Penetration Testing Pricing for 2026
One of the key practices in testing an organization’s security posture is to perform regular penetration testing. Organizations use these tests to simulate real-world attacks and uncover security gaps before malicious actors can exploit them.
In fact, the global penetration testing market was valued at $2.74 billion in 2025 and is projected to grow to $7.41 billion by 2034, according to Fortune Business Insights.
In this blog, we’ll take a close look at how much penetration testing may cost. We’ll cover the factors that influence pricing, the different types of tests, and what organizations should expect when budgeting for penetration testing services.
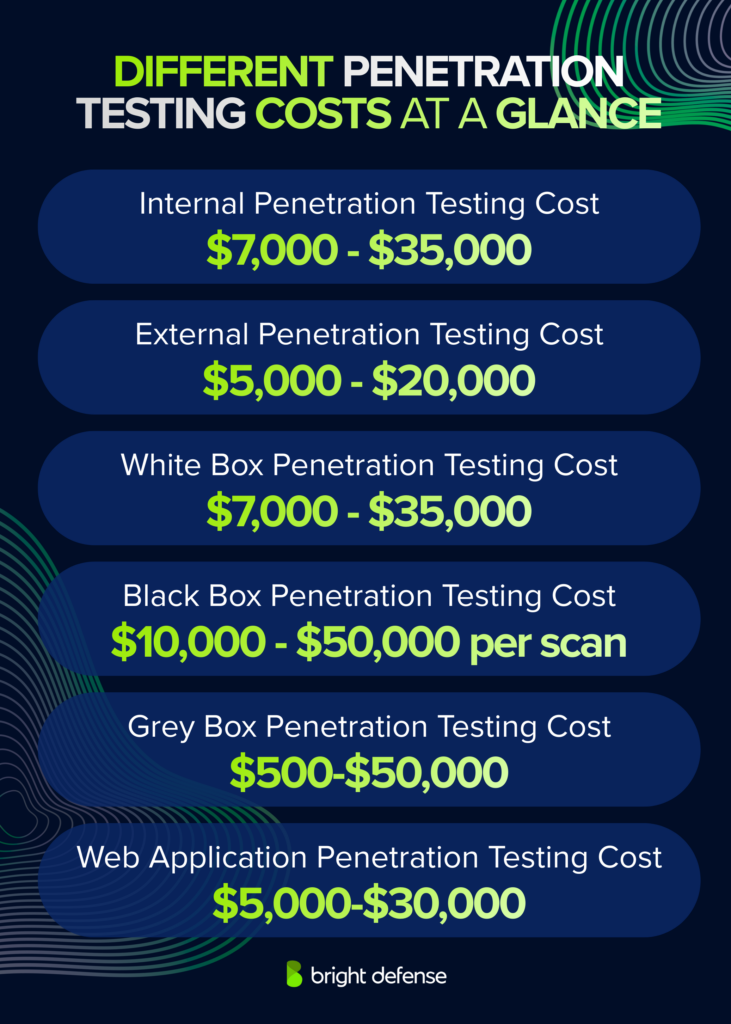
DIfferent Penetration Testing Costs At a Glance
- On average, businesses spend between $5,000 and $40,000+ depending on the type, scope, and complexity of the penetration test.
- Internal Penetration Testing Cost: $7,000 – $35,000
- External Penetration Testing Cost: $5,000 – $20,000
- White Box Penetration Testing Cost: $500 – $2,000 per scan
- Black Box Penetration Testing Cost: $10,000 – $50,000 per scan
- Grey Box Penetration Testing Cost: $500 – $50,000
- Web Application Penetration Testing Cost: $5,000 – $30,000
While these reflect typical market rates, Bright Defense offers penetration testing plans at significantly lower cost without compromising on quality. See below for our pricing:
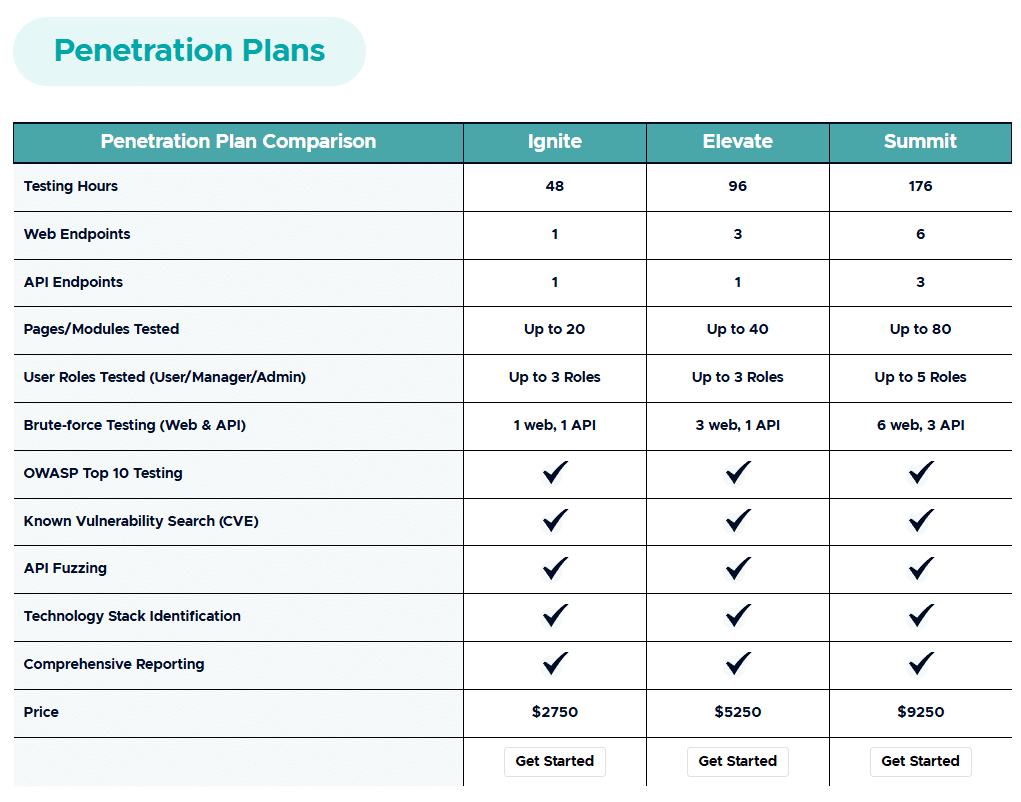
Bright Defense Penetration Testing Pricing
Checking Out the Various Types of Penetration Testing and their Costs
Penetration testing, often called pen testing, encompasses various types, each designed to evaluate different aspects of an organization’s security posture. The main types of penetration tests include:
Pen Testing Types and Pricing Table
| Penetration Test Type | Description | Typical Cost Range (USD) |
|---|---|---|
| Internal Penetration Test | Simulates insider threats or external attackers who have gained internal access. Tests weak passwords, unpatched systems, misconfigurations. | $7,000 – $35,000 |
| External Penetration Test | Simulates attacks from external actors. Targets public-facing assets like websites, services, and ports to identify entry points. | $5,000 – $20,000 |
| White Box Penetration Testing | Full access test with internal knowledge including source code and architecture. Deep, thorough audit for hidden vulnerabilities. | $500 – $2,000 per scan |
| Black Box Penetration Testing | No prior knowledge provided. Mimics real-world external hacker behavior. Focus on probing external weaknesses. | $10,000 – $50,000 per scan |
| Grey Box Penetration Testing | Partial system knowledge provided. Mimics a semi-informed attacker with limited access. Balances insight and realism. | $500 – $50,000 |
| Web Application Penetration Testing | Focuses on security of web apps. Identifies issues like XSS, SQL injection, and broken authentication. | $5,000 – $20,000 |
1. Internal Penetration Test
Internal penetration testing often costs between $7,000 and $35,000, although smaller single-site internal network tests can start around $4,000 to $7,000, while broader multi-site environments may run $8,000 to $15,000+ depending on scope and complexity.
Internal penetration testing simulates attacks that could occur after an attacker gains access to internal systems, whether through a malicious insider or stolen credentials used to bypass perimeter defenses. Testers attempt to find how far an attacker could move inside the environment, what sensitive data they could reach, and which internal weaknesses could be exploited, as described in IBM’s overview of network penetration testing.
The price depends on network size, the number of systems and segments in scope, Active Directory complexity, and the overall number and complexity of the testing targets. Larger organizations with broader internal environments usually fall on the higher end of the range, which aligns with current pricing factors described by Compass IT Compliance.
2. External Penetration Test
External penetration testing often costs between $5,000 and $20,000.
External penetration testing evaluates an organization’s perimeter security by targeting internet-facing assets such as servers, routers, websites, and employee computers. Testers act like outside attackers, looking for exposed services, weak perimeter defenses, and vulnerable public-facing systems.
Costs vary based on the number of external assets, the complexity of the environment, and the depth of testing required. A smaller test focused on a limited public-facing footprint will usually cost less than a broader engagement covering multiple IPs, applications, VPN gateways, and other internet-exposed services.
3. White Box Penetration Testing
White box penetration testing often starts at $7,000+.
White box testing gives testers full access to the system, including source code, credentials, network diagrams, and architecture documentation. With that level of access, testers can examine the environment more thoroughly and uncover deeper vulnerabilities that are harder to spot in black box or gray box engagements.
Because this method involves more visibility and a more exhaustive review, it is often more time-consuming and more expensive than more limited testing approaches. Costs can rise further when the scope includes multiple applications, detailed code review, or complex infrastructure.
4. Black Box Penetration Testing
Black box penetration testing generally starts around $5,000 and many professional engagements fall within a broader range of $10,000 to $35,000, while larger or more complex projects can exceed $100,000.
Black box testing simulates a real-world attacker with no prior knowledge of the system. Testers rely on publicly available information to gather intelligence, map the environment, and find entry points without any internal data.
Costs vary based on the number of external assets, the complexity of the environment, and how much reconnaissance, validation, and exploitation work the scope requires. Broader internet-facing environments usually cost more than a narrow test with clearly defined targets.

5. Grey Box Penetration Testing
Grey box penetration testing often costs between $7,000 and $40,000+.
Grey box testing gives testers partial knowledge of the system. They may receive limited credentials, documentation, or access, which simulates an attacker with insider assistance or stolen credentials. (IBM)
Pricing for grey box testing varies depending on how much access is granted, the number of systems in scope, and the overall complexity of the environment. The hybrid nature of this method makes it flexible for many testing scenarios, which is one reason the final cost can vary so widely. (Scytale)

6. Web Application Penetration Testing
The average penetration testing cost for web apps ranges between $5,000 and $30,000.
Web application penetration testing focuses entirely on web-based systems. Testers evaluate business logic, input validation, authentication, and session management vulnerabilities.
Pricing depends on the complexity of the application, the number of user roles, and the depth of testing. A simple app with fewer pages may fall at the lower end, while more complex platforms with multiple integrations and sensitive data handling can push costs higher.

Factors Influencing the Cost of Penetration Testing
Several critical factors influence the cost of a penetration test. Understanding these elements helps organizations budget effectively for their cybersecurity needs. Let’s check them out:
1. Scope and Complexity
The scope of a penetration test directly affects its cost. Testing a single web application is usually less expensive than assessing an entire corporate environment. Larger scopes require more time, more validation work, and more resources. Current public pricing guidance shows that a penetration test can start at around $5,000 and rise well beyond $40,000+ as the scope expands.
Complexity also plays a role. Environments with diverse technologies, legacy systems, custom applications, or intricate network architectures usually require more specialized skills and more testing time, which raises the cost. Vendors that publish current pricing guidance consistently list scope, size, and technical complexity among the main drivers of penetration testing fees.
Example: A basic web application assessment may cost around $5,000 to $15,000, while a large enterprise engagement covering multiple applications, cloud assets, and internal or external infrastructure can exceed $100,000. Complexity matters as well. A simpler tech stack is faster and easier to test, but an environment with legacy systems, multiple platforms, and custom applications usually demands more expertise and more time, which drives up the price.
2. Expertise and Qualifications of the Penetration Tester
The skill level and certifications of the penetration tester affect pricing. Highly experienced professionals with credentials such as OSCP, CISSP, or CREST CRT usually charge more because they bring stronger technical depth and recognized expertise. The CISSP also requires at least 5 years of cumulative paid work experience, which helps explain why more senior testers often come at a higher rate.
Example: A junior tester may charge less, but a senior tester with certifications such as OSCP, CISSP, or CREST and strong experience in application or network security will usually charge more. Public pricing guidance from current penetration testing firms places many reputable providers around $200 to $300 per hour, while skilled or senior testers often fall in the $250 to $500 per hour range. Those higher rates often reflect deeper testing ability, better validation, and fewer security blind spots.
3. Duration
The length of a penetration test influences the price. Most penetration tests are completed in 1 to 3 weeks, although smaller scopes can take only a few days and larger environments can require several weeks. Longer engagements usually provide a more in-depth review of the organization’s security posture.
Longer durations generally cost more because they require more testing time, more validation, and more reporting. Traditional penetration tests commonly cost between $5,000 and $50,000+ per engagement, with pricing rising as scope and complexity increase.
Example: a small website assessment may cost around $5,000 to $15,000 and take roughly 1 to 2 weeks, while a large enterprise application can cost $50,000 to $100,000+ and take about 4 to 8 weeks.
4. Tools and Technology
The sophistication and type of tools used can affect pricing. Commercial platforms, advanced testing suites, and custom tooling all add cost, especially when a test requires more manual validation or deeper coverage. For example, Burp Suite Professional is priced at $499 per user for a 1-year subscription, and penetration tests are commonly priced at roughly $1,000 to $3,000 per day depending on tester seniority and project demands.
Example: A straightforward test that relies on standard tooling and a shorter engagement will usually cost less. If the tester needs advanced platforms, more manual analysis, or custom scripts to assess proprietary systems, the price can climb because the work takes more time and usually calls for more experienced specialists. Current pricing guidance from penetration testing firms continues to list project scope, technical complexity, and tester experience as major cost drivers.
5. Manual vs. Automated Penetration Testing
Penetration tests can be manual or automated, or use a combination of both. Automated testing is usually less costly because tools can scan systems quickly and repeatedly with less hands-on effort, but manual assessment is often needed to find business logic errors, race conditions, and certain zero-day vulnerabilities that automated tools may miss. NIST also notes that security testing techniques may be performed manually or with automated tools, and that no one technique provides a complete picture of a system’s security.
Example: Automated tools are faster and usually cheaper for broad coverage and repeatable checks, while manual testing is slower and more expensive but better at mimicking real-world attacks and validating complex flaws. A hybrid approach is common because it balances cost, speed, and testing depth.
6. Legal and Compliance Considerations
Adhering to legal and regulatory standards can add to the cost of a penetration test. Compliance with laws and frameworks such as GDPR Article 32, which requires organizations to regularly test and evaluate security measures, and PCI DSS, which includes regular security testing requirements, often calls for additional expertise, more detailed documentation, and more reporting work. In healthcare, the HHS proposed update to the HIPAA Security Rule would require vulnerability scanning at least every 6 months and penetration testing at least once every 12 months. Specific industry requirements may also call for more specialized testing procedures, which can raise the total cost.
Example: A basic web application penetration test may cost around $5,000 to $15,000, while HIPAA-focused penetration testing is often listed around $10,000 to $50,000. That higher range usually reflects added scoping, documentation, and compliance-related reporting in regulated environments.
7. Remediation and Retesting Support
Many penetration testing engagements include support for remediation and retesting. This phase helps confirm that identified vulnerabilities have been fixed and that the fixes did not introduce new issues. Some providers include remediation guidance and one follow-up retest in the original engagement, while others price that work separately.
Remediation support usually involves detailed guidance to help your team address the issues found during testing. Retesting then verifies that the corrective actions worked as intended. Current public pricing guidance notes that standalone retests can cost around $2,000 to $5,000, although some contracts include one retest at no extra charge.
Example: A company might pay around $20,000 for a mid-range penetration test, then another $2,000 to $5,000 for a standalone retest if that work is not included in the original scope. While this phase may be optional in some engagements, skipping it can leave important fixes unverified.
8. Vendor Reputation and Location
The reputation and location of the vendor performing the penetration test can significantly affect cost. Well-established vendors with a strong track record often charge more because they usually bring more experienced professionals, more mature methodologies, and stronger reporting processes. Public pricing guidance notes that vendor rates commonly vary based on reputation, certifications, and the level of tester experience.
The geographical location of the vendor can also play a role. Vendors in regions with higher labor and operating costs often charge more than those in lower-cost markets, although scope, complexity, and tester skill still remain major pricing drivers.
Example: A reputable penetration testing firm may quote around $1,000 to $3,000 per day, while reputable providers also commonly publish hourly rates around $250 to $300, with skilled specialists often billed at $250 to $500 per hour. Vendors in higher-cost regions may quote more for the same general scope, but the quality of the team and the depth of the assessment usually matter more than geography alone.
Pricing Models
Penetration testing services use several common pricing structures:
- Per-Hour vs. Per-Project: Some providers charge an hourly rate, with current public pricing guidance commonly placing qualified penetration testers at around $200 to $350 per hour, while other firms cite a more typical range of about $250 to $300 per hour.
- Retainer-Based Models: For recurring security testing, some vendors offer retainer-based or subscription-style models instead of one-off projects. Penetration Testing as a Service, or PTaaS, is now commonly positioned as an ongoing or on-demand model rather than a single annual engagement.
- Value-Based Pricing: Some providers price work based on the business value delivered, the risk reduced, or the importance of the assets being tested rather than billing only for hours or a fixed scope. Value-based pricing is a recognized pricing model built around the customer’s perceived value and expected outcomes.
- Bounty-Based: Larger organizations may also run bug bounty programs that pay security researchers based on the severity or impact of the vulnerability reported. Public program policies on HackerOne commonly describe rewards as being determined by severity.
Understanding Different Penetration Testing Pricing Models
Penetration testing is commonly priced through hourly billing, fixed-fee project work, retainer or PTaaS arrangements, value-based pricing, and bug bounty programs used as a supplemental security-testing model.
- Per-Hour vs. Per-Project: Some providers charge an hourly rate, while others use a fixed project fee for a clearly defined scope. Current public pricing guidance places typical hourly rates for reputable firms at about $200 to $350 per hour, and Blaze InfoSec notes that many providers still start around $200 to $300 per hour.
- Retainer-Based Models: A retainer model can be more economical for ongoing testing because it lets organizations buy a pool of pentest days or hours up front and use them over time. SecureLeap describes retainers as a bucket of testing time used over 12 months, and PTaaS providers such as NetSPI and Cobalt position this model as an ongoing program rather than a one-time engagement.
- Value-Based Pricing: Some providers base their pricing on the value they bring to your organization rather than charging only for time or scope. Salesforce defines value-based pricing as pricing based on the buyer’s perceived value of a product or service and the outcomes it delivers.
- Bounty-Based: Larger organizations may also run bug bounty programs that pay security researchers based on the severity or impact of the vulnerability reported. HackerOne describes bug bounty programs as rewarding ethical hackers for valid vulnerability reports, and many live programs state that rewards are tied to severity.
Each model has its own tradeoffs, and the right choice depends on your organization’s testing frequency, scope stability, and budget.
Other Types of Pen Tests
Other types of pen tests include:
1. Social Engineering Test
Social engineering testing focuses on the human element of security and measures how susceptible an organization’s personnel are to tactics such as phishing, pretexting, baiting, and tailgating. In this type of assessment, testers simulate deception-based attacks to see whether employees disclose sensitive information, grant improper access, or take unsafe actions that could lead to a broader compromise. NIST defines social engineering as an attempt to deceive an individual into revealing information or taking an action that can adversely affect a system, and it specifically lists phishing, pretexting, baiting, and tailgating among common techniques.
2. Physical Penetration Test
Physical security testing evaluates controls such as locks, sensors, cameras, badge readers, and access control systems to measure how well a facility can prevent unauthorized access. In this type of assessment, a tester attempts to bypass physical barriers and gain entry to restricted areas, equipment, or systems in order to confirm whether physical security weaknesses could lead to a broader compromise. NIST describes physical security testing as an effort to confirm vulnerabilities by attempting to circumvent locks, badge readers, and other physical security controls, typically to gain unauthorized access to specific hosts.
3. Wireless Penetration Test
Wireless penetration testing focuses on technologies such as Wi-Fi, Bluetooth, NFC, and other wireless communication systems to identify weaknesses in encryption, authentication, protocol configuration, and device exposure. In this type of assessment, testers analyze how wireless signals, access points, pairings, and connected devices could be abused to gain unauthorized access, intercept traffic, or exploit insecure protocols. NIST notes that wireless connections, including Bluetooth and NFC, are vulnerable to threats such as eavesdropping, injection, and relay attacks, while its wireless device security guidance also points to Wi-Fi, Bluetooth, cellular, and NFC as key protocols that require security evaluation.
4. Cloud Penetration Testing
Cloud penetration testing focuses on cloud infrastructure and services, assessing security weaknesses in IaaS, PaaS and SAAS environments. It typically examines configuration issues, identity and access controls, exposed services, storage permissions, network paths, and workload settings to determine whether misconfigurations or weak controls could lead to unauthorized access or data exposure. Because cloud security follows a shared responsibility model, the exact scope of a cloud penetration test depends on which parts of the environment the customer is responsible for securing.

Differences Between Penetration Testing and Vulnerability Scans
Understanding the differences between a penetration test and a vulnerability scan is crucial, especially when considering penetration testing costs and the overall cybersecurity strategy of an organization.
| Category | Penetration Testing | Vulnerability Scanning |
|---|---|---|
| Scope and Depth | In-depth, simulates real-world attacks to exploit weaknesses. | Surface-level, automated scan to find known vulnerabilities. |
| Methodology | Manual, performed by skilled testers mimicking real attackers. | Automated, software-driven scanning. |
| Cost Implications | Higher cost due to complexity, manual effort, and expertise. | Lower cost, efficient way to find common weaknesses. |
| Frequency and Use | Performed occasionally, often during major security reviews or system changes. | Conducted frequently as part of ongoing security maintenance. |
| Outcome and Reporting | Delivers detailed reports, exploited paths, and actionable remediation advice. | Provides a list |
1. Scope and Depth
Most penetration tests are more comprehensive and are designed to simulate real-world attacks to determine whether security weaknesses can actually be exploited. NIST explains that penetration testing typically builds on discovery activities such as network and service identification and vulnerability scanning, then goes further through controlled attack attempts to validate exposure and test resilience.
In contrast, a vulnerability scan is more automated and surface-level, with the main goal of identifying known vulnerabilities in systems and software rather than simulating a full attacker workflow. NIST specifically states that penetration testing goes beyond automated vulnerability scanning, which is why penetration tests usually provide deeper insight than scanning alone.
2. Methodology
Penetration tests are often manual and require a skilled tester to think creatively, mimicking the actions of a potential attacker. This can include exploiting weaknesses, chaining issues together, bypassing security controls, and attempting to gain unauthorized access to confirm real-world impact. NIST explains that penetration testing goes beyond discovery and scanning by using controlled attack techniques to validate whether vulnerabilities can actually be exploited.
Vulnerability scans, however, are mostly automated and rely on software to examine systems and networks for known vulnerabilities. OWASP describes vulnerability scanners as automated tools that look for security weaknesses, while NIST notes that automated scanning alone does not provide the same depth as penetration testing.
3. Cost Implications
Penetration testing is often manual and requires a skilled tester to think creatively, mimicking the actions of a potential attacker. That can include exploiting vulnerabilities, chaining weaknesses together, bypassing security controls, and attempting to gain unauthorized access to confirm real-world impact.
Vulnerability scans, however, are mostly automated and rely on software to scan systems and networks for known vulnerabilities. They are useful for broad, repeatable detection, but they do not provide the same depth as a full penetration test.
4. Frequency and Use
Vulnerability scans are typically performed more frequently, often as part of regular security maintenance. For example, PCI DSS requires internal and external vulnerability scans at least every 3 months and after significant changes.
Penetration tests, on the other hand, are conducted less frequently and are usually reserved for deeper security validation. PCI penetration testing guidance calls for penetration testing at least annually and after any significant change, which matches how many organizations schedule pen tests as part of broader security audits or after major changes to the IT environment.
5. Outcome and Reporting
Penetration tests usually produce detailed reports that document exploited vulnerabilities, explain their potential business and technical impact, and include recommendations for remediation.
Vulnerability scans generate a list of known vulnerabilities, often ranked by severity, but they do not usually include the detailed exploitation and impact analysis found in most penetration tests.
In summary, while both penetration tests and vulnerability scans are important parts of cybersecurity, they serve different purposes. Penetration tests provide a deeper, more manual assessment of security weaknesses through controlled exploitation and validation, which is one reason they usually cost more. Vulnerability scans provide a faster, more automated way to detect known weaknesses across systems and software, but they do not offer the same depth of analysis as a full penetration test.
Estimating Your Penetration Testing Budget
Budgeting for penetration testing varies widely. Small businesses and startups may spend around $4,000 to $12,000 for a smaller engagement, while a basic single web application test often starts around $5,000 and can run to $15,000 depending on scope. Larger corporate environments with broader internal, external, cloud, or application scope can exceed $100,000. It is important to assess your needs carefully and leave room for additional costs that may arise during testing, remediation, or retesting.
Here are some key cost drivers:
- Type of testing being performed: Internal, external, web application, wireless, cloud, and social engineering tests all vary in cost based on the skills, time, and depth of testing required.
- Number of assets being tested: Pricing usually increases with the number of systems in scope, such as web applications, APIs, hosts, domains, or IPv4 and IPv6 assets.
- Testing methodology: White box testing, where testers receive full access, often takes more time because it allows for deeper analysis. Grey box testing uses limited access and usually falls somewhere in the middle. Black box testing gives testers no internal knowledge and can require more reconnaissance before exploitation begins.
Focusing in Web Application Pen Testing Pricing
Key cost drivers in Web Application penetrating testing include:
- Number of web applications
- Number of user roles being tested
- Number of unique pages such as app.domain.com/* → all pages under the root app domain
- API testing
Tips for Choosing a Penetration Testing Service
When selecting a pen testing service, consider:
Provider’s expertise and reputation: Look for providers with proven experience in the kind of testing you need, a solid record of similar engagements, and a team with widely recognized certifications. Common credentials include CEH, OSCP or OSCP+, CREST certifications such as CRT and CCT, GPEN, LPT (Master), CISSP, and CompTIA PenTest+
Deliverables and reports: Make sure the provider supplies a detailed report that clearly explains validated findings, likely impact, evidence, and remediation recommendations. NIST describes security testing and assessment as a process that includes analyzing findings and developing mitigation strategies, which is why reporting quality matters as much as testing depth
ROI of services: Evaluate the price against the depth of testing, the clarity of the final report, the availability of remediation guidance or retesting, and the business value of finding exploitable weaknesses before an attacker does

The Role of Penetration Testing in Compliance
Penetration testing plays an important role in meeting many cybersecurity frameworks and standards. It helps organizations validate that security controls work as intended and identify weaknesses before attackers can exploit them. Frameworks and guidance such as PCI DSS, NIST SP 800-115, and the OWASP Web Security Testing Guide all recognize penetration testing as an important security assessment practice, and the HHS proposed update to the HIPAA Security Rule would require penetration testing at least once every 12 months. This makes penetration testing an important part of compliance readiness, risk reduction, and ongoing security assurance. (NIST CSRC)
- SOC 2 and ISO 27001: Penetration testing helps validate the technical controls that support a SOC 2 examination and an ISO/IEC 27001:2022 information security management system. SOC 2 examines controls relevant to security, availability, processing integrity, confidentiality, and privacy, while ISO/IEC 27001 defines the requirements for an ISMS built around ongoing risk management.
- CMMC and NIST: Penetration testing is especially relevant for contractors and organizations working within NIST-based security programs. The Department of Defense’s CMMC Level 2 is based on NIST SP 800-171 Rev. 2, and NIST SP 800-53 Rev. 5 control CA-8 defines penetration testing as a specialized assessment that goes beyond automated vulnerability scanning.
- HIPAA: Penetration testing helps identify security gaps that could expose electronic protected health information. HHS’s proposed update to the HIPAA Security Rule would require vulnerability scanning at least every 6 months and penetration testing at least once every 12 months.
Continuous compliance is now a practical necessity. Regular penetration testing supports ongoing control validation, helps organizations respond to changing threats, and strengthens long-term cybersecurity assurance across regulated and high-risk environments.
Final Thoughts
Understanding the pricing of penetration testing is crucial in making informed decisions for your cybersecurity needs. It’s a balance of cost and quality, ensuring your business is protected without overspending. Remember, the cheapest option may not always be the most effective, and the most expensive one may not be necessary for your specific needs.
Penetration Testing from Bright Defense!
If you are interested in penetration test for your organization, Bright Defense can help. Bright Defense offers penetration testing and vulnerability scanning services through our partnership with Red Sentry and Breachlock. Both firms offer comprehensive services and exceptional support, and 5 star ratings on G2.
Bright Defense mission is to protect our clients from cybersecurity threats through continuous compliance. Additionally, we offer services including continuous cybersecurity compliance, managed security awareness training, AI-enable phishing, and virual CISO (vCISO) services. We understand that penetration testing is a key component to meeting compliance standards.
If you are interested in a penetration test quote, contact our security team today.
FAQ
Penetration testing, or pen testing, is a simulated cyberattack against your computer system, network, or web application to identify vulnerabilities and security issues.
The cost of penetration testing can vary based on several factors, including the scope and complexity of the project, the expertise required, duration, tools and technology used, and legal and compliance considerations.
There are mainly three types:
1. Internal Pen Testing: Focuses on evaluating the security of internal networks and systems.
2. External Pen Testing: Concentrates on identifying and exploiting vulnerabilities in external-facing assets.
3. Web Application Pen Testing: Exclusively assesses the security of web applications.
Penetration testing services may offer various pricing models, such as per-hour or per-project rates, retainer-based models, value-based pricing, and bounty-based programs.
The cost can range from a few thousand dollars for small businesses to tens of thousands for larger corporations. It depends on the type of testing, number of assets, and testing methodology.
Yes, by identifying and addressing vulnerabilities proactively, penetration testing can prevent security breaches that might lead to significant financial and reputational damages.
Yes. Automated scans can identify common vulnerabilities, but manual testing by expert pen testers is critical for a more thorough and insightful assessment.
The duration varies based on the scope and complexity of the project. It can range from a few days to several weeks.
Yes, ensuring that penetration testing complies with relevant laws and regulations is crucial, as it can add layers of complexity and cost to the process.
Regular testing is recommended, especially when significant changes are made to your systems or applications, or at least annually.
Professional penetration testers typically conduct tests in a manner that minimizes disruption to normal business operations.
Success is measured by the thorough identification of vulnerabilities and the provision of actionable recommendations for strengthening your cybersecurity defenses.
Yes, there are cost-effective options available for small businesses, and considering the potential costs of a breach, it’s a worthwhile investment.
For more information about our services, visit our partnership pages with Red Sentry and Breachlock, which offer comprehensive services and exceptional support.
Get In Touch