become more complex over the past three years, and a 2026 industry survey found that only 28% of organizations continuously monitor security controls in real time while 72% still rely on periodic assessments.
This shift is driven by several factors:
- Technological advancements: New tools now make real-time compliance tracking practical. NIST defines continuous monitoring as maintaining ongoing awareness of security, vulnerabilities, and threats, and says it gives organizations visibility into assets and the effectiveness of deployed controls.
- Regulatory expectations: Rules and oversight models increasingly favor continuous monitoring over point-in-time reviews. FedRAMP’s current playbook requires at least monthly vulnerability scans of 100% of inventory components, and its collaborative monitoring model requires an ongoing authorization report every 3 months.
- Business continuity and risk management: Continuous monitoring helps reduce the chance that small control failures turn into expensive incidents. IBM’s 2025 Cost of a Data Breach Report puts the global average breach cost at $4.4 million, while PwC’s Global Compliance Survey 2025 found that 85% of organizations said compliance requirements had become more complex over the past three years.
In short, compliance monitoring is not only a defensive response to non-compliance. It embeds compliance into daily operations, replaces reactive review cycles with ongoing visibility, and helps organizations respond faster as requirements and risks change.
Key Components of an Effective Compliance Monitoring Program
To build an effective compliance monitoring program, organizations need a structure that is clear enough to operate every day and flexible enough to adapt when risks, systems, or requirements change. At a minimum, that means defining what must be monitored, assigning ownership, collecting evidence consistently, addressing issues quickly, and reviewing the program regularly so it stays relevant over time.
Here are the key elements that contribute to the efficacy of a compliance monitoring system:
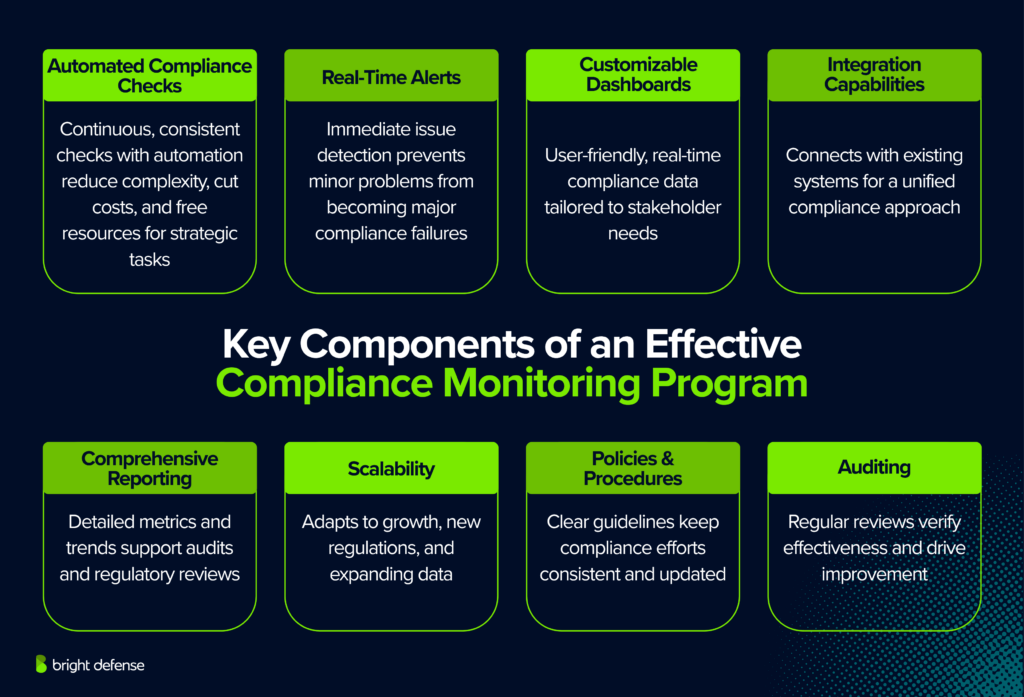
1. Automated Compliance Checks
Automation is a cornerstone of modern compliance monitoring because it allows organizations to perform continuous, consistent checks with far less manual effort. In RegScale’s 2026 State of Continuous Controls Monitoring report, 83% of organizations said manual compliance work causes moderate or major delays, and 53% said evidence collection alone consumes the equivalent of one full-time employee.
Automated systems scan controls, configurations, and related evidence for deviations from compliance requirements and alert the right personnel when issues appear. NIST says continuous monitoring is supported by automation across areas such as vulnerability management, patch management, event management, incident management, asset management, and configuration management. This improves consistency, reduces manual effort, and frees teams to focus on more strategic work.
2. Real-Time Alerts
Real-time alerts are essential for identifying and responding to potential compliance issues as soon as they appear. Current research shows that only 26% of organizations integrate incident response into their third-party risk programs, and fewer than half monitor even 50% of their extended supply chain for cyber threats. (SecurityScorecard)
Real-time alerts help organizations address problems as they arise, which reduces the chance that minor issues grow into larger compliance failures. NIST says continuous monitoring supports ongoing awareness of threats, vulnerabilities, and control effectiveness, giving teams the information they need to respond in a timely manner. (NIST Publications)
3. Customizable Dashboards
Customizable dashboards give teams a clear way to view real-time compliance status without sorting through separate reports. NIST’s continuous monitoring guidance says effective programs should collect information for metrics, assessments, and reporting, and it calls for status reports customized to support decision-making at different organizational tiers. CISA’s current FISMA metrics guidance also points to continuous monitoring dashboards and reports as part of mature monitoring. That makes it easier for IT teams, compliance staff, and executives to track the KPIs that matter to them and respond faster when issues appear.
4. Integration Capabilities
A strong compliance monitoring system should integrate with the organization’s existing systems and software. NIST says effective continuous monitoring includes an organization-wide perspective and integration with the system development life cycle, which helps embed compliance activities into daily operations instead of treating them as a separate exercise. That kind of integration reduces fragmented oversight and gives teams more timely visibility into control status, configuration changes, and emerging issues. (NIST Publications)
Effective integration also helps maintain a unified view of the organization’s compliance posture across departments and functions. NIST says continuous monitoring provides ongoing awareness of security, vulnerabilities, threats, and the effectiveness of deployed controls, while current CISA FISMA metrics guidance points to continuous monitoring dashboards and reports that support organization-wide visibility and decision-making. That broader visibility makes it easier to spot gaps early, coordinate corrective action, and keep compliance aligned with how the business actually operates. (NIST)
5. Comprehensive Reporting
Comprehensive reporting capabilities are essential for tracking compliance over time and preparing for audits. Effective reports should show compliance metrics, surface trends, document exceptions, and highlight areas that need corrective action. NIST’s continuous monitoring guidance specifically calls for collecting information for metrics, assessments, and reporting, then analyzing and reporting findings so organizations can make timely risk decisions. (NIST Publications)
That documentation is valuable for both internal review and external oversight. NIST also calls for customized status reporting to support decision-making across organizational levels, while current CISA FISMA metrics continue to treat continuous monitoring and reporting as a core part of security program oversight. (NIST Publications)
6. Scalability
As organizations grow and change, their compliance monitoring systems must scale with them. NIST says continuous monitoring should support an organization-wide view, tie into the system development life cycle, and provide ongoing visibility into assets, threats, vulnerabilities, and control effectiveness. In practice, that means the system must handle more systems, more data, more users, and more control evidence without losing reliability or slowing response times. (NIST Publications)
It also means the system should absorb new regulations, added business units, and broader technical environments without disrupting existing compliance work. Current federal guidance on continuous diagnostics and monitoring similarly stresses enterprise-wide visibility across assets, users, and activities, which reflects the same need for scalable oversight as organizations expand. (bidenwhitehouse.archives.gov)
7. Compliance Policies and Procedures
A strong compliance monitoring program starts with clearly defined policies and procedures. These documents explain how compliance is maintained in day-to-day operations, set expectations for control owners and employees, and give the organization a consistent basis for monitoring, escalation, and corrective action. Current guidance from HHS OIG includes written policies and procedures among the core elements of an effective compliance program, and DOJ guidance continues to treat policies and procedures as a central part of a well-designed program. (HHS Inspector General)
To stay effective, those policies and procedures should be clear, accessible, and reviewed regularly as regulations, systems, and business operations change. NIST’s continuous monitoring guidance also stresses that monitoring strategies and supporting processes should be reviewed and updated over time so the program stays aligned with current risk and operating conditions. (NIST Publications)
8. Auditing
Regular auditing is essential for verifying whether compliance policies and procedures are actually working in practice. Audits help organizations detect gaps, inconsistencies, and weak control performance, creating clear opportunities for corrective action and continuous improvement. Current guidance from the U.S. Department of Justice treats testing, monitoring, and auditing as core indicators of an effective compliance program, while HHS OIG continues to include internal auditing as a basic element of compliance oversight.
Effective auditing usually combines scheduled reviews with targeted follow-up when risk indicators, process changes, or prior findings suggest closer scrutiny is needed. NIST’s continuous monitoring guidance also calls for organizations to analyze and report assessment and monitoring results on an ongoing basis so they can confirm adherence to internal standards and external requirements and improve the program over time. This disciplined approach reinforces compliance and shows a sustained commitment to operational integrity.
Challenges in Implementing Compliance Monitoring
Implementing compliance monitoring effectively is difficult because organizations must keep policies, controls, evidence collection, and accountability aligned as systems, regulations, and business operations change. NIST states that continuous monitoring requires ongoing awareness of assets, threats, vulnerabilities, and control effectiveness, while DOJ and HHS OIG guidance emphasize periodic testing, clear ownership, written procedures, and continuous improvement as core parts of an effective compliance program. These demands make implementation challenging, especially when monitoring must work across multiple teams, technologies, and regulatory requirements without disrupting daily operations.
Here are some of the most common challenges businesses face when setting up a compliance monitoring system:
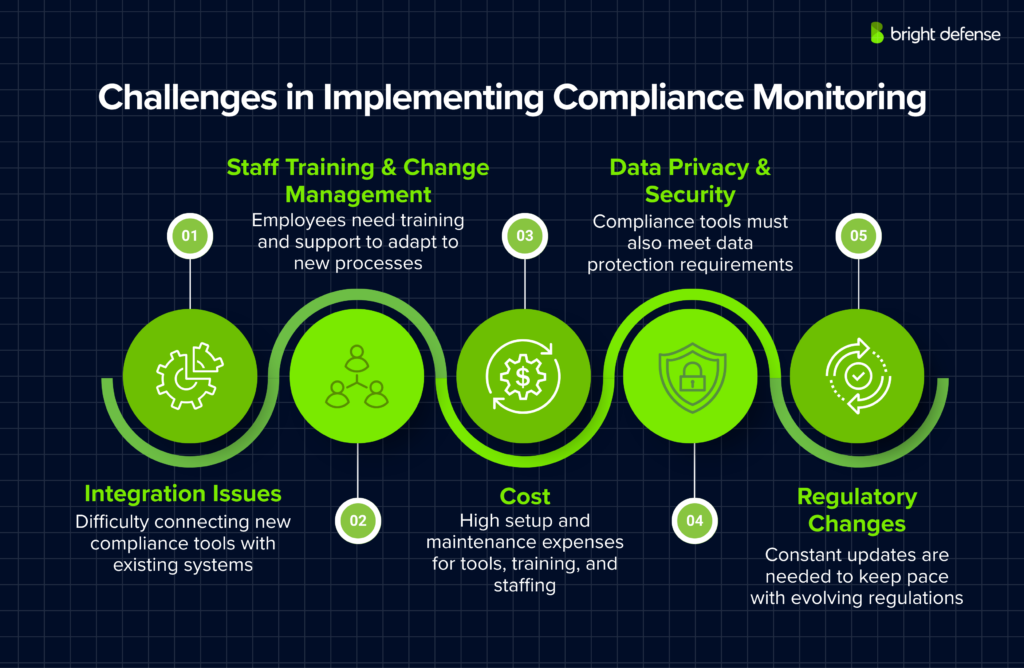
1. Technological Integration Issues
One of the main challenges in compliance monitoring is integrating new tools with existing systems. Many organizations already rely on a mix of platforms for identity, cloud operations, asset management, ticketing, and security controls, so new monitoring technology must fit into that environment without disrupting day-to-day work. NIST says continuous monitoring should support an organization-wide view and integrate with the system development life cycle, while CISA’s CDM program is built around cybersecurity tools, integration services, and dashboards, which shows how central system integration has become. (nvlpubs.nist.gov) (cisa.gov)
Getting these systems to work together usually requires careful planning, data mapping, workflow design, and, in some cases, changes to existing infrastructure. Without that work, monitoring can become fragmented, evidence can remain scattered across systems, and teams can lose the unified visibility that continuous compliance depends on. (nvlpubs.nist.gov)
2. Staff Training and Change Management
Implementing a new compliance monitoring system is as much about managing people as it is about managing technology. Employees need to be trained not only on how to use new tools, but also on why compliance monitoring matters, what their responsibilities are, and when issues should be escalated. The U.S. Department of Justice says a well-designed compliance program includes appropriately tailored training and communications, and HHS OIG lists training and education as a core element of an effective compliance program.
Change management also matters. NIST’s continuous monitoring guidance stresses defined roles, responsibilities, and regular updates to the monitoring strategy as risks, systems, and operations change. That makes transition planning essential, especially in organizations that are still heavily tied to older processes and traditional compliance habits.
3. Cost Considerations
The initial cost of setting up a strong compliance monitoring program can be significant. Common expenses include software, system integration, employee training, and, in some cases, added internal staff or outside consultants. NIST notes that continuous monitoring programs should use automation where possible, but that automation still has to be implemented, connected to existing systems, and maintained over time. (NIST Publications)
Businesses should look beyond the upfront cost and weigh the long-term value. Manual compliance work is already expensive in practice: in RegScale’s 2026 State of Continuous Controls Monitoring report, 83% of organizations reported moderate or major delays from manual compliance work, and 53% said evidence collection alone consumes the equivalent of one full-time employee. That is why companies should compare initial spending against the longer-term benefits of better audit readiness, faster issue detection, and lower manual workload. (businesswire.com)
4. Data Privacy and Security
With greater data collection and monitoring comes greater responsibility for data privacy and security. Compliance monitoring systems often process sensitive operational, employee, customer, or health-related information, so the systems themselves must follow the same protection rules the organization is trying to monitor. Under the GDPR, organizations must follow principles such as data minimization and integrity and confidentiality, apply data protection by design and by default, and use appropriate technical and organizational security measures. Under the HIPAA Security Rule, covered entities and business associates must protect electronic protected health information through administrative, physical, and technical safeguards. That means compliance monitoring tools need strong access controls, secure handling of sensitive data, and governance practices that match the regulatory environment they operate in.
5. Keeping Up with Regulatory Changes
The regulatory landscape changes constantly, and keeping a compliance monitoring system current can be difficult. Organizations need to update controls, policies, workflows, and evidence practices as laws, standards, and risk expectations change. The U.S. Department of Justice specifically asks whether a company’s risk assessment is current, whether reviews rely on continuous access to operational data, and whether those reviews lead to updates in policies, procedures, and controls.
That ongoing maintenance can be resource-intensive and usually requires steady attention from compliance, security, legal, and IT teams. NIST’s continuous monitoring guidance also states that the monitoring strategy should be reviewed regularly for relevance and accuracy so organizations can respond to risk in a timely manner.
Overcoming These Challenges
Organizations can address these challenges with a practical, structured approach that makes compliance monitoring easier to run and easier to maintain over time. NIST’s continuous monitoring guidance calls for a defined strategy, clear responsibilities, ongoing analysis and reporting, response to findings, and regular review and updates to the program. DOJ and HHS OIG guidance also stress written policies, training, testing, auditing, and corrective action as core parts of an effective compliance program.
- Invest in scalable solutions: Choose monitoring tools that can grow with the organization and integrate with existing systems, workflows, and reporting needs. NIST ties effective continuous monitoring to organization-wide visibility and regular program updates as systems and risks change.
- Prioritize training and support: Build training and support into the rollout so employees understand both how to use the system and why the monitoring process matters. DOJ and HHS OIG both treat training and education as core parts of an effective compliance program.
- Plan financially: Budget for both setup and ongoing operating costs, including software, integration work, internal time, and program maintenance. That cost should be weighed against the long-term value of stronger oversight, fewer manual gaps, and faster corrective action.
- Strengthen security controls: Apply strong internal controls, written procedures, and regular updates to protect the data handled inside the monitoring system itself. DOJ’s current compliance guidance states that internal controls and written policies should identify, escalate, and report risky activity and reduce known risks.
- Stay informed: Review the monitoring strategy regularly and update it as regulations, risks, and business operations change. NIST explicitly calls for organizations to review and update the monitoring strategy and program over time.
What are Three Techniques for Monitoring Compliance?
Most effective compliance programs rely on three core techniques: internal audit and formal reviews, automated monitoring and tools, and self-assessments with control checks. HHS OIG includes auditing and monitoring among the core elements of an effective compliance program, DOJ guidance emphasizes ongoing monitoring and control testing, and NIST describes continuous monitoring as ongoing awareness of control effectiveness and risk.
- Internal audit and formal reviews: Conduct audits and targeted reviews to check whether business processes follow compliance rules, industry standards, and regulatory requirements, and to assess current compliance status. HHS OIG and DOJ both treat auditing, monitoring, and testing as central compliance activities.
- Automated monitoring and tools: Use compliance monitoring software and automated control checks to track policies, security settings, evidence, and control performance across systems on an ongoing basis. NIST states that continuous monitoring should use automation where possible to support timely awareness of vulnerabilities, threats, and control performance.
- Self-assessments and control checks: Conduct regular reviews by control owners and the compliance team to confirm controls are working as intended, document evidence, and flag issues early. DOJ guidance asks whether companies test controls and whether compliance personnel have access to the operational data needed for effective monitoring, while NIST ties ongoing assessment and reporting to timely risk decisions.
Together, these techniques help compliance programs prevent, detect, and correct issues before they grow into larger legal, financial, or operational problems..
Essential Tools for Effective Compliance Monitoring
In the realm of regulatory compliance, leveraging the right tools can significantly streamline processes, enhance security, and ensure continuous adherence to standards. Organizations across industries can benefit from a diverse array of tools designed to automate compliance tasks, manage user identities, train employees, and more. Below, we explore some of the key categories and specific tools that help businesses maintain robust compliance systems.
1. Compliance Automation Tools
These tools are designed to reduce the complexity of achieving and maintaining compliance by automating continuous monitoring, evidence collection, and audit workflows.
Drata: Drata’s compliance platform automates evidence collection and monitoring for frameworks such as SOC 2, ISO 27001, and HIPAA. It says it can connect to 300+ systems or custom APIs to centralize workflows, surface control issues proactively, and give teams a real-time view of compliance status.
Vanta: Vanta focuses on security and compliance automation, with continuous monitoring, automated evidence collection, and support for frameworks such as SOC 2, ISO 27001, HIPAA, and GDPR. Vanta says it uses 400+ integrations for HIPAA evidence collection and supports 35+ security and privacy frameworks.
Secureframe: Secureframe helps organizations obtain and maintain compliance with frameworks such as SOC 2, ISO 27001, HIPAA, and PCI DSS. Its platform includes continuous daily monitoring with alerts for failing tests, automated evidence collection, and 100+ integrations mapped to compliance controls and requirements.
2. Identity and Access Management (IAM) Tools
Effective management of user access is critical for maintaining the security and integrity of data systems, and it plays a central role in compliance. IAM tools help organizations control authentication, access rights, lifecycle changes, and policy enforcement across users, devices, and applications.
- JumpCloud: JumpCloud offers an open directory platform that helps organizations manage identities, devices, and access from a single system. Its platform supports SSO, MFA, device management, and conditional access, which can help strengthen access control and support compliance efforts across distributed environments.
- Okta: Okta provides identity and access management tools for workforce and customer environments, including single sign-on, multi-factor authentication, lifecycle management, and identity governance. These capabilities help organizations manage secure and policy-based access across applications and systems, which supports broader compliance and security requirements.
3. Security Awareness Training Automation Platforms
Educating employees on security best practices is an important part of a broader compliance strategy. Security awareness platforms help automate that work through recurring training, phishing simulations, assessments, and reporting, which makes employee education easier to maintain over time.
- KnowBe4: KnowBe4’s Security Awareness Training platform combines automated training management with simulated phishing, AI-driven recommendations, and reporting. The company says its content library is available in 35 languages, and its platform is built to automate administration of awareness programs and related workstreams.
- Proofpoint Security Awareness Training: Proofpoint’s Security Awareness Training platform helps organizations identify high-risk users, measure human risk, and run behavior-based training programs. Its tools also include phishing simulations, tests, and assessments designed to help organizations automate targeted training and measure how employee awareness improves over time.
4. Security Information and Event Management (SIEM) Tools
SIEM tools play an important role in continuous security monitoring, incident detection, and compliance reporting. They help organizations collect, correlate, and analyze security data across systems so teams can detect threats faster and maintain stronger oversight of security controls.
- Splunk: Splunk offers SIEM and broader security operations capabilities through Splunk Enterprise Security and its compliance solutions. Splunk says its platform provides real-time posture and insights across IT resources and security controls, along with automated compliance tasks and customized reporting to support audits and security monitoring.
- IBM QRadar: IBM QRadar SIEM helps organizations centralize security visibility, support real-time threat detection, and streamline compliance workflows. IBM also states that QRadar supports compliance efforts through near-real-time threat detection, security analytics, and more than 700 supported integrations and partner extensions.
5. GRC (Governance, Risk, and Compliance) Platforms
These platforms provide a broader approach to governance, risk, and compliance by helping organizations manage policies, controls, audits, risks, and regulatory obligations in one connected environment.
- MetricStream: MetricStream offers Connected GRC and BusinessGRC solutions designed to bring together risk, compliance, audit, cyber risk, and third-party management. The company says its platform supports integrations with regulatory content, compliance data, threat intelligence, and third-party risk information, giving organizations a more unified view of governance and compliance activity.
- RSA Archer: Archer provides a single, configurable platform for integrated risk management across internal functions and third-party ecosystems. Archer says its platform supports automated compliance monitoring, risk quantification, and integrated risk and compliance workflows, while its compliance solutions are built to improve visibility into risk and compliance data and support more consistent oversight across frameworks.
6. Data Protection and Privacy Management Tools
These tools help organizations manage privacy obligations, reduce data protection risk, and maintain stronger control over sensitive information across systems, workflows, and third parties.
- OneTrust: OneTrust says its platform helps companies manage privacy, consent, and AI governance while automating compliance and reducing risk. Its privacy automation capabilities are positioned to support GDPR compliance and broader privacy management through assessments, data mapping, and rights-related workflows.
- TrustArc: TrustArc offers privacy management and data governance tools built for ongoing privacy operations and compliance. The company says its platform supports continuous compliance, end-to-end privacy management, and can automate up to 80% of privacy compliance and data risk management work.
Final Thoughts
Navigating the complexities of regulatory compliance requires more than adherence to rules. It demands a strategic integration of robust tools across the organization. Businesses can maintain a sustainable compliance posture by utilizing compliance automation tools, identity management systems, and security awareness training platforms.
The right tools streamline compliance processes, ensure continuous monitoring, and fortify the human element of security, creating a proactive environment where compliance is integrated into daily operations. As regulations evolve and complexities increase, adopting these sophisticated tools is essential for enhancing operational efficiency and maintaining stakeholder trust. This strategic approach mitigates risks and positions businesses for long-term success in an ever-changing regulatory landscape.
Bright Defense Delivers Continuous Compliance Monitoring!
If you are ready to implement continuous compliance, Bright Defense can help. Our monthly engagement model combines our vCISO expertise with compliance automation to help you meet frameworks like SOC 2, ISO 27001, HIPAA, PCI, CMMC, and more. We help you build the policies and procedures to meet your compliance requirements and work with you through the audit process and beyond.
FAQs
Compliance monitoring is the ongoing process of checking and verifying that an organization’s operations meet all relevant regulations and internal policies. It involves routine reviews or tests to ensure compliance and to identify any areas of non-compliance early.
In the context of AP Government, compliance monitoring refers to activities by bureaucratic agencies to ensure that companies or other regulated entities are following laws, regulations, and requirements as intended by public policy. It’s essentially the bureaucracy checking that those under its jurisdiction comply with external standards or rules.
Compliance monitoring is continuous, meaning it’s an ongoing activity, not a one-time check. It is dynamic, as it adjusts to regulatory changes and operational shifts. It is also collaborative, involving compliance officers, management, and employees working together. It is risk-focused, targeting high-risk areas for closer monitoring. It is technology-driven, using tools and software for real-time tracking and reporting.
A compliance monitoring report details the findings from compliance checks. It includes identified risks, compliance status, areas of non-compliance, and suggested actions to resolve issues. This helps organizations understand their compliance position and take necessary steps to improve it.
Internal monitoring involves continuous review of daily operations to spot and fix compliance risks as they arise. Compliance auditing is a formal, periodic evaluation to check if regulations are followed and to assess the effectiveness of the compliance monitoring system.
Compliance monitoring is important because it helps catch and correct issues early, ensuring the organization’s activities remain within legal and policy bounds. This proactive oversight protects the organization from legal penalties and reputational damage, improves operational performance by addressing gaps, and demonstrates accountability to regulators and stakeholders.
Monitoring and enforcing compliance with the HIPAA Security Rule is the responsibility of the U.S. Department of Health and Human Services’ Office for Civil Rights (OCR). This federal office oversees adherence to HIPAA’s requirements and can take action if entities fail to comply.
The Office of Laboratory Animal Welfare (OLAW) is the entity responsible for overseeing and monitoring institutional compliance with Public Health Service (PHS) policy.
Compliance monitoring introduces oversight and accountability for bureaucratic agencies, ensuring they implement policies as intended by lawmakers. However, this oversight can also pose a challenge to policy implementation by the bureaucracy, potentially slowing down or complicating an agency’s ability to carry out policies efficiently. In sum, it holds the bureaucracy accountable but may constrain how freely agencies can operate.
Compliance monitoring means maintaining continuous oversight of regulatory adherence, not one-time checks
Most organizations follow a repeatable compliance framework:
1. Define applicable laws, regulations, and regulatory environments
2. Perform risk assessment and assessing risk across systems and processes
3. Assign ownership within the compliance team and allocate sufficient resources
4. Run monitoring plans using audits, tools, and automated compliance solutions
5. Conducting audits and tracking findings through compliance reporting
6. Address gaps through corrective actions and compliance initiatives
7. Review results to support proactive risk management and prioritizing compliance
The focus is on continuous oversight rather than annual spot checks.
Compliance monitoring focuses on risk reduction, visibility, and accountability.
Key objectives include:
– Reducing legal and financial risks linked to regulatory breaches
– Safeguard sensitive data and support strong data security controls
– Detect gaps early through proactive risk management
– Support effective risk management across changing regulations
– Maintain clear documentation for audits and regulators
– Strengthen compliance training and employee training outcomes
– Improve coordination across compliance efforts and compliance programs
– Prevent severe consequences such as fines, enforcement actions, or business disruption
Well-run compliance monitoring activities help organizations stay prepared, consistent, and audit-ready as regulations evolve.
Compliance monitoring systems are structured tools or platforms used to manage ongoing compliance monitoring activities.
An effective compliance monitoring system typically supports:
– Central tracking of compliance rules and industry standards
– Mapping regulations to business processes and controls
– Risk assessment and risk evaluation tied to each requirement
– Automated reporting and compliance reporting workflows
– Evidence collection to support internal audit and external reviews
– Visibility into current compliance status across teams
These systems help compliance programs operate continuously rather than relying on manual checks.
The goal is operational visibility, controlled change, and fast response when evidence shows controls are not working as intended
A one-time audit provides point-in-time assurance, while monitoring runs continuously or on a defined cadence so issues surface sooner than annual reviews
Common activities include reviewing access and privilege changes, tracking configuration and patch status, checking logging coverage, validating backups and recovery, reviewing vendor and tool changes, and recording evidence that controls operated during the period
Monitoring frequency should match risk, with higher-risk systems checked more often and lower-risk areas checked on a slower cadence that still supports risk-based decisions
Start with accounts and admin access changes, MFA coverage for key accounts, critical system patch status, backup success plus restore testing, and security alert review because these areas commonly decide whether an incident stays small or becomes expensive
18. Do I need compliance monitoring if I am not legally regulated?
Yes, monitoring still helps because customer security reviews and common assurance approaches focus on whether controls actually operate over time, not only whether they exist on paper
19. What should I do when monitoring shows a control failure?
Record what failed and when, contain immediate risk if needed, fix the root cause, retest the control, and keep the evidence trail so you can explain the incident and the corrective action later
20. What is a simple way to start a compliance monitoring program?
Define the control set and owners, decide what evidence proves each control works, set a review cadence, automate collection where possible, and track exceptions through a ticketed process until closure
21. What are the 3 C’s of compliance?
There is no single official set of the “3 C’s of compliance.” Major U.S. guidance centers on DOJ’s three fundamental questions and OIG’s seven elements, while industry sources use different informal versions of the phrase, which is why it is better treated as shorthand than as a formal standard.
22. What are the 7 pillars of compliance?
The 7 pillars of compliance usually mean the seven elements of an effective compliance program: written policies and standards, a compliance officer or oversight, training and education, open communication, internal monitoring and auditing, disciplinary standards, and corrective action after problems are found.
References
- PricewaterhouseCoopers (PwC). (2025). PwC’s Global Compliance Survey 2025 (report). PwC.
- A-LIGN. (2025, January 28). A-LIGN releases fifth annual Compliance Benchmark Report (press release / article). A-LIGN.
- IBM Security & Ponemon Institute. (2025). Cost of a Data Breach Report 2025: The AI Oversight Gap (report). IBM. Public copy.
- Ponemon Institute & GlobalSCAPE. (2017). The True Cost of Compliance with Data Protection Regulations(research report). GlobalSCAPE (now Fortra).
Get In Touch