Updated:
April 8, 2026
SOC 2 Requests From Enterprise Clients: What To Do Next
Enterprise customers demand SOC 2 as definitive proof that your product handles data securely.
Your ability to provide this documentation often determines whether a deal advances or stalls indefinitely in procurement.
For SaaS and SMB founders, SOC 2 has shifted from an optional advantage to a mandatory contract prerequisite.
This expectation reflects a clear market standard: 77% of businesses now report that stakeholders demand verified proof of compliance before moving forward.
This guide details exactly how to evaluate your current security posture, define your next steps, and achieve SOC 2 compliance without disrupting your sales momentum.
Key Takeaways
- SOC 2 is now a common requirement in enterprise sales
- Buyers use it as proof that your security controls are real
- Most enterprise customers prefer SOC 2 Type II
- Clear scope and organized evidence help deals move faster
- SOC 2 works best as an ongoing process, not a one-time project
What Enterprise Customers Usually Mean When They Ask For SOC 2
Your enterprise customers usually mean, “Show us independent proof that your security controls are mature enough for our vendor review, preferably in a current SOC 2 report that we can use in procurement, security, and compliance review.”
SOC 2 is a report that reviews controls related to security and other trust criteria. It is designed for users who need clear and detailed assurance about how those controls work. Google Cloud describes SOC 2 reports as third-party attestations that include testing of control design and operating effectiveness during the audit period.
A simple example makes this clearer. A bank wants to use your platform to store customer account data. As a regulated financial institution, the bank is required to verify that its third-party vendors protect sensitive data.
They request your SOC 2 report to confirm that only authorized users can access the data, that the data is encrypted, and that security processes are followed consistently. The report gives the bank independent evidence that their customers’ data is handled securely and the documentation they need to satisfy their own compliance obligations.
Why Do Enterprise Clients Request SOC 2 Reports?
Enterprise customers ask for SOC 2 because it gives them confidence, reduces uncertainty, and helps them manage vendor relationships in a safer and more structured way.
Here are broader reasons with clearer explanations:

1. SOC 2 Reduces Security Risk
Companies want to reduce the chance of costly security incidents, service disruptions, and data exposure when they rely on outside vendors.
That concern is growing because Verizon’s 2025 Data Breach Investigations Report found that third parties were involved in 30% of confirmed breaches, up from 15% the year before.
A SOC 2 report helps buyers screen vendors earlier and gives them more comfort that basic security controls are already in place.
2. SOC 2 Speeds Enterprise Vendor Selection
Companies trust vendors more when they can see clear proof that security practices and data protection standards are already in place. 46% of software buyers prioritize security certifications and data privacy practices when choosing a vendor.
That number shows that buyers place real value on visible proof of controls. A SOC 2 report helps build that trust because it gives buyers documented evidence that a vendor’s controls were formally reviewed.
3. SOC 2 Sets the Benchmark for Vendor Evaluation
Large organizations often evaluate many vendors at the same time, so they need a way to make decisions without spending months on deep technical reviews.
SOC 2 provides a ready-made overview of a vendor’s security posture, which helps teams move forward more quickly.
4. SOC 2 is a Standard Way Of Evaluating Vendors
Companies prefer to use a consistent method when reviewing vendors so that every option is judged fairly.
SOC 2 offers a common framework that allows different vendors to be evaluated against the same set of expectations.
5. SOC 2 Strengthens Internal And External Accountability
Teams responsible for choosing vendors must show that they made careful and informed decisions.
SOC 2 acts as documented proof that proper checks were completed, which helps justify decisions to leadership, auditors, and stakeholders.
6. SOC 2 Supports Regulatory And Business Expectations
Many industries expect organizations to assess the security of their vendors as part of normal business operations.
77% of organizations cite compliance with standards such as ISO 27001, NIST, and SOC 2 as their top requirement for third-party vendors.
SOC 2 helps companies meet these expectations and demonstrate that they take vendor risk seriously.
7. SOC 2 Simplifies Vendor Management
Managing multiple vendors becomes easier when there is a shared standard in place.
SOC 2 creates a common reference point that different teams can rely on when reviewing, onboarding, and monitoring vendors.
What To Do After A SOC 2 Request Comes In
The right approach after a SOC 2 request comes in is to follow a short, structured review process before sending any documents. Here are the steps you can follow:
1. Clarify What “SOC 2” Means In That Deal
Enterprise customers use “SOC 2” as a catch-all term. 65% of organizations say customers, investors, and suppliers now require more demonstration of compliance than in previous years, and that growing pressure takes different forms in every deal.
One buyer wants the SOC 2 Type II report, another wants a bridge letter, and another is really looking for trust center access or a completed security questionnaire.
Getting that point straight at the start avoids the most common mistake, which is sending a document that does not solve the customer’s actual review need.
2. Match the Request To the Right Scope and Time Period
A SOC 2 report does not cover an entire company in the abstract. It covers a defined system, service, environment, or legal entity over a specific audit period. That is why scope and timing matter so much.
A report can be current and still miss the product under review, or it can cover the right product and still feel stale because the audit window ended months ago. In those cases, a bridge letter or supporting explanation may matter just as much as the report itself.
3. Check the Sharing Path Before Anything Goes Out
SOC 2 reports are controlled documents, not general marketing assets. Some companies release them under NDA, some route them through a trust center, and some require an internal approval before the file is shared.
That part should be sorted out before anyone sends attachments around. A rushed release creates internal friction and can expose material more broadly than intended.
4. Send the Smallest Useful Package, Not Just a Random File
Revenue teams report that 52% of deals are delayed during SOC 2 security review, with an average delay of 3.1 weeks, which goes to show how often this stage slows deal progression.
SOC 2 reviews move faster when the materials match the customer’s evaluation process rather than sending a generic report alone.
Some buyers only need the SOC 2 report, while others expect a more complete package that includes a bridge letter, security FAQ, subprocessor list, or completed security questionnaire.
The goal is to send the smallest SOC 2 package that still answers the buyer’s requirements without creating unnecessary follow-up. Clear scope explanation improves review speed when the SOC 2 report applies to a specific product or environment, since stakeholders can quickly understand what systems and controls are in scope.
5. Be Ready For the Follow-Up Questions Right Away
The SOC 2 report usually opens the door rather than closing the review. Security teams often come back with questions about exceptions, encryption, access control, logging, incident response, vulnerability management, subprocessors, or business continuity.
Having those answers ready keeps the deal moving and shows that the company can handle enterprise diligence without turning every request into a long back-and-forth thread.
The first real job is qualification, and the rest of the process is controlled delivery. That is what keeps a simple SOC 2 request from turning into unnecessary back and forth.
What Is The Step-By-Step Roadmap To Achieving SOC 2 Compliance?
When an enterprise requests SOC 2 compliance, rushing to submit an incomplete report creates risk. A controlled approach focuses on planning, implementing required controls, and verifying that each requirement meets the Trust Services Criteria before submission.
This overview explains how to achieve SOC 2 compliance in a faster yet controlled manner through defined steps.
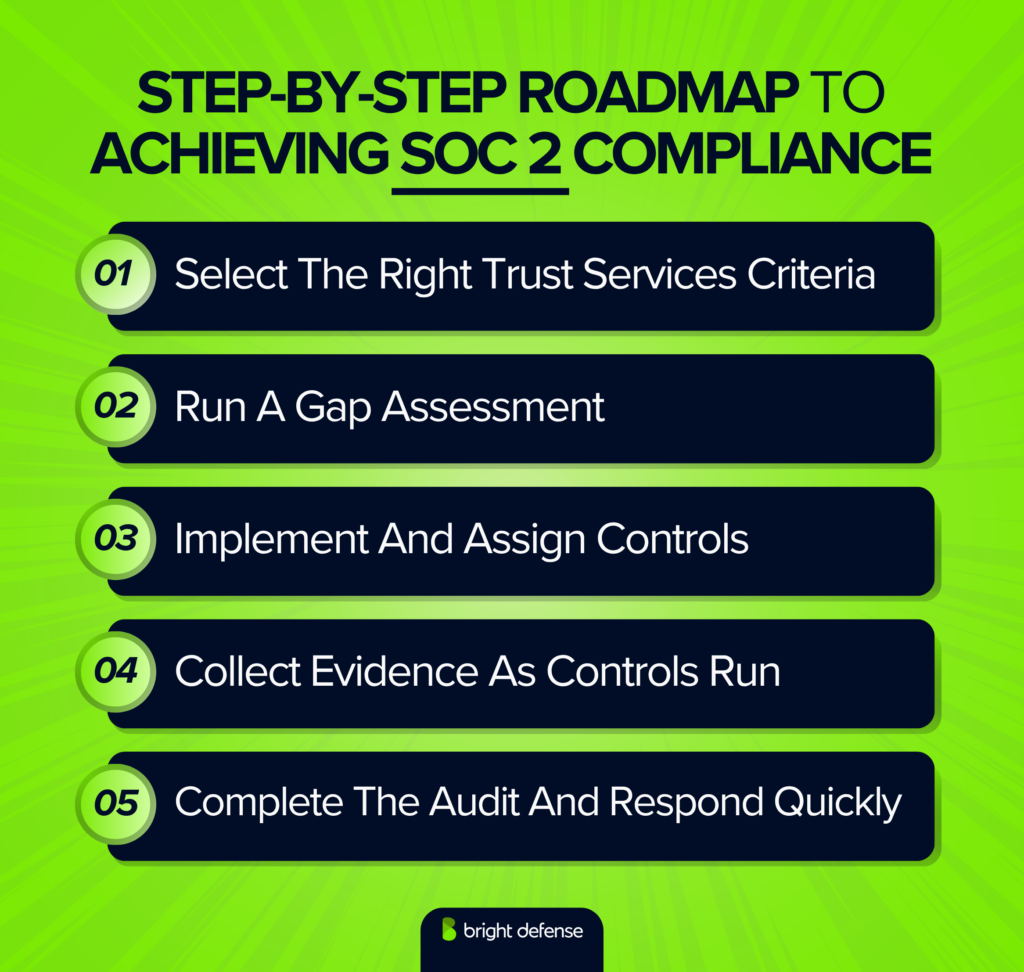
1. Select The Right Trust Services Criteria
The right Trust Services Criteria reflect how your product operates and what your enterprise customers expect from it. Security is always required in SOC 2. The remaining criteria should match your service design, data handling practices, and contractual commitments.
A platform centered on uptime may require Availability, which goes to show how common that expectation is, with 71% of SOC 2 reports including Availability alongside Security. A product handling sensitive data may require Confidentiality or Privacy.
The focus should remain on relevance. Adding unnecessary criteria increases audit scope without improving your position in enterprise reviews.
2. Run a Gap Assessment
A gap assessment reveals what enterprise customers will notice before an auditor does. First-time SOC 2 gap analyses show that 40 to 60% of control areas contain gaps, which goes to show how common early weaknesses are.
This step acts as a pressure test for your controls, policies, and documentation against real buyer expectations. Missing policies, weak access controls, limited documentation, or inconsistent vendor oversight can slow procurement and raise concerns.
Addressing these gaps early, on the other hand, gives your team time to fix issues before they become objections during enterprise security reviews.
3. Implement and Assign Controls
Controls represent the operational side of SOC 2 that enterprise customers evaluate closely. Closing gaps is necessary, but execution matters more. Each control requires a defined process, a responsible owner, and consistent evidence.
Access control stands out as a critical area, which goes to show how often it fails in practice, with approximately 70% of material SOC 2 findings tied to weaknesses in CC6 access control criteria.
Access reviews, provisioning, deprovisioning, and role management should function consistently in daily operations. Policies alone do not satisfy enterprise buyers. Clear ownership and repeatable execution build trust during reviews.
4. Collect Evidence as Controls Run
Evidence collection should occur while controls operate, not at the last minute. 41% of companies report that a lack of continuous compliance slows down their sales cycles, which goes to show enterprise buyers expect current, verifiable proof.
That expectation requires capturing records generated during normal operations. These records include access review results, approval logs, onboarding and offboarding tickets, vulnerability remediation records, backup checks, vendor review notes, incident response tests, and policy acknowledgments.
Each record should clearly show who performed the control, when it happened, what was reviewed, and what action was taken. A consistent evidence trail, on the other hand, demonstrates that controls operate reliably over time.
5. Complete the Audit And Respond Quickly
Completing the audit marks a milestone, but response speed determines how enterprise buyers perceive your readiness. SOC 2, GDPR, and vendor risk assessments can add 2 to 4 weeks to the average B2B SaaS sales cycle, which goes to show how delays affect deal momentum.
Enterprise customers often request the SOC 2 report, bridge letters, management responses, control clarifications, and follow-up security answers on a tight timeline. Delayed responses create friction and raise concerns about operational maturity.
A defined process for sharing audit materials, answering questionnaires, and routing security questions to the right people supports faster responses. The goal is to help enterprise customers move through review with confidence while reinforcing your position as a trusted vendor.
Do You Need SOC 2 Type I Or Type II?
Most companies that sell to enterprise customers need SOC 2 Type II because it gives deeper assurance during procurement, security review, and vendor risk assessment.
46% of software buyers prioritize security certifications and data privacy practices when choosing a vendor, and for nearly all of them, a point-in-time snapshot is not enough. That is the core reason most enterprise sales cycles require SOC 2 Type II over Type I.
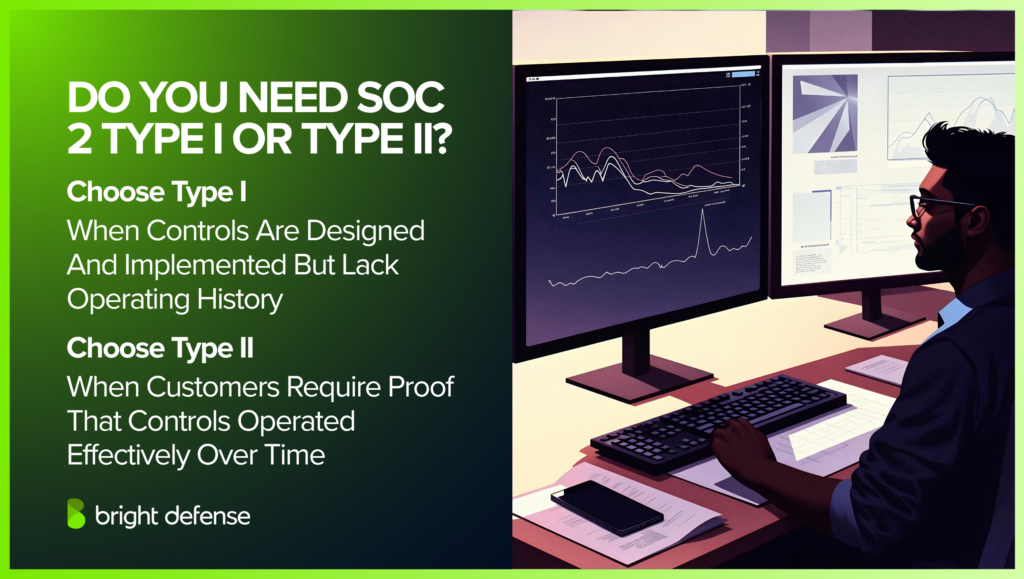
Type I, on the other hand, is usually the right starting point when controls are in place but have not been operating long enough for a period-based audit.
- Choose Type I if your controls are already designed and in place, but you do not have enough operating history yet to show they worked over a review period.
- Choose Type II if enterprise customers want stronger proof that those controls were not only designed properly but actually operated effectively over time.
In most enterprise sales cycles, Type II is the one customers expect because it gives deeper assurance during procurement, security review, and vendor risk assessment.
When Should You Start Collecting Evidence?
Start collecting evidence as soon as the controls are live, and ideally from the first day of the audit period.
For SOC 2, waiting until the audit is close usually creates gaps because many controls need proof over time, such as access reviews, onboarding and offboarding records, change approvals, vulnerability remediation, incident response activity, and policy acknowledgments.

Type I still needs evidence that controls were designed and implemented, while Type II needs a steady record showing those controls actually operated during the review window. The practical rule is simple: once a control exists, its evidence collection should start right away.
Realistic SOC 2 Timelines, Expectations, And What To Tell Customers During The Process
SOC 2 usually takes weeks for Type I and several months for Type II, depending on how ready the controls and evidence already are.

Type I can often be completed in about 4 to 8 weeks once scope, policies, and evidence are in good shape. Type II usually takes 3 to 6 months or more because the controls need time to operate and leave a clear evidence trail.
The best message for customers is a specific status update, such as “Type I is in progress,” “Type II evidence collection started in January,” or “The audit is active and the report is expected after fieldwork closes.” Bright Defense fits into the preparation side of that process by helping get scope, controls, and evidence ready before the auditor starts testing.
Mistakes That Slow SOC 2 Down
The mistakes that slow SOC 2 down are misaligned scope, unclear ownership, reactive evidence handling, informal processes, unvalidated controls, and unresolved issues that create friction during audit testing instead of during planning.
This section explains the common mistakes that delay SOC 2 and how they affect enterprise timelines.
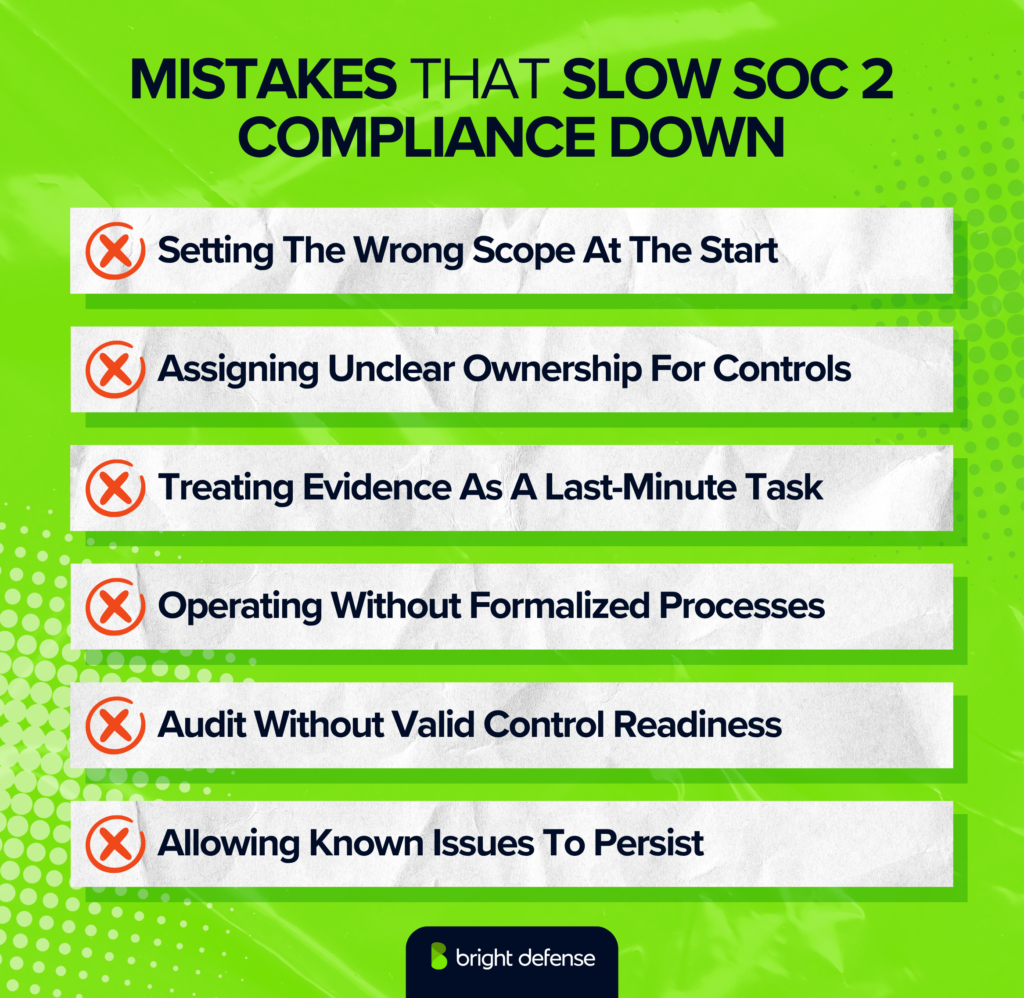
1. Setting The Wrong Scope At The Start
An overly broad or unclear scope increases audit complexity and extends timelines. Extra systems, vendors, and processes introduce unnecessary controls and evidence requirements.
Unclear boundaries, on the other hand, force auditors to ask repeated clarification questions, which leads to rework and slower progress during fieldwork.
2. Assigning Unclear Ownership For Controls
Distributed ownership without clear accountability creates bottlenecks. Control activities span multiple teams, yet no single owner tracks execution, evidence, or auditor communication.
This fragmentation, on the other hand, slows responses and creates gaps when auditors request clarification or additional proof.
3. Treating Evidence As A Last-Minute Task
Reactive evidence collection leads to incomplete or inconsistent records. Evidence collected late often lacks proper timestamps or alignment with control requirements.
Continuous evidence collection, on the other hand, keeps records accurate and reduces pressure when enterprise buyers request your report.
4. Operating Without Formalized Processes
Unwritten or informal practices fail under audit scrutiny. Auditors expect proof that controls operate consistently over time.
Reliance on team habits, on the other hand, creates uncertainty around repeatability, which increases testing effort and follow-up requests.
5. Entering The Audit Without Validated Control Readiness
Unverified controls introduce risk during audit fieldwork. Missing policies, incomplete procedures, and weak records surface late when timelines are already tight.
Early validation, on the other hand, allows your team to correct issues before auditors begin testing and prevents disruption during the audit.
6. Allowing Known Issues To Persist
Unresolved control issues compound over time and delay audit completion. Fixes often require re-running controls and collecting new evidence.
Immediate remediation, on the other hand, reduces dependency chains and keeps your audit moving without unnecessary delays.
A faster SOC 2 timeline depends on reducing operational friction before audit testing begins. Fixing these issues early improves audit speed and strengthens your position during enterprise security reviews.
How To Prepare Evidence And Get Ready For A SOC 2 Audit
Preparing SOC 2 evidence requires building consistent records for each control and organizing them in a way that auditors can quickly verify.
A SaaS or SMB founder should treat evidence preparation as an ongoing operational process rather than a last-minute task tied to a deal.
1. Map Each Control To Specific Evidence
Start with your SOC 2 controls and define exactly what proof supports each one. Access reviews map to review logs, change management maps to tickets and approvals, and incident response maps to documented events and timelines. This removes guesswork during the audit.
2. Collect Evidence Continuously During the Audit Period
Evidence must show that controls operated over time, not just once. Save screenshots, logs, approvals, and reports as they happen. A steady collection process prevents gaps and avoids last-minute scrambling when an enterprise buyer requests your report.
3. Standardize Evidence Format And Naming
Auditors review large volumes of files, so consistency matters. Use clear file names, include dates, and tie each item to a control ID. Organized evidence reduces back-and-forth and speeds up audit fieldwork.
4. Document The Process Behind Each Control
Evidence alone is not enough without context. Each control should have a short description of how it operates, who owns it, and how often it runs. This helps auditors understand your system without repeated clarification requests.
5. Run Internal Reviews Before The Auditor Starts
Conduct a mock audit or internal check to validate completeness. Look for missing approvals, inconsistent timestamps, or weak documentation. Early validation catches issues before they become audit findings.
6. Align Evidence With The Audit Period
A Type II audit requires proof that controls worked consistently across the review window. Evidence outside that period does not count. Make sure all records clearly fall within the defined timeframe.
7. Prepare For Auditor Questions And Follow-Ups
Auditors often request clarification or additional proof. Keep control owners ready to respond quickly with context, updated evidence, or explanations. Fast responses keep the audit moving and prevent delays.
8. Centralize Evidence In One System
Store all evidence in a single repository instead of scattered folders, emails, or chat threads. Centralization improves visibility, reduces version confusion, and makes it easier to share access with auditors.
What Happens After You Achieve SOC 2
After you achieve SOC 2, your focus shifts to maintaining compliance and using the report to move enterprise deals forward faster.
SOC 2 becomes part of your ongoing operations rather than a one-time milestone.
1. You Use The Report To Close Enterprise Deals Faster
Your SOC 2 report reduces friction in security reviews and procurement. Enterprise buyers rely on it as verified proof, which shortens questionnaires and speeds up approvals during the sales process.
2. You Maintain Controls Throughout The Year
Controls must continue operating consistently after certification. Access reviews, logging, monitoring, and policy enforcement need to run on schedule, or gaps will surface in your next audit and in customer reviews.
3. You Prepare For The Next Audit Cycle Early
SOC 2 audits repeat annually, so evidence collection and control monitoring continue year-round. Continuous readiness prevents last-minute pressure and keeps your audit timeline predictable.
4. You Handle Ongoing Customer Security Requests
Enterprise customers regularly ask for your SOC 2 report, updates, or clarification. A clear process for sharing documents and responding quickly helps maintain deal momentum and builds long-term trust.
SOC 2 does not end at certification. It becomes a continuous signal that your company can meet enterprise security expectations at any point in the buying process.
What Are Realistic Cost Expectations For SOC 2?
SOC 2 costs typically range from $20,000 to $100,000+ depending on audit type, scope, and internal readiness. Audit fees make up the largest portion, with Type I audits costing around $10,000 to $25,000 and Type II audits ranging from $20,000 to $60,000+.
Additional costs include compliance tools, which often run $5,000 to $25,000 per year, along with remediation work if controls are weak. Costs increase when scope is broad or multiple criteria are added, while a focused scope and strong existing controls keep total spend lower.
How to Choose the Right Readiness Partner And Auditor
The right readiness partner helps get the control environment ready for scrutiny, and the right auditor turns that work into a report enterprise customers will trust.
Here are some ways to choose your readiness partner:
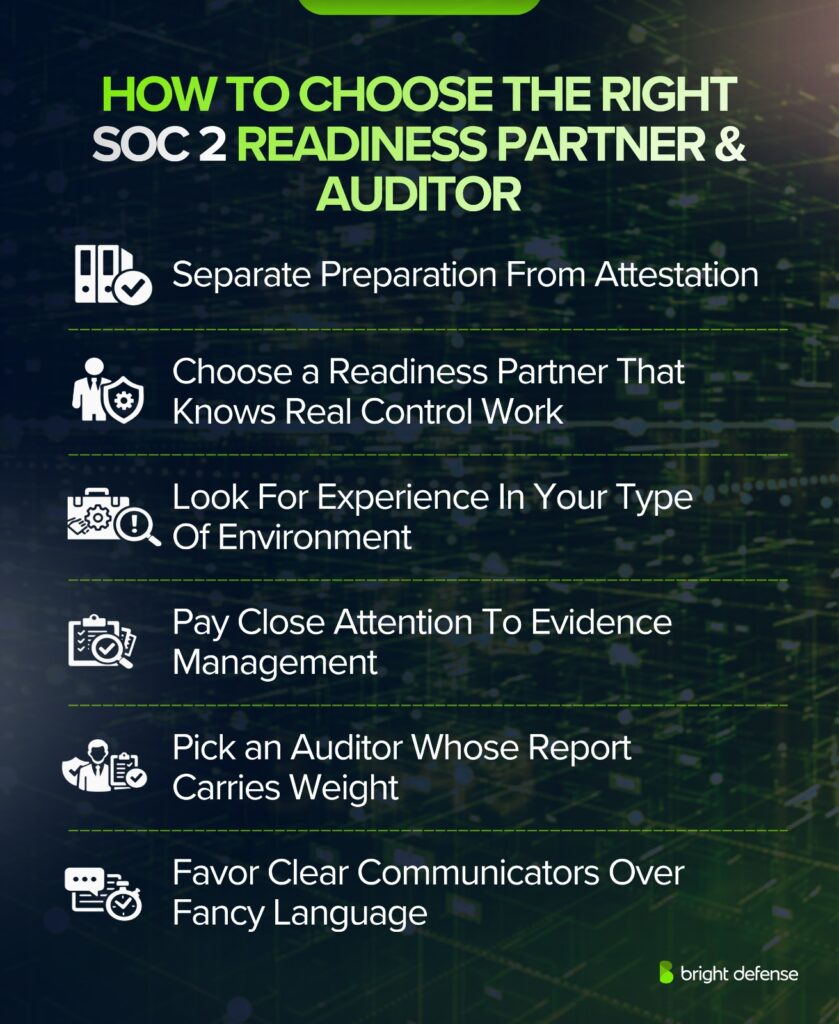
1. Separate Preparation From Attestation
A readiness partner helps with scoping, control design, policy cleanup, evidence collection, and internal prep. An auditor does not play that role. The auditor tests the environment independently and issues the SOC 2 report. Confusion usually starts when both roles get blended together in one conversation. A cleaner approach is to judge each role on its own purpose.
2. Choose A Readiness Partner That Knows Real Control Work
The strongest readiness partner is not just good at giving templates. The real value comes from helping turn requirements into operating habits that hold up during testing. That includes access reviews, onboarding and offboarding, change control, vulnerability management, logging, incident handling, and vendor oversight. A firm that only hands over documents often leaves the hard part untouched.
3. Look For Experience In Your Type Of Environment
Scope is where many SOC 2 projects go sideways. A good readiness partner should be able to pin down which product, systems, entities, teams, and vendors belong in scope without turning it into a long abstract exercise. A good auditor should be just as sharp on the same boundaries. Sloppy scope decisions usually create rework, extra cost, and avoidable delays.
4. Pay Close Attention To Evidence Management
Evidence is often the difference between a smooth audit and a painful one. The better readiness partner will have a clear way to collect screenshots, tickets, approvals, logs, review records, and policy acknowledgments throughout the audit window. The better auditor will ask for evidence clearly and consistently, without making every request feel improvised.
5. Pick An Auditor Whose Report Carries Weight
Enterprise customers do not just review the report content. They care about whether the audit feels credible. A respected auditor with a disciplined SOC 2 practice usually makes procurement and security review easier because the report is easier to trust and easier to defend internally. Brand name matters less than audit quality, consistency, and familiarity with real enterprise reviews.
6. Favor Clear Communicators Over Fancy Language
Good firms explain gaps plainly, answer questions directly, and keep requests understandable. That matters during readiness because teams need practical direction, not compliance theater. It matters during audit because weak communication usually turns simple requests into long email chains and missed deadlines.
The simple way to think about it is this: choose a readiness partner that helps the company operate cleanly before the audit, and choose an auditor whose report will stand up in a serious enterprise review.
How Bright Defense Can Help You Get SOC 2 Ready
Bright Defense cybersecurity compliance services turn SOC 2 from a vague customer demand into a structured execution plan with defined scope, readiness assessment, control implementation, policy alignment, and organized evidence collection within a formal compliance program.
The approach centers on practical preparation for SaaS and SMB teams, including gap analysis to identify control deficiencies, strengthening security practices across systems, implementing required cybersecurity controls, and structuring audit-ready evidence that withstands external review.
The process incorporates continuous monitoring, security awareness training, and incident response testing, which strengthens compliance posture and supports long-term audit readiness.
For founders, this matters because SOC 2 readiness depends on consistent control execution, operational discipline, and proper handling of sensitive data across daily workflows rather than surface-level understanding.
FAQ
The system description is the section that explains what your service does, how it works, and which people, processes, technology, and data are part of the audited system. It matters because it defines the audit boundary and gives the auditor the context needed to evaluate your controls.
A common Type II timeline includes pre-audit preparation of 1 to 3 months plus an observation period of3 to 12 months, with audit work often listed at 2 to 5 weeks and report drafting at 2 to 6 weeks, and a common audit-fee range published for Type II is $12,000 to $20,000 for small to midsize firms with larger and more complex orgs cited at$30,000 to $100,000+.
It depends, but a practical response is a short written plan that states your target report type, the criteria in scope, your target observation window, and when you expect to share the report, since SOC 2 is meant for customers who need detailed assurance. (AICPA & CIMA)
No. SOC 2 reports are meant for users who need detailed information and assurance, so companies limit distribution to customers, prospects, and partners with a valid need, based on customer expectations, the defined audit scope, and applicable compliance requirements. (AICPA & CIMA)
No. A SOC 3 report serves as the general-use option for public sharing, while SOC 2 remains restricted to controlled distribution, which supports accurate compliance status and structured compliance support practices. (AICPA & CIMA)
It depends. Many programs use observation periods between 3 and 12 months, so a shorter window still requires sufficient evidence that key controls operated effectively throughout the period and align with the organization’s compliance program. (Vanta)
Run the program continuously. Consistent execution across the year uses ongoing monitoring practices such as continuous evidence collection, access reviews, and remediation, supported through continuous control monitoring and periodic refresh assessments so the Type II period remains clean and supportable. (AICPA & CIMA)
You need a defined system scope, documented controls tied to the relevant Trust Services Criteria, management’s system description and assertion, and an independent CPA examination of those controls within a structured audit process.
A common requirement is restricting access to customer data and protecting its confidentiality through security practices such as access controls and encryption, supported by continuous monitoring. SOC 2 focuses on confidentiality and privacy, and Microsoft states that customer content is encrypted at rest and in transit in its online services.
In SOC 2, customer data refers to the users’ data your system processes, including sensitive information that the system stores, uses, retains, discloses, or disposes of, particularly when organizations store customer data across systems.
Get In Touch