Updated:
March 1, 2026
SOC 1 vs SOC 2 vs SOC 3 – What’s the Difference?
Not all SOC reports serve the same purpose. While they may sound similar, SOC 1, SOC 2, and SOC 3 each focus on different types of risk, audiences, and use cases.
If you are unsure which one applies to your business or your customers are asking for one you are not familiar with, this breakdown will help clear things up.
In this guide, you will get a practical look at what each report covers, who it is meant for, and when to use it.
Key Takeaways
- SOC 1 focuses on financial controls and is relevant when your service affects customer financial reporting. It supports audits, SOX compliance, and financial assurance processes.
- SOC 2 centers on data protection and internal system controls tied to security, availability, processing integrity, confidentiality, and privacy. It’s a common requirement for SaaS and cloud providers.
- SOC 3 is a public summary of SOC 2 with no sensitive audit data. It helps companies demonstrate security maturity without disclosing internal details.
- You might need both SOC 1 and SOC 2 if your service impacts both financial systems and sensitive data. Start with the one your customers prioritize, then consider adding the other based on demand.
Everything About SOC 1
SOC 1 is an audit report focused on financial controls. It’s designed for situations where a company’s services and systems can affect its customers’ financial reporting or financial statements. In essence, SOC 1 evaluates whether the service organization has effective internal controls in place to ensure accurate and reliable financial data for their clients.
The main goal of SOC 1 is to provide assurance that these controls around financial information are suitably designed and operating effectively.
This report is not public. It’s shared with customers, auditors, and regulators under NDA.
What It Includes
- A description of the company’s systems and processes
- Details about service organization’s controls related to financial reporting
- The auditor’s opinion on whether those controls are designed and working properly
- Results of control testing
- Management’s assertion about control effectiveness
It’s detailed and often requested during SOX audits or financial reviews.
Two Types
- SOC 1 Type I: Reviews controls at a single point in time snapshot
- SOC 2 Type II: Tests how those controls perform over a set period (usually several months)
Most customers prefer Type II for more reliable assurance.
How It’s Created
- The company defines the scope, which systems and processes affect customer financials
- An independent auditor reviews the design and operation of related controls
- For Type II, the auditor tests those controls over time
- The report is shared with authorized parties
When To Use SOC 1
- You provide services that impact clients’ financial reporting
- Your customers ask for SOX compliance support
- You run payroll, billing, claims processing, or similar financial systems
Everything About SOC 2
SOC 2 is a detailed audit report that shows how a company safeguards customer data and system operations. It focuses on controls related to security, availability, processing integrity, confidentiality, and privacy, collectively known as the Trust Services Criteria (TSC) defined by the AICPA.
Unlike a SOC 3, a SOC 2 report is not public; it’s typically shared under NDA with customers, partners, or regulators who request it, because it contains in-depth information about your internal systems and controls.
SOC 2 is used in vendor reviews, risk assessments, and compliance automation programs. It proves that your internal systems and controls actually do what you claim.
What It Includes
- A full list of controls
- Details on how those controls were tested
- Results of testing, including any exceptions or gaps
- Management’s description of the system and security policies
- The auditor’s opinion on effectiveness
This report is detailed and often dozens of pages long.
Two Types
- SOC 2 Type I: Checks if the required controls are in place at a specific point in time. This evaluates the design and implementation of controls as of a certain date. Essentially, a Type I answers, “Were the right controls designed and present on Day X?”
- SOC 2 Type II: This report confirms security controls work consistently over time (3-12 months), making it the preferred standard for demonstrating higher assurance to customers and partners.
Type II is the standard for most buyers and partners.
How It’s Created
- The company defines which Trust Services Criteria apply
- An independent auditor reviews internal systems and controls
- For Type II, controls are tested over a fixed audit period
- The third party auditor delivers a report showing what passed, failed, or needs work
When To Use SOC 2
- You handle customer or partner data
- Your clients demand proof of security
- You need to pass vendor due diligence
- You want to build trust without exposing everything publicly (use SOC 3 for that)
Everything About SOC 3
SOC 3 is a publicly distributable version of a SOC 2 report. In essence, think of SOC 3 as a high-level, “redacted” SOC 2 Type II report.
It covers the same five Trust Services Criteria (security, availability, processing integrity, confidentiality, privacy) and provides an auditor’s assurance that the company meets those criteria, but it omits the detailed testing descriptions and results.
SOC 3 is meant for anyone to read (no NDA required), making it useful as a marketing and trust-building too.
SOC 3 gives companies a way to show proof of strong information security practices without handing out a full SOC 2 report. This is valuable when you want to demonstrate your security compliance to the general public or prospects who may not want (or be qualified) to parse a lengthy SOC 2.
What It Includes
- A short summary of the auditor’s opinion
- A statement from the company about its controls
- A high-level overview of the system
- A clear statement that it meets certified public accountants AICPA Trust Services Criteria
That’s it. No testing details, no control lists, no sensitive data.
How It’s Created
- The company completes a SOC 2 Type II audit
- If that audit is successful, the same auditor can issue a SOC 3
- The company can then publish the SOC 3 report online
When To Use SOC 3
- You need a public trust signal
- You want to show compliance without sharing internal details
- You already passed a SOC 2 Type II audit
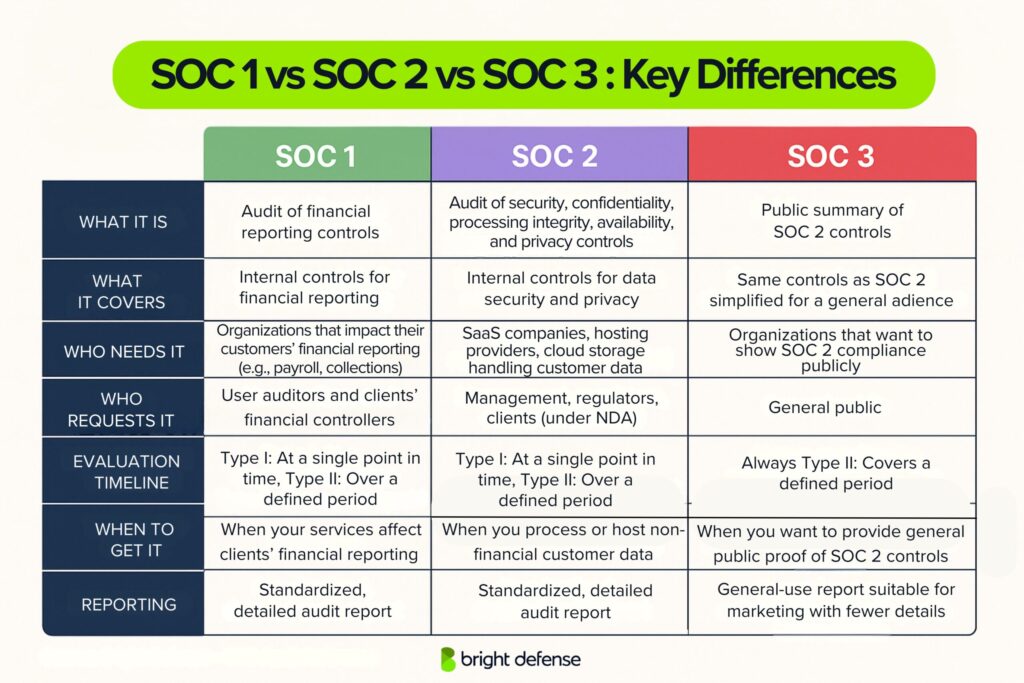
Key Differences Between SOC 1, SOC 2, and SOC 3 Reports
| Aspect | SOC 1 (Financial Controls) | SOC 2 (Security & Data Controls) | SOC 3 (Public Summary) |
|---|---|---|---|
| Purpose | Focuses on controls related to financial reporting. It is intended to provide assurance that a service provider’s systems won’t negatively impact clients’ financial statements. | Evaluates controls related to security, availability, processing integrity, confidentiality, and privacy. Shows that the organization has strong information security and IT practices. | Provides a summarized version of SOC 2 controls. Designed for general viewing, it confirms adherence to security criteria without sharing technical specifics. |
| Audience | Aimed at user entities and their financial auditors. Used by clients who rely on the service provider’s systems for financial reporting. Not meant for public sharing. | Shared with customers, partners, and compliance teams who need to evaluate the organization’s risk posture. Typically disclosed under a confidentiality agreement. | Intended for the general public and prospective customers. Useful for those who want basic assurance without needing full technical detail. |
| Content Detail | Offers in-depth descriptions of controls impacting financial records. Includes test procedures and detailed results. Structured for audit and compliance professionals. | Contains detailed analysis of technical and administrative security controls. Includes system architecture, policy reviews, test outcomes, and any observed exceptions. | Provides a high-level overview of the system and audit opinion. Does not include control tests or specific configurations. |
| Distribution | Restricted to clients, their auditors, and regulators. Often shared under NDA. Contains sensitive financial control data. | Also restricted and typically shared under NDA. Contains confidential security information, so it is not made public. | Freely shareable. Commonly posted on websites or used in marketing materials to demonstrate trust without disclosing internal systems. |
| Common Use Cases | Used when a service could impact a client’s financial reporting, such as payroll processors or financial software providers. Often required during financial audits. | Used by SaaS providers, cloud platforms, and IT services that handle customer data. Often requested during vendor assessments or by clients with strict security requirements. | Used in sales materials, trust pages, or public-facing resources to show compliance with security standards without revealing internal control frameworks. |
Which SOC Report Should You Choose?
The right SOC report depends on your services and what your clients need.
- SOC 1: Choose SOC 1 if your service involves clients’ financial reporting. This applies to payroll providers, accounting platforms, or claims processors. Clients (or their auditors) use SOC 1 to validate the accuracy of financial data impacted by your operations.
- SOC 2: Go with SOC 2 if your service manages customer data, system uptime, or security, common for SaaS, IT, or cloud-based platforms. It shows that you have controls in place for security, availability, and confidentiality. When clients ask for “security certifications,” they usually mean SOC 2.
- SOC 3: This is a public-facing version of SOC 2 (Type II). It shares the fact that you passed a SOC 2 audit without disclosing internal details. Use it as a trust signal on your website or in marketing. You can’t get a SOC 3 without completing SOC 2 first.
- Both SOC 1 & SOC 2: Some companies need both, especially fintechs or data-heavy platforms. One client might care about financial accuracy (SOC 1), while another wants proof of cybersecurity (SOC 2). Having both helps meet multiple stakeholder demands.
Tip: If you expect to need both, prepare for them in sequence. Many internal processes (like access control or change management) apply to both audits, so reusing that work can cut down on effort. Some firms combine readiness efforts to make the process more efficient.
Will You Need Both a SOC 1 and SOC 2 Report?
The right SOC report depends on the kind of services you offer and the type of data you handle for your customers.
If your service impacts financial reporting, for example payroll, billing, or accounting platforms, you will likely need a SOC 1 report.
If you host applications, manage infrastructure, or process sensitive customer data, then a SOC 2 report will be the right fit. SOC 3 reports are public summaries based on SOC 2 and are typically used to support marketing and trust communications.
Some companies end up needing both SOC 1 and SOC 2.
This happens when different clients have different priorities. One might focus on financial accuracy, while another wants proof of information security practices.
The good news is that the audit prep and readiness assessment can often overlap, which makes it easier to go through both at the same time. Many cloud service providers and firms working with enterprise customers face this situation.
What Are the SOC 2 Trust Services Criteria?
SOC 2 reports are built around five key Trust Services Criteria developed by the AICPA. These criteria define the areas a service organization’s controls must address to show strong internal controls for protecting customer data. Depending on the scope of the audit, a company may cover all five or focus on only a few.
Here are the five criteria:
1. Security
This is the core requirement in every SOC 2 report. It addresses how a company protects systems and data from unauthorized access, breaches, and other risks. Continuous monitoring plays a key role in maintaining this control over time.
2. Availability
This evaluates whether systems are accessible and usable as agreed with customers. It covers uptime, performance monitoring, and disaster recovery practices.
3. Processing Integrity
This ensures systems process data accurately, completely, and in a timely manner. It applies when the business handles transactions or automated processing.
4. Confidentiality
This focuses on protecting same information such as business secrets, internal documents, or customer agreements from unauthorized disclosure.
5. Privacy
This covers how personal information is collected, used, stored, and deleted. It applies to companies that handle customer or user data tied to an individual.
Each criterion includes specific control objectives and SOC compliance audit considerations. Most SOC 2 reports include Security by default and then add others based on the company’s services and customer expectations.
What is SOC 2 type 1 and SOC 2 type 2?
There are some key differences between SOC 2 Type I and SOC 2 Type II. Let’s look at what sets them apart and how each might apply to your organization.
SOC 2 Type I
- Evaluates the design and implementation of controls at a specific point in time
- Confirms that controls exist and are properly configured
- Covers only one date (e.g., March 31, 2025)
- Used by early-stage companies or those needing to show SOC audit readiness quickly
- Requires fewer artifacts and takes less time to complete
SOC 2 Type II
- Evaluates whether controls are functioning over a defined period (e.g., January 1 to June 30, 2025)
- Verifies ongoing performance and enforcement of controls
- Requires operational evidence like logs, access reviews, and support tickets
- Often requested by customers and regulators for higher assurance
- Takes longer to complete but carries greater credibility
| Aspect | SOC 2 Type I | SOC 2 Type II |
| Scope | Controls are reviewed at a single point in time | Controls are reviewed over a period (usually 3–12 months) |
| Focus | Confirms controls are designed and implemented correctly | Confirms controls are consistently operating as intended |
| Duration Covered | One specific date (e.g., March 31, 2025) | A defined range (e.g., January 1 to June 30, 2025) |
| Effort | Shorter process, less evidence required | Longer process, requires operational logs, reviews, and documentation |
| When to Use | Early-stage audits, fast procurement needs, or first-time certification | Ongoing vendor assurance, customer trust, and mature compliance requirements |
| Evidence Required | Control listings, policies, screenshots | Logs, audit trails, tickets, access reviews, and proof of operational activity |
How to Get SOC 2 Certified With Bright Defense
Getting a SOC 2 certification can be time consuming and expensive if you go in unprepared. Many teams spend months pulling together policies, chasing evidence, and figuring out what auditors expect. Bright Defense helps cut through that with a setup built for security focused, cloud native teams.
Our platform simplifies SOC 2 from the start. No bloated checklists. No generic playbooks. Just a clear path from setup to audit.
Step 1: Connect Your Stack
Bright Defense integrates with your cloud tools in minutes. We pull evidence automatically from AWS, GCP, GitHub, Okta, and more. No need to dig for screenshots or chase IT tickets.
Step 2: Map to SOC 2 Criteria
Once connected, the platform tracks required controls for security, availability, confidentiality, processing integrity, and privacy. You see what’s already in place and what still needs work. Control mapping follows standard SOC 2 trust service criteria and highlights where your controls meet or differ from the same controls used in similar audits.
Step 3: Fix Gaps with Help from Our Team
If anything is missing like a password policy, audit log, or vendor risk review, we flag it. You get clear and direct steps to close the gaps. Our team is available throughout the process, so you know exactly what service organization management and auditors expect regarding documented security controls.
Step 4: Get Audited
When you’re ready, we connect you with a SOC 2 auditor from our network. They know how Bright Defense works, which helps the process move quickly. Your evidence is already organized. We stay involved and help with responses during the audit to support your organization’s ability to meet SOC 2 standards.
Want to see how this works for your team
Talk to us before you start chasing policies or pulling data. Bright Defense gives you a direct path to SOC 2 compliance that’s fast, clear, and built for security teams who already have enough on their plate.
FAQs
A SOC 1 report covers controls at a service organization that are likely relevant to a customer’s internal control over financial reporting, and it is intended for user entities and their financial statement auditors.
A SOC 2 report covers controls relevant to security, availability, processing integrity, confidentiality, or privacy for a service organization’s system.
A SOC 3 report addresses the same Trust Services Criteria areas as SOC 2 but provides less detail, and it is considered a general-use report that can be freely distributed.
SOC 1 is about controls that matter to customers’ financial reporting, while SOC 2 is about controls that matter to security and related Trust Services Criteria categories.
SOC 2 is the more detailed report intended for restricted use, while SOC 3 is a less detailed, general-use report intended for broad sharing.
SOC 1 is the usual request when your service can impact a customer’s financial reporting, while SOC 2 is the usual request when the customer wants security and data-handling assurance for your service.
Yes, a SOC 3 report can be shared publicly, while SOC 1 and SOC 2 reports are commonly handled under NDA in many vendor programs.
A SOC 3 report supports a quick public assurance check, and a SOC 2 report is the next ask when you need the detailed testing and results for a deeper vendor review.
SOC 1 reports cover controls at a service organization that matter to a customer’s internal control over financial reporting (ICFR), SOC 2 reports cover controls tied to the Trust Services Criteria (security, availability, processing integrity, confidentiality, privacy), and SOC 3 reports cover the same trust topics as SOC 2 but in a general-use format with less detail.
No, SOC 3 is not better than SOC 2 for vendor due diligence because SOC 3 has less detail, while SOC 2 is meant for users who need detailed information and assurance about controls.
L1 (Tier 1) SOC analysts monitor alerts and do initial triage, L2 (Tier 2) analysts perform deeper incident analysis and containment/recovery work, and L3 (Tier 3) analysts handle major escalations and proactive threat hunting, often supervising advanced testing activities.
Get In Touch