Updated:
April 29, 2026
CCPA Cybersecurity Audit 101: Requirements & How to Prepare
The CCPA cybersecurity audit is a mandatory annual review under Article 9 of California’s regulations that takes effect on January 1, 2026 and assesses how a business protects personal data across 18 control areas.
The results are reported by an independent auditor and a senior executive must certify the outcome to the California Privacy Protection Agency (CPPA).
Strong security practices now shape both compliance and customer trust, with a majority of consumers unwilling to do business with companies that raise security concerns.
This guide explains who must complete the audit, what the 18 control areas cover, how compliance deadlines apply across revenue tiers, and the key preparation steps before certification so organizations understand what is required to meet California’s privacy and security expectations.
Key Takeaways
- CCPA cybersecurity audit obligations are enforceable January 1, 2026, regardless of certification deadline
- CCPA certification is due April 1, 2028, 2029, or 2030 depending on revenue tier
- Fines reach $2,663 per violation and $7,988 for intentional violations or those involving minors. Each affected consumer counts separately. The CPPA has discretion to grant cure opportunities or skip to enforcement.
- NIST CSF 2.0 audits can satisfy CCPA requirements alone or with supplementation. SOC 2 and ISO 27001 work with a gap analysis against the 18 components in § 7123(c). The auditor decides which components apply.
- CCPA auditors require tested evidence, not written policies. Retain all records for five years
What is the CCPA Privacy Law?
The CCPA is California’s privacy law that gives residents more control over their personal information and places clear obligations on businesses that collect, use, share, or sell that data.
The law grew out of rising concern over major data-misuse scandals, a weak patchwork of privacy rules in the United States, and the global impact of the GDPR, which pushed privacy into the center of business and regulatory discussions. Businesses operating under both regimes often ask how GDPR and CCPA differ and where their obligations overlap.
California first passed the CCPA in 2018, and major amendments were signed on October 11, 2019. Under the law, personal information includes identifiers such as names, aliases, postal addresses, IP addresses, email addresses, Social Security numbers, driver’s license numbers, license plate numbers, passport numbers, and other data that can identify a person or household.
The CCPA gives California residents the right to know the following information collected by businesses:
- What personal information is collected
- Whether it is sold or disclosed and to whom
- Opt out of the sale of personal information
- Access their data
- Request deletion in many cases
- Discrimination for exercising those rights
A business falls under the CCPA when it meets at least one of these thresholds:
- It has annual gross revenue of more than $26,625,000 (the inflation-adjusted threshold for 2025, updated from the original $25 million baseline).
- It buys, sells, or shares the personal information of 100,000 or more California consumers or households per year.
- It derives 50% or more of annual revenue from selling or sharing consumers’ personal information.
The CCPA applies to out-of-state businesses that do business in California and meet at least one of these thresholds. Physical presence in California is not required.
Who Must Complete a CCPA Cybersecurity Audit?
A CCPA cybersecurity audit is required for businesses whose processing of consumers’ personal information presents significant risk to consumers’ security under Article 9 of the California regulations.
A business must complete a CCPA cybersecurity audit when it is subject to the CCPA and its processing presents significant risk to consumer security. Two pathways trigger the audit requirement.
The first pathway applies to any business that derives 50% or more of annual revenue from selling or sharing consumers’ personal information.
The second pathway applies to any business with annual gross revenue above $26,625,000 that also processes the personal information of 250,000 or more California consumers or households, or the sensitive personal information of 50,000 or more California consumers.
Nonprofits and government agencies are generally not covered by the CCPA.
Categories of businesses commonly affected include:
- Data brokers
- Ad-tech companies
- Retail media networks
- E-commerce platforms
- SaaS platforms
- Marketing and CRM providers
- Health-tech companies
- Fintech and payments companies
How SOC 2 and ISO 27001 Support CCPA Audit Readiness
SOC 2 and ISO 27001 support CCPA audit readiness because they give businesses a documented control environment, repeatable security processes, and third-party assessed evidence that can carry forward into Article 9 preparation.
SOC 2 examines controls relevant to security, availability, processing integrity, confidentiality, and privacy, while ISO/IEC 27001 defines the requirements for an information security management system built around risk management and continual improvement.
Those frameworks do not replace the CCPA cybersecurity audit, but they can make readiness easier because their policy, access control, logging, vendor management, incident response, and evidence practices align closely with the control areas California requires auditors to assess.
The California regulations expressly state that a business may use a cybersecurity audit, assessment, or evaluation prepared for another purpose, provided it meets Article 9 on its own or through supplementation.
The practical takeaway is that SOC 2 and ISO 27001 can reduce audit preparation work and strengthen audit evidence, though your team still needs to confirm that every CCPA-specific requirement is fully covered.
What the CCPA Cybersecurity Audit Evaluates
The CCPA cybersecurity audit evaluates whether a business’s cybersecurity program is properly established, documented, maintained, and enforced to protect personal information from unauthorized access, destruction, use, modification, disclosure, and loss of availability.
The audit reviews controls across 18 areas, including authentication, encryption, access controls, vulnerability testing, network security, incident response, and business continuity.
The audit report must explain the systems reviewed, the criteria used, the evidence examined, and how effective those controls are in preventing security failures.
Breakdown of the 18 Audit Control Areas
Section 7123(c) of California’s regulations identifies the 18 control areas that the auditor must assess, where applicable:
- Authentication – Reviews multi-factor authentication and strong, unique passwords or passphrases used to protect access to systems and data.
- Encryption of Personal Information – Examines whether personal information is encrypted both at rest and in transit.
- Account Management and Access Controls – Reviews least-privilege access, privileged account limits, account creation controls, and physical access restrictions for personal information.
- Inventory and Management of Personal Information and Systems – Examines data inventories, data mapping, classification, tagging, hardware and software inventories, allowlisting, and device approval processes.
- Secure Configuration of Hardware and Software – Reviews software updates, cloud and on-premises security settings, masking of sensitive data, patch management, and change management practices.
- Vulnerability Scans and Penetration Testing – Examines internal and external scans, penetration testing, and vulnerability disclosure or reporting programs such as bug bounty processes.
- Audit-Log Management – Reviews the centralized storage, retention, and monitoring of logs.
- Network Monitoring and Defenses – Examines detection and prevention tools such as bot detection, intrusion detection, intrusion prevention, and data loss prevention systems.
- Antivirus and Antimalware Protections – Reviews safeguards that detect and block malicious software.
- System Segmentation – Examines whether the business separates systems appropriately through tools such as firewalls, routers, and switches.
- Control of Ports, Services, and Protocols – Reviews whether unnecessary ports, services, and protocols are limited or restricted.
- Cybersecurity Awareness – Examines how the business keeps current with changing cyber threats and countermeasures.
- Cybersecurity Education and Training – Reviews security training for employees, contractors, and other personnel with system access, including onboarding, annual training, and post-breach training.
- Secure Development and Coding Best Practices – Examines secure coding, code review, and testing practices used during software development.
- Oversight of Service Providers, Contractors, and Third Parties – Reviews how the business monitors outside parties for compliance with CCPA contract obligations and security requirements.
- Data Retention and Disposal – Examines whether retention schedules are enforced and personal information is disposed of securely when no longer needed.
- Incident Response – Reviews plans and procedures for detecting, responding to, and recovering from security incidents.
- Business Continuity and Disaster Recovery – Examines how the business maintains operations and recovers data after major disruptions or disasters.
What Steps Should to Take to Prepare for a CCPA Cybersecurity Audit?
Preparing for your first CCPA cybersecurity audit starts with an internal review to assess your program, map it to the 18 control areas, fix gaps, gather evidence, and then engage an independent auditor.
A strong preparation process usually follows these 5 steps:
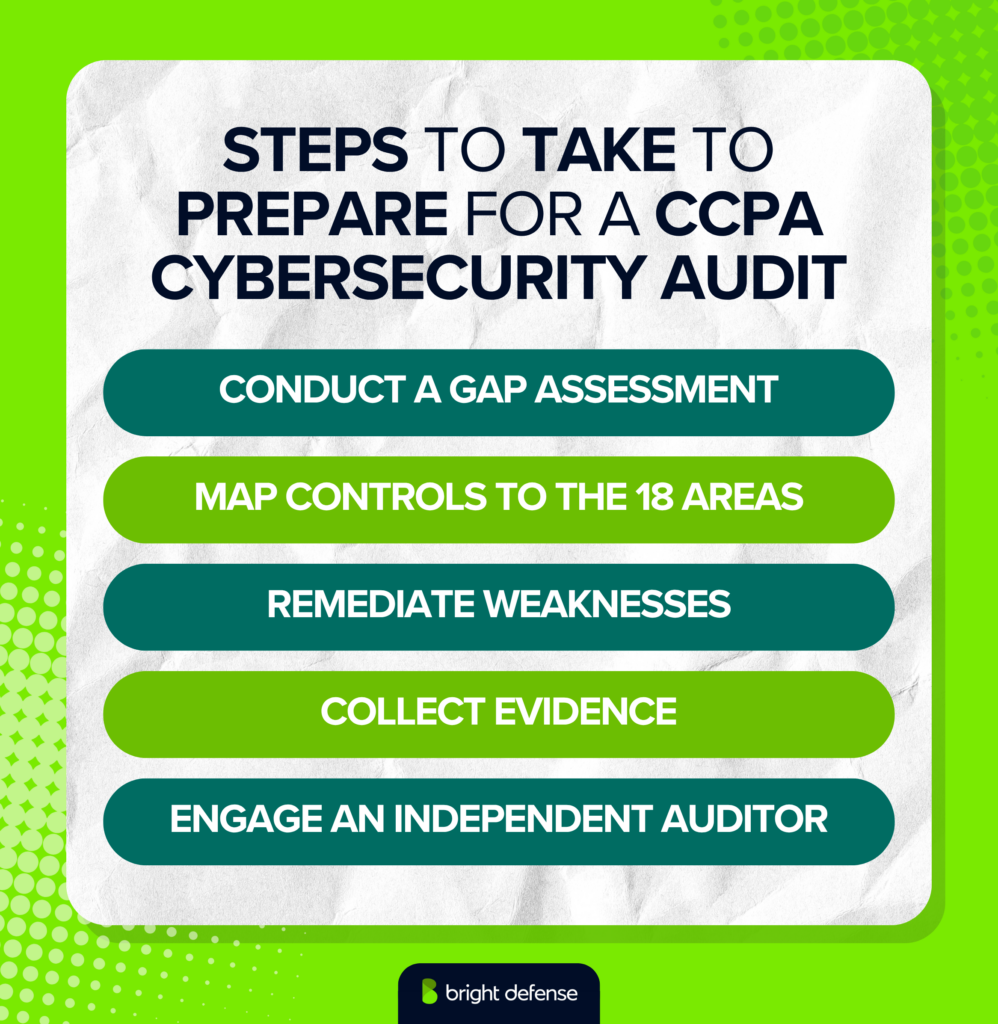
1. Conduct a Gap Assessment
Review your current cybersecurity program, written policies, procedures, technical safeguards, and governance records against what the regulation says the audit must assess: the establishment, implementation, maintenance, and enforcement of your cybersecurity program. This step should identify where controls are missing, informal, outdated, or not consistently followed.
2. Map Controls to the 18 Areas
Build a control matrix that ties your existing safeguards to each applicable Article 9 category, such as authentication, encryption, access control, inventory management, secure configuration, vulnerability testing, logging, network defenses, training, incident response, and disaster recovery. This gives your team a clear way to show what exists, what is in scope, and where equivalent controls may already cover a requirement.
3. Remediate Weaknesses
Fix the gaps that raise the risk of unauthorized access, disclosure, modification, destruction, or loss of availability of personal information. Focus first on high-risk weaknesses such as missing multi-factor authentication, weak logging, poor vendor oversight, incomplete retention rules, or untested incident response procedures because the audit report must describe gaps in detail and document your plan and timeframe for resolving them.
4. Collect Evidence
Assemble the proof an auditor will rely on, such as policies, standards, system inventories, training records, scan results, penetration test results, change records, incident response playbooks, vendor review materials, screenshots, sample tickets, and interviews with owners for each control. The regulation states that audit findings must rely primarily on specific evidence, including documents reviewed, sampling and testing performed, and interviews conducted, rather than management assertions alone.
5. Engage an Auditor
Select a qualified, objective, independent auditor who uses accepted professional auditing standards and give that auditor access to the information needed to define scope, criteria, and testing. A business may use an existing audit, assessment, or evaluation prepared for another purpose, though it must be supplemented where needed to satisfy Article 9 in full.
Preparation does not end with fieldwork. Your team should keep the evidence file, remediation tracker, and control matrix in one place because the business and auditor must retain audit-related documents for at least 5 years and the business must later submit an annual certification to the CPPA.
How Long Does A CCPA Cybersecurity Audit Take?
A first time CCPA cybersecurity audit usually takes about 8 to 16 weeks for organizations with a reasonably mature security program, while companies with major control gaps or weak documentation may need 4 to 6 months. This timeline reflects the work involved in scoping the audit, mapping controls, collecting evidence, fixing weaknesses, supporting independent testing, and preparing for certification.
The following is a practical timeline most businesses can expect.
- Scoping And Gap Assessment: 1 To 2 Weeks: This phase defines what systems, data, teams, and vendors fall within scope and identifies the most important control gaps.
- Control Mapping And Evidence Collection: 2 To 4 Weeks: This phase maps existing safeguards to the 18 audit areas and gathers the records an auditor will review, such as policies, logs, training records, scan results, and incident response materials.
- Remediation Of Key Gaps: 2 To 8 Weeks Or Longer: This phase takes the most time because missing controls, weak processes, or limited documentation often need correction before the audit begins.
- Independent Audit Testing And Reporting: 2 To 4 Weeks: The auditor reviews scope, tests controls, examines evidence, conducts interviews, and prepares the audit report.
- Executive Review And Certification Preparation: 1 To 2 Weeks: This final stage covers remediation follow up, internal signoff, and preparation for the written certification submitted to the CPPA.
How Much Does A CCPA Cybersecurity Audit Cost?
A CCPA cybersecurity audit costs about $40,000 to $360,000 in first-year direct compliance costs, depending on company size, scope, and whether the business already uses an existing security framework.
The CPPA’s Standardized Regulatory Impact Assessment (October 2024) estimates per-firm first-year compliance costs by revenue tier:
- $39,375 to $56,250 for businesses under $100 million in revenue
- $105,000 to $150,000 for businesses between $100 million and $1 billion
- $253,750 to $362,500 for businesses above $1 billion
Figures reflect 2022 dollars and include internal labor for smaller firms that conduct the audit in-house. Subsequent audits are modeled at 15% to 30% of first-year cost, with the decline gradual across successive years. Remediation, tools, consulting, and internal preparation should be budgeted separately.
What Are the Penalties & Enforcement Risks Under a CCPA Cybersecurity Audit?
Failing to complete a required CCPA cybersecurity audit creates regulatory, financial, and litigation exposure because violations of the audit rule are treated as violations of the CCPA.
The following are the main enforcement and penalty risks businesses face.
1. Administrative Enforcement And Fines
The CPPA can investigate, order a business to stop non-compliant practices, and impose fines of up to $2,663 per violation or $7,988 per intentional violation, including cases involving minors’ data. These amounts reflect the 2025 CPI adjustment and remain in effect through 2026. The per-violation structure creates cumulative exposure since each affected consumer or day of non-compliance may count separately, which goes to show how quickly penalties can scale into significant totals.
2. Regulatory Oversight And Audit Obligations
The CPPA leads administrative enforcement, while the California Attorney General can bring civil actions in court. Both authorities can request cybersecurity audit records within 30 days, and businesses must retain those records for at least 5 years. A business submits only a certification of completion each year, while full audit reports remain on file until requested during an investigation.
3. Timing Of Enforcement Risk
The cybersecurity requirements take effect on January 1, 2026, while certification deadlines follow a phased schedule through 2030. Enforcement risk begins in 2026 regardless of reporting deadlines, which means businesses may face penalties before their first certification is due.
4. Private Right Of Action And Breach Liability
Consumers can file lawsuits after a qualifying data breach when personal information is exposed due to failure to maintain reasonable security practices. Statutory damages range from $107 to $799 per consumer per incident, or actual damages, whichever is greater. Class actions can multiply this exposure into tens or hundreds of millions when large datasets are affected.
5. Litigation Impact Of Audit Findings
Cybersecurity audits often become key evidence in post-breach litigation. A completed audit that identifies risks and documents remediation supports a defensible position. A missing or incomplete audit weakens that position and signals failure to meet California’s defined security expectations.
6. Enforcement Trends And Activity
Recent enforcement activity shows increasing regulatory pressure. The CPPA issued multimillion-dollar penalties in 2025 and continues to process a high volume of consumer complaints and active investigations, which confirms that audit compliance is a practical requirement rather than a theoretical obligation.
What Are the Key Priorities for CCPA Cybersecurity Audit Readiness?
CCPA cybersecurity audit readiness focuses on scope, evidence, and ongoing control performance rather than documentation alone. The following are the key priorities organizations must address to prepare for the audit.
1. Defined Audit Scope
A defensible scope starts with showing why the audit covers the systems, data, business units, and third-party relationships that matter most under the rule.
The statute expressly links audit scope to the size and complexity of the business and the nature and scope of its processing activities, and the final regulations require the auditor to assess the business’s information system and the policies, procedures, and practices selected for review.
In practice, companies need a clear rationale for what sits in scope, what sits out of scope, and how personal information moves across applications, infrastructure, vendors, and business processes.
2. Mapped Controls And Evidence
The audit rule is written around concrete control areas, not general promises. The regulation points to control components such as authentication and phishing-resistant multifactor authentication, encryption, access controls, personal information inventories and data-flow maps, audit-log management, secure development practices, service provider oversight, retention and disposal, incident response, and disaster recovery.
Readiness therefore depends on mapping each relevant control to an accountable owner, a written policy or procedure, the system or process where the control operates, and the records that prove it is working.
3. Proven Control Effectiveness
Operating effectiveness is where many programs will stand or fall because the regulations do not allow audit findings to rest mainly on management assertions.
The auditor must rely primarily on specific evidence, including documents reviewed, sampling and testing performed, and interviews conducted, and the audit report must explain why that evidence supports the findings.
The rules even require the report to describe how the business implements and enforces compliance with its cybersecurity program, which signals that written controls alone will not be enough without repeatable execution over time.
4. Independent Audit And Governance
The audit must be carried out by a qualified, objective, independent professional using accepted auditing standards.
An internal auditor is permitted, but that person must remain free from influence and cannot participate in activities they may later assess, such as preparing the business’s documents or maintaining the cybersecurity program.
The report must go to an executive team member with direct responsibility for the cybersecurity program, which makes governance design part of readiness, not an afterthought.
5. Remediation And Compliance Timeline
The audit report must describe gaps or weaknesses, document the business’s plan to address them, and state the timeframe for resolution. Businesses must then submit a certification of completion to the CPPA by April 1 following any year in which they were required to complete the audit, and both the business and the auditor must retain relevant audit documents for at least 5 years.
The first deadlines are phased: April 1, 2028 for businesses with more than $100 million in 2026 gross revenue, April 1, 2029 for businesses between $50 million and $100 million, and April 1, 2030 for businesses below $50 million. Covered businesses will need to retain audit-related documents for at least 5 years, submit a certification of completion to the CPPA, and follow phased deadlines that begin with audit reports due in 2028, 2029, or 2030 depending on revenue tier.
How Bright Defense Supports CCPA Cybersecurity Compliance
Bright Defense supports CCPA cybersecurity compliance through deep expertise in cybersecurity frameworks, audit readiness, and regulatory requirements aligned with Article 9. We help organizations assess gaps, map controls to required areas, strengthen security practices, and maintain audit ready documentation, which ensures businesses meet regulatory expectations while building a defensible, evidence backed cybersecurity program.
Get In Touch