Updated:
May 8, 2026
SOC 2 for SaaS: Why It Matters and How to Achieve It
SOC 2 is a security framework based on AICPA standards that defines how a system protects, processes, and stores customer data. An independent CPA firm reviews those controls and issues a formal report describing their design and operation.
SaaS products handle large volumes of customer data, which places SOC 2 at the center of enterprise security reviews. According to ISC2’s 2025 Supply Chain Risk Survey, 77% of organizations cite compliance with standards such as ISO 27001, NIST, or SOC 2 as their top vendor requirement. Enterprise buyers expect documented evidence during procurement.
A completed SOC 2 report gives sales teams concrete documentation to share during security reviews, which keeps deals moving through procurement without extended back and forth.
The sections below cover why SaaS companies pursue SOC 2, the two report types, the five Trust Services Criteria, the SOC 2 control list, the compliance process, and the execution mistakes that slow teams down.
Key Takeaways
- SOC 2 adoption in SaaS companies stems from customer demand and plays a direct role in how quickly deals move forward
- Type II is the standard during growth since it proves controls operate over time
- System design defines scope through data isolation, access control, cloud roles, and third party tools
- Most failures come from execution gaps such as unmanaged access, weak policies, scattered evidence, and inconsistent systems
Why SOC 2 is Crucial for SaaS Companies
SOC 2 matters for SaaS companies because enterprise buyers, investors, and partners require documented security controls before approving vendor relationships.
The framework provides the standardized evidence security reviews demand, which helps close deals faster, answers vendor questionnaires, and builds a control foundation that overlaps with other compliance frameworks such as HIPAA and GDPR.
Data security expectations rise as SaaS companies grow. In AppOmni’s 2025 State of SaaS Security Report, a survey of 803 security leaders and practitioners, 75% of organizations experienced a SaaS security incident in the past 12 months, a 33% jump from the year before.
Below is a detailed analysis as to why SOC 2 is a crucial step if you’re a SaaS company:

1. SOC 2 Eases Investor Due Diligence for SaaS Companies
Investors evaluate more than product and revenue. They assess how a company manages risk, particularly around customer data. A SOC 2 report signals operational maturity. 65% of organizations report that customers, investors, and suppliers now require more demonstration of compliance than in previous years, according to Vanta’s 2024 State of Trust Report.
SOC 2 shows that controls are in place and followed consistently. It gives investors a clearer view of how systems and processes function. A gap in that visibility can raise concerns during review and affect how risk is perceived.
2. SOC 2 Shortens Enterprise Sales Cycles for SaaS Companies
Enterprise buyers rarely move forward without reviewing vendor security posture. A SOC 2 report answers those concerns upfront. It removes much of the repeated back and forth during security review and gives the buyer documented proof of how systems and data are protected.
Companies with a SOC 2 Type II report see a direct effect on deal velocity. For B2B sales, a SOC 2 report removes the security review bottleneck that costs IT decision-makers an average of 6.5 hours per week in vendor risk assessments, according to Vanta’s 2024 State of Trust Report. Fewer deals stall. Procurement approvals move faster.
Conversations stay focused on product and fit, not on security documentation gaps.
3. SOC 2 Reduces the Burden of Vendor Security Questionnaires
Security questionnaires arrive early in the buying process and ask for detailed, repetitive answers. Without a structured framework, teams respond manually each time.
SOC 2 provides a consistent way to answer these requests. A standardized report covers common security concerns, which reduces repeated effort across deals and frees engineering and compliance teams from questionnaire fatigue.
4. SOC 2 Supports Adjacent Regulatory Requirements
SOC 2 is not a substitute for HIPAA, GDPR, or PCI DSS. It gives SaaS companies a useful starting point. The SOC 2 control environment overlaps with compliance expectations around:
- Access
- Monitoring
- Incident response
- Data handling
Even when another regulation drives the requirement, SOC 2 creates structure. It reduces the distance between customer expectations and formal obligations.
Relevant Read: Why SOC 2 is Critical for Your AI Startup.
“At Bright Defense, we specialize in guiding SaaS companies through every step of the SOC 2 process — from readiness assessments to audit day — so you can win trust and close deals faster.”
How Does SaaS Architecture Affect SOC 2 Requirements?
SaaS architecture affects SOC 2 requirements through data isolation, cloud responsibility, deployment controls, and third-party tools. Meanwhile, teams must manage access, changes, and data flow across systems. Clear ownership and consistent monitoring are also required to maintain control and visibility.
Let’s check out each how each SaaS architecture is affected by SOC 2 requirements:
1. Multi-Tenancy and Data Isolation
Multi-tenancy lets multiple customers share the same infrastructure while keeping their data separate. The model increases efficiency. It raises the risk of data exposure when isolation fails.
Data must stay logically separated at every layer, including databases, application logic, and access controls. Tenant-level permissions, scoped queries, and strict access boundaries enforce that separation.
Systems must prevent one tenant from accessing another tenant’s data, including edge cases such as misconfigured APIs or shared storage. Auditors focus on how the architecture applies these boundaries in real scenarios.
2. Cloud Shared Responsibility
Most SaaS products run on cloud platforms such as AWS, GCP, or Azure. These providers secure the underlying infrastructure. The SaaS team remains responsible for what runs on top.
Cloud providers handle data centers, hardware, and core network security. The SaaS team controls access, configurations, and data flow within the application.
SaaS teams still own:
- User access through IAM
- Encryption settings
- Network rules such as security groups
- Application-level permissions
SOC 2 auditors expect clear ownership across these layers. They look for consistent monitoring of access, changes, and system activity.
3. CI/CD Pipeline Controls
CI/CD pipelines govern how code moves from development to production, which places them directly within SOC 2 scope.
SOC 2 focuses on whether code changes are controlled, reviewed, and tracked. Key control areas include:
- Restricted access to code repositories and deployment tools
- Approval workflows for code changes
- Version control and change tracking
- Automated testing before release
These controls confirm that only authorized changes reach production and that every update follows a defined process.
4. Subprocessor Management
Most SaaS companies rely on third-party tools to run parts of their product or operations. These vendors are subprocessors, and they often handle or access customer data, which extends SOC 2 scope.
Common examples include:
- Cloud providers
- Payment processors
- Analytics tools
- Support platforms
Even when these systems sit outside the core product, they affect how data is stored, processed, and transferred. SOC 2 focuses on how a SaaS company governs these relationships.
Key expectations include:
- Maintaining a current list of active subprocessors
- Documenting what data each vendor handles
- Reviewing vendor security practices
- Defining access and data usage boundaries
Auditors expect visibility and control. Teams should know where customer data flows and who has access at each step.
How To Choose A SOC 2 Consultant For SaaS
A SOC 2 consultant for a SaaS company should match the company’s stage, bring direct SaaS experience, and guide readiness and audit support without performing the audit itself.
An effective consultant defines scope, organizes evidence, drafts policies, and prepares the team for interviews while the CPA firm handles the independent examination.
The criteria below help narrow the selection.
1. Choose A Consultant With Real SaaS Experience
Start with a consultant who has worked with SaaS companies similar in size, architecture, and sales motion. That experience keeps scope tied to the actual product, shared cloud infrastructure, customer questionnaires, release cycles, and third-party dependencies. SOC 2 is built around the Trust Services Criteria and the system description in scope, so the consultant’s familiarity with SaaS realities matters.
2. Keep The Consultant And Auditor Separate
Use a consultant for readiness and a CPA firm for the audit. The AICPA states that a SOC 2 examination can only be performed by an independent, licensed CPA firm. The consultant cannot be the auditor.
3. Confirm The Exact Deliverables
Ask for a written list of deliverables before signing. A capable consultant should define scope, map controls, draft or refine policies, organize evidence, support remediation, prepare the team for interviews, and stay involved through the audit window so the hardest parts do not fall back on the internal team.
4. Favor Clear Scope And Predictable Pricing
Fixed-fee pricing or tightly defined milestone pricing is easier for a SaaS company to budget than open-ended hourly billing. The statement of work should spell out what is included, what is excluded, how many review cycles are covered, and whether audit support is part of the fee.
5. Check Tool And Workflow Fit
The consultant should fit the way the team already works, whether that means a compliance platform, shared documents, ticketing systems, or a hybrid setup. Workflow fit reduces process overhead, keeps engineering time focused, and makes evidence collection and control ownership easier to manage.
6. Look For Specific Proof Of Experience
Request recent SaaS references, sample deliverables, expected timelines, and examples of controls the consultant commonly helps implement. The AICPA has warned that some providers in this market make misleading promises about scope, time, or fees, so favor consultants whose answers stay specific and supported.
7. Choose A Consultant Who Fits The Next Stage
The first SOC 2 report should match near-term sales and compliance needs. The consultant should help decide whether to start with Type 1 or Type 2, which Trust Services Criteria belong in scope, and what larger customers are likely to ask for over the next year.
A direct way to evaluate finalists is to ask three questions:
- Which SaaS companies similar to ours have you taken through SOC 2?
- Exactly what work do you do, and what does the CPA firm do?
- What will our team own?
The consultant with the clearest scope, the best SaaS fit, and the most specific answers is the safer choice.
“Bright Defense takes a continuous compliance approach — helping your SaaS team build and maintain security controls that satisfy SOC 2 auditors without disrupting your product roadmap.”
SOC 2 Type I vs. Type II: Which One Do You Need as a SaaS Organization?
SOC 2 Type I analyzes whether necessary controls are designed correctly at a single point in time. Meanwhile, Type II goes further and tests how those controls perform over months.
For growth-stage SaaS companies, SOC 2 compliance is usually expected when selling to enterprise clients.
| Aspects | SOC 2 Type I | SOC 2 Type II |
| Audit focus | Control design | Control performance over time |
| Timeframe | Point-in-time review | 3 to 12 months observation |
| Depth | Surface-level validation | In-depth operational proof |
| Purpose | Show initial readiness | Prove long-term reliability |
| Buyer perception | Early-stage credibility | Strong trust signal |
| Evidence required | PoliciesConfigsScreenshots | LogsAudit trailsHistorical records |
| Monitoring | Not required to prove consistency | Continuous monitoring expected |
| Control testing | Design validation only | Design with operating effectiveness |
| Access control checks | Reviewed once | Reviewed periodically with records |
| Change management | Documented process | Tracked changes with approvals and logs |
| Incident response | Policy exists | Incidents logged, tracked, and resolved with evidence |
| Effort level | Lower effort | Higher effort and coordination |
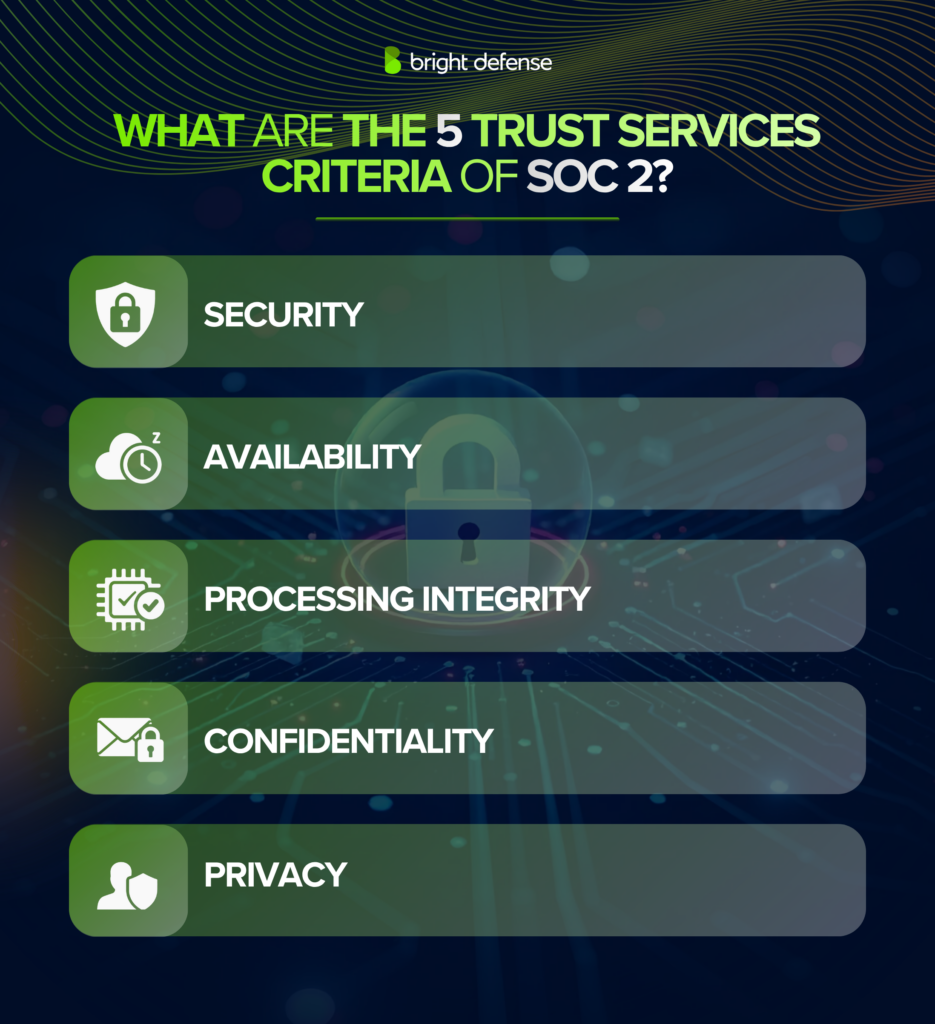
What Are the 5 Trust Services Criteria of SOC 2?
The five Trust Services Criteria of SOC 2 areSecurity, Availability, Processing Integrity, Confidentiality, and Privacy.
These criteria define how a SaaS company protects systems and data, and they form the foundation of every SOC 2 audit. For a deeper look at each one, see our breakdown of the SOC 2 trust services criteria.
1. Security
Security is the foundation of SOC 2 and the only mandatory criterion. It focuses on protecting systems and data from unauthorized access, misuse, or breaches. This includes controls like multi-factor authentication, access controls, encryption, and network firewalls. For the full breakdown, see the complete SOC 2 controls list.
Security also covers how your team monitors systems, detects threats, and responds to incidents.

Plus, auditors look for clear policies and real activity, such as access logs and alert tracking. If this layer is weak, nothing else in your SOC 2 report holds weight.
2. Availability
Availability focuses on keeping systems operational and accessible as expected. It covers how infrastructure handles uptime, performance, and reliability under normal and peak conditions.
Key controls include:
- Uptime monitoring
- Load balancing
- Backup systems
- Disaster recovery plans
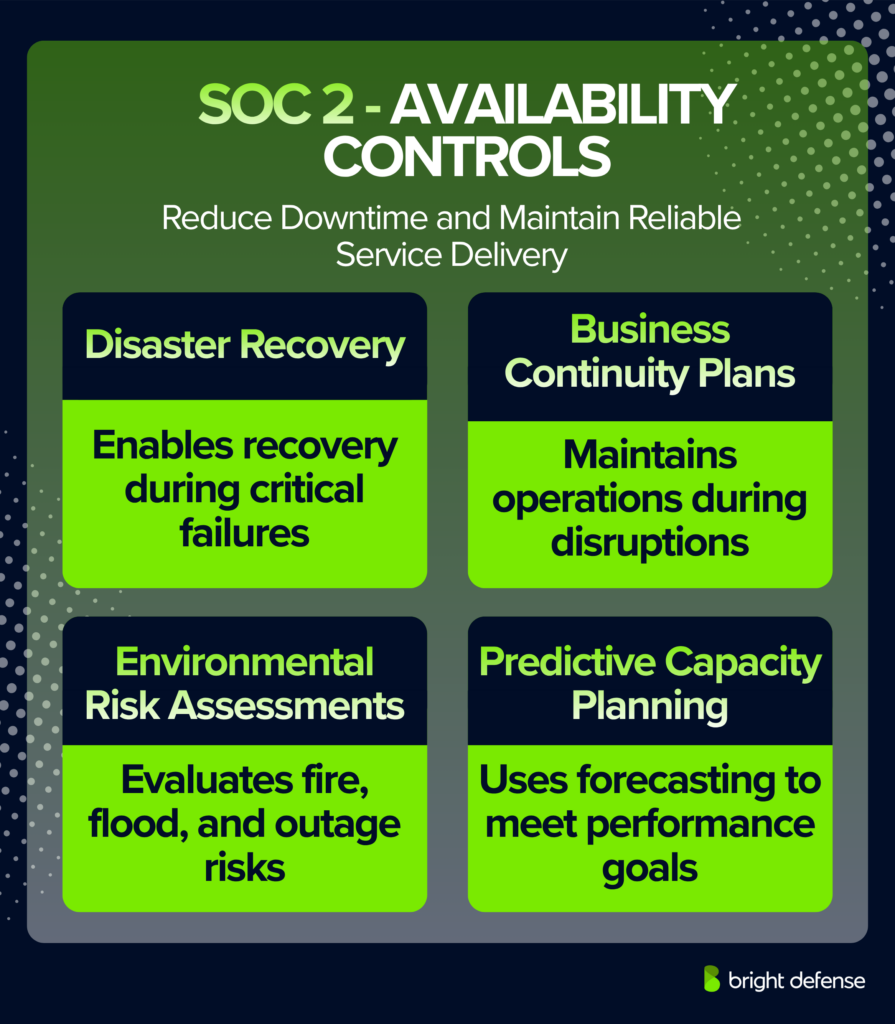
Meanwhile, teams must track system health and respond quickly to outages or disruptions. Moreover, auditors check whether
- Systems stay available as promised
- Recovery processes work when something fails
3. Processing Integrity
Processing Integrity confirms that systems process data accurately, completely, and on time. It focuses on whether the product delivers the correct output based on the input it receives.
Data must move through the system without distortion. Inputs need validation, and outputs must stay consistent. Any failure should surface through clear signals rather than silent errors.
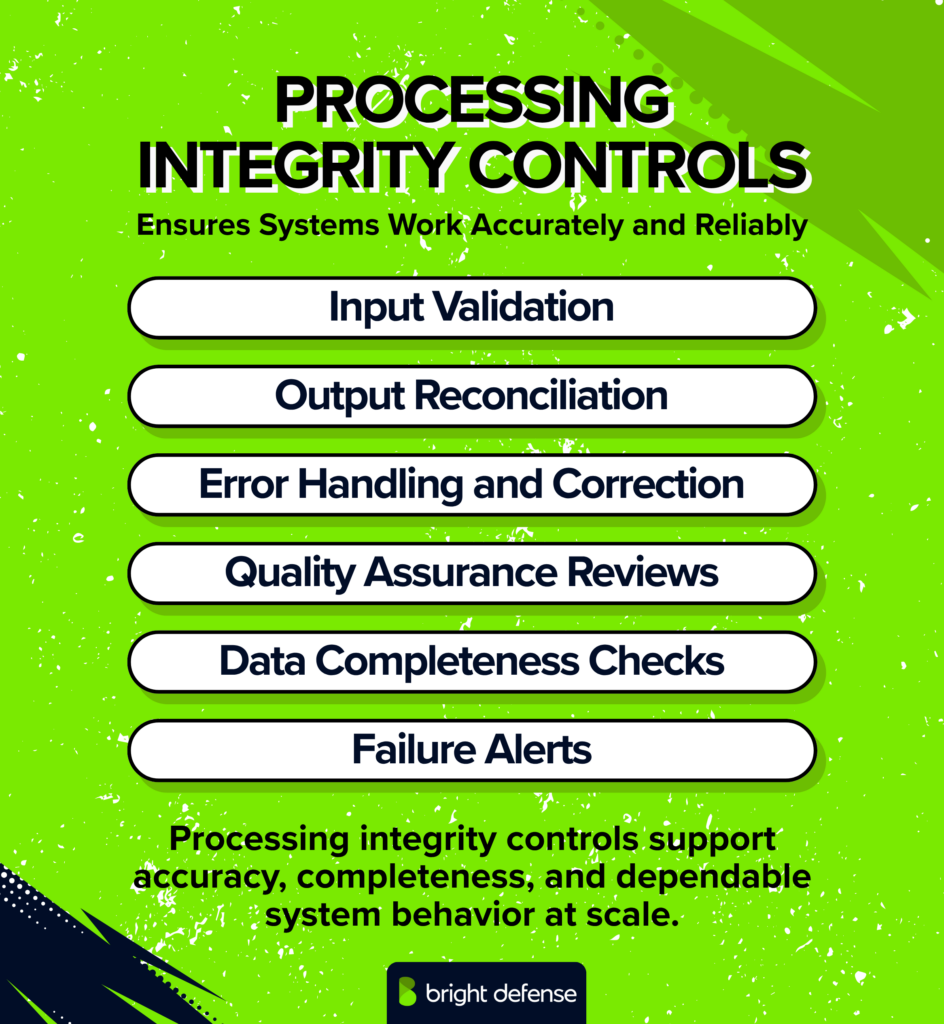
Likewise, auditors review how your system handles mistakes and whether your team fixes them in a timely way.
4. Confidentiality
Confidentiality focuses on protecting sensitive data from unauthorized access or exposure. At a SaaS company, it applies first to customer data. It extends to internal information such as:
- Contracts
- Financial records
- Intellectual property
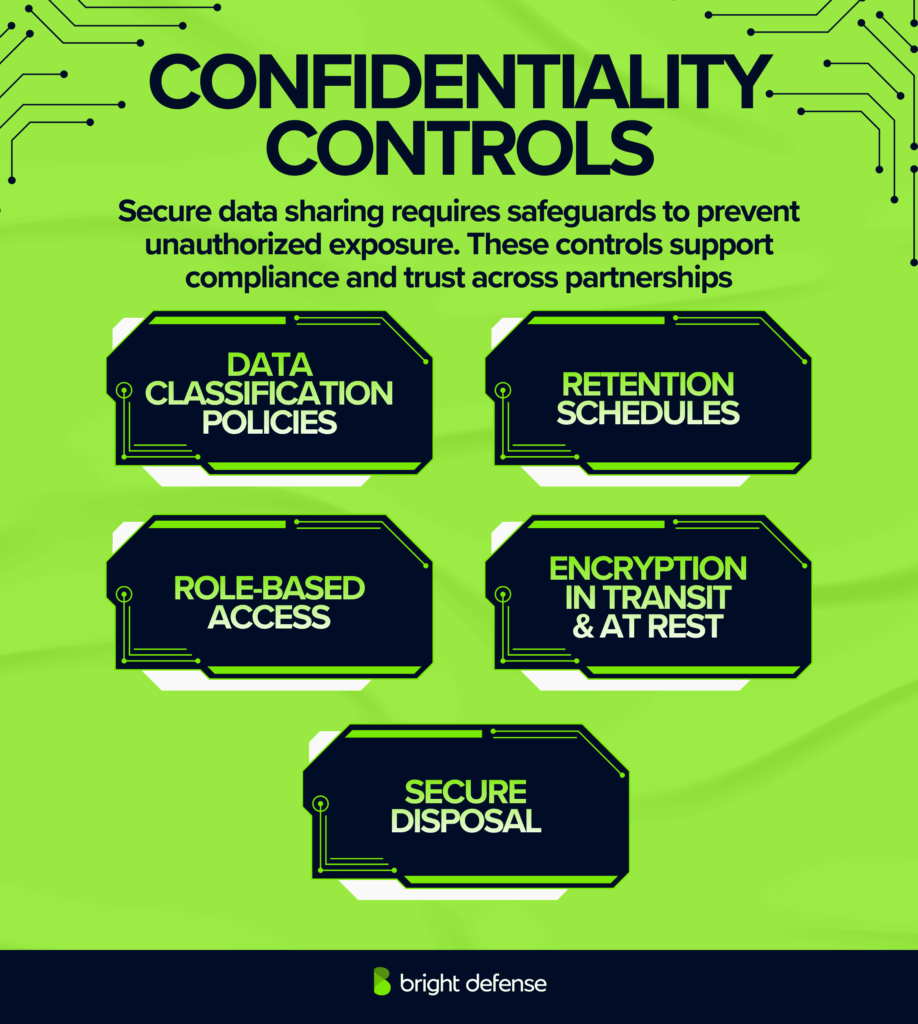
Access to sensitive data must stay limited to authorized users. Role-based access, encryption, and data classification enforce that boundary. Auditors review how the team stores, shares, and restricts sensitive information, and whether those controls hold up in real use.
5. Privacy
Privacy focuses on how a SaaS company collects, uses, stores, and deletes personal data. It addresses user rights and expectations, not only technical data protection. 81% of U.S. adults say they feel very or somewhat concerned with how companies use the data collected about them, according to Pew Research Center’s 2023 data privacy survey.
A SaaS team must define:
- What personal data is collected
- Why it is collected
- How long it is retained

Likewise, you must keep the consent, data usage, and deletion processes clear and consistent.
Auditors review whether —
- Your practices match your privacy policies
- Personal data is handled in a controlled and accountable way
SOC 2 vs. ISO 27001 vs. Other Frameworks: What SaaS Companies Need to Know?
SaaS teams often compare frameworks before starting compliance. Therefore, you must understand how each maps to SOC 2 requirements. It can help you to avoid extra work and focus on what actually applies to your system.
| Aspects | SOC 2 | ISO 27001 | HIPAA | GDPR |
| Framework type | Audit report | Certification standard | Legal rule set | Legal regulation |
| Core structure | Trust Services Criteria | ISMS framework | Security and privacy rule | Data protection law |
| Control approach | FlexibleRisk-based | PrescriptiveStructured | Fixed safeguards | Legal obligations |
| Mandatory scope | Security required | Full ISMS required | Full compliance required | Full compliance required |
| Technical controls | AccessLoggingInfraChange mgmt | Risk logsAsset mgmtControls library | AccessAudit logsEncryption | Data accessConsentStorage |
| Change management | Required and tested | Required in ISMS | Required | Implied through accountability |
| Access control depth | Strong focus (IAM, MFA) | Defined in control sets | Strict for PHI access | Focus on user rights |
| Data handling | Based on selected criteria | Based on risk plan | Strict for health data | Strict for personal data |
| Monitoring | Continuous control tracking | Periodic review cycles | Ongoing safeguards | Ongoing security compliance checks |
| Audit evidence | LogsReportsActivity trails | Documentation with audits | Documentation with audits | Legal documentation |
| Implementation effort | Moderate and scoped | High and broad scope | High and strict rules | High, legal with technical |
What Is the SOC 2 Compliance Process?
The SOC 2 compliance process includes scoping systems, assessing gaps, and fixing control issues. Teams then collect evidence and run a readiness check. Finally, an auditor reviews controls and issues a report based on performance and design.
Here is what a SOC 2 engagement actually looks like from start to finish:
1. Scoping: Scoping defines what systems, data, and processes fall under your SOC 2 audit. It includes cloud infrastructure, code repositories, access systems, and third-party security tools that handle customer data. You also decide which Trust Services Criteria apply.
2. Gap Assessment: Gap assessment reviews your current controls against SOC 2 requirements. It helps to identify what’s missing or not enforced. This mostly includes policies, access controls, logging, and system configurations.
3. Remediation: Remediation focuses on fixing the gaps identified during the assessment. It covers updating policies, tightening access controls, enabling logging, and improving security configurations. Teams also assign clear ownership to each control.
4. Evidence Collection: Evidence collection involves gathering proof that each control is in place and working as intended. It includes access logs, change records, policy acknowledgments, and system activity. Auditors rely on this documentation to verify consistency and confirm that controls operate over time
5. Readiness Assessment: Readiness assessment is an internal check before the formal audit. It reviews whether controls are properly documented, consistently followed, and supported with evidence. This step helps identify weak areas, missing logs, or unclear ownership.
6. Audit: An independent third-party audit firm executes the audit. Here, the auditors review your controls, systems, and evidence to assess whether they meet SOC 2 requirements. Type I analyzes control design at a point in time. Meanwhile, Type II examines how controls perform over a defined period.
7. Report Issuance: Once the audit is complete, the auditor issues a SOC 2 report detailing the scope, controls, and findings. It includes the auditor’s opinion on whether controls are properly designed and operating as expected, along with any noted exceptions.
Common SOC 2 Compliance Mistakes SaaS Companies Make
SOC 2 compliance for SaaS companies often fails due to common operational gaps. These include unused policies, poor access control, delayed offboarding, ignored logs, scattered evidence, and inconsistent systems. Each issue creates risk and slows down audit readiness.

1. Unfollowed Policies
Most SaaS teams keep policies in folders that no one reads. 65% of employees often bypass cybersecurity policies to make their lives easier, according to CyberArk’s 2024 Employee Risk Survey of 14,003 workers across six countries. SaaS teams working toward SOC 2 are not exempt. Gaps become obvious when access reviews, incident response, or offboarding steps are not part of daily operations. The disconnect traces back to rushed documentation and unclear ownership.
2. Access Management Gaps
Access control breaks down as SaaS teams grow. People get added to AWS, GitHub, Slack, and similar tools, but access is rarely cleaned up afterward. Former employees still have active accounts. Permissions stack over time. Some users end up with more access than the role requires.
The risk is silent. It is not always visible internally, and it is easy for auditors to spot during access reviews.
3. Offboarding Blind Spots
Offboarding looks simple on paper and breaks down in execution. Access removal does not always happen right away. It gets delayed or missed entirely.
That gap carries real consequences. Malicious insider attacks produced the highest average breach cost at USD 4.92 million per incident in 2025, according to IBM’s Cost of a Data Breach Report, making insider-linked breaches the most expensive initial attack vector for the second year in a row. Old accounts can persist even when they are not in active use.
SOC 2 expects a clear, repeatable offboarding process. Access must be removed quickly every time. Offboarding that depends on memory instead of a defined workflow becomes an audit finding.
4. Ignored Logs
Most SaaS systems already collect logs across access, changes, and system activity. Collection is rarely the problem.
The gap appears in review. Logs sit untouched unless something breaks. Over time, the team stops noticing unusual access patterns or repeated failed login attempts until a security review surfaces them.
5. Underestimating Evidence Collection
Evidence collection takes more effort than most SaaS teams expect. Teams need to gather:
- Screenshots
- Access reviews
- Approval records
- System logs
These documents live across different tools and people. When the audit begins, the team ends up searching through scattered systems, which makes evidence collection slow and unreliable.
6. A Patchwork Tech Stack
As SaaS teams grow, they add tools quickly. Companies use an average of 112 SaaS applications, down from a 2022 peak of 130, according to BetterCloud’s State of SaaSOps 2024 report. Each tool solves a specific problem, and they do not always work well together.
Access, logging, and controls end up handled differently across systems. One tool may be tightly managed, another loosely configured. Teams lose a clear view of how systems connect and who owns which control.
How to Get Compliant Without Slowing Down Engineering
Run compliance on a parallel track separate from product sprints. Also, automate evidence collection so engineers aren’t pulled in manually. Plus, assign one dedicated compliance owner outside engineering to handle auditor requests, track evidence, and manage gaps.
1. Separate Compliance Work from Sprint Cycles
When you mix compliance tasks into product sprints, it creates two problems at once. Engineers lose focus. Evidence collection gets deprioritized when delivery pressure builds.
Therefore, run compliance on a parallel track with its own —
- Owner
- Calendar
- Backlog
Again, policy reviews, access audits, and vendor checks follow the audit calendar, not the product roadmap.
2. Automate Evidence Collection Early
Manual evidence collection takes up a lot of engineering time. Tasks, like screenshots, log exports, and access review records, repeat across the entire Type II window and usually fall on an engineer.
You can use automation tools to handle this continuously in the background. Access logs, configuration snapshots, and control activity get captured without anyone pulling them manually.
Meanwhile, your engineering team stays out of it entirely. The evidence is simply there when the auditor asks.
3. Assign a Compliance Owner Outside Engineering
When no one specifically owns compliance, engineers become the fallback. Every auditor request, policy gap, and missing log ends up in someone’s hands who should be shipping the product.
One dedicated owner, whether it’s internal or external, handles all of that coordination. They track —
- Evidence deadlines
- Manage auditor communication
- Flag control gaps before they become audit findings
Engineering has a clear boundary. Compliance gets someone accountable for it.
“With Bright Defense as your compliance partner, your engineering team stays focused on shipping features while we handle the complexity of SOC 2 — from policy creation to evidence collection and auditor coordination.”
What is The SOC 2 Audit Process?
The SOC 2 audit process is a structured review that happens across several activities.
- Audit Planning and Scoping Confirmation: This step defines what the audit will cover. Teams identify systems, tools, and data flows that handle customer data. That includes cloud infrastructure, code repositories, and internal processes.
- Request for Evidence: During this stage, auditors request documents and records to verify controls. This may include policies, access logs, and review records. Teams need to provide clear and organized evidence.
- Control Testing: In this stage, auditors test whether your controls work in practice. They review activities like access approvals, incident response actions, and change management steps. Testing often covers a period of time. Auditors check if controls were followed consistently.
- Walkthroughs and Interviews: Auditors speak with team members across functions. It may include engineering, HR, or operations. They review how processes actually work and compare them with documented controls.
- Findings and Management Responses: At this stage, auditors document any gaps or issues found during testing. Each finding is recorded in the report. It gives a clear view of where controls do not fully meet SOC 2 requirements.
- Report Drafting and Issuance: In this final stage, auditors compile the SOC 2 report. The report reflects how well controls meet the required criteria. Once issued, it becomes the formal document that companies can share during security reviews.
Which Is Better for SaaS: SOC 2 or ISO 27001?
SOC 2 is usually the better starting point for a SaaS company, while ISO 27001 becomes more valuable for global recognition and structured security management. The choice depends on what your customers expect during vendor evaluation.
SOC 2 provides a detailed auditor report that shows how your security controls perform over time. This format fits SaaS sales cycles where buyers request proof during security reviews, especially in U.S. markets.
ISO 27001 provides a formal certification that your company runs a risk-based information security management system. This certification carries strong international recognition and fits procurement-driven or global markets.
SOC 2 works better for closing deals with detailed assurance requirements. ISO 27001 works better for signaling long term governance and global credibility. Many SaaS companies adopt SOC 2 first, then add ISO 27001 as they scale.
For a side-by-side breakdown, see our comparison of SOC 2 vs. ISO 27001.
How Bright Defense Helps SaaS Companies Get SOC 2 Ready
Bright Defense helps you approach SOC 2 as an ongoing program, not a one-time audit. We work with you from early readiness all the way through your Type II audit period. That means your controls stay active and your evidence stays organized.
Here’s how we support your SOC 2 journey for your SaaS company —
- We turn your current setup into a clear SOC 2 roadmap
- We work alongside your team to put real controls in place
- We keep your audit evidence organized and ready throughout the year
- We stay on top of gaps and fixes as they come up, so small issues don’t turn into audit risks
- We guide your team on day-to-day security practices
This approach helps you avoid rushed audits and reduce gaps in evidence. It also helps to maintain a SOC 2 security posture that stands up during customer reviews and sales conversations.
If you want a clearer path to SOC 2 without handling everything alone, talk to our team about our SOC 2 consulting services.
FAQs
SOC 2 compliance for SaaS companies is a security framework that verifies how a company protects customer data. It focuses on controls related to security, availability, processing integrity, confidentiality, and privacy, based on the AICPA’s Trust Services Criteria.
SOC 2 is not legally required for SaaS companies. However, many customers and enterprise buyers expect it during security reviews. In practice, SOC 2 for SaaS companies becomes a business requirement when handling sensitive customer data or selling into regulated industries.
SOC 2 compliance typically takes between 3 to 12 months. The timeline depends on your current security setup, audit type, and readiness. Type I is faster, while Type II requires ongoing monitoring over several months.
After a SOC 2 audit, the auditor issues a report detailing your controls and their effectiveness. For SaaS companies, this report is shared with customers during security reviews. It remains valid for about 12 months, after which a new audit is required.
SOC 2 focuses on validating specific security controls through an audit report. On the other hand, ISO 27001 is a certification based on a full information security management system. SOC 2 is more common in the US, while ISO 27001 has broader global use.
The Trust Services Criteria cover Security, Availability, Processing Integrity, Confidentiality, and Privacy, and your SaaS scope typically includes the criteria that match what your product promises customers in contracts and security documentation.
Yes, Security is treated as the required baseline in SOC 2 reporting, with the other criteria added when your service commitments or customer requirements call for them.
Type I evaluates whether controls are designed appropriately at a point in time, while Type II evaluates design and operating effectiveness across an observation period that is commonly 3–12 months.
The system boundary is the defined set of services, infrastructure, people, processes, and data flows covered in the report’s system description, and it drives what controls must be documented and tested. AICPA description criteria are used to prepare and evaluate that system description during a SOC 2 examination.
Send a short security package that states your target report type (often Type II), your in-scope criteria, and your planned timing, then share what you already have such as policies, an architecture overview, and recent security testing artifacts, while keeping claims limited to what you can evidence. SOC 2 is meant for users who need detailed assurance, so a clear plan plus current controls evidence usually moves the deal forward while the report is in progress.
A common schedule includes prep work of 1–3 months, an observation period of 3–12 months, audit work of 2–5 weeks, and report creation of 2–6 weeks, with the observation period driving most of the calendar time.
Audit fees are commonly cited at $7,500–$15,000 for Type I for small to midsize companies and Type II often starting around $12,000–$20,000 for small to midsize companies, with larger scopes reaching $100,000+. Total first-year spend including prep work and the audit is commonly described in the $10K–$80K+ range, depending on readiness, tooling, and remediation workload. For a full breakdown of what to budget, see our guide to SOC 2 audit costs.
No, SOC 2 reports are generally treated as restricted-use reports shared with customers and prospects, while SOC 3 reports are general-use reports that can be freely distributed.
A stable approach uses ongoing control checks, steady evidence collection, and fast remediation when gaps appear, which matches the continuous monitoring concept of maintaining ongoing awareness of security, vulnerabilities, and threats to support risk decisions. A simple operating rhythm includes scheduled access reviews, change tracking, ticketed exceptions, and periodic restore tests so evidence exists throughout the Type II period instead of being rebuilt at the end.
It means a SaaS company has its controls examined against SOC 2 criteria such as security, availability, processing integrity, confidentiality, or privacy to show customers how it protects their data.
The Rule of 40 says a SaaS company’s revenue growth rate plus profit margin should total at least 40% as a quick measure of growth and profitability together.
Get In Touch