Updated:
April 16, 2026
120+ Penetration Testing Statistics for 2026
This collection organizes penetration testing and cybersecurity statistics into topic-based sections.
These top penetration testing statistics come from primary sources published in 2025 or early 2026, and the figures are hyperlinked to their original documents.
The data covers the penetration testing industry from market growth and adoption rates to breach costs, remediation timelines, and the growing role of AI in security validation.
Penetration Testing Market Size and Growth Stats
- The global market for penetration testing was valued at USD 2.74 billion in 2025. (Fortune Business Insights)
- Fortune Business Insights projects the penetration testing market will grow from $3.09B in 2026 to $7.41B by 2034 at a compound annual growth rate of 11.60%. (Fortune Business Insights)
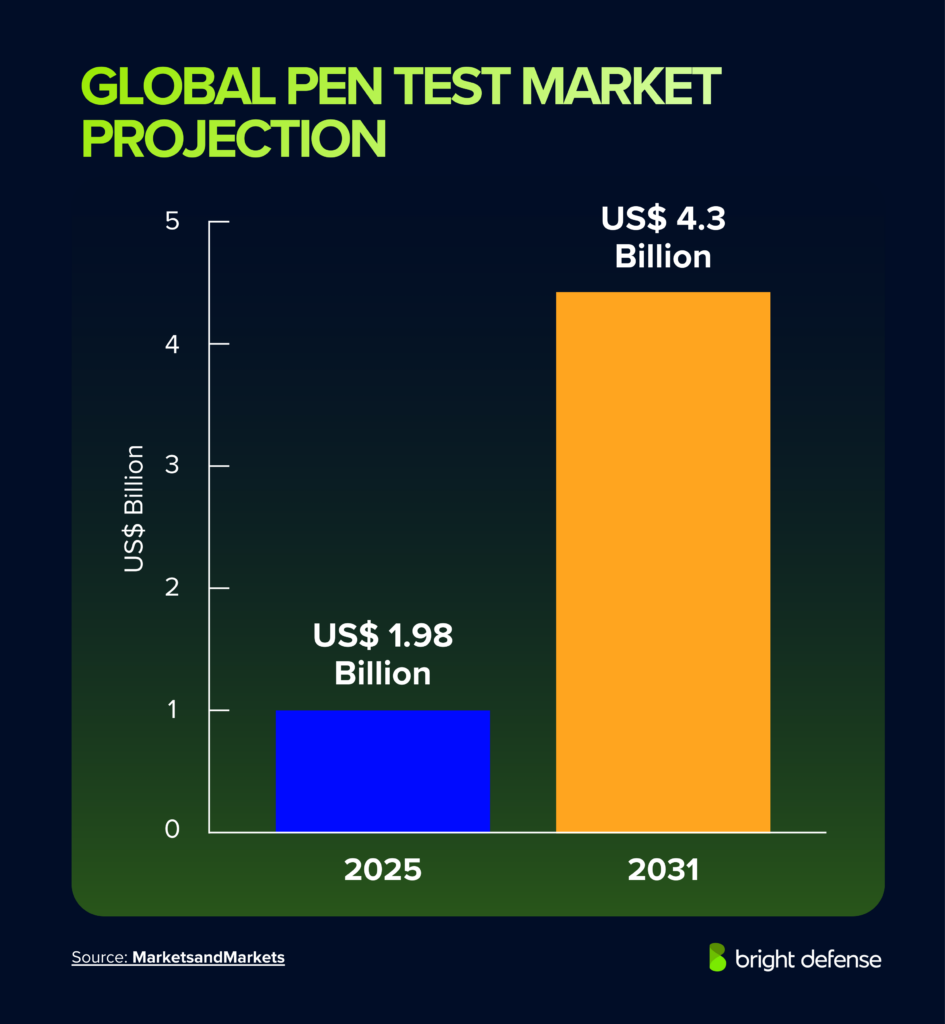
- MarketsandMarkets projects the global market will grow from USD 1.98 billion in 2025 to USD 4.39 billion by 2031 at a 14.2% CAGR. (MarketsandMarkets)
- Mordor Intelligence projects the pen test market to grow to USD 5.54 billion by 2031 at a 15.29% CAGR. (Mordor Intelligence)
- North America held 35.10% of the global network security market share for penetration testing in 2025. (Fortune Business Insights)
- Web application penetration testing accounts for 35.60% of all penetration tests, leading all test types. (Mordor Intelligence)
- The healthcare segment is expected to grow at a 17.20% CAGR through 2031, driven by incoming HIPAA revisions requiring healthcare organizations to conduct annual pen tests. (Mordor Intelligence)
- BFSI held the largest end-user share at 28.70% of the penetration testing market in 2025. (Mordor Intelligence)
- Asia-Pacific pen test market is forecast to grow at a 16.78% CAGR through 2031, the fastest of any region in the penetration testing industry. (Mordor Intelligence)
- Large enterprises and leading companies contribute 66% of penetration testing market revenue. (AppSecure/Straits Research)
- SME adoption of penetration testing is growing at an 18.58% CAGR, making advanced security testing more accessible to smaller organizations. (AppSecure/Straits Research)
- The mobile penetration testing segment covering mobile applications in the USA, Canada, Japan, China, and Europe will drive a 20.7% CAGR. (Digital Journal)
- Penetration testing for the public sector is likely to expand the industry further by 2028. (Digital Journal)

Penetration Testing Adoption & Budgets
- 67% of U.S. enterprises experienced a breach in the previous 24 months despite large security stacks and existing strong security measures. (Pentera)
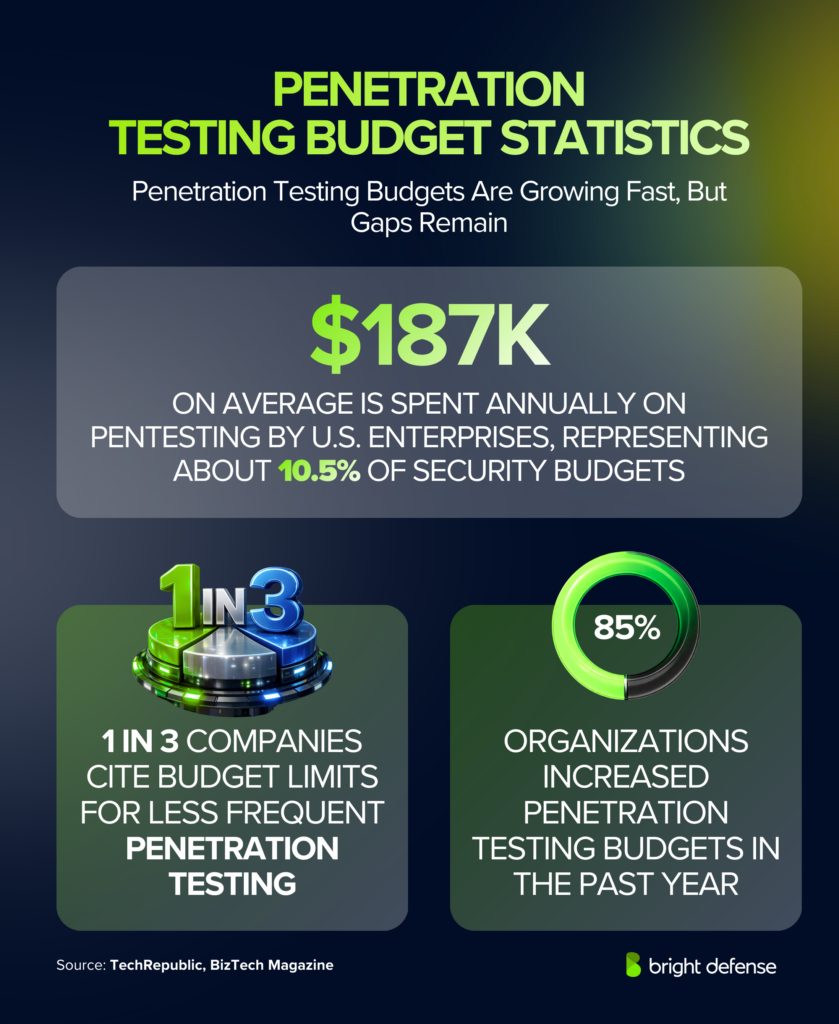
- U.S. enterprises spend an average of USD 187,000 annually on pentesting, roughly 10.5% of IT security budgets. (Pentera)
- Average total IT security budgets for U.S. enterprises are USD 1.77 million. (Pentera)
- More than 50% of CISOs plan to increase their pentesting budgets in 2025. (Pentera)
- 85% of organizations raised their penetration testing budgets in the past year. (TechRepublic via Cybersecurity Ventures)
- 1 in 3 companies cite budget as their reason for not conducting regular penetration tests more frequently. (BizTech Magazine via Cybersecurity Ventures)
- 48% of CISOs cited the availability of skilled penetration testers as a top obstacle for the third consecutive year. (Pentera)
- 55% of enterprises now use software-based penetration testing tools for in-house testing. (Pentera)
- Half of CISOs cite software-based testing as their primary method for assessing security posture and uncovering security gaps. (Pentera)
- 70%+ of organizations have adopted Penetration Testing as a Service (PTaaS), a form of crowdsourced security testing, with another 14% planning to. (Pentera)
- Only 29% of organizations conduct pen testing primarily for compliance initiatives; the rest do it for control validation, investment prioritization, or attack damage assessment. (Pentera)
- 32% use pen test results to prioritize security investments, 28% test for control validation, and 16% include pen testing in merger and acquisition due diligence. (Pentera)
- U.S. enterprises use an average of 75 security tools, with 45% reporting stack growth. (Pentera)
- Organizations with 11 to 50 tools generate around 883 alerts per week; those with 76 to 100 tools see 2,048 alerts; and over 101 tools produce 3,074 alerts. (Pentera)
- The average U.S. organization processes 2,000 security alerts per week. (Pentera)
- Cyber-insurance providers recommended or required additional security tools for 93% of surveyed CISOs. (Pentera)
- 59% of organizations implemented at least one tool at their insurer’s request to support vulnerability management programs. (Pentera)
- Organizations with fewer than 50 tools reported breaches at a 93% rate, while those with more than 100 tools had 61%. (Pentera)
- 96% of organizations make changes to their IT environment at least quarterly, which supports the case for continuous security assessments. (Pentera)
- Nearly a third of enterprises suffered compromises on their web-facing assets. (Pentera)
- External attack surfaces were compromised almost twice as often as internal networks. (Pentera)
Pentesting Outcomes and Remediation

- 94% of organizations consider pentesting to be a core part of their security programs. (Cobalt)
- 81% of firms feel confident in their security posture, yet pentests consistently reveal hidden security vulnerabilities. (Cobalt)
- 75% of organizations set two-week remediation SLAs for pentest findings. (Cobalt)
- The median time to resolve any pentest finding is 67 days, far exceeding the two-week target. (Cobalt)
- Serious findings have a median remediation time of 50 days. (Cobalt)
- Less than half of all pentest findings ever get fixed, with only 48% resolved. (Cobalt)
- Serious findings fare better at a 69% resolution rate. (Cobalt)
- In 2017, only 27% of serious findings were resolved; by 2024, remediation time dropped from 112 days to 37 days. (Cobalt)
- Larger firms take longer: organizations with over 5,001 employees take 61 days to resolve serious findings, versus 27 days for firms with 1 to 100 employees. (Cobalt)
- Only 21.1% of serious AI/LLM pentest findings are resolved, compared with 73.5% for web tests and 75.5% for API tests. (Cobalt)
- Median remediation time for serious AI/LLM findings is about 19 days, yet the resolution rate remains the lowest across all pentest categories. (Cobalt)
- Internal penetration tests reveal network findings with an MTTR of 44 days, compared with 25 days for API and 19 days for AI/LLM. (Cobalt)
- Manufacturing has the longest MTTR for serious findings at 122 days; Hospitality is the shortest at 20 days. (Cobalt)
- 57% of organizations resolve 90% or more of serious findings, while 15% resolve 10% or fewer. (Cobalt)
- Criticality is the top driver for remediation at 36%, followed by ease of fix at 21%, compliance at 16%, PII exposure at 15%, and asset sensitivity at 12%. (Cobalt)
- Manual testing uncovered nearly 2,000 times more unique security vulnerabilities than automated scans alone. (AppSecure/Straits Research)
- Pentesters could breach internal network perimeters in 93% of companies tested. (Positive Technologies)
- Automated scanners increased vulnerability detection by nearly 39% over the past year, but manual pen testing uncovered far more business-critical flaws. (Astra)
- Critical vulnerability findings rose 83% year over year, with attackers increasingly chaining low-severity issues into high-impact exploit paths. (Astra)
AI in Penetration Testing and Cybersecurity
- 13% of organizations reported breaches of AI models or applications, and 97% of those lacked proper AI access controls. (IBM)
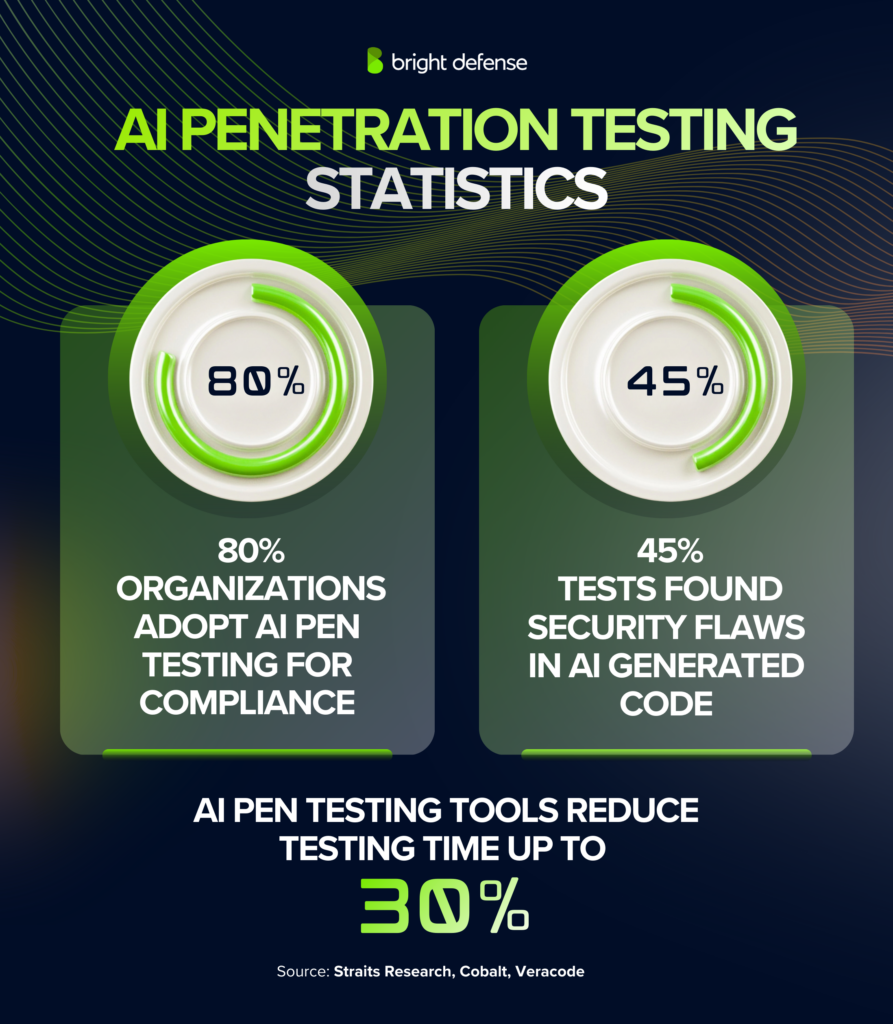
- AI-generated code introduced risky security flaws in 45% of tests across more than 100 models. (Veracode)
- AI-related vulnerability reports grew 210% in 2025, while prompt injection reports rose 540%, making prompt injection the fastest-growing AI attack vector. (HackerOne)
- AI-powered pen testing tools reduce testing time by up to 30%. (Straits Research)
- 80% of organizations cite regulatory compliance as a primary reason for adopting AI-driven pen testing solutions. (Straits Research)
- About 28% of organizations use AI-driven tools that perform reconnaissance automation, vulnerability prioritization, and attack path simulation during advanced security testing. (Black Hat Community Survey, 2025)
- Evolving cyber threats such as generative AI attacks were a top concern for 50% of security professionals, an increase of 15 percentage points from 2024. (Fortra)
- Serious findings from AI and LLM penetration tests had a median remediation time of 50 days, showing that AI-related weaknesses often remain open for long periods. (Cobalt)
Penetration Testing ROI

- 92% of respondents used a third-party penetration testing company in some capacity. (Core Security)
- 72% said rigorous penetration testing had prevented a breach at their organization. (Core Security)
- PTaaS delivered 50% faster time-to-results versus traditional consulting in the scenario studied. (Cobalt)
- PTaaS produced 25% lower management costs in the same analysis. (Cobalt)
- PTaaS produced 56% lower direct fees, with $22,900 saved per test. (Cobalt)
- Critical applications should be tested once a quarter according to a published penetration testing metrics report. (Cobalt)
- 42% of respondents said they actively used time-to-fix as a penetration testing metric. (Cobalt)
Breach Costs and Impact
- Global breach costs declined for the first time in 5 years, with the US $4.44 million global average representing a 9% decrease from 2024. (IBM)
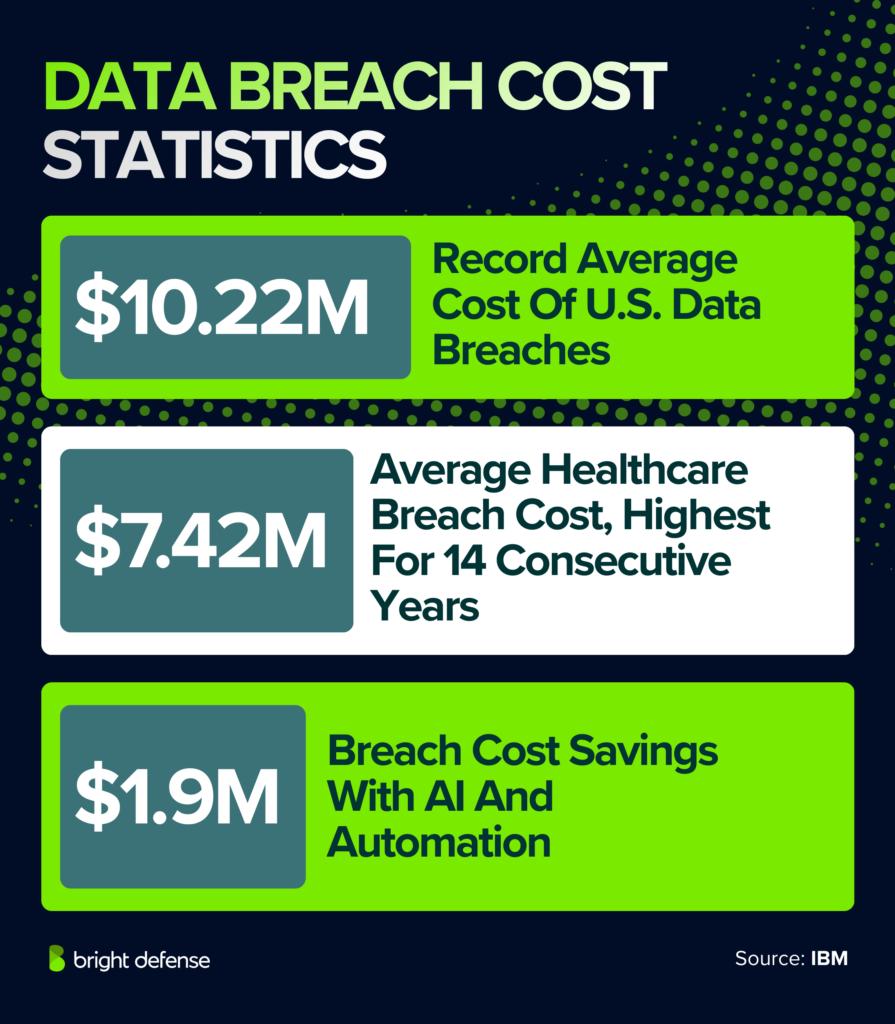
- U.S. breaches hit a record US $10.22 million on average. (IBM)
- Healthcare organizations remained the costliest industry for breaches at USD 7.42 million per incident for the fourteenth consecutive year. (IBM)
- Organizations using AI and automation extensively saved an average of $1.9 million in breach costs and reduced the breach lifecycle by 80 days. (IBM)
- Breaches involving unsanctioned AI systems added about $670,000 to the average price tag. (IBM)
- Shadow AI breaches cost organizations USD 4.63 million on average. (IBM)
- Malicious insider attacks cost an average $4.92 million per breach. (IBM)
- Third-party or supply chain security breaches averaged $4.91 million and took the longest to resolve at 267 days. (IBM)
- Breaches across multiple environments averaged $5.05 million, while on-premises breaches averaged $4.01 million. (IBM)
- Ransomware victims who disclosed incidents faced average costs of $5.08 million despite a majority refusing to pay. (IBM)
- Customer data including PII was compromised in 53% of all breaches, while intellectual property carried the highest per-record cost at $178. (IBM)
- $900,000 in breach-cost savings was associated with internal detection versus attacker disclosure. (IBM)
- The mean time to identify and contain a breach dropped to 241 days, the lowest in 9 years. (IBM)
- More than half of organizations that suffer a breach do not plan to increase security investments; only 49% plan post-breach investments. (IBM)
- 63% of breached organizations lacked AI governance or were still developing policies. (IBM)
Attack Vectors and Threat Patterns
- Exploiting vulnerabilities is now the initial access vector in 20% of breaches, up 34% year-over-year. (Verizon)
- Credential abuse remains the most common initial access vector at 22% of breaches, often tied to broken access control and weak authentication. (Verizon)
- Incidents involving a third party doubled from 15% to 30%. (Verizon)
- Human error and involvement was a factor in 60% of breaches. (Verizon)
- Espionage-motivated breaches rose to 17% of incidents, a 163% increase, with 70% leveraging vulnerability exploitation. (Verizon)
- Ransomware appeared in 44% of breaches, up from 32%, a 37% increase year-over-year. (Verizon)
- SMBs experienced ransomware in 88% of their breaches, compared to 44% for large organizations. (Verizon)
- The median ransom payment decreased to $115,000, and 64% of victims refused to pay. (Verizon)
- Only about 54% of perimeter device vulnerabilities were fully remediated; patching took a median 32 days. (Verizon)
- Edge-device and VPN vulnerabilities accounted for 22% of exploitation incidents, an eightfold increase from 3%. (Verizon)
- The median time to remediate secrets leaked via third-party GitHub repositories was 94 days. (Verizon)
- 46% of compromised systems in infostealer logs were non-managed devices. (Verizon)
- Credential dumps appeared in 54% of ransomware victim domains and 40% contained corporate emails, increasing the risk of sensitive data exposure. (Verizon)
- 15% of employees accessed generative-AI systems on corporate devices every 15 days; 72% used personal emails and 17% used corporate emails without integrated authentication. (Verizon)
- Roughly 16% of breaches involved attackers using generative AI. (IBM)
- AI-generated text in malicious emails doubled over 2 years. (Verizon)
- NIST registered 40,000 CVEs in 2024, up from 28,000 in 2023. (NIST via Verizon DBIR)
- Time-to-exploit dropped from 32 days in 2022 to just 5 days in 2023-2024, including remote code execution vulnerabilities. (Mandiant/Google via CyberMindr)
- Only about 3% of all disclosed vulnerabilities carry meaningful real-world risk. (Industry aggregate, 2024)
- A majority of ransomware victims do not involve law enforcement, with only 40% engaging authorities in 2025. (IBM)
Cybersecurity Priorities, Outsourcing, and Skills
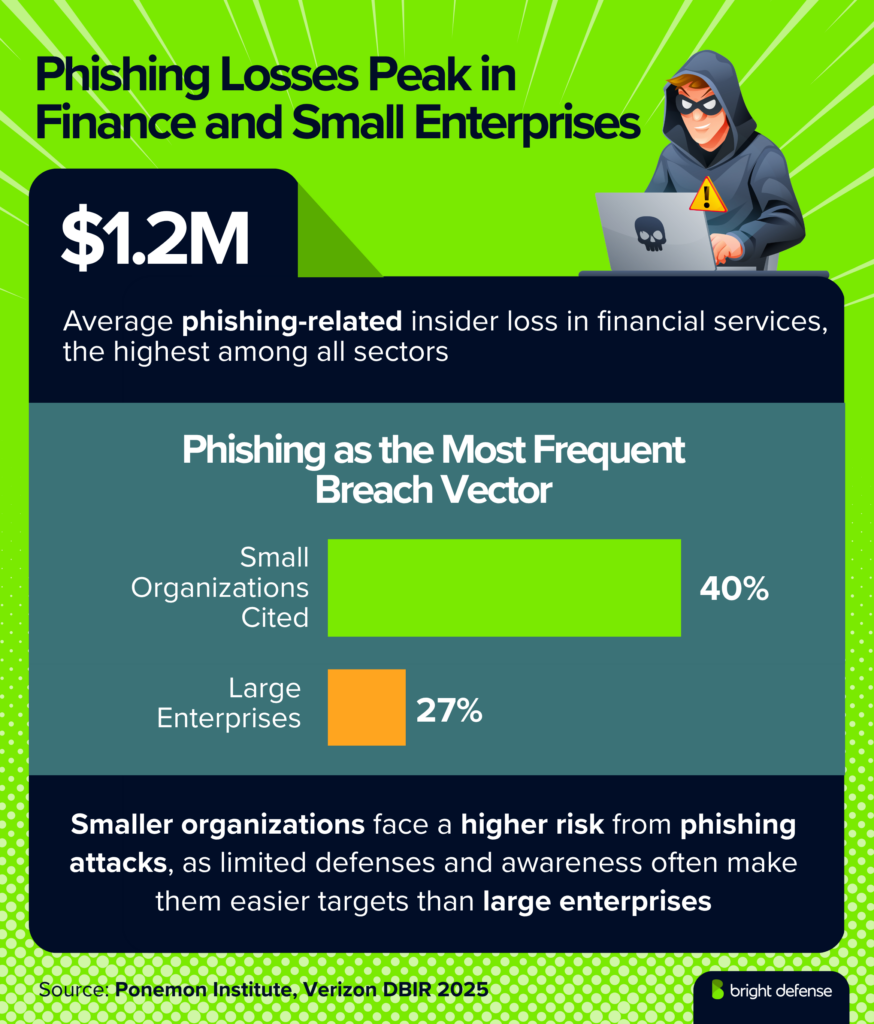
- 83% of respondents identified phishing and smishing as top security risks. (Fortra)
- Malware and ransomware were top risks for 71%. (Fortra)
- 60% listed social engineering among top threats. (Fortra)
- 58% cited accidental data loss, insecure data storage, and excessive data exposure as concerns. (Fortra)
- 59% of respondents pointed to budget limitations as a major challenge. (Fortra)
- 77% plan to identify vulnerabilities and close security gaps in the next 6 to 12 months. (Fortra)
- 75% are focused on improving security culture and awareness. (Fortra)
- 45% reported a skills gap, up 6 points from 2024. (Fortra)
- 44% struggle to balance security with business efficiency. (Fortra)
- Penetration testing is the most outsourced function: 60% plan to outsource pentesting to an external penetration testing company. (Fortra)
- 56% intend to outsource email security and anti-phishing. (Fortra)
- 47% will outsource vulnerability management program support. (Fortra)
- Zero-day attack concern dropped from 50% to 38%, suggesting improved detection tools. (Fortra)
- Only 14% of U.S. CISOs trust the government to protect the private sector, and 22% say they cannot rely on government support at all. (Pentera)
- CISA states more than 90% of successful cyber-attacks start with a phishing email. (CISA)
Vulnerability and Exploitation Trends
- Around 69% of all vulnerabilities are accounted for by CVEs with a network attack vector. (RiskBased Security)
- 28,695 vulnerabilities were unearthed in 2020. (RiskBased Security)
- 82% of respondents in a vulnerability management survey rely on the prioritization of vulnerabilities. (SANS)
- Nearly 78% of those respondents prioritize vulnerabilities using CVSS severity rating. (SANS)
- 73% of surveyed organizations believe that exploitability goes beyond CVSS severity and rely on a risk-based approach to prioritization. (SANS)
- 52% of organizations patch or resolve critical vulnerabilities and security risks within a week. (Industry aggregate)
- The implementation of zero trust and multifactor authentication measures is only prioritized by 33% of organizations. (Endpoint Security Trends Report)
- The TAC Security survey reveals that 88% of businesses review security risks on their own rather than relying on a vulnerability management solution. (TAC Security)
- More than 1,000 high-risk vulnerabilities with CVSS 10.0 have appeared in recent years. (Cyphere)
- 62% of tested systems contain several vulnerability types, including cross site scripting, server security misconfiguration, and critical issues together. (Cyphere)
- 73% of successful corporate breaches involve web application vulnerabilities. (Kaspersky Lab)
- The most vulnerable points for a security breach are applications at 35% and networks at 21%. (Broadcom/VMware)
Check Out More Stat Based Articles:
Penetration Testing Jobs and Salary Statistics
The U.S. recorded 22,075 online job postings for pentesters in 2021, rising to 27,409 in 2022. Employers frequently require Information Security, Penetration Testing, Linux, Python, and Java as technical skills, and about 66% of listings require a bachelor's degree.
The average U.S. salary for penetration testers reached $101,446 in 2022. Entry-level professionals earn about $70,324, mid-career testers with 5 to 9 years earn approximately $110,251, and senior specialists with 10 to 19 years can reach $120,953.
The workforce remains heavily skewed: 13% of ethical hackers are women and 87% are men. Unfilled cybersecurity positions grew from 1 million in 2013 to 3.5 million in 2021, and the BLS projects 35% job growth for information security analysts between 2021 and 2031. Gartner predicts that 25% of cybersecurity leaders will leave the field entirely due to work-related stress, creating additional downstream demand for skilled penetration testers.
| Country | Average Salary |
|---|---|
| Germany | €58,151 per year |
| Netherlands | €44,352 per year |
| France | €42,624 per year |
| Italy | €30,968 per year |
| United Kingdom | £38,702 per year |
Tools and Technologies Used in Penetration Testing
Penetration testing relies on specialized tools for vulnerability discovery, exploitation simulation, network analysis, and attack path validation. Survey data from the 2025 Black Hat community highlights adoption rates among application security and penetration testing professionals.
| Penetration Testing Tool | Primary Use | Adoption Rate |
|---|---|---|
| Burp Suite Pro | Web application security testing | 78% |
| Nmap | Network discovery and port scanning | 72% |
| Metasploit Framework | Exploitation and attack simulation | 65% |
| Nessus | Automated vulnerability scanning | 61% |
| Wireshark | Packet capture and network traffic analysis | 58% |
| SQLMap | SQL injection detection and exploitation | 49% |
| OWASP ZAP | Open source web application security testing | 42% |
| Cloud Security Posture Management Tools | Cloud configuration and risk monitoring | 35% |
Open-source tools remain central to most testing programs. The CoreSecurity penetration testing report found that 72% of companies rely on open-source penetration testing tools, while 50% use commercial alternatives. When evaluating paid tools, 69% of companies prioritize reporting capabilities, 64% value multi-vector testing, and 58% want automation of redundant tasks.
Cloud Security Posture Management platforms such as Prisma Cloud and Wiz appear more frequently in penetration testing workflows as organizations shift workloads into cloud infrastructure.
Automation adoption remains uneven. Only 29% of organizations have automated 70% or more of their security testing, and just 44% have incorporated security tests into coding workflows. 66% of organizations automated test builds, yet only 52% follow through with CI-integrated automated security testing.
Cost and Return on Investment of Penetration Testing
Penetration testing costs vary according to scope, system complexity, and testing depth. The following ranges reflect common market pricing across several testing categories.
| Type of Penetration Test | Typical Cost Range |
|---|---|
| Web Application Pen Test | $4,500 to $15,000 |
| Network Infrastructure Pen Test | $6,000 to $20,000 |
| Red Team Exercise | $20,000 to $100,000+ |
| Social Engineering Test | $3,000 to $10,000 |
Pricing depends on the size of the environment, the number of in-scope assets, and testing depth. A focused single-app web test typically falls at the lower end, while red team exercises carry the widest range because they simulate full-scale attack campaigns across networks, applications, and social engineering vectors over extended timeframes.
The financial case for penetration testing ties directly to breach economics. The global average breach cost reached $4.44 million in 2025 and the average U.S. breach hit $10.22 million, while organizations using AI and automation extensively saved $1.9 million per breach and shortened the breach lifecycle by 80 days.
PTaaS models further reduce costs, delivering 56% lower direct fees and saving $22,900 per test compared to traditional consulting engagements. Even a single prevented incident can offset years of testing investment.
Effectiveness of Penetration Testing in Breach Prevention
Comprehensive security assessments through penetration testing identify exploitable weaknesses before threat actors attempt to use them. Research data highlights clear differences between organizations that test regularly and those that perform security testing infrequently.
| Security Testing Insight | Statistic |
|---|---|
| Breached organizations without a pen test in the previous year | 68% |
| Reduction in breach rates for organizations conducting quarterly tests | 53% |
| Vulnerabilities rated high or critical during pen tests | 81% |
Security assessments frequently uncover configuration weaknesses, outdated systems, and authentication flaws that attackers commonly exploit.
Effectiveness of Penetration Testing in Breach Prevention
Penetration testing identifies exploitable weaknesses before threat actors reach them. The data consistently shows that organizations running regular tests catch more vulnerabilities and spend less recovering from incidents than those that test infrequently or not at all.
67% of U.S. enterprises experienced a breach in the previous 24 months despite expanding security stacks, and 84% of pen test engagements found at least one exploitable vulnerability. Meanwhile, 72% of organizations said penetration testing had directly prevented a breach. Organizations using AI-powered security tools and proactive testing programs saved an average of $1.9 million per breach and shortened their breach lifecycle by 80 days.
Security assessments frequently uncover configuration weaknesses, outdated systems, and authentication flaws that attackers commonly exploit.
| Common Vulnerability Found in Pen Tests | Frequency |
|---|---|
| Misconfigured Cloud Storage (AWS S3, Azure Blob) | 37% |
| Outdated Software Components | 32% |
| Weak Authentication Mechanisms | 29% |
| Insecure APIs | 26% |
| Privilege Escalation Vulnerabilities | 21% |
Pentesters breached internal network perimeters in 93% of companies tested, and critical vulnerability findings rose 83% year over year as attackers increasingly chain low-severity issues into high-impact exploit paths. These numbers reinforce the value of testing beyond automated scanning, where manual pen testing uncovered nearly 2,000 times more unique vulnerabilities than scanners alone.
Regulatory Compliance Requirements That Drive Penetration Testing
| Regulation | Requirement | Adoption Impact |
|---|---|---|
| GDPR (European Union) | Requires regular security assessments | Drives testing in 41% of European firms |
| HIPAA (United States Healthcare) | Requires risk assessments for patient data systems | Leads to testing in 35% of healthcare providers |
| PCI DSS | Requires annual penetration testing for Level 1 merchants | Mandatory for payment processing security |
| ISO/IEC 27001 | Recommends periodic security testing within risk management programs | Adopted by 28% of certified organizations |
| NIS2 Directive (European Union) | Requires annual red team exercises for critical infrastructure operators | Expands testing across essential sectors |
PCI DSS sets the most explicit cadence: pen tests at least annually and after any significant change. A proposed 2025 HIPAA update moves toward mandatory annual testing. SOC 2 auditors expect pen test results as evidence for Security (CC4.1) and Vulnerability Management (CC7.1) controls. In the EU, DORA adds threat-led testing for financial entities and NIS2 expands red team obligations across essential infrastructure.
The AI Surge in Offensive Security
Artificial intelligence is reshaping penetration testing on both sides of the battlefield.
On the defensive side, multi-agent AI frameworks are automating full pen tests with minimal human input. RapidPen achieved shell access on targets within 200 to 400 seconds at under $0.60 per run. xOffense reached a 79.17% sub-task completion rate on standardized benchmarks, outperforming PentestGPT and VulnBot.
Threat actors are moving just as fast. HexStrike-AI, an open-source framework integrating over 150 security tools with LLM orchestration, was weaponized within hours of release to exploit Citrix NetScaler zero-days. Check Point researchers noted that exploitation timelines collapsed from weeks to under 10 minutes. Villager, an AI-native framework combining Kali Linux with DeepSeek AI, hit over 11,000 downloads on PyPI within two months of its July 2025 release.
Organizations that fail to integrate AI-augmented pentesting into their security programs risk falling behind attackers who already have.
What This Means for Security Leaders
Penetration testing simulates real-world cyberattacks against systems, networks, and applications, exposing exploitable vulnerabilities that automated scanners frequently miss. Phishing simulations still produce click rates between 10% and 20%, and password reuse, weak credentials, and absent multi-factor authentication remain among the most common findings.
IBM's 2025 Cost of a Data Breach Report documented a global average breach cost of $4.44 million. Organizations using AI-powered security tools saved an average of $1.9 million per breach and shortened their breach lifecycle by 80 days. Over 70% of firms now use PTaaS, and 85% increased pen test spending over the past year.
Cyber insurance carriers increasingly tie premium discounts to independent pen test results, pushing penetration testing from a discretionary activity toward a financial requirement.
| Factor | Detail |
|---|---|
| High-Risk Vulnerabilities | More than 1,000 CVSS 10.0 vulnerabilities have appeared in recent years |
| Compliance | 75% of security professionals run pen tests to meet compliance mandates |
| Third-Party Testing | 58% of organizations rely on external penetration testing providers |
| Web Application Risk | 73% of successful corporate breaches involve web application vulnerabilities |
| Multiple Vulnerabilities | 62% of tested systems contain several vulnerability types together |
| Maintaining Standards | 66% of organizations struggle to maintain strong security practices |
| Repeat Testing | 40% of pentest engagements occur for repeat clients |
| AI Impact | AI acts both as a testing tool and a new attack surface |
| Cloud and API Security | Cloud environments and APIs require dedicated penetration testing |
| Human Element | Social engineering and employee mistakes still succeed during pentests |
How Bright Defense Can Help With Penetration Testing
Bright Defense helps organizations uncover real security weaknesses before attackers can take advantage of them. Our penetration testing services examine web applications, APIs, cloud environments, networks, and internal systems with real-world attack methods that reveal where your defenses may break down.
We focus on practical findings, clear risk context, and remediation guidance your team can use to strengthen security without wasting time on vague results. You can learn more through our Penetration Testing Services, our guide on What Penetration Testing Is, and our overview of Penetration Testing Pricing.
FAQ
Verizon's DBIR team reported 22,052 real-world security incidents and 12,195 confirmed data breaches across 139 countries, which is one reason DBIR numbers are widely used to justify recurring pentests and retests after major changes.
Vulnerability exploitation reached 20% as an initial access vector, which supports prioritizing external attack-surface testing and validating fixes with targeted retesting, not only scanning.
Verizon reported only about 54% of edge-device and VPN vulnerabilities were fully remediated, with a median of 32 days to remediate, which is a practical argument for testing critical perimeter services regularly and confirming patch outcomes.
Verizon reported ransomware was present in 44% of breaches, the median payment was $115,000, and 64% of victim organizations did not pay, which makes ransomware-focused testing of identity, segmentation, backups, and recovery workflows a recurring priority.
Fortune Business Insights projects the penetration testing market grows from $3.09B in 2026 to $7.41B by 2034, while MarketsandMarkets projects growth from $1.98B in 2025 to $4.39B by 2031, which signals sustained demand even as tooling becomes more automated.
PCI guidance states penetration testing must be performed at least annually and after any significant change, which is why many teams adopt a similar cadence outside PCI when systems handle sensitive data or internet-facing services.
Core Security's survey report says common program changes included added emphasis on network security tests at 36% and phishing campaigns or social engineering at 30%, which reflects broader scope moving beyond web apps alone.
Core Security reported only 9% said compliance needs had no impact on their pen testing strategy, and the report notes this was down 7% from the prior year, which suggests compliance is still a major driver for what gets tested and how often.
IBM reported a global average data breach cost of $4.4M in its 2025 Cost of a Data Breach report, which is frequently cited to justify funding for offensive testing plus remediation and retesting cycles.
Verizon's median remediation time of 32 days for perimeter device vulnerabilities and the 20% initial-access share tied to vulnerability exploitation support a practical workflow where major releases, perimeter exposure changes, or new integrations trigger targeted retesting rather than waiting for an annual test.
PTES says the standard consists of 7 main sections: Pre-engagement Interactions, Intelligence Gathering, Threat Modeling, Vulnerability Analysis, Exploitation, Post Exploitation, and Reporting. (Penetration Testing Execution Standard)
CISA states more than 90% of successful cyber-attacks start with a phishing email. (CISA)
MarketsandMarkets projects the market grows from USD 1.98 billion in 2025 to USD 4.39 billion by 2031, at 14.2% CAGR. Mordor Intelligence projects the market grows from USD 2.36 billion in 2025 to USD 5.54 billion by 2031, at 15.29% CAGR.
The 80/20 rule is a prioritization heuristic stating that 80% of outcomes often come from 20% of causes, so teams focus first on the highest-impact risks and controls. (Investopedia)
15. How long does it take to fix a serious pentest finding?
The median time to resolve a serious pentest finding is 50 days across all categories. Larger firms with over 5,001 employees take 61 days, while smaller firms with 1 to 100 employees resolve serious findings in 27 days. (Cobalt)
16. What percentage of pentest findings actually get fixed?
Only 48% of all pentest findings ever get resolved. Serious findings fare better at a 69% resolution rate. AI/LLM pentest findings have the lowest resolution rate at 21.1%. (Cobalt)
17. How does PTaaS compare to traditional penetration testing on cost?
PTaaS delivered 50% faster time-to-results, 25% lower management costs, and 56% lower direct fees, saving $22,900 per test versus traditional consulting. (Cobalt)
18. How much do organizations spend on penetration testing annually?
U.S. enterprises spend an average of USD 187,000 annually on pentesting, about 10.5% of their total IT security budgets. More than 50% of CISOs plan to increase their pentesting budgets in 2025. (Pentera)
19. What are the fastest-growing AI attack vectors relevant to penetration testing?
AI-related vulnerability reports grew 210% in 2025, and prompt injection reports rose 540%, making prompt injection the fastest-growing AI attack vector. AI-generated code introduced risky security flaws in 45% of tests across more than 100 models. (HackerOne, Veracode)
Get In Touch