Updated:
May 7, 2026
160+ Password Statistics in 2026
A study of 19.03 billion leaked passwords found that 94% were reused or duplicated. Stolen credentials appeared as the initial access vector in 22% of all confirmed breaches in the 2025 Verizon DBIR.
That’s just the tip of the iceberg. Credential theft, password reuse and weak authentication habits affect every industry, age group and region. Password-specific data also sits inside a wider set of cybersecurity statistics that show how attackers, defenders and organizations are evolving each year.
To give you a full picture of where password security stands today, the team at Bright Defense has compiled a comprehensive list of up-to-date 161+ valid password statistics for 2025. In this article, you’ll find hand-picked statistics about:
- Global trends in password exposure and reuse
- Password composition and creation habits
- Password management and passkey adoption
- Credential-based attacks and initial access tactics
- Industry and country-level password patterns
- Major exposures and breach impacts
- Breach cost and recovery metrics
- Operational and human impacts of password fatigue
- Timeline shifts and future directions
Without further ado, let’s check out the stats!
Global Trends in Password Exposure & Reuse

- 19.03 billion leaked passwords were analyzed in a single study, and only 6% (1.14 billion) were unique, meaning 94% were reused across multiple accounts. (Cybernews)
- 42% of passwords were 8 to 10 characters long, with eight characters the single most common password length. (Cybernews)
- About 27% of all passwords consisted solely of lowercase letters and digits, while 19% mixed uppercase and lowercase letters, numbers and special characters, a sharp rise from 1% in 2022. (Cybernews)
- More than 24 billion credentials were exposed worldwide in 2022, with only 6.7 billion of those unique. (DemandSage)
- 6 million records were compromised in the first quarter of 2023 alone, and attackers steal about 1 million passwords every week. (DemandSage)
- 18.4 billion data points were leaked in the U.S. by 2025, including 2.28 billion passwords, and 84% of people reuse passwords, while only 34% update them monthly. (DemandSage)
- 4.5 million people continued to use the same password “123456” and 24% of Americans use easily guessable passwords such as “abc123” or “123456.” (DemandSage)
- 35% of individuals believe their account compromises were due to weak passwords, and 27% blame company-wide data breaches. (Secureframe)
- Employees reuse the same password an average of 13 times, and small-business employees manage around 85 passwords, with 63% using their company mobile device for personal tasks. (DemandSage)
- 92% of IT professionals reuse passwords, and 46% of users had at least one password stolen during 2024. (Huntress)
- 24% of American adults reuse the same password for 1 to 2 accounts, 23% reuse it for 3 to 4 accounts, 14% reuse it for 5 to 6 accounts, 7% reuse it for 7 to 8 accounts, 4% reuse it for 9 to 10 accounts and 4% reuse a single password across 11 or more accounts. (Forbes)
Password Composition & Creation Habits
- The password “123456” appeared 338 million times, “1234” appeared 727 million times and the words “password” and “admin” appeared 56 million and 53 million times respectively in leaked datasets. (Cybernews)
- Only 6% of the 19 billion passwords analyzed were unique. (Cybernews)
- 24% of all passwords are exactly eight characters long, making it the most common password length. (Secureframe)
- The female name “Ana” appears in 178.8 million passwords, or about 1% of all leaked passwords. (Cybernews)
- Positive words like “love” (87 million occurrences), “sun” (34 million), “dream” (6.1 million), “joy” (6.9 million) and “freedom” (2 million) were common in the dataset. (Cybernews)
- Pop-culture references proliferate in common passwords; names such as “Mario” (9.6 million), “Joker” (3.1 million), “Batman” (3.9 million), “Thor” (6.2 million) and “Elsa” (2.9 million) were found in the dataset. (Cybernews)
- Swear words like “ass” (165 million occurrences) and “fuck” (16 million) appeared frequently in leaked credentials. (Cybernews)
- Animal names and place names were popular passwords: “lion” appeared 9.8 million times, “fox” 7.8 million, “Rome” 13 million, “summer” 3.8 million and the month “May” 28 million times. (Cybernews)
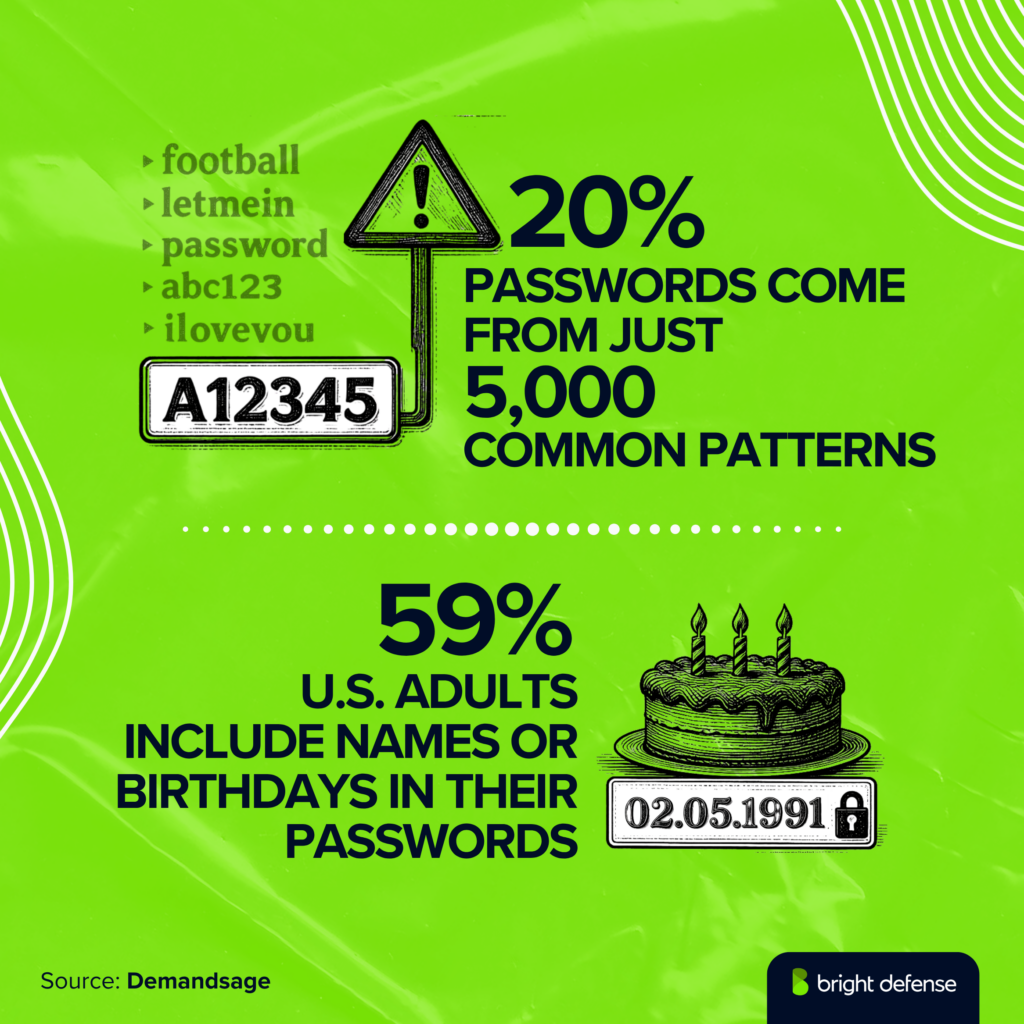
- 59% of U.S. adults include birthdays or names in their passwords, including 22% who use their own name, 33% who use a pet’s name, 14% who use a child’s name and 15% who use their partner’s name. (DemandSage)
- 15% of people use their first name in their passwords. (Secureframe)
- 20% of Fortune 500 passwords contain the company name. (Secureframe)
- Among 10 million remote desktop protocol (RDP) attack passwords, about 420,000 ended with a number between 0 and 99. (Secureframe)
Password Length and Cracking Times

- 42% of passwords fall between 8 and 10 characters, while 19% include all four character categories (uppercase and lowercase letters, numbers and symbols). (Cybernews)
- 57% of passwords include a dictionary word, and 45% can be cracked within 1 minute, 59% within 1 hour and 73% within 1 month. (Secureframe)
- Only 23% of passwords would take over a year to crack with current algorithms. (Secureframe)
- A 14-character password containing only numbers can be cracked in about 14 minutes, while adding letters extends the time to 24 years, and adding symbols increases it to 1,760 million years. (Secureframe)
- 18.82% of attacked passwords consist solely of lowercase letters, and 20% of all passwords in use are drawn from just 5,000 patterns. (Secureframe)
Variations and Reuse Practices

- 73.6% of Americans reuse passwords, and 79.1% use slight variations such as adding a number or symbol. (Casino.org)
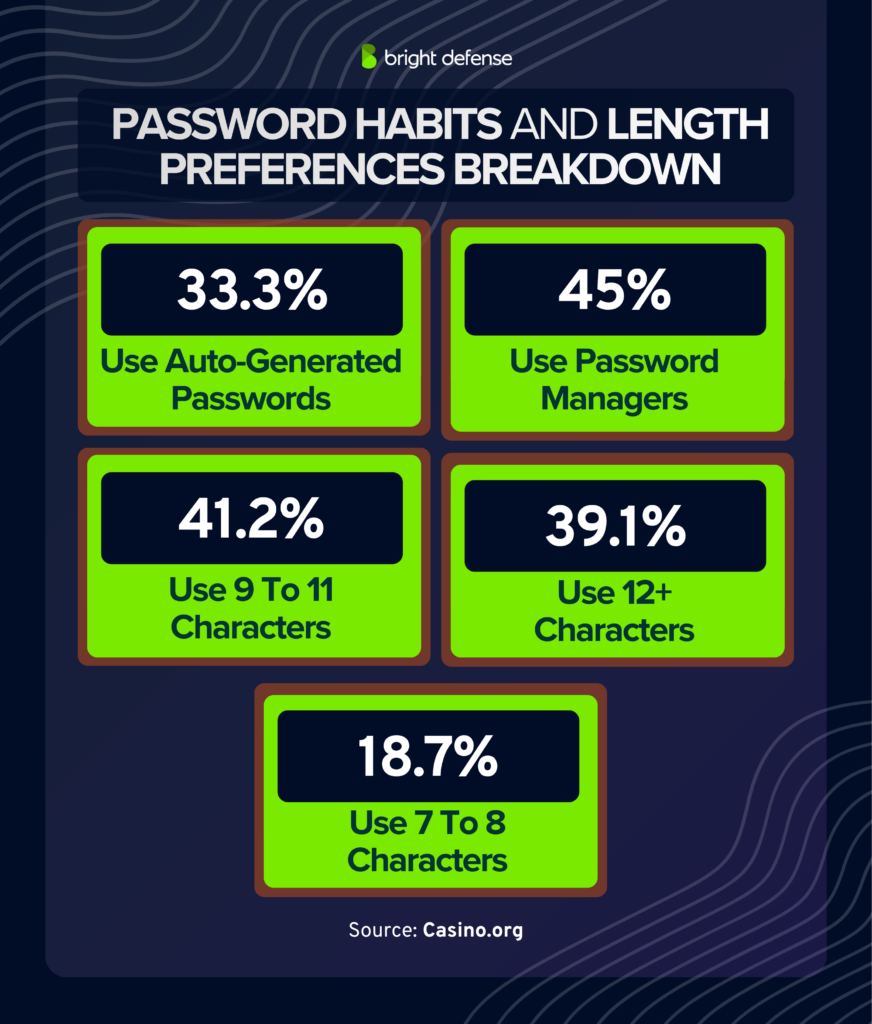
- About 33.3% use auto-generated passwords from random password generators, 45% use a password manager, 41.2% favor passwords of 9 to 11 characters, 39.1% prefer 12 or more characters, 18.7% use 7 to 8 characters and 1.1% use fewer than 6 characters. (Casino.org)
- The average number of passwords an individual maintains was 27.6, with 35.9% of respondents saying they rarely forget passwords, 17.3% forgetting a few times a month and another 17.3% claiming they never forget. (Casino.org)
- About 14.1% forget a password once a month, 8.7% weekly and 6.6% once a week. (Casino.org)
- 43% of users have not updated a password in over 5 years, 21.5% keep the same password for 1 to 3 years, 16.1% for 3 to 5 years, 9.8% update every 6 to 12 months, 7.9% every 1 to 6 months and only 1.8% update monthly. (Casino.org)
- Only 21% of Americans regularly reset passwords, while 68% had to change passwords across multiple accounts after a compromise, and 18% reuse variations of old passwords when resetting. (Secureframe)
- 54% manage passwords entirely through memory, 33% use pen and paper and 25% reuse passwords across 11 to 20+ accounts. (Bitwarden)
- 69% of Americans feel overwhelmed by the number of passwords they have to remember and 45% are anxious about password strength. (Pew Research)
- Approximately 41% write passwords down, 34% save them in their browser and 21% frequently reset them. (Pew Research)
- Among adults 65 and older, 63% admit to writing passwords down, whereas 49% of adults under 30 store passwords in their browsers. (Pew Research)
- Adoption of password managers rose from 20% in 2019 to 32% in 2023, and 49% of 18- to 29-year-olds use them. (Pew Research)
Password Management & Passkey Adoption
Password Manager Usage
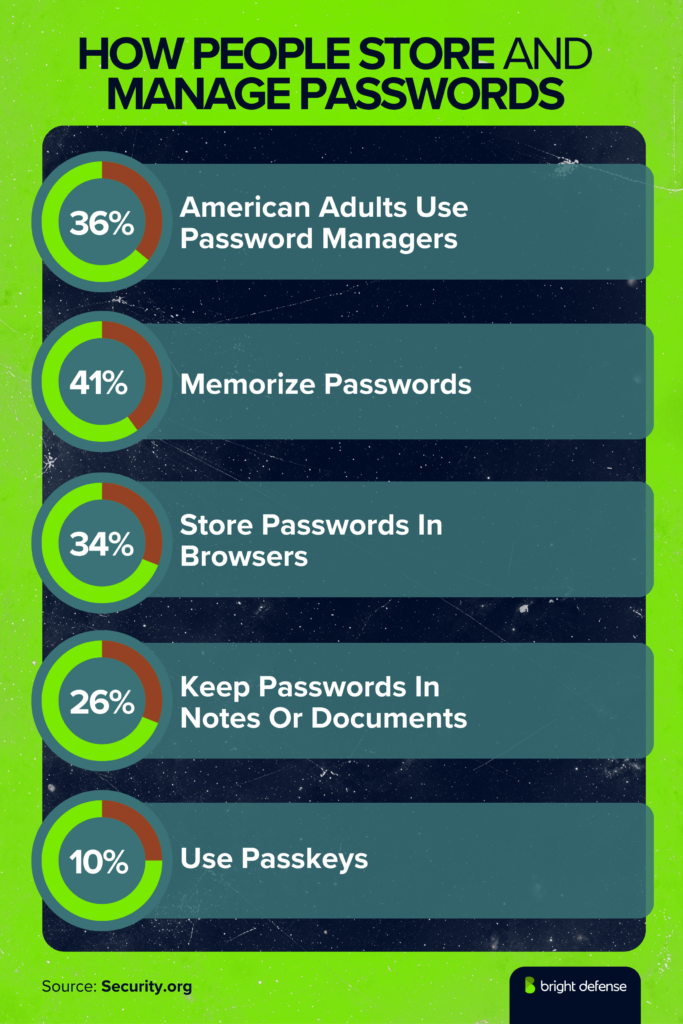
- 36% of American adults use password managers, representing about 94 million users. (Security.org)
- 41% of Americans still memorize their passwords, 34% store them in browsers, 26% keep them in notes or documents and 25% write them down on paper. (Security.org)
- Only 10% use passkeys, and 18% admit to using the same password across multiple accounts. (Security.org)
- 30% of internet users rely on password managers, 55% memorize passwords, 32% write them on paper, 27% save them in browsers and 25% save them in notes. (DemandSage)
- 34% of Americans use password management tools, while 41% rely on memory. (DemandSage)
- Only 7% of the global population view password managers as the best method for securing credentials, yet 75% of non-users are willing to adopt them. (Secureframe)
- Users of password managers are less likely to suffer identity theft: 17% of password manager users reported identity theft compared with 32% of non-users. (Secureframe)
- Younger individuals (under 30) rely more on memorization (64%) than those over 60 (35%). (Security.org)
- 53% believe fingerprint scans are more secure than passwords, 47% believe facial recognition is more secure, 41% trust 4- or 6-digit PINs, 34% trust SMS one-time passcodes, 17% trust device recognition and only 6% consider passwords the most secure method. (Entrust)
- More than 51% of people reset a password at least once a month, while 15% do so weekly. (Entrust)
- When given a choice, 58% of respondents choose biometrics over passwords, with 33% always choosing biometrics and 25% usually choosing them. (Entrust)
Passkey Adoption and Multi-Factor Authentication
- More than 15 billion online accounts support passkeys, and Amazon alone has created 175 million passkeys, while Google has enabled passkeys on 800 million accounts and recorded 2.5 billion passkey sign-ins over two years. (FIDO Alliance)
- PlayStation Network saw a 24% reduction in sign-in time and an 88% conversion rate when passkey benefits were presented. (FIDO Alliance)
- More than 13 million au ID customers use passkeys; LY Corporation (Yahoo! JAPAN) has 27 million active passkeys, with 50% of smartphone authentications now passkey-based and sign-ins 2.6 times faster than SMS one-time passwords. (FIDO Alliance)
- The marketplace Mercari has 7 million passkey users and recorded zero phishing incidents since introducing passkeys in March 2023. (FIDO Alliance)
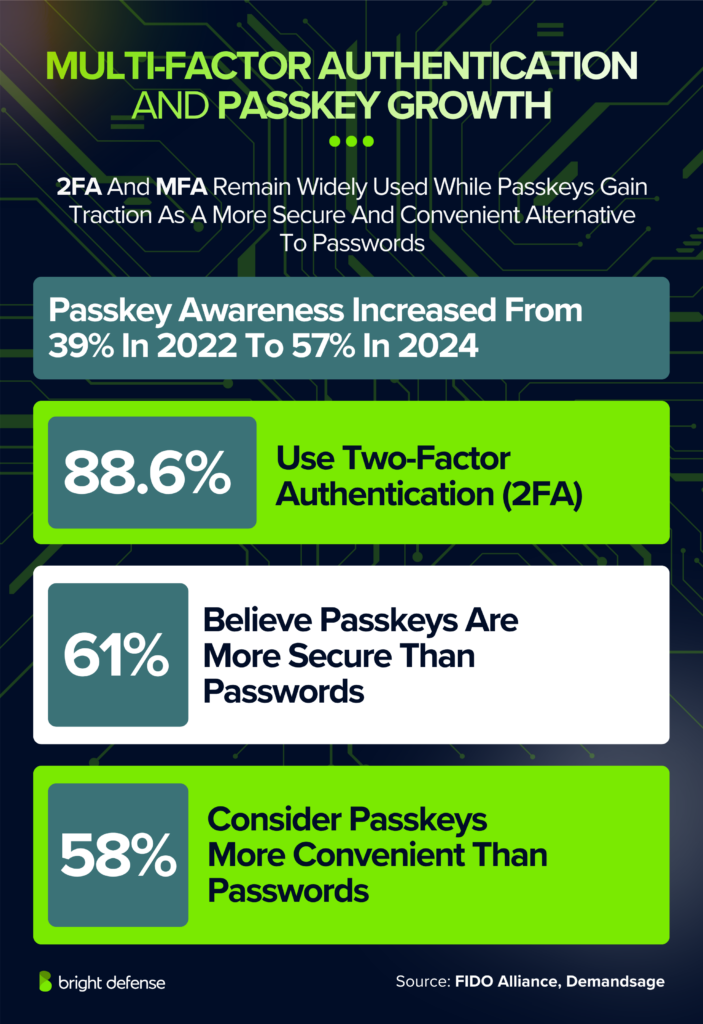
- Passkey familiarity rose from 39% in 2022 to 57% in 2024, and 25% of consumers enable passkeys whenever possible. (FIDO Alliance)
- About 61% of consumers believe passkeys are more secure than passwords, and 58% consider them more convenient. Adoption varies by region: about 80% in China, 70% in India, 62% in Japan, 58% in Singapore, 52% in Australia and 44% in South Korea use passkeys. (FIDO Alliance)
- 42% of people abandoned an online purchase in the past month due to password issues, with the rate rising to 50% for consumers aged 25 to 34 and falling to 17% for those over 65. (FIDO Alliance)
- Microsoft blocks about 7,000 password attacks per second, more than twice the rate in 2023. (Microsoft)
- Users registered nearly 1 million passkeys per day, and passkey sign-in success rates reached 98% compared with 32% for passwords; sign-ins were 8 times faster. (Microsoft)
- More than 15 billion Microsoft user accounts can support passkeys, and its new default sign-in process reduced password use by 20%. (Microsoft)
Credential-Based Attacks & Initial Access Tactics
Attack Vectors and Prevalence
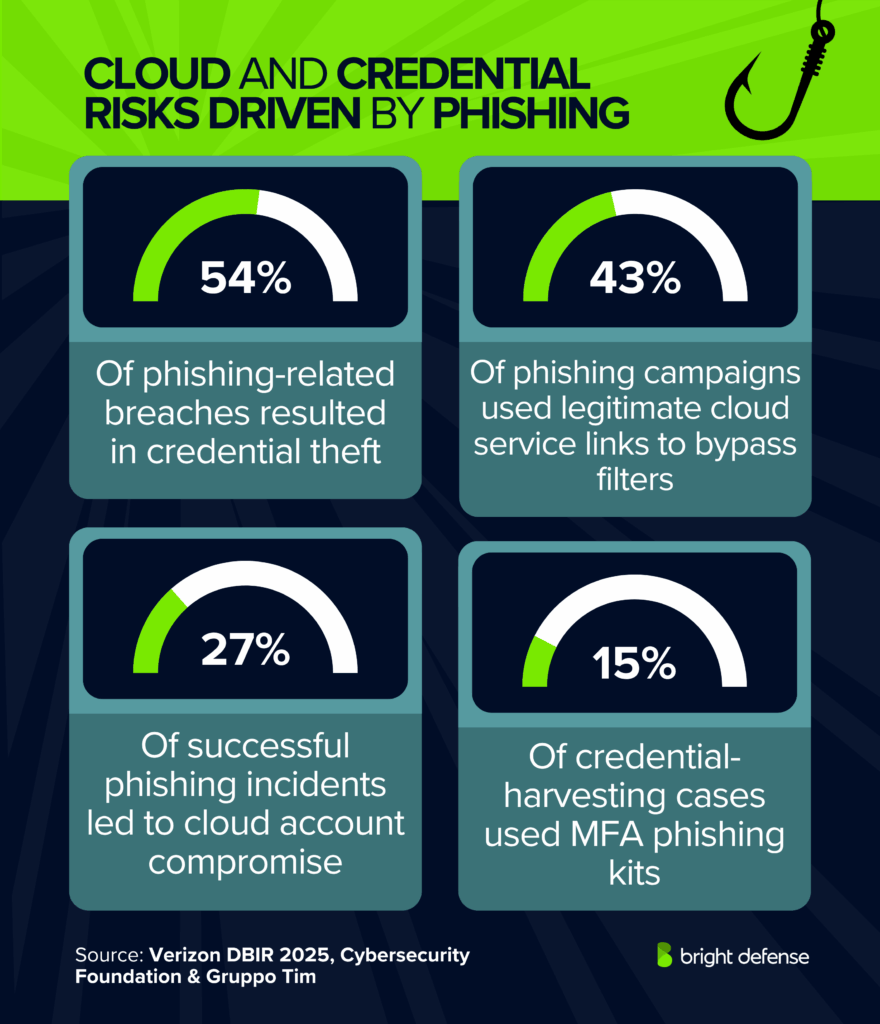
- 22% of breaches used stolen credentials, down from 31% in the previous reporting period. (Verizon DBIR 2025)
- Exploitation of vulnerabilities accounted for 20% of breaches, a 34% increase from the prior year, while phishing remained steady at around 15%. (Verizon)
- In basic web application attacks, about 88% of breaches involved the use of stolen credentials, sometimes as the sole action. (Verizon)
- Credential abuse often overlaps with vulnerability exploitation; attackers may exploit a vulnerability to deploy malware that steals credentials. (Verizon)
- Stolen credentials were identified in 16% of intrusions in 2024, up from 10% in 2023 after a drop from 14% in 2022. (Mandiant)
- Valid accounts were used for initial access in 20.8% of incidents, external remote services accounted for 22.4%, exploitation of public-facing applications for 22.2% and phishing for 13.1%. (Mandiant)
- 24% of 2024 cyber incidents involved infostealers, malicious programs designed to harvest credentials from personal and financial information stored on devices. (Huntress)
- 35% of hacked individuals blamed weak passwords for the compromise and 30% attributed it to password reuse. (Forbes)
- The success rate of a credential stuffing attack ranges from 0.2% to 2%, meaning even a modest percentage yields numerous compromised accounts when billions of credentials are tested. (Cybernews)
- 81% of company breaches involve poor password practices. (DemandSage)
- 28% of cybersecurity professionals believe weak passwords are employees’ worst security habits, and 46% of users choose easy-to-remember passwords over complex passwords. (Huntress)
- Only 13% use random password generators, 63% change passwords only when prompted and 8% share credentials. (Huntress)
- 80% of confirmed data breaches involving Mastercard cards stem from weak or stolen passwords. (Secureframe)
Attack Targets and Stolen Information
- 29% of targeted accounts were social media profiles, 15% were email accounts, 9% were home Wi-Fi routers, 8% were online shopping or financial accounts, 7% were streaming services or public Wi-Fi, 7% were gaming platforms and 6% were healthcare accounts; 4% involved biometric devices. (Forbes)
- Among those whose credentials were stolen, 77% lost personal information; 39% lost their first and last names, 38% lost phone numbers, 34% lost addresses, 25% lost credit-card numbers, 24% lost Social Security numbers and 22% lost banking information. (Forbes)
- 24 billion credentials are exposed each year and 39% of stolen information includes both first and last names. (Huntress)
Initial Access Trends Over Time
- The prevalence of stolen credentials fluctuated from 14% of intrusions in 2022 to 10% in 2023, followed by a resurgence to 16% in 2024. (Mandiant)
- Verizon’s DBIR reported a decrease in stolen-credential usage from 31% in 2024 to 22% in 2025, while vulnerability exploitation increased by 34%. (Verizon)
- Breaches involving stolen or compromised credentials take an average of 292 days to identify and contain, the longest of any attack vector. (IBM)
- 16% of breaches start with compromised credentials at an average cost of $4.81 million; phishing accounts for 15% of breaches costing $4.88 million, and malicious insiders represent 7% costing $4.99 million. (IBM)
- Malicious attacks made up 55% of breaches, while IT failures accounted for 23% and human error for 22%. (IBM)
Industry & Region-Specific Impacts
Sector-Specific Patterns
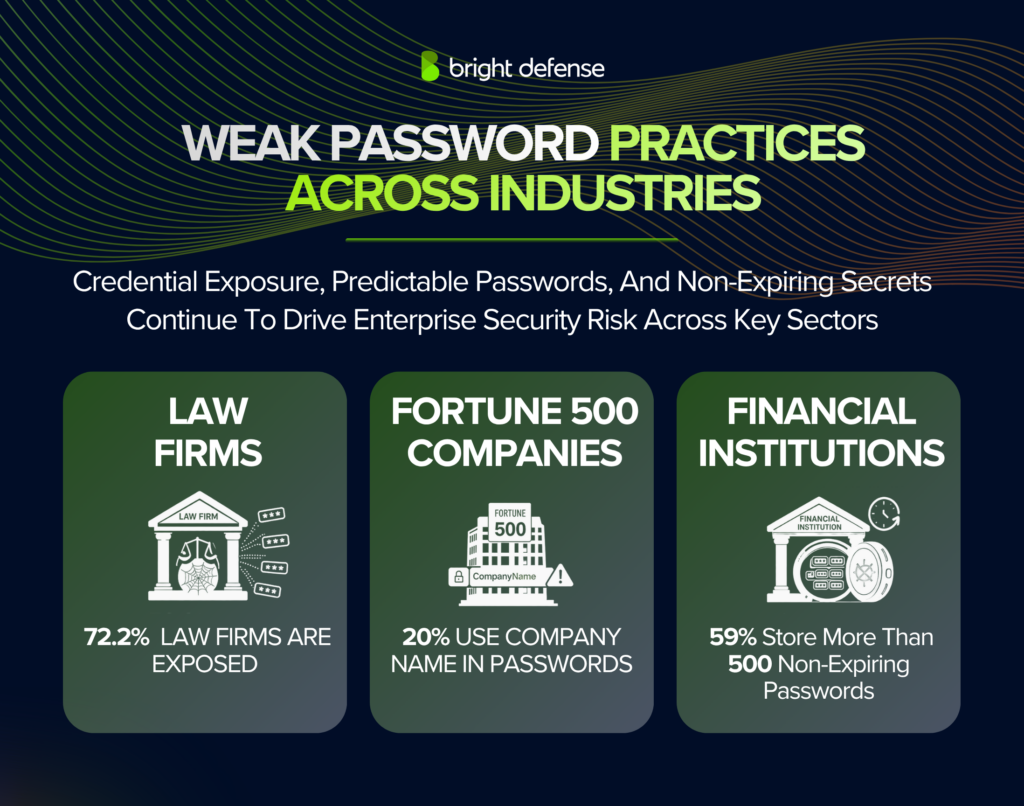
- 20% of Fortune 500 passwords contain the company name, raising corporate espionage risks. (Secureframe)
- The human resources sector had the highest percentage (31%) of unique passwords, while the telecommunications sector had 20% unique passwords. (Secureframe)
- 59% of financial services firms have more than 500 non-expiring passwords, while 72.2% of 5,140 audited law firms had employee credentials available on the dark web, representing 1,001,313 passwords or about 195 passwords per firm. (Secureframe)
- MFA adoption rates vary by sector: 87% in technology, 77% in insurance, 75% in professional services, 72% in education, 71% in finance, 66% in manufacturing, 64% in healthcare, 59% in public sector and 55% in hospitality. (DemandSage)
- The global password management market is projected to reach $15.2 billion by 2032 with a 20.7% CAGR, and the global multi-factor authentication market is expected to reach $53 billion by 2030. (Secureframe)
- Only 60% of IT leaders use privileged access management systems, and 43% have replaced passwords with biometrics or passkeys for some applications. (Secureframe)
- Obstacles to passwordless authentication adoption include legacy platform constraints (20%), lack of skills (23%), budget limitations (20%) and the perception that authentication is not a developer priority (4%). (Secureframe)
Country- and State-Level Data

- 35% of Generation Z respondents never or rarely update passwords after a data breach, whereas only 10% always update them. (Bitwarden)
- Approximately 38% of Gen Z and 31% of Millennials change only a single character or reuse a password when “updating” it. (Bitwarden)
- 72% of Gen Z reuse passwords compared with 42% of Boomers. (Bitwarden)
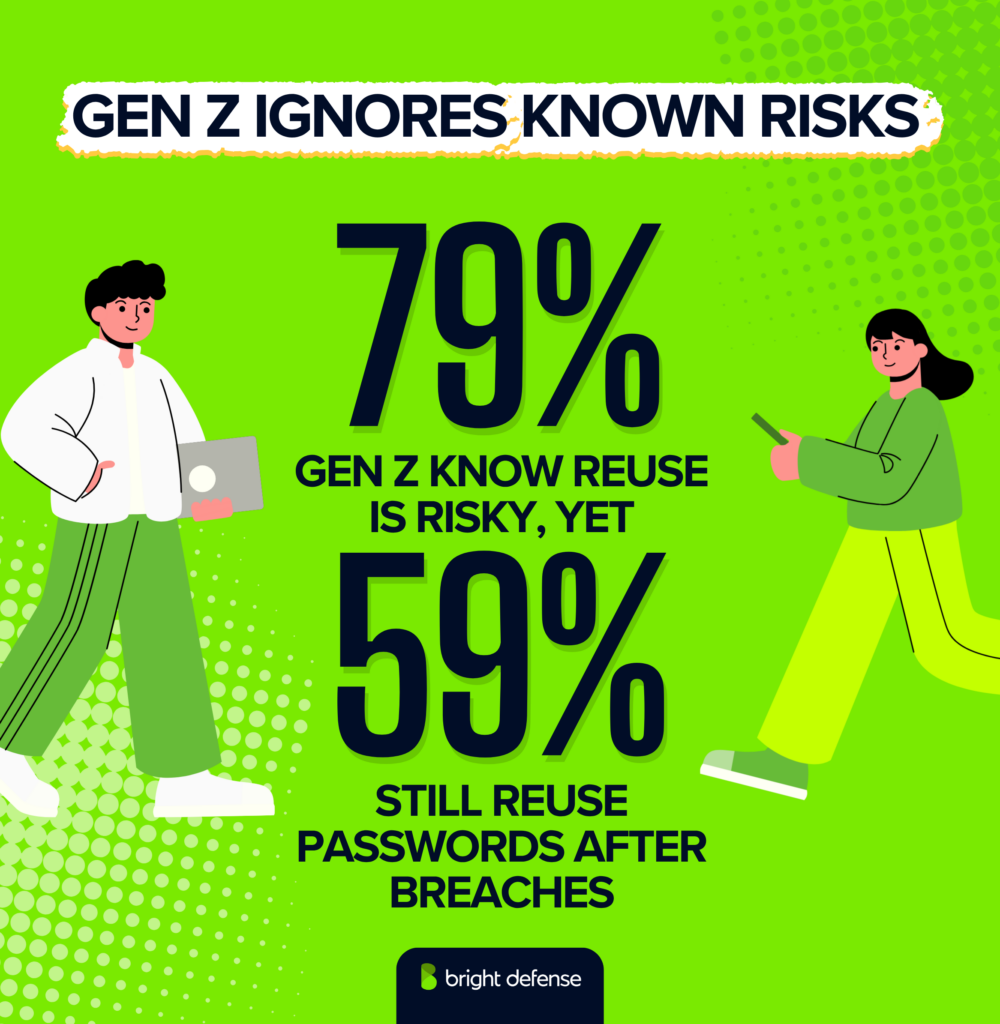
- 79% of Gen Z know that reuse is risky, yet 59% reuse passwords when updating accounts after a breach, compared with 23% of Boomers. (Bitwarden)
- More than 80% of younger respondents enable multi-factor authentication, and 44% of Gen Z change streaming-service passwords to revoke access. (Bitwarden)
- About 62% of Gen Z feel stressed managing passwords; 46% use password managers, while only 33% of Generation X do so and 21% of Generation X either do not know how or do not trust password managers. (Bitwarden)
- Gen Z share passwords through text messages (25%), screenshots (19%) or verbally (19%). (Bitwarden)
- A survey across the U.S., U.K., Australia, France, Germany and Japan revealed that 25% of respondents reuse passwords across 11 to 20 accounts or more, 36% incorporate personal information into their passwords and 54% manage all your passwords through memory. (Bitwarden)
- 33% use pen and paper to store passwords, 32% feel unprepared to defend against AI-related attacks, 37% view workplace security habits as risky and 45% have adopted passkeys even though 41% do not fully understand them. (Bitwarden)
- 19% of respondents had suffered a security breach, 23% had their passwords stolen, 48% access personal or work data on public Wi-Fi networks and 32% share passwords insecurely. (Bitwarden)
- In Rhode Island, 12.5% of respondents reuse passwords, 62.5% avoid variations, 50% use auto-generated passwords and 12.5% change passwords every few months. (Casino.org)
- Louisiana showed 61.9% password reuse, 66.6% avoiding variations, 38% using auto-generated passwords and 66.6% adopting passwords longer than 12 characters. (Casino.org)
- In Maine, 28.5% reuse passwords and 28.5% update them regularly. (Casino.org)
- 24% of websites do not allow special characters in passwords. (Spacelift)
- Passkey adoption varies across countries: 80% in China, 70% in India, 62% in Japan, 58% in Singapore, 52% in Australia and 44% in South Korea. (FIDO Alliance)
- APAC organizations reported that passkey-based sign-ins are 2.6 times faster than SMS one-time passcodes. (FIDO Alliance)
Major Exposures & Breach Impacts
Volume of Exposed Credentials
- Cybernews identified 19.03 billion leaked passwords and noted that only 6% were unique passwords. (Cybernews)
- 24 billion credentials were exposed in 2022 and 6.7 billion of them were unique. (DemandSage)
- About 6 million records were exposed in the first quarter of 2023, and 1 million passwords are stolen weekly. (DemandSage)
- American adults collectively manage about 94 million password manager subscriptions. (Security.org)
Common Passwords and Dictionary Words
- The simple sequence “1234” appeared 727 million times in leaked credentials. (Cybernews)
- The password “admin” was used 53 million times and “password” 56 million times across popular passwords in breach datasets. (Forbes)
Types of Stolen Data
- In incidents involving compromised credentials, 77% of victims had personal data stolen. (Forbes)
- The stolen information included names (39% of cases), phone numbers (38%), home addresses (34%), credit-card numbers (25%), Social Security numbers (24%) and banking details (22%). (Forbes)
- 23% of individuals do not know whether their passwords have been breached and 32% are unsure whether their credentials are listed on dark web marketplaces. (Secureframe)
Breach Cost and Recovery Metrics
- Breaches initiated with compromised credentials constitute 16% of all incidents and cost an average of $4.81 million, while those initiated by phishing account for 15% at $4.88 million and malicious insiders account for 7% with a cost of $4.99 million. (IBM)
- Malicious attacks made up 55% of breaches, IT failures 23% and human error 22%. (IBM)
- The global average breach cost increased to $4.88 million, a 10% rise over the previous year; the average U.S. breach cost reached $9.36 million, while costs in the Middle East averaged $8.75 million, Benelux $5.90 million, Latin America $3.67 million and India $2.36 million. (IBM)
- Organizations using security AI and automation saved $2.2 million on average per breach, and two out of three organizations were deploying AI across their security operations centers (a 10% increase). (IBM)
Operational and Human Impacts
- 27.1% of people believe managing multiple passwords wastes time, while employees reuse one password an average of 13 times. (DemandSage)
- 69% of individuals feel overwhelmed by the number of passwords they must manage and 30% attribute a breach to password reuse. (Huntress)
- 45% of Americans feel anxious about password strength and 41% write passwords down. (Pew Research)
- 43% of respondents have an electronic identity (eID), 36% said no and 21% were unsure, while only 27% of Americans recognized that they have an e-passport despite universal issuance since 2006. (Entrust)
- 17.3% of participants forget passwords a few times per month and 17.3% never forget them. (Casino.org)
- 47% of people forget passwords multiple times each month and 15.3% forget weekly. (Secureframe)
- About 51% reset passwords monthly due to forgetting them, 15% reset weekly and 43% have not updated a password in more than 5 years. (Secureframe)
- 51% of password manager users become more security-conscious at work, 45% reduce password reuse and 65% of respondents believe that using password managers improves their online security. (Bitwarden)
- 40% said they use multi-factor authentication for personal accounts and 41% for work accounts; 57% adopted 2FA in response to phishing incidents. (Bitwarden)
- 25% of consumers enable passkeys whenever possible, and 61% believe passkeys are more secure than passwords. (FIDO Alliance)
- 10% of consumers have adopted passkeys as of the latest survey. (Security.org)
- Passkey sign-ins have a 98% success rate compared with 32% for passwords, and sign-ins are 8 times faster. (Microsoft)
- The FIDO Alliance recorded zero phishing incidents on Mercari after passkeys were introduced. (FIDO Alliance)
Timeline Shifts & Future Directions
Decreases in Stolen-Credential Usage
- The share of intrusions involving stolen credentials fell from 14% in 2022 to 10% in 2023 but increased to 16% in 2024. (Mandiant)
- Verizon’s DBIR observed a drop in stolen-credential usage from 31% in the 2024 report to 22% in the 2025 edition, and exploitation of vulnerabilities increased by 34%. (Verizon)
- Breaches involving compromised credentials remain costly at $4.81 million on average, reinforcing the need for continuous monitoring and credential hygiene. (IBM)
Growth of Passkeys, MFA and Password Managers
- Passkey awareness jumped from 39% in 2022 to 57% in 2024, and 25% of consumers enable passkeys whenever possible. (FIDO Alliance)
- Nearly 1 million passkeys are registered each day, and passkey sign-ins cut password use by 20%. (Microsoft)
- The global password management market will reach $15.2 billion by 2032. (DemandSage)
- Adoption of password managers rose from 20% in 2019 to 32% in 2023. (Pew Research)
- 88.6% of respondents use 2FA, and MFA adoption reaches 87% in technology and 77% in insurance among other sectors. (DemandSage)
- 42% of people abandoned purchases due to password issues, and passkeys could mitigate these losses. (FIDO Alliance)
- 45% of Americans use password managers, indicating increasing adoption. 58% of people choose biometrics when given a choice, and only 6% consider passwords the most secure option. (Entrust)
Growth in Number of Passwords Per User
- The typical person must keep track of 250 to 300 passwords, while business users juggle roughly 85 passwords. (Spacelift)
- The average American uses about 27.6 passwords. (Casino.org)
- The average person has 87 passwords at work and another 168 personal passwords, implying a total of 255 passwords, which represents a 70% increase since 2020. (Secureframe)
How to Choose a Strong Password
A strong password is a credential that resists both automated cracking tools and manual guessing. The ideal password length is at least 16 characters, according to current NIST recommendations and industry consensus. It should contain a mix of uppercase and lowercase letters, numbers and special characters arranged in a non-predictable sequence.
Avoid using personal information such as names, birthdays or pet names. 59% of U.S. adults incorporate birthdays or names into their passwords, and 20% of Fortune 500 passwords contain the company name. These patterns give attackers a starting point for dictionary-based and targeted brute force attacks.
Random password generators produce credentials with high password entropy that resist pattern-based cracking. Only 13% of people currently use random password generators, according to Huntress. Passphrases made up of unrelated words offer another approach. A passphrase of four or more random words can exceed 16 characters while remaining memorable.
Each online account should have its own unique credential. 94% of leaked passwords are reused or duplicated, so a single compromised password can expose every account sharing that credential. Storing credentials in a reputable password manager eliminates the need to memorize complex passwords for every service.
Password Breach Statistics
Weak or stolen credentials ranked as the top initial breach vector, involved in 22% of all data breaches in the 2024–2025 Verizon DBIR reporting period. In basic web application attacks, that figure reaches 88%.
Common passwords like “123456” and “password” remained the most frequently compromised in 2025, appearing 338 million and 56 million times respectively in breach datasets. A breach involving stolen credentials takes an average of 292 days to identify and contain, the longest lifecycle of any attack vector. In 2024, infostealers were responsible for 24% of all cyber incidents, according to the Huntress Cyber Threat Report.
Nearly half (46%) of people had a password stolen in 2024. An estimated 24 billion credentials are exposed each year in data breaches. 29% of users report breaches in social media accounts, and 15% report email account compromises. Poor passwords contributed to 81% of corporate data breaches, and approximately80% of confirmed Mastercard data breaches stem from weak or stolen passwords.
Between 2017 and 2020, hackers published 555 million stolen passwords on the dark web. Over 60% of password breaches involve compromised credentials driven by credential stuffing. The connection between password theft and downstream financial fraud makes credential protection a priority for both cybersecurity teams and individual internet users.
Password Reuse Statistics
Password reuse creates a “domino effect” that lets attackers move from one compromised account to many. Roughly 60% to 85% of people reuse passwords across multiple sites, and nearly 73% of individuals use the same password for both personal and work accounts. The average person reuses passwords 14 times across different accounts.
After a breach, 68% of users had to reset passwords on multiple accounts. Yet 63% of users only change passwords when prompted. 72% of Gen Z reuse passwords compared to 42% of Boomers. The average user now manages approximately 170 to 191 passwords across different accounts, and that volume makes reusing credentials a common shortcut.
According to 30% of people, their passwords were stolen because they had reused them. Approximately 23% use the same password across three to four different accounts. More than 60% of Americans use the same password for more than one account. A single compromised password can give attackers unauthorized access to every account sharing that credential through credential stuffing attacks.
Stats About Password Security Best Practices
An 8-character, lowercase-only password can be cracked in less than a second. A complex 11-character password containing mixed characters can take 400 years to crack. Experts now prioritize passwords of 16+ characters for protection against brute force attacks. These password security statistics demonstrate that password entropy matters more than any single complexity rule.
NIST now recommends using unrelated words for passphrases to improve memorability and security, rather than forcing users to include arbitrary special characters. Around 48% of people reuse the same password across multiple sites. The most common password remains “123456,” which appeared 338 million times in breach datasets.
The average number of passwords per person continues to climb steadily. One estimate places it at 255 total personal passwords and work credentials combined.44% of internet users almost never change or reset their passwords. Many industries fall short of setting the right password security policies, with adoption of privileged access management systems reaching only 60% among IT leaders.
Good password habits start with using a unique credential for each account, storing those credentials in a reputable password manager, enabling two-factor authentication and updating passwords regularly. Users tend to default to familiar patterns, and security teams must account for this behavior when designing authentication policies.
How to Improve Your Password Security
Start with a password manager. The number of people using a password manager rose from 20% in 2019 to 32% in 2023. Password manager users reported an identity theft rate of only 17%, compared with 32% for non-users. A password manager generates and stores strong, random passwords for each account so that no credential is reused.
Enable multi-factor authentication on every account that supports it. About 88% of security-conscious respondents already use 2FA for critical accounts. MFA can stop 96% of bulk phishing attacks and 76% of targeted attacks, based on Microsoft research.
Adopt passkeys where available. Passkey sign-ins succeed 98% of the time compared with 32% for password logins, and they eliminate the risk of phishing entirely. Mercari recorded zero phishing incidents after deploying passkeys in 2023.
Check whether your credentials have been exposed. 23% of individuals do not know whether their passwords have been breached and 32% are unsure whether their credentials appear on dark web marketplaces. Services such as Have I Been Pwned and built-in browser alerts can flag compromised passwords.
Set a password length of at least 16 characters for all new credentials. Avoid personal information, dictionary words and predictable patterns. Update passwords regularly, but avoid the practice of changing a single character or appending a number to a base password.38% of Gen Z and 31% of Millennials make only minimal changes when “updating” a credential.
Password Sharing Statistics
Password sharing remains widespread across personal and work contexts. 52.9% of people share passwords with others, according to GoodFirms. 8% of people openly admit to sharing credentials with family or friends, according to Huntress.
Gen Z share passwords through text messages (25%), screenshots (19%) or verbally (19%). 32% of respondents in the Bitwarden World Password Day survey share passwords insecurely. 44% of Gen Z change streaming-service passwords specifically to revoke access from someone they previously shared credentials with.
Sharing passwords over plaintext channels like SMS or email creates opportunities for interception. The safest method for sharing passwords is through a password manager’s built-in sharing feature, which transmits the credential in encrypted form and allows the owner to revoke access at any time.
Password Management Statistics
36% of American adults use password managers, representing about 94 million users. The password management industry is expected to reach more than $2 billion in revenue by the end of 2025. The broader market is set to grow to $15.2 billion by 2032 with a CAGR of over 20.7%.
65% of respondents said using a password manager improved their security posture. 51% of password manager users became more security-conscious at work, and 45% reduced password reuse. Major platforms like Google and Amazon have seen massive surges in passkey adoption, with Google reaching 800 million passkey-enabled accounts.
Password management tools tend to be more common in larger organizations than in small and medium-sized businesses. More than half of IT managers report that their employees don’t take cybersecurity measures seriously or only take them somewhat seriously. The gap between enterprise password hygiene and SMB practices remains a significant vulnerability.
Multi-Factor Authentication (MFA) Usage
Roughly 70% of enterprise users have adopted MFA by 2025, according to DemandSage. Small-business adoption sits much lower, in the range of 30% to 35%. Enabling two-factor authentication can stop 96% of bulk phishing attacks and 76% of targeted attacks.
About 88.6% of people now use multifactor authentication for at least their most critical accounts.40% use MFA for personal accounts and 41% for work accounts. 57% adopted 2FA specifically in response to phishing incidents.
MFA adoption rates vary by sector: 87% in technology, 77% in insurance, 75% in professional services,72% in education, 71% in finance, 66% in manufacturing, 64% in healthcare, 59% in public sector and 55% in hospitality.
Hardware tokens, authenticator apps and biometric verification each provide different levels of phishing resistance. Passkeys offer the strongest protection because the private key never leaves the device. 97% of identity-based attacks leverage password spray or brute force techniques, and MFA remains the most effective countermeasure against both. Offensive security assessments surface the same pattern — our penetration testing statistics show how often weak or reused credentials hand testers an initial foothold during real engagements.
Password Management Policies at Organizations
Only 60% of IT leaders use privileged access management systems, and 43% have replaced passwords with biometrics or passkeys for some applications. Obstacles to passwordless authentication adoption include legacy platform constraints (20%), lack of skills (23%), budget limitations (20%) and the perception that authentication is not a developer priority (4%).
Organizations that implemented passkeys saw a 26% reduction in password usage, 77% reported fewer help-desk calls and 83% met digital transformation goals.59% of financial services firms have more than 500 non-expiring passwords, and72.2% of audited law firms had employee credentials available on the dark web. These figures illustrate why organizational password management policies must cover password expiration, credential monitoring and phishing-resistant authentication methods. They also line up with broader cybersecurity compliance statistics showing how many organizations actually meet — or miss — framework-level control requirements for access management and identity each year.
Future of Password Security
Passkeys use biometrics or device-level PINs instead of traditional passwords, eliminating the password problem at its root. More than 15 billion online accounts now support passkeys, and consumer awareness grew from 39% in 2022 to 57% in 2024.
Microsoft’s data shows passkey sign-ins succeed 98% of the time, compared with 32% for password logins. Passkey sign-ins are 8 times faster and eliminate the risk of phishing entirely. Mercari recorded zero phishing incidents after deploying passkeys in 2023.
Enterprise deployment is accelerating. 87% of businesses have deployed or are deploying passkeys, and 90% reported improvements in authentication security. 77% of organizations reported cost reductions after implementing passkeys.
Passwords are becoming a legacy authentication method. Organizations that invest in passkeys, MFA and credential monitoring tools now will face fewer password breaches, lower recovery costs and stronger resilience against credential-based attacks.
The growth in multi-factor authentication adoption across sectors, combined with the rapid rise in passkey registrations, points toward a future where stolen passwords carry less value to attackers.
How Quickly Can a Weak Password be Cracked?
An 8-character lowercase-only password can be cracked in less than a second. 45% of all passwords can be cracked within 1 minute, and 73% fall within 1 month. Adding symbols and increasing password length to 14+ characters extends cracking time to millions of years.
Why Bright Defense Delivers Quality Cybersecurity Compliance Services
Bright Defense delivers quality cybersecurity compliance services through a practical, threat-informed approach that focuses on how attacks actually happen. The team designs compliance programs around real failure points such as credential abuse, where 94% of leaked passwords are reused and stolen credentials contribute to 22% of breaches .
Each engagement emphasizes control effectiveness, not just documentation, with clear validation, enforced processes, and measurable outcomes. This results in compliance programs that move beyond audit readiness and function as active security controls in day-to-day operations.
Final Thoughts
The password statistics compiled in this report show how pervasive credential risks remain despite growing adoption of password managers and passkeys. Hundreds of millions of credentials are exposed each year, with only small percentages being unique.
Predictable patterns, personal information and pop-culture references dominate password composition, making credential stuffing attacks profitable even with low success rates. Weak or reused passwords remain among the most common causes of account compromise, and nearly all identity-based attacks use password spray or brute force.
The data show promising trends at the same time. Passkey awareness has more than doubled in two years, and businesses are rapidly deploying passwordless technologies that reduce login friction and improve security. Multi-factor authentication adoption is strong across most sectors, and password manager usage is growing steadily.
Human factors, including password fatigue, memory lapses and resistance to change, continue to hamper security programs. Security leaders should use the quantitative insights presented here to strengthen credential policies, invest in passwordless solutions, educate users and adopt AI-driven detection to reduce the window of opportunity for attackers.
Password Stats FAQs
The common number used to be about 100, but new research suggests the average person manages roughly 168 personal passwords and 87 business account passwords. That puts the total at more than 250 credentials per person, a 70% increase since 2020.
The most common password is “123456.” It appeared 338 million times in a study of 19 billion leaked passwords. The sequence “1234” appeared 727 million times, and the words “password” and “admin” appeared 56 million and 53 million times respectively.
Millions of passwords are likely compromised across the world every day. Attackers steal about1 million passwords per week, and Microsoft blocks roughly 7,000 password attacks per second. Cyberattacks occur approximately every 39 seconds worldwide.
“123456” is the most hacked password. It appeared in338 million leaked records. The words “password” (56 million) and “admin” (53 million) rank closely behind.
Passwords can be stolen through phishing (deceptive emails or websites that trick users into entering credentials), brute force attacks (automated tools that test millions of combinations per second), credential stuffing (reusing leaked passwords from one breach against other sites), infostealer malware (programs that harvest saved passwords from browsers and devices) and data breaches (large-scale compromises that expose databases of credentials). In 2024, infostealers were responsible for 24% of all cyber incidents.
Change your master password immediately and enable multi-factor authentication on the password manager account. Then change the passwords for your most sensitive accounts (banking, email, work accounts) first, followed by all remaining stored credentials. Check whether your email addresses appear in breach notification services. Review account activity logs for unauthorized access. Consider switching to a password manager that uses zero-knowledge encryption, where the provider cannot access your vault contents.
The ideal length is at least 16 characters. An 8-character lowercase-only password can be cracked in less than a second. A 14-character password containing numbers, letters and symbols can resist cracking for1,760 million years. NIST recommends passphrases made of unrelated words as an effective alternative to complex character strings.
A password is a string of characters used to verify the identity of a user attempting to access a device, account or system. Passwords serve as the most common form of authentication across personal accounts, business accounts and online services. The term originates from historical use of secret words to gain entry to restricted areas. Modern password security extends far beyond simple words to include complex combinations of letters, numbers and special characters.
192.168.1.1 is the default IP address for many home routers and access points. The default username and password combination varies by manufacturer. Common defaults include “admin/admin,” “admin/password” or “admin/1234.” These default credentials should be changed immediately after setup. Among 10 million RDP attack passwords analyzed, about 420,000 ended with a number between 0 and 99, and the password “admin” appeared53 million times in leaked datasets. Default router passwords are a frequent target for attackers scanning for unsecured home networks.
You can check whether your password has been exposed in a data breach through services like Have I Been Pwned, which maintains a database of compromised credentials. Most modern browsers (Chrome, Firefox, Edge, Safari) include built-in password checkup features that alert you when a saved credential appears in known breach datasets.
Password managers such as 1Password, Bitwarden and Dashlane offer similar breach-monitoring features. 23% of individuals do not know whether their passwords have been breached, and 32% are unsure whether their credentials appear on dark web marketplaces.
You cannot view your email password in plaintext through your email provider. Email services store passwords in hashed form, which means the original text is not retrievable. You can find your saved email password in your browser’s password settings (Chrome: Settings > Passwords; Firefox: Settings > Privacy & Security > Saved Logins; Safari: Settings > Passwords) or in your password manager’s vault. You will need to authenticate with your device PIN, fingerprint or face scan to view the stored credential.
Based on the Cybernews analysis of 19 billion leaked passwords, the most frequently appearing password patterns are: “1234” (727 million occurrences), “123456” (338 million), “ass” (165 million), “love” (87 million), “password” (56 million), “admin” (53 million) and “sun” (34 million). These popular passwords represent some of the easiest targets for automated cracking tools and credential stuffing attacks.
A strong password is at least 16 characters long and contains a random mix of uppercase and lowercase letters, numbers and special characters. It does not include dictionary words, personal information, names, dates or predictable patterns. A strong password is unique to a single account and stored securely in a password manager rather than memorized or written on paper. 57% of passwords include a dictionary word, and 45% can be cracked within 1 minute. Strong passwords avoid all of these vulnerabilities.
Stolen credentials were the initial access vector in 22% of confirmed breaches in the 2025 Verizon DBIR. In basic web application attacks, that figure rises to 88%. IBM’s research found that credential-related breaches cost an average of $4.81 million and take 292 days to detect and contain.
Password manager users reported an identity theft rate of 17%, compared with 32% for non-users. 65% of password manager users said the tool improved their security posture, and 51% became more security-conscious at work.
Passkeys are cryptographic credentials tied to a user’s device. They use biometrics (fingerprint, face scan) or a device PIN for authentication. Passkeys never leave the device, cannot be phished and do not require memorization. Sign-in success rates with passkeys reach 98% compared with32% for passwords.
Microsoft blocks about 7,000 password attacks per second, which equals more than 600 million password attacks per day. This rate is more than double the frequency observed in 2023. 97% of identity-based attacks rely on password spray or brute force techniques.
An estimated 84% of people reuse passwords according to DemandSage. A study of 19 billion leaked passwords found that 94% were reused or duplicated. 72% of Gen Z and 42% of Boomers reuse credentials.
Credential stuffing is an automated attack that tests stolen username-password pairs against multiple websites. The success rate ranges from 0.2% to 2%, but when billions of credentials are available, even a small percentage yields thousands of compromised accounts. Password reuse across multiple sites is the primary reason these attacks succeed.
Breaches starting with compromised credentials cost $4.81 million on average. The global average breach cost reached $4.88 million in 2024, a 10% increase year over year. U.S. breach costs averaged $9.36 million. Organizations using AI and automation saved $2.2 million per breach.
Passkey usage among consumers reaches 80% in China, 70% in India, 62% in Japan, 58% in Singapore, 52% in Australia and44% in South Korea.
Password managers are significantly safer than memorization.54% of people manage all passwords through memory, yet 47% forget passwords multiple times per month. Password managers generate strong, random passwords for each account, reducing password reuse and the risk of credential stuffing attacks. The recommended approach is to use a password manager protected by a strong master password and enabled with MFA.
Get In Touch