Updated:
April 1, 2026
SOC 2 For Startups: The Definitive Guide
SOC 2 compliance directly influences revenue, partnerships, and investor confidence in early-stage startups. Many startups prioritize product and growth first, yet buyers and investors often expect compliance before moving forward.
83% of enterprise buyers require SOC 2 certification from SaaS vendors before signing contracts, and 67% of startups that obtained SOC 2 reported it directly enabled deals they would have otherwise lost.
If you’re a startup this blog will be helpful for you. it should be able to inform you why SOC 2 is critical for beginigng phase of your business
Let’s dive right in!
What Is SOC 2 and Why is It Important for Startups?
SOC 2 is a set of rules that explains how a company should protect customer data. It focuses on five areas: security, availability, processing integrity, confidentiality, and privacy.
An independent auditor reviews a company’s systems and processes to check whether these rules are followed. The outcome is a SOC 2 report, which shows customers that the company handles data in a safe and responsible way.
For startups, SOC 2 matters because it builds customer trust, supports sales conversations, and shows prospects, partners, and investors that the company takes data protection seriously.
SOC 2 reports come in two types:
- SOC 2 Type I: Reviews whether controls are properly set up at one point in time
- SOC 2 Type II: Reviews whether controls work properly over a period of time
The following are a few startups where SOC 2 is considered a critical requirement:
- SaaS startups: They host customer data and business workflows in the cloud, so buyers want proof that the platform is secure.
- Fintech startups: They handle payment details, banking data, and financial records, which makes trust and control requirements much stricter.
- Healthtech startups: They work with patient and health-related information, so strong data protection practices matter from the start.
- Cybersecurity startups: They sell security services or tools, so customers expect them to meet high internal security standards themselves.
- HR and payroll startups: They process employee records, salary data, tax information, and other private business details.
- Legal tech startups: They store contracts, legal files, and confidential client documents that require careful access control.
- Data analytics and AI startups: They often collect and process large amounts of customer or operational data, which raises privacy and security concerns.
- Managed service providers and IT startups: They often have direct access to client systems, networks, and sensitive internal data.
Why Should Startups Adopt SOC 2?
Startups pursue SOC 2 to close deals faster, meet enterprise security requirements, and build buyer trust. The sections below cover the core reasons.
1. SOC 2 Helps Companies Grow Revenue Faster
Weak compliance slows down revenue. 41% of companies face slower sales due to gaps in their compliance posture, while 3 in 4 companies with stronger continuous compliance programs report that approach actively drives business growth.

35% of enterprise organizations with over $1 billion in revenue cite winning new clients as the primary driver of their compliance investment, and over 75% of consumers say they will not purchase from companies they do not trust with their data. A completed SOC 2 report signals that trust upfront, which leads to quicker decisions and higher conversion rates for your startups.
2. SOC 2 Makes Customer Security Reviews Easier
Customer security reviews become easier with a standardized report that addresses most security requirements upfront. Repeated questionnaires and manual proof requests drop significantly for companies that hold a SOC 2 report, reducing review time and effort.

46% of software buyers select vendors based on security certifications and data privacy practices, making a verified third-party report a direct factor in purchase decisions. Your buyers can rely on that report instead of requesting separate documentation, which simplifies the entire review process.
3. SOC 2 Builds Trust With Larger Buyers
If you’re a startup that is working with larger buyers they’d require you strict vendor risk checks. And the best part of having a SOC 2 report provides verified proof that security controls have undergone independent review. As a result, it increases the trust it requires to onboard larger buyers.
77% of organizations require compliance with frameworks such as SOC 2, ISO 27001, or NIST during procurement, while 63% expect detailed security information before initial engagement, which goes to show that third-party validation directly influences vendor selection.

Your customers pay close attention to how you handle their data, and SOC 2 signals that strong safeguards are in place from the start. 70% of business leaders report improved trust and reputation after strengthening security and compliance, which often becomes the deciding factor when customers compare competing providers.
4. SOC 2 Reduces Major Security Gaps
The structured audit process helps your startup identify and reduce control gaps over time. Each audit cycle reviews how well controls are designed and whether they operated correctly during the review period. Gaps that appear in one report become priority fixes before the next review, which creates a repeatable cycle of improvement.
That structure gives startups a practical way to catch weaknesses they might otherwise miss. Access review failures, incomplete change management logs, and missing evidence for key controls are common findings that surface during audits. Addressing those findings strengthens the overall control environment and reduces the chance of a serious gap going unnoticed.
5. SOC 2 Supports Better Risk Management
A formal process for identifying, testing, and fixing control weaknesses is central to how SOC 2 supports risk management. A survey of 300 U.S. organizations found that 87% reported negative outcomes from low compliance maturity, including 40% that reported security incidents and 41% that reported slower sales cycles.

Those numbers show why a structured compliance framework matters for managing risk. The audit process requires companies to define their control objectives, test them against real operating conditions, and document the results. That turns risk management from a general priority into a measurable practice with clear records of what works and what needs attention.
6. SOC 2 Improves Vendor and Third Party Oversight
Vendor and third-party oversight improves when both sides work from a standardized report that shows how a service provider manages security controls. That structure matters because vendor risk is a growing business concern. 70% of organizations are highly concerned about cybersecurity risk in their supply chains.
28% experienced a cybersecurity incident tied to a third-party vendor or supplier in the past two years, which shows the concern is grounded in real exposure. 45% conduct third-party risk assessments annually, and a completed report gives those assessments a consistent baseline to work from. Companies gain a clearer way to review vendors, compare security practices, and keep oversight more consistent over time.
7. SOC 2 Helps Build a Security First Culture
A SOC 2 program makes security part of daily work through regular training, clear policies, access reviews, and incident response processes. This is crucial because 68% of breaches involved the human element, meaning employee behavior directly affects security outcomes.

Security awareness training, defined access controls, and documented incident response procedures are baseline requirements under the framework, which pushes companies to treat security as an ongoing business practice rather than a one-time task.
Over time, that structure helps employees spot risks earlier, follow security rules more consistently, and report problems before they grow.
8. SOC 2 Shows Stronger Security Maturity
Documented controls, and proofs that security practices work over time are the markers of stronger security maturity. That makes a completed SOC 2 report a useful signal of how seriously a company manages risk and protects data.

A benchmark study of 193 SOC reports found that 54.9% contained at least one control exception, while the average number of exceptions per report fell from 2.7 to 1.73 year over year. Those numbers show that the audit process can reveal control weaknesses and reflect progress as companies fix them and operate with more consistent security practices.
9. SOC 2 Creates Clear Control Ownership
Clear control ownership comes from documented controls, assigned responsibilities, and regular testing over time.
That structure pushes companies to name owners for tasks such as access reviews, incident response, change management, vendor oversight, and evidence collection.

Defined ownership reduces confusion, strengthens accountability, and makes security work easier to manage across teams.
10. SOC 2 Improves Business Continuity Readiness
Business continuity readiness improves through documented backup, recovery, and incident response controls that teams review and test over time.
Most startups lack formal recovery testing until a compliance framework requires it. The audit process pushes companies to define recovery objectives, document backup procedures, and run tests that prove those plans work under real conditions.

That process surfaces gaps in recovery timelines, backup coverage, and team coordination before an actual outage forces the issue.A more structured way to prepare for outages, test recovery plans, and fix weak points before a real disruption happens is one of the more practical outcomes of maintaining the framework.
Startups That Benefit Most from SOC 2 Compliance
For startups handling sensitive data and aiming to scale quickly, SOC 2 can be a critical step toward securing their operations and building trust with stakeholders.
This section delves into the types of startups that stand to benefit significantly from SOC 2 compliance.

1. Startups Handling Sensitive Data
Startups that collect, store, or process sensitive data are strong candidates for SOC 2 compliance. This includes personal information, payment data, health records, customer files, and other business-critical information.
SOC 2 gives these startups a formal way to show that they protect data through defined controls such as restricted access, logging, risk management, and incident response. That level of discipline matters to customers who want proof that their information is handled responsibly.
2. Startups Seeking Enterprise Clients
Startups that want to win enterprise clients often need SOC 2 to move through procurement and vendor risk reviews. Large companies rarely rely on promises alone when they evaluate a software vendor or service provider.
They want documented evidence that security practices are in place and reviewed by an independent auditor. A SOC 2 report helps a startup answer security questionnaires more efficiently, support sales conversations with credible documentation, and reduce hesitation from larger buyers.
3. Startups In Regulated Industries
Startups in finance, healthcare, education, and similar sectors can benefit from SOC 2 because these industries place close attention on security, privacy, and operational accountability.
SOC 2 does not replace sector-specific laws or standards, yet it provides a strong control framework that supports broader compliance efforts. A startup with SOC 2 can enter audits, customer reviews, and partnership discussions with a clearer record of how it protects systems and data.
4. Startups Planning Rapid Growth
Startups preparing for rapid growth often benefit from SOC 2 before expansion creates operational strain. Growth usually brings larger customers, more employees, more vendors, and greater scrutiny from investors and partners.
SOC 2 helps a startup build repeatable security practices early, rather than trying to fix gaps after growth exposes them. That preparation can make scaling more orderly, improve readiness for due diligence, and present the company as a more mature business.
How SOC 2 Makes Startups More Competitive
SOC 2 makes startups more competitive as it provides a clear, recognized way to address security concerns early and qualify for larger deals. It helps startups appear credible during vendor selection, which directly affects revenue opportunities.
The impact shows in sales performance, since 41% of organizations with low compliance maturity experience slower sales cycles, while 63% of buyers expect detailed security information before engaging, and 56% consider certifications extremely important during early evaluation.
Enterprise expectations are even stricter, with 77% requiring compliance with standards such as SOC 2, ISO 27001, or NIST during procurement. For startups, SOC 2 shifts perception from high risk to viable vendor, which reduces friction in security reviews and opens access to larger customers.
How SOC 2 Builds A Foundation For Long Term Success
SOC 2 builds a foundation for long-term success through repeatable controls, clear accountability, and independent validation that continues to provide value after the audit period. It turns security from a reactive task into a structured system that scales with the business.
Teams follow defined processes, which reduces inconsistency and limits last-minute remediation work during growth or new sales cycles. Internal ownership becomes clearer, which improves how quickly issues are identified and resolved. External validation strengthens trust with buyers, which shortens security reviews and reduces friction in procurement.
Over time, this structure allows companies to respond to customer requirements faster, maintain stronger control visibility, and operate with fewer disruptions as they expand into larger and more demanding markets.
These outcomes align with broader trends, where three in four organizations with continuous compliance programs report business value, 87% of companies with low compliance maturity report negative outcomes, 82% of enterprise organizations express concern about supply chain cyber risk, 34% report third-party incidents in the past two years, 63% of buyers expect detailed security information before engagement, and 56% rate certifications as extremely important during vendor discovery.
Common Challenges and Solutions
Achieving SOC 2 compliance can be a challenging journey for startups, often marked by hurdles that can seem daunting, especially for those with limited resources or experience in data security and privacy practices. This section explores common challenges startups face during the SOC 2 compliance process and offers practical solutions to navigate these obstacles effectively.
1. Resource Constraints
Challenge: Many startups operate with limited financial and human resources, making the comprehensive SOC 2 compliance process seem overwhelming.
Solution: Prioritize and phase your compliance efforts. Start with a more attainable goal, such as a SOC 2 Type I report. Use automated tools to streamline and reduce the workload. Consider outsourcing specific tasks to specialized consultants or service providers like Bright Defense.
2. Knowledge and Expertise Gaps
Challenge: The complexity of SOC 2 requirements can be challenging for startups without in-house compliance expertise.
Solution: Leverage external expertise through consultants or compliance firms that specialize in SOC 2. Additionally, invest in training for your team to build internal expertise over time.
3. Maintaining Compliance Over Time
Challenge: SOC 2 is not a one-time achievement but requires ongoing effort to maintain compliance as your startup evolves.
Solution: Implement continuous monitoring tools and establish internal processes for regularly reviewing and updating your security measures and policies. Foster a culture of compliance and security awareness within your team. We recommend tools like Drata, KnowBe4, and JumpCloud to boost security controls through automation.
4. Balancing Speed to Market and Compliance
Challenge: Startups are often under pressure to launch products quickly. This can conflict with the time-consuming process of achieving SOC 2 compliance.
Solution: Integrate compliance considerations into your product development lifecycle from the start. This proactive approach helps ensure that security and privacy are built into your product, reducing delays and rework.
5 Steps To SOC 2 Compliance For Startups
SOC 2 compliance for startups usually follows five clear steps, starting with scope and ending with the audit.
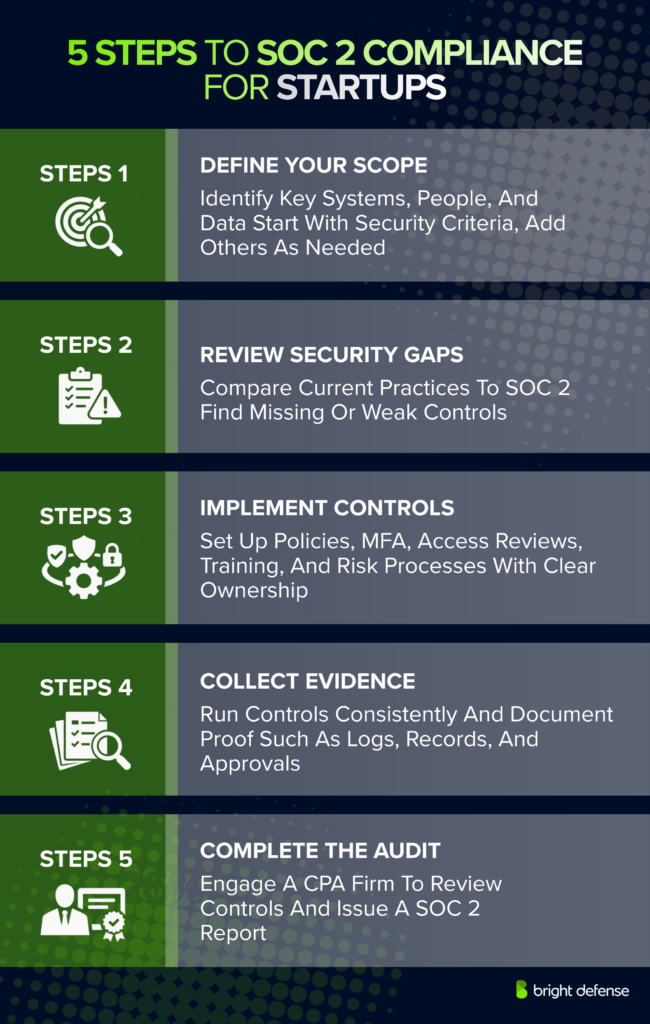
- Define Your Scope: Start with the systems, people, and data that matter most to your customers. Most startups begin with the Security Trust Services Criteria, then add others such as Availability or Confidentiality when customer needs call for them. This step sets the boundaries for the audit and keeps the project focused.
- Review Your Current Security Gaps: Compare your existing policies, tools, and processes against SOC 2 requirements. Look at access controls, logging, vendor management, incident response, employee onboarding and offboarding, and backup practices. This review shows what is missing, what needs updates, and what already meets the standard.
- Put The Right Controls In Place: Create or improve the controls needed for SOC 2. That often includes written policies, multi-factor authentication, access reviews, security awareness training, change management, risk assessments, and incident response procedures. Each control should have a clear owner so responsibilities do not get lost.
- Collect Evidence And Operate The Controls: Run the controls consistently and keep records that show they are working. Evidence can include access review logs, training records, policy approvals, risk assessment documents, screenshots, and incident response records. For a Type II report, auditors need proof that controls worked over a period of time, not just on one day.
- Choose An Auditor And Complete The Audit: Work with a licensed CPA firm that performs SOC 2 audits. The auditor reviews your controls, tests your evidence, and issues the final report. Many startups start with SOC 2 Type I, then move to Type II once they have enough operating history.
Final Thoughts
SOC 2 compliance is a significant undertaking for startups, but it’s also a powerful tool for building trust, enhancing security, and achieving sustainable growth. By navigating the common challenges with strategic solutions and leveraging SOC 2 status as a growth driver, startups can set themselves apart in a competitive marketplace. Achieving and maintaining SOC 2 compliance demonstrates a startup’s commitment to data security and privacy, earning the trust of customers, investors, and partners alike. This commitment, in turn, lays a solid foundation for long-term success and resilience in the digital age.
Remember, SOC 2 compliance is not just a badge to be earned but a commitment to operational excellence and customer trust that requires ongoing effort and dedication.
Bright Defense Delivers SOC 2 For Startups!
If your startup is considering SOC 2 compliance, Bright Defense can help. Our monthly engagement continuous compliance service model delivers a robust security program to help your startup achieve SOC 2. Our services include a compliance automation platform to increase efficiency and lower the cost of compliance. Once compliance is achieved, we constantly enhance your security program to keep up with the evolving threat landscape and compliance standards.
We also deliver continuous compliance solutions for other compliance frameworks, including ISO 27001, HIPAA, CMMC, and PCI. Additional services include gap analysis, security risk assessments, security awareness training, multi-factor authentication, disaster recovery planning, and more.
Get started on your SOC 2 compliance journey today with Bright Defense!
Frequently Asked Questions
What Is SOC 2 for Startups?
SOC 2 for startups refers to the process by which emerging companies demonstrate their commitment to data security by adhering to the American Institute of Certified Public Accountants’ (AICPA) standards for managing customer data. This involves implementing rigorous security controls, policies, and procedures to protect sensitive information and establishing a strong security posture.
How Do Startups Determine Appropriate Security Controls?
Startups should begin by conducting a thorough risk assessment to identify potential security risks specific to their operations. Based on this assessment, startups can tailor their security measures to address these risks effectively, ensuring their security program is both comprehensive and aligned with SOC 2 standards.
What Does Security Training for Employees Involve?
Security training for employees aims to foster a security-first culture within the organization. This involves educating staff on standard security processes, the importance of maintaining the integrity of confidential data, and how to respond to security incidents. Effective training ensures that all team members understand their role in upholding the organization’s security controls.
How Do You Choose an Auditing Firm for SOC 2 Compliance?
Choosing an auditing firm for a SOC 2 compliance audit involves researching firms with extensive experience in conducting SOC 2 audits within your industry. Look for a firm that not only understands the technical requirements of SOC 2 but also has a track record of working with startups to operationalize security controls effectively.
Why Is a Security Program Important for SOC 2 Compliance?
A comprehensive security program is essential for SOC 2 compliance as it demonstrates the organization’s ongoing commitment to securing its operations and data. This program should include regular security training, a robust risk assessment process, and the implementation of effective security measures to mitigate identified security risks.
How Can Startups Use SOC 2 to Improve Their Security Posture?
Startups can use SOC 2 as a framework to strengthen their security posture by systematically addressing the security controls and practices required for compliance. This process encourages startups to formalize their approach to security, from assessing and mitigating risks to implementing and monitoring security measures consistently.
What Is Involved in a SOC 2 Compliance Audit?
A SOC 2 compliance audit involves a comprehensive review of the organization’s security controls to ensure they meet the SOC 2 standards. The auditing firm will evaluate the effectiveness of these controls, the organization’s adherence to stated security policies, and the overall maturity of its security program.
How Does SOC 2 Compliance Protect Against Data Breaches?
SOC 2 compliance helps protect against data breaches by requiring startups to implement and maintain robust internal controls and security measures designed to safeguard confidential data. Through regular monitoring and evaluation, startups can identify and rectify vulnerabilities, reducing the risk of security incidents.
How Can Startups Operationalize Security Controls?
Startups can operationalize security controls by integrating them into their daily operations and standard business processes. This includes automating security measures where possible, ensuring security controls are maintained and updated in response to new threats, and embedding security considerations into the development and deployment of new products or services.
What Are the Benefits of Establishing Standard Security Processes?
Establishing standard security processes benefits startups by creating a consistent and repeatable approach to managing security risks. This consistency helps ensure that security measures are effectively implemented and maintained across the organization, improving the overall security profile and compliance posture.
How Can Startups Foster a Security First Culture?
Fostering a security-first culture involves prioritizing security at all levels of the organization, from the executive team to individual contributors. This culture is built through regular security training, clear communication about the importance of security, and encouraging employees to proactively identify and report potential security risks.
How Does SOC 2 Impact an Organization’s Security Profile?
SOC 2 compliance positively impacts an organization’s security profile by demonstrating a commitment to industry-recognized security standards and practices. Achieving and maintaining SOC 2 compliance signals to customers, partners, and stakeholders that the organization takes security seriously and has implemented a robust security program to protect sensitive data.
SOC 2 is a report on controls at a service organization relevant to security, availability, processing integrity, confidentiality, or privacy, which is why SaaS and other service startups use it to answer customer due diligence requests with formal assurance.
Startups that handle customer data or provide services customers rely on for sensitive workloads commonly pursue SOC 2 because the report is intended for users who need detailed assurance about the controls used to process users’ data.
The Trust Services Criteria cover Security, Availability, Processing Integrity, Confidentiality, and Privacy, and many startups start with Security first, then add other criteria when customer requirements demand it.
Type I evaluates whether controls are designed appropriately at a point in time, while Type II evaluates whether controls are designed and operating effectively over a defined period.
A common timeline includes pre-audit preparation of 1–3 months, an observation period of 3–12 months for Type II, an audit phase of 2–5 weeks, and report creation and delivery of 2–6 weeks.
Yes. A direct path to Type II is common when the startup can support the observation period and customers want Type II evidence.
Audit fees are often quoted around $7,500–$15,000 for a small to midsize Type I and $12,000–$100,000+ for Type II, with total first-year spend often higher once tools, internal time, and remediation work are included.
No. SOC 2 is written for users who need detailed information, while SOC 3 is the general-use report that can be freely distributed, so many startups use SOC 3 for public posting and share SOC 2 privately with customers.
Most companies run SOC 2 on an annual 12-month cadence or a semi-annual 6-month cadence, depending on customer expectations and internal capacity.
A practical starting point is a tight system boundary, a clear list of in-scope services and vendors, a decision on which Trust Services Criteria apply, and an evidence plan that matches the observation window the auditor will test.
Get In Touch