Updated:
March 24, 2026
80+ Zero-Day Exploit Statistics (March – 2026)
Zero-day exploitation hit 90 confirmed cases in 2025, up 15% from the prior year, with nearly half of all attacks targeting enterprise infrastructure. For the first time, commercial surveillance vendors outpaced nation-state espionage groups as the leading source of attributed zero-day exploitation.
With those numbers as a backdrop, the team at Bright Defense has compiled a comprehensive list of up-to-date, sourced zero-day exploit statistics for 2025 and 2026. Every figure is drawn from primary research by Google Threat Intelligence Group, VulnCheck, Mandiant, Forescout Vedere Labs, IBM, Google Project Zero, and Crowdfense. In this article, you’ll find hand-picked statistics about:
- Zero-day exploitation volume and year-over-year trends
- Enterprise vs. end-user zero-day targeting
- Weaponization speed and time-to-exploit
- Operating system, browser, and mobile zero-day vulnerabilities
- Most targeted vendors and platforms
- Threat actor attribution: nation-states, commercial surveillance vendors, and financially motivated groups
- Zero-day market economics and exploit pricing
- Financial impact of zero-day breaches
- Detection challenges, defensive strategies, and notable zero-day attacks in history
Without further ado, let’s check out the stats!
Zero-Day Exploitation Volume and Year-Over-Year Trends
- Google Threat Intelligence Group tracked 90 detected zero-day exploits in 2025. (Google GTIG)
- That count is 15% higher than the revised 2024 figure of 78. (Google GTIG)
- Google tracked 100 exploited zero-days in 2023, which remains the record high. (Google GTIG)
- In 2022, Google tracked 63 exploited zero-days. (Google GTIG)
- Annual zero-day volume has remained within a 60 to 100 range across the past four years. (Google GTIG)
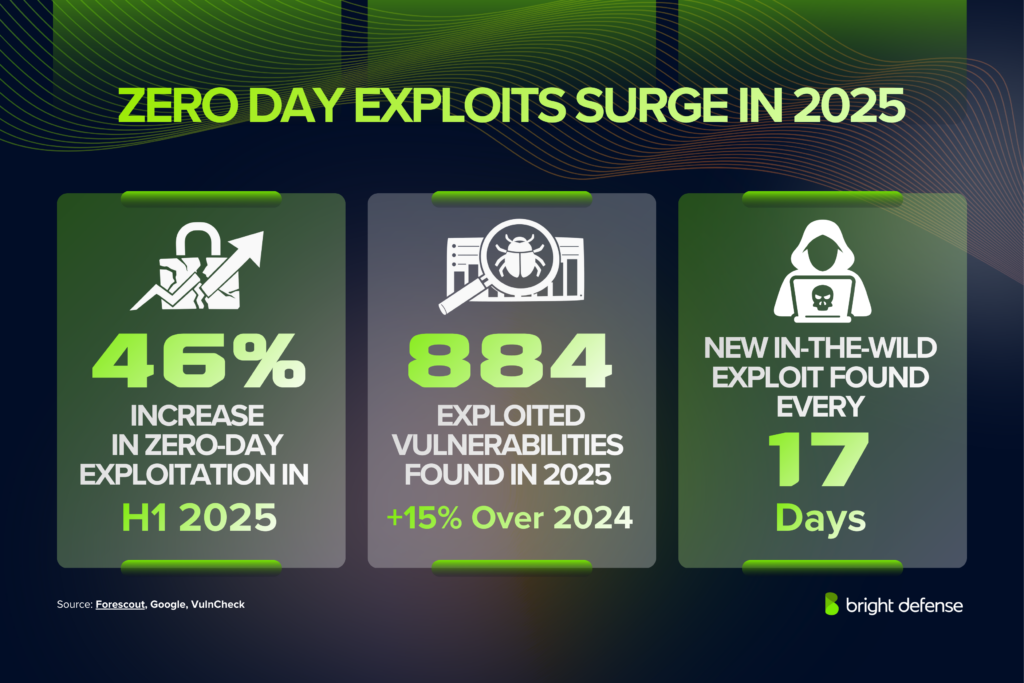
- Forescout Vedere Labs measured a 46% increase in zero-day exploitation during H1 2025 alone. (Forescout)
- VulnCheck identified 884 known exploited vulnerabilities with first-time exploitation evidence in 2025, a 15% increase over 2024. (VulnCheck)
- 41% of CVEs added to the CISA Known Exploited Vulnerabilities catalog in 2025 were zero-days. (Todyl)
- Google Project Zero data shows a new in-the-wild exploit is discovered every 17 days on average. (Project Zero)
- Only 1% of the roughly 48,000 CVEs reported in 2025 were confirmed exploited in the wild. (VulnCheck)
Annual zero-day exploitation counts have settled into an elevated baseline that far exceeds pre-2021 levels. These statistics track the scale and direction of the problem.
Enterprise vs. End-User Zero-Day Targeting
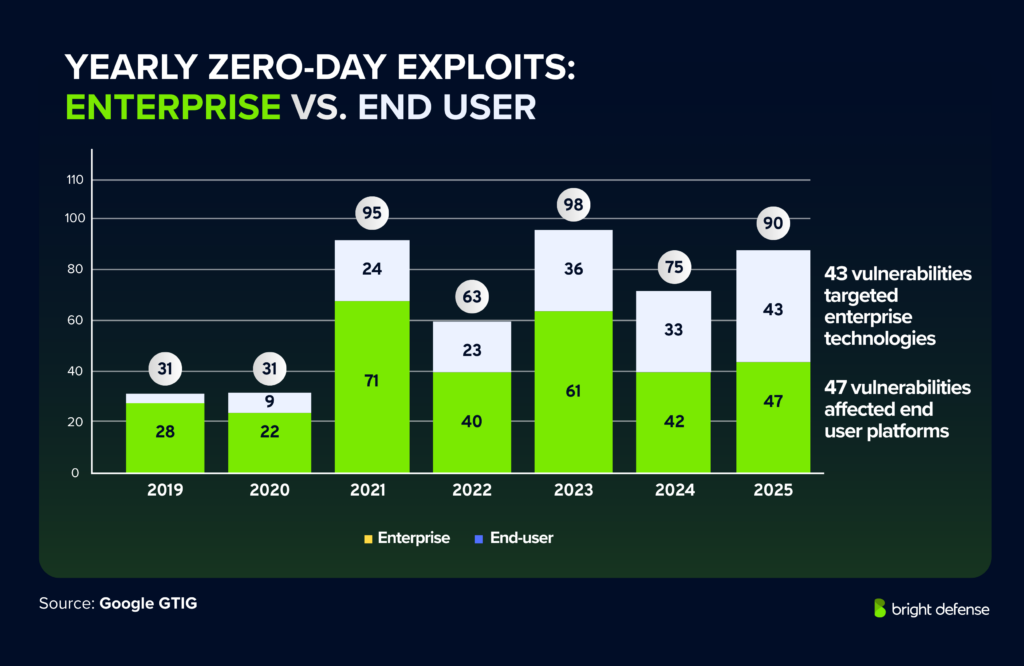
- Enterprise technologies accounted for 43 zero-days in 2025, representing 48% of all tracked zero-day exploitation. (Google GTIG)
- Both the raw number and the share of enterprise-targeted zero-days reached all-time highs in 2025. (Google GTIG)
- End-user platforms accounted for 47 zero-days (52%) in 2025. (Google GTIG)
- Security and networking products accounted for 21 of the 43 enterprise zero-days in 2025, roughly half. (Google GTIG)
- Google identified 14 edge-device zero-days in 2025, noting the real total is likely higher because detection on edge devices is weak. (Google GTIG)
- In 2024, 33 enterprise zero-days represented 44% of all tracked zero-day exploitation. (Google GTIG)
- The enterprise count rose from 33 in 2024 to 43 in 2025, a gain of 10. (Derived from Google GTIG data)
- In 2024, 20 of 33 enterprise zero-days targeted security and networking devices, accounting for over 60% of enterprise zero-day exploitation. (Google GTIG)
- 90% of all vendors targeted by zero-days in 2024 were enterprise vendors (18 of 20 total). (Derived from Google GTIG data)
- In 2023, 22 of 23 targeted vendors were enterprise vendors, approximately 95.7%. (Derived from Google GTIG data)
- Enterprise software exhibits a consistent struggle: networking devices highlights the value attackers place on trusted edge infrastructure that lacks endpoint detection. (Google GTIG)
The targeting split between enterprise technologies and consumer platforms reveals a significant trend toward corporate infrastructure. Attackers are deliberately choosing products that offer broad network access and fewer detection opportunities.
Zero-Day Weaponization Speed and Time-to-Exploit
- 28.96% of known exploited vulnerabilities in 2025 had exploitation evidence on or before the day the CVE was published. (VulnCheck)
- The comparable figure for 2024 was 23.6%, meaning the on-or-before-publication rate rose by 5.36 percentage points year over year. (VulnCheck)
- Rapid7 reported that 53% of new widespread-threat vulnerabilities through the start of 2024 were exploited before vendors could issue fixes. (Rapid7)
- Rapid7 found that 43% of known exploited CVEs in its dataset since January 2021 were zero-days. (Rapid7)
- Of those zero-day cases, 55% were exploited within one week of public disclosure, and 60% within two weeks. (Rapid7)
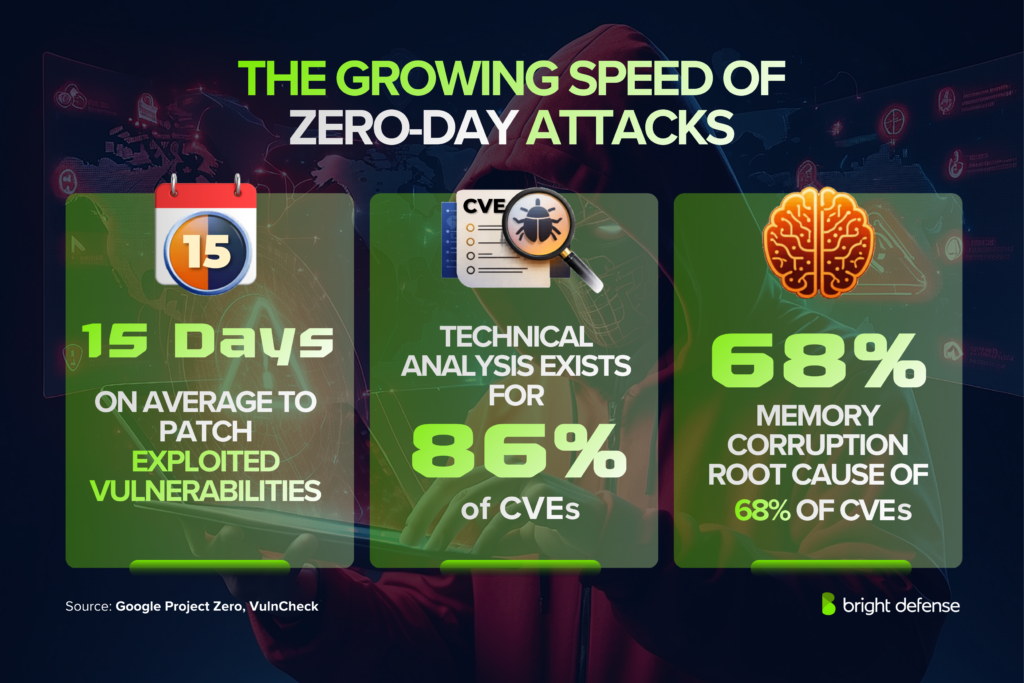
- Vendors take 15 days on average to patch actively exploited vulnerabilities. (Project Zero)
- A detailed technical analysis on root cause exists for 86% of CVEs in the Project Zero tracking list. (Project Zero)
- Memory corruption is the root cause of 68% of listed CVEs in the Project Zero tracker. (Project Zero)
- VulnCheck found 118 unique sources were first to publicly report exploitation activity in 2025. (VulnCheck)
- 47.7% of VulnCheck KEVs in 2025 carried 2025 CVE identifiers, underscoring the speed of weaponization. (VulnCheck)
The disclosure-to-exploitation window is collapsing. Organizations with limited resources requiring deciding which patches to apply first face an increasingly hostile timeline.
Operating System Zero-Day Vulnerabilities
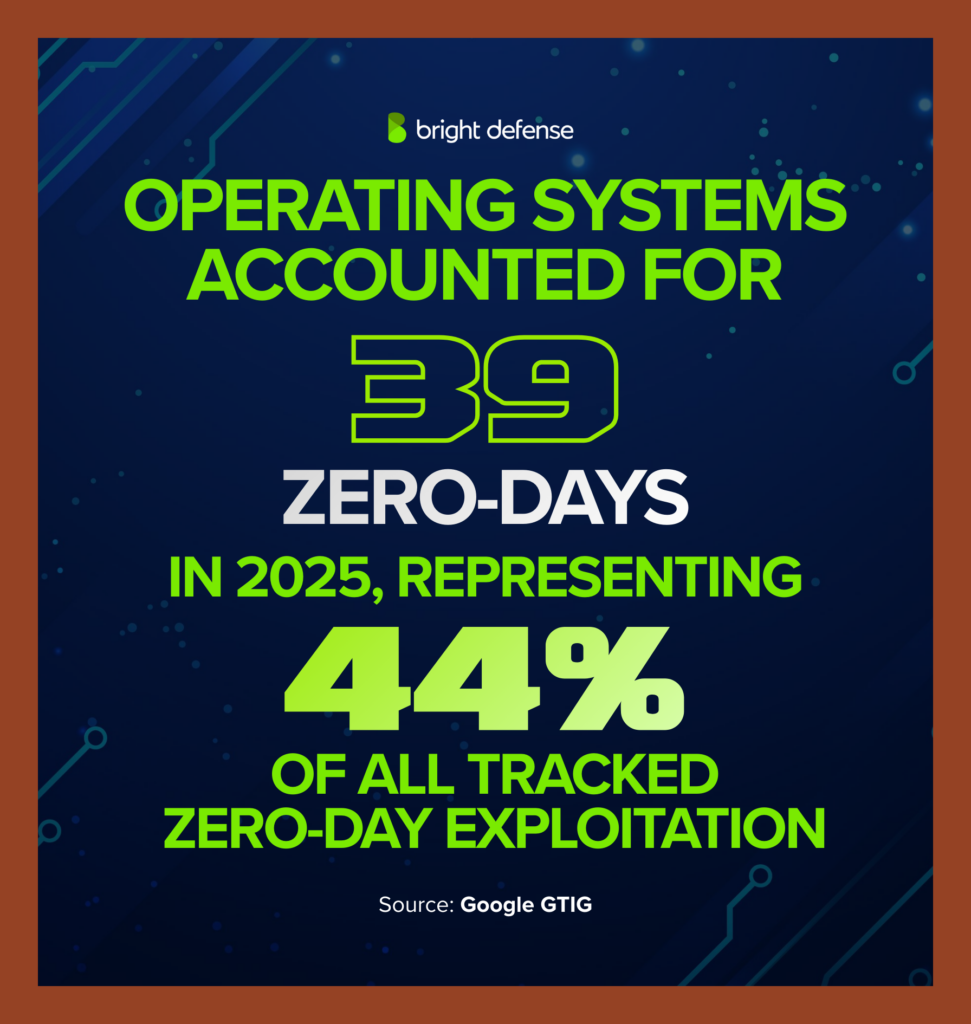
- Operating systems accounted for 39 zero-days in 2025, representing 44% of all tracked zero-day exploitation. (Google GTIG)
- The OS share rose from 40% in 2024 to 44% in 2025, and from 33% in 2023. (Google GTIG)
- In 2024, operating systems accounted for 31 zero-days. In 2023, the figure was 33. (Google GTIG)
- Desktop OS zero-days have fluctuated between 16 and 23 per year in recent years, with a gradual upward trajectory. (Google GTIG)
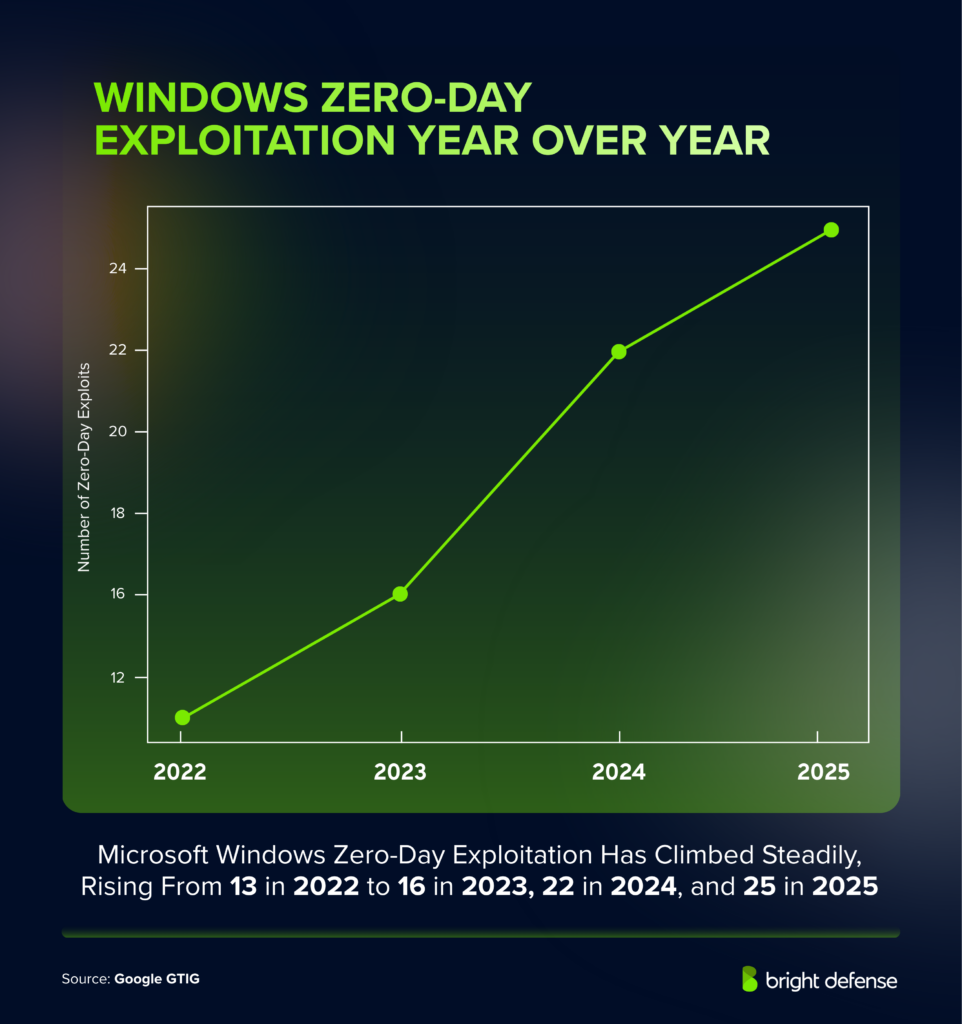
- Microsoft Windows zero-day exploitation rose from 13 in 2022 to 16 in 2023 to 22 in 2024. (Google GTIG)
- Mobile operating system exploitation reached 15 zero-days in 2025, up from 9 in 2024, though still below the 17 tracked in 2023. (Google GTIG)
- Exploit chains made up of multiple zero-days are used almost exclusively (around 90%) against mobile devices. (Google GTIG)
- Multiple exploit chains discovered in 2025 included three or more vulnerabilities. (Google GTIG)
- Google found more complete exploit chains in 2025 than in earlier years, when sometimes only partial chains or a single vulnerability was identified. (Google GTIG)
Operating systems remain the most exploited product category, reflecting the broad attack surface they present across desktop and mobile environments.
Browser and Mobile Zero-Day Exploitation Trends
- Browsers accounted for less than 10% of all tracked zero-day exploitation in 2025. (Google GTIG)
- Browser zero-days fell from 17 in 2023 to 11 in 2024 to just 8 in 2025, the lowest figure Google has recorded. (Google GTIG)
- None of the browser sandbox escapes analyzed in 2025 were generic to the browser sandbox itself; they targeted the underlying operating system or hardware. (Google GTIG)
- Chrome was the primary browser target in 2024. (Google GTIG)
- In 2024, 3 of 7 Android zero-days were in third-party components. In 2023, 5 of 7 Android zero-days were in third-party components. (Google GTIG)
- Mobile zero-days rebounded from 9 in 2024 to 15 in 2025 as commercial surveillance vendors expanded their exploit chains to bypass newer security boundaries. (Google GTIG)
Browser zero-day exploitation dropped to historical lows in 2025, a shift that security leaders attribute to stronger browser security hardening and improved attacker operational security.
Vendors and Platforms Most Targeted by Zero-Day Exploits
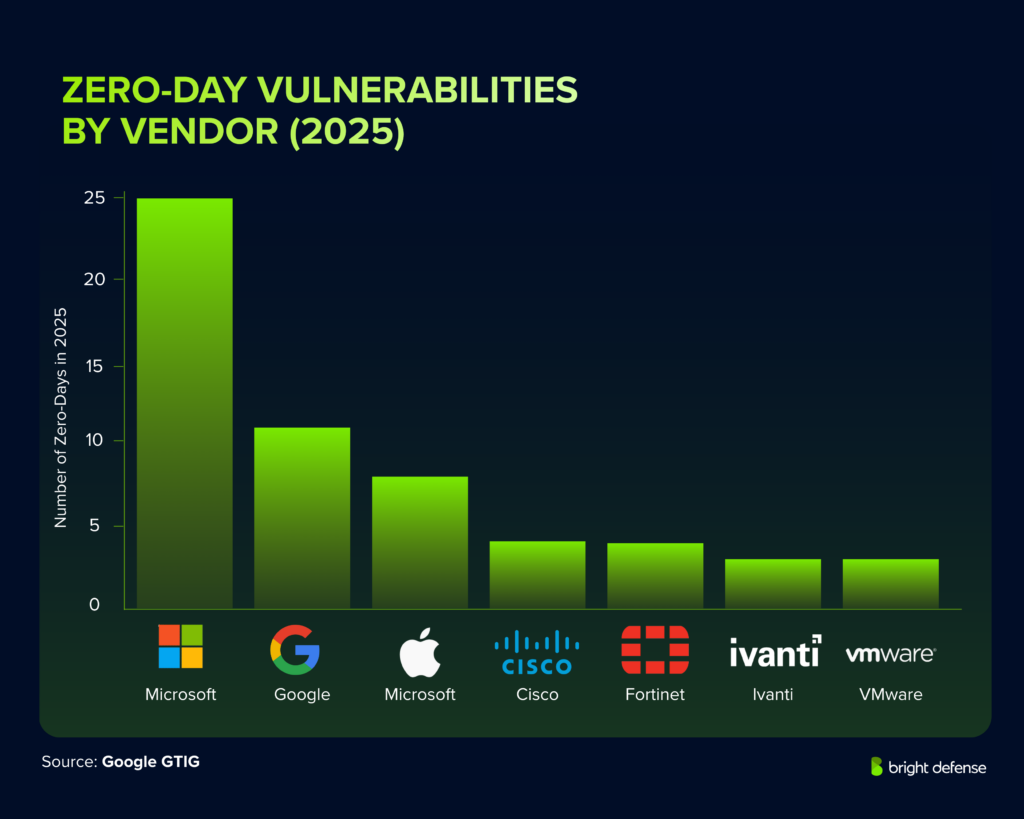
- Microsoft led targeted vendors with 25 zero-days in 2025, followed by Google (11), Apple (8), Cisco (4), Fortinet (4), Ivanti (3), and VMware (3). (Google GTIG)
- Google identified 18 unique enterprise vendors targeted in 2024, out of 20 total targeted vendors. (Google GTIG)
- In 2023, Google tracked 22 unique enterprise vendors targeted, out of 23 total. (Google GTIG)
- Forescout found Microsoft products accounted for approximately 30% of H1 2025 zero-day exploitation, followed by Google at 11% and Apple at 8%. (Forescout)
- Network edge devices were the most frequently targeted technologies in 2025 according to VulnCheck, with 191 KEVs identified. (VulnCheck)
A handful of major vendors absorb the bulk of zero-day exploitation, reflecting their massive install bases and the value attackers place on gaining access to widely deployed security and networking products.
Zero-Day Threat Actor Attribution
Who is exploiting zero days? Google attributed exploitation for 42 of the 90 tracked zero-days in 2025, giving the clearest picture yet of the actors behind the attacks.

Commercial Surveillance Vendors Take the Lead
- For the first time, commercial surveillance vendors surpassed state-sponsored espionage groups in attributed zero-day exploitation in 2025, with 15 attributed zero-days versus 12 for nation-state groups. (Google GTIG)
- Three additional zero-days were marked as "likely CSV," bringing the potential total to 18. (SecurityWeek)
- Commercial surveillance vendors focused heavily on mobile and browser exploit chains, adapting to bypass newer security boundaries on mobile devices. (Google GTIG)
Nation-State Espionage: China's Persistence and North Korea's Surge

- China-linked groups were the most active state-sponsored threat actors in 2025, with at least 10 attributed zero-days, double the 5 from 2024. (Google GTIG)
- The 2025 PRC-linked count was still below the 2023 level of 12. (Google GTIG)
- Just over half of attributed zero-day exploitation by state-sponsored espionage groups in 2025 focused on edge devices and security appliances. (Google GTIG)
- In 2024, PRC-linked groups were tied to 5 zero-days, and North Korean state actors were tied to 5 zero-days. (Google GTIG)
- 2024 was the first year since 2012 that North Korean actors tied for the highest attributed total among state-sponsored groups. (Google GTIG)
- In 2025, Google did not attribute any zero-days to North Korean groups. (Google GTIG)
- In 2024, traditional espionage actors accounted for nearly 53% of attributed zero-day exploitation (18 zero-days total). (Google GTIG)
- Of those 18 espionage-linked zero-days in 2024, 10 were tied to likely nation-state groups and 8 to commercial surveillance vendors. (Google GTIG)
Financially Motivated Threat Groups
- In 2025, financially motivated threat groups were attributed 9 zero-days, up from 5 in 2024, nearly tying the prior high of 10 in 2023. (Google GTIG)
- 2 of those 9 financially motivated actors' zero-days in 2025 led to ransomware deployment. (Google GTIG)
- 56.4% of 2025 ransomware CVEs were first identified through active zero-day exploitation. (VulnCheck)
- Mandiant found that 55% of threat groups active in 2024 were financially motivated, a steady increase year over year. (Mandiant M-Trends 2025)
Zero-Day Exploits as the Top Initial Access Vector
- For the fifth consecutive year, exploits were the most commonly observed initial access vector, responsible for 33% of all intrusions investigated by Mandiant. (Mandiant M-Trends 2025)
- The four most frequently exploited vulnerabilities in 2024 were all contained in edge devices such as VPNs, firewalls, and routers. (Mandiant M-Trends 2025)
- Stolen credentials overtook phishing as the second most common initial access method in 2024, at 16%, compared to 14% for phishing. (Mandiant M-Trends 2025)
- Mandiant was unable to determine an initial access vector for 34% of 2024 intrusions, indicating potential deficiencies in enterprise logging and detection capabilities. (Mandiant M-Trends 2025)
- Data theft occurred in approximately 66% of investigated cases. (Mandiant M-Trends 2025)
Vulnerability exploitation remains the dominant method attackers use to gain access to target networks.
Zero-Day Market Economics
- A working zero-click smartphone exploit (Android or iOS) is priced up to $9 million by vulnerability broker Crowdfense. (Crowdfense)
- Crowdfense offers $5 million to $7 million for iOS zero-days and up to $5 million for Android zero-days. (SecurityWeek)
- Chrome and Safari zero-days command $3 million to $3.5 million on the Crowdfense acquisition program. (SecurityWeek)
- WhatsApp and iMessage zero-days are valued at $3 million to $5 million. (Crowdfense)
- Russian zero-day acquisition firm Operation Zero has offered up to $20 million for full exploit chains targeting iOS and Android. (TechCrunch)
- Zero-day exploit prices have been inflating at an estimated 44% annually over the past decade, driven by stronger platform hardening and higher demand from intelligence agencies and financially motivated actors. (Industry estimates)
The economics of the zero-day market create a structural incentive problem. Proper implementation standards for bug bounty programs can offer researchers a legitimate path to disclosure, but government and private-sector payouts routinely dwarf those rewards by orders of magnitude.
Financial Impact of Zero-Day Breaches
- Average data breach cost reached $4.88 million in 2024, a 10% increase and the largest yearly jump since the pandemic. (IBM)
- 70% of breached organizations reported the breach caused significant or very significant disruption. (IBM)
- Organizations extensively using AI in security operations experienced average breach costs of $3.84 million versus $5.72 million for those without AI. (IBM)
- The healthcare sector faced the highest breach costs of any industry, with attacks on critical systems carrying premium financial consequences. (IBM)
- The average time to identify and contain a breach stood at 258 days for identification and 64 days for containment. (IBM)
The economic damage from zero-day attacks extends far beyond the immediate technical response.
Detection Challenges of Zero-Day Exploits
- Google noted that in 2024, attribution covered just under half of all tracked zero-day cases, well above the roughly 30% attribution level reported for 2022. (Google GTIG)
- Google says the 14 edge-device zero-days identified in 2025 likely understate the real total because detection on security appliances and edge gear remains weak. (Google GTIG)
- Mandiant could not determine the initial access vector in 34% of 2024 investigations, pointing to gaps in logging and monitoring across high-value targets. (Mandiant M-Trends 2025)
- Security and networking devices sit at the network edge and often lack EDR capabilities, making them invisible to many detection tools. This gap in visibility makes these devices ideal high-value targets for state-sponsored threat actors seeking persistent, undetected access. (Google GTIG)
- Improved attacker operational security has reduced visible browser exploitation, meaning some zero-day attacks are simply never detected. (Google GTIG)
Detecting zero-day attacks presents unique difficulty because no prior signature, indicator, or patch exists at the time of exploitation.
What Is a Zero-Day Exploit?
A zero-day exploit is a cyberattack that targets a software vulnerability that the vendor or developer has not yet fixed or publicly disclosed. The term “zero-day” indicates that the software creator has had zero days to release a patch or mitigation.
Attackers use this hidden flaw to run malicious code, gain unauthorized access, steal data, or disrupt systems before security teams recognize the weakness.
Security researchers often report these vulnerabilities once they are found, which allows vendors to develop and release updates. Systems remain at high risk until a patch becomes available and organizations apply the fix.
The Zero-Day Lifecycle
The zero-day lifecycle is the sequence a software vulnerability follows from its existence in code to its eventual remediation. A zero-day begins as an undiscovered flaw, becomes dangerous once someone finds and weaponizes it, and ends when the vendor releases a fix and affected organizations apply it.
- Vulnerability Exists: A coding error, design flaw, or insecure implementation creates a weakness in software, hardware, or firmware. The flaw remains unknown to the vendor and users at this stage.
- Discovery: A threat actor, security researcher, or internal team identifies the hidden vulnerability. The issue becomes a true zero-day when it is known to someone who can act on it before a patch is available.
- Exploit Development: An attacker or researcher builds a method to trigger the flaw. This exploit may allow remote code execution, privilege escalation, data theft, or system disruption.
- Active Exploitation: Attackers use the exploit against real targets. Defenders face the highest risk during this period because no official patch exists and detection guidance may be limited.
- Disclosure: The vulnerability becomes known to the vendor, the public, or both. Disclosure may happen through responsible reporting, incident response findings, or public exposure after attacks begin.
- Patch Creation: The vendor investigates the root cause and develops a security update or mitigation. This stage may include temporary workarounds before a full fix is ready.
- Patch Release And Remediation: The vendor publishes the patch, and organizations deploy it across affected systems. The vulnerability stops being a zero-day once a fix is available, though risk can continue until patching is complete.
Types Of Zero-Day Vulnerabilities And Attacks
Zero-day vulnerabilities and attacks usually fall into these main categories:
- Remote code execution: A remote code execution zero-day lets attackers run malicious code on a target system from another device or over the internet. This type often gives threat actors an immediate path to install malware, deploy ransomware, or take control of a server or endpoint without physical access.
- Privilege escalation: A privilege escalation zero-day allows attackers to gain higher permissions than their account or process should have. This type is often used after initial access because it helps attackers move from a limited user account to administrator or root-level control.
- Authentication bypass: An authentication bypass zero-day gives attackers access to systems, applications, or accounts without valid credentials. This weakness can expose sensitive environments because it removes one of the main barriers that normally blocks unauthorized users.
- Memory corruption: A memory corruption zero-day exploits flaws in the way software handles memory, such as buffer overflows or use-after-free errors. These issues can lead to arbitrary code execution, application crashes, or unstable system behavior depending on how the flaw is triggered.
- SQL injection: An SQL injection zero-day targets web applications that fail to properly handle database queries. Attackers can use this type to read, modify, or delete stored data, which makes it especially dangerous for customer records, financial details, and login systems.
- Cross-site scripting: A cross-site scripting zero-day allows attackers to inject malicious scripts into web pages that other users load in their browsers. This type can lead to session theft, credential capture, malicious redirects, or unauthorized actions performed in a victim’s account.
- Command injection: A command injection zero-day occurs when an application passes unsafe input to the operating system and allows attackers to run commands on the host. This type can result in full server compromise, data theft, or the installation of backdoors for continued access.
- Denial of service: A denial-of-service zero-day causes a system, service, or application to crash, freeze, or become unavailable. This type does not always give attackers direct access, though it can create serious operational disruption and affect business continuity.
- Browser and plugin exploits: A browser or plugin zero-day targets web browsers, extensions, or related components that users interact with every day. Attackers often use these flaws in phishing campaigns or compromised websites to infect devices when a user visits a page or opens web content.
- Operating system kernel exploits: An operating system kernel zero-day targets the core part of the OS that manages hardware and system resources. This type is especially serious because successful exploitation can give attackers deep control over the device and let them bypass built-in security protections.
- Mobile device exploits: A mobile device zero-day affects smartphone operating systems, messaging apps, browsers, or other mobile software components. These flaws are often valuable in surveillance, espionage, and targeted intrusions because they can expose messages, calls, location data, and stored files.
- Network service exploits: A network service zero-day targets internet-facing systems such as VPNs, firewalls, email servers, web servers, or remote management tools. These flaws are highly dangerous because they can give attackers an initial foothold in an organization without requiring user interaction.
Defensive Strategies Against Zero-Day Exploits
Defending against zero-day attacks requires moving beyond traditional patch-based security toward architectures that assume breach.
1. Reduce the Attack Surface
Minimize internet-exposed services. Audit and harden all edge devices, security appliances, and VPN gateways. Disable unnecessary features and restrict administrative interfaces from public access, focusing on disabling specific services that are not business-critical.
2. Deploy Behavioral and Anomaly-Based Detection
Signature-based tools cannot catch what has never been seen. Security teams need behavioral analytics that flag unusual network activity, unexpected privilege escalation, or anomalous data flows across affected systems.
3. Implement Network Segmentation and Least Privilege
Segment networks so a compromised edge device cannot provide direct lateral access to critical systems. Apply least-privilege access controls to every user, service account, and system process.
4. Maintain a Real-Time Asset Inventory (SBOM)
When a new zero-day drops, the first question is which systems are affected. A current Software Bill of Materials (SBOM) lets security teams identify exposure within hours rather than days.
5. Monitor Threat Intelligence Feeds
Consume real-time threat intelligence from sources like Google GTIG, VulnCheck, CISA KEV, and Mandiant. Automated ingestion of threat intelligence feeds directly into SIEM and SOAR platforms shortens response time.
6. Invest in Endpoint Detection and Response (EDR) for Edge Devices
The consistent struggle with edge-device exploitation stems from a lack of EDR visibility. Prioritize solutions that can monitor firmware integrity, detect configuration changes, and alert on anomalous traffic from these devices.
10 Notable Zero-Day Attacks in History
Zero-day attacks exploit software flaws before a patch exists, giving defenders no time to respond.
The following incidents show how a single unpatched vulnerability can escalate into widespread data theft, operational disruption, or long-term surveillance:
1. MOVEit Hack Hit Thousands Worldwide
Breach Disclosed: 31 May, 2023

The MOVEit Transfer breach was publicly disclosed on 31 May, 2023, after Progress Software warned customers about a zero-day SQL injection flaw, tracked as CVE-2023-34362, that let attackers reach backend databases without authentication.
The CL0P extortion group exploited the bug from at least 27 May, 2023, deployed the LEMURLOOT web shell, and stole data from exposed file-transfer servers. The fallout spread through vendors, government bodies, universities, and major enterprises, turning one software flaw into a large-scale supply-chain data theft event.
Progress issued patches on 31 May, 2023, then released more fixes in June 2023 as additional related flaws surfaced.
2. Barracuda ESG Breach Forced Device Replacements
Breach Disclosed: 19 May, 2023

Barracuda disclosed the Email Security Gateway zero-day on 19 May, 2023, after finding a remote command injection flaw, CVE-2023-2868, in affected ESG appliances. Attackers exploited the bug through malicious email attachments, gained code execution, and in some cases kept access even after the initial patch.
Barracuda pushed a remediation update on 20 May, 2023, but the investigation later showed some compromised devices could not be trusted to remain clean. That finding changed the response from patch-and-monitor to full appliance replacement for impacted customers. The incident became a notable reminder that edge email gateways can turn into persistent intrusion points when exploitation reaches the underlying appliance.
3. WinRAR Flaw Let Fake Files Hide Malware
Breach Disclosed: 02 Aug, 2023

The WinRAR archive spoofing issue became publicly actionable on 02 Aug, 2023, when WinRAR 6.23 shipped a full fix for CVE-2023-38831 after a beta patch on 20 Jul, 2023. The bug let a crafted archive display a harmless-looking file, such as a JPG or TXT, while launching hidden malicious content when the user opened it.
Group-IB reported the flaw after seeing active exploitation against traders and other targets, and MITRE assigned the CVE on 15 Aug, 2023. The practical risk centered on user deception, because the archive view masked the real executable path and made malware delivery look routine and trustworthy to the victim. (WinRAR download free and support)
4. Chrome Zero-Day Patch Closed Active Attacks
Breach Disclosed: 25 Mar, 2022
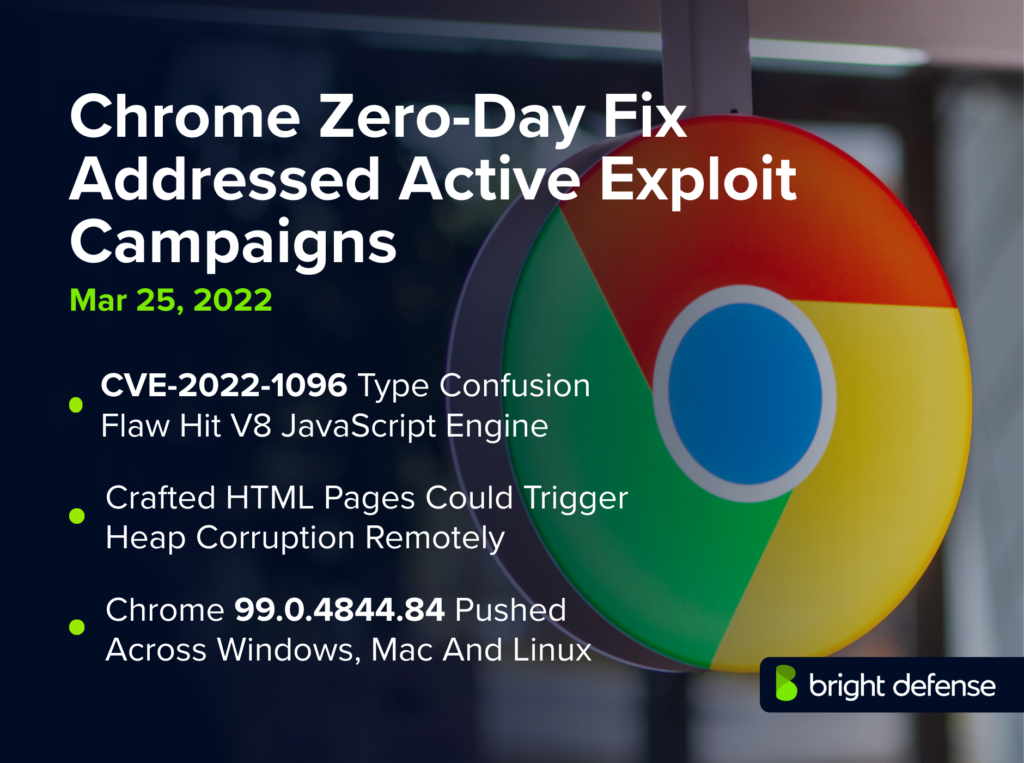
Google publicly disclosed this Chrome V8 zero-day on 25 Mar, 2022, when it released Chrome 99.0.4844.84 for Windows, Mac, and Linux to fix CVE-2022-1096, a type confusion flaw in the V8 JavaScript engine. The company said it was aware of reports that an exploit existed in the wild, which placed the issue in active-attack territory rather than routine patching.
A successful exploit could let a remote attacker trigger heap corruption through a crafted HTML page and potentially escape normal browser safety boundaries. The response timeline was fast and direct: publish the advisory, push the stable update, and restrict technical details until more users had patched.
5. Log4Shell Sparked A Global Java Panic
Breach Disclosed: 09 Dec, 2021

The Apache Log4j crisis broke into public view on 09 Dec, 2021, when CVE-2021-44228, widely called Log4Shell, was disclosed as a critical remote code execution flaw in the Log4j 2 Java logging library. The bug let attackers trigger JNDI lookups through crafted log messages and, in many cases, execute code on exposed systems without valid credentials.
Because Log4j sat deep inside countless enterprise apps, cloud services, and security tools, the issue turned into a rapid global incident response exercise. Apache released Log4j 2.15.0 first, then follow-on fixes in December 2021 as related weaknesses surfaced and defenders raced to inventory, patch, and hunt for exploitation.
6. Kaseya Attack Crippled MSPs In One Blow
Breach Disclosed: 02 Jul, 2021
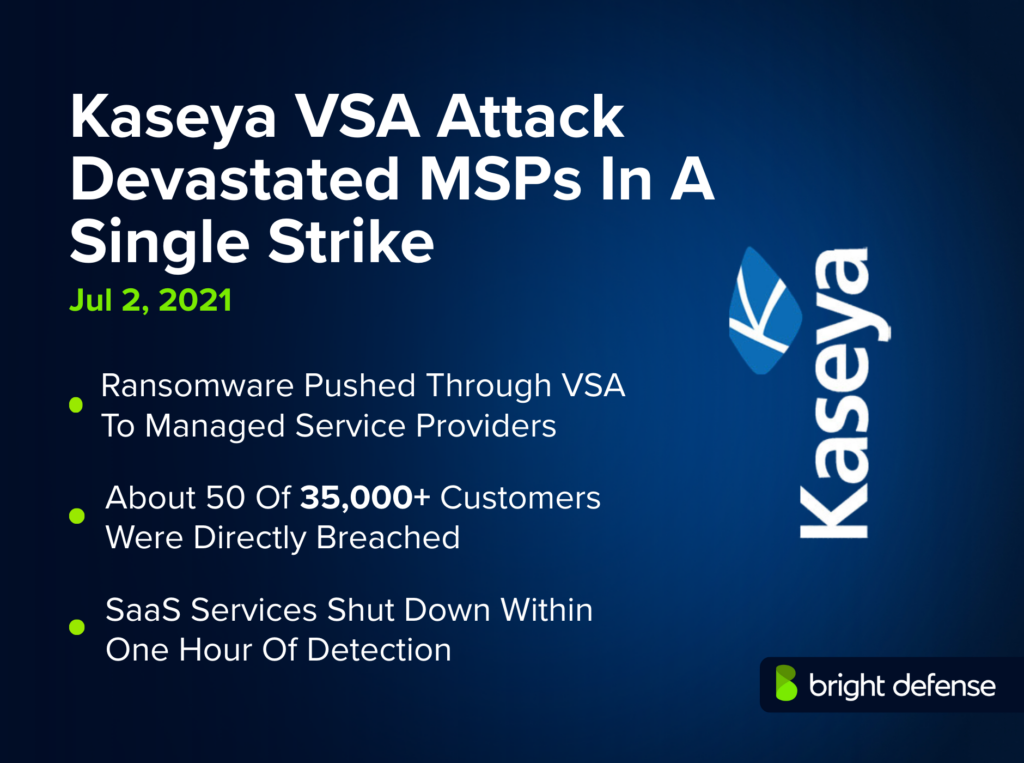
The Kaseya VSA supply chain ransomware attack was disclosed on 02 Jul, 2021, after Kaseya received reports of malicious activity affecting its on-premises VSA product and shut down SaaS services within about 1 hour. The attackers abused VSA to push ransomware through managed service providers, which turned a single compromise into downstream impact across many small and midsize businesses.
Kaseya later said about 50 of more than 35,000 customers were directly breached, though the indirect blast radius was much wider because MSP tools manage many client endpoints at once. The response timeline centered on shutdown, incident triage, law enforcement coordination, and staged restoration through early July 2021.
7. PrintNightmare Exposed Windows Print Weakness
Breach Disclosed: 06 Jul, 2021
PrintNightmare became a full public emergency on 06 Jul, 2021, when Microsoft issued CVE-2021-34527 guidance and released out-of-band security updates for a remote code execution flaw in the Windows Print Spooler service. The vulnerability drew intense attention because exploitation could let an attacker run code with SYSTEM-level privileges and potentially move from local access to full domain compromise in poorly protected environments.
Public proof-of-concept code and confusion around earlier CVE tracking accelerated the risk window and pushed many defenders into emergency mitigation mode. Microsoft’s action timeline moved from advisory to patches on 06 Jul and 07 Jul, 2021, followed by clarified hardening guidance as organizations worked through Point and Print exposure.
8. ProxyLogon Let Hackers Own Exchange Servers
Breach Disclosed: 02 Mar, 2021
ProxyLogon was publicly disclosed on 02 Mar, 2021, when Microsoft revealed active exploitation of a chain of 4 zero-day flaws affecting on-premises Exchange Server, including CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065. The exploit chain let attackers bypass authentication, write files, install web shells, and keep long-term access to email environments.
Microsoft linked the early campaign to HAFNIUM, then warned that additional actors were moving quickly against unpatched servers. The operational impact was severe because Exchange often held sensitive mail, credentials, and internal workflow data. Microsoft’s response began with emergency updates on 02 Mar, 2021, then expanded through March 2021 with mitigation tools, IOC guidance, and responder playbooks.
9. Zoom Flaw Exposed Windows Password Hashes
Breach Disclosed: 31 Mar, 2020
The Zoom UNC path injection issue became public on 31 Mar, 2020, when researchers showed that the Windows client would turn shared file paths sent in chat into clickable UNC links. That behavior could force Windows to send a victim’s NTLM credentials to an attacker-controlled SMB server, exposing password hashes and opening the door to follow-on abuse.
In some cases, attackers could pair the trick with user interaction to launch local programs through deceptive links. The incident landed during Zoom’s wider 2020 security crisis, which raised pressure for rapid fixes and safer defaults across the platform’s desktop client and collaboration features. Source: (BleepingComputer)
10. Stuxnet Exposed The First Digital Sabotage
Breach Disclosed: 15 Jul, 2010

Stuxnet became publicly known on 15 Jul, 2010, the closest widely verified disclosure date, though security firms had detected related activity in June 2010. The worm was far more than ordinary malware: it used multiple Windows zero-days, spread through USB media and network paths, then targeted Siemens Step 7 industrial control environments with code built to alter PLC behavior while masking the sabotage from operators.
That made Stuxnet a landmark cyber-physical attack rather than a standard data theft case. The action timeline moved from initial discovery in mid-2010 to rapid reverse engineering, emergency Microsoft patching, and global scrutiny of nation-state offensive cyber operations.
The BRICKSTORM Paradigm: Intellectual Property Theft Fueling Future Zero-Days
A 2025 malware campaign known as BRICKSTORM, attributed to PRC-nexus espionage operators, signals a new paradigm in zero-day exploitation. Rather than limiting operations to data theft from client environments, the threat actors targeted intellectual property from technology companies, potentially including source code and proprietary development documents.
This stolen IP could be used for vulnerability discovery in the vendor's own software, creating a self-reinforcing cycle: steal IP, find new flaws, develop new exploits, compromise more targets. The campaign poses a threat not only to the original victims but to their downstream customers and partners.
Vulnerabilities Exploited Before Patches: Mass Compromise Events
The window between zero-day disclosure and widespread exploitation is shrinking faster than most organizations can respond. Several recent events illustrate how quickly a single zero-day can scale into a mass compromise.
- The MOVEit Transfer breach affected over 2,500 organizations through a single SQL injection zero-day. (Multiple sources)
- Mandiant observed that the four most exploited vulnerabilities in 2024 were all in edge devices such as VPNs, firewalls, and routers. (Mandiant M-Trends 2025)
- Within two weeks of disclosure and proof-of-concept publication for CVE-2024-3400 (Palo Alto Networks PAN-OS), Mandiant observed more than a dozen separately tracked groups exploiting the vulnerability. (Mandiant M-Trends 2025)
- Eight distinct clusters, including five suspected Chinese espionage groups, exploited Ivanti Connect Secure vulnerabilities in early 2024. (Mandiant M-Trends 2025)
AI’s Growing Role in Zero-Day Threats
Artificial intelligence is becoming a major force in zero-day threats because it can speed up how attackers find vulnerabilities, build exploits, and scale their operations. Google GTIG warned in its 2025 report that AI will likely accelerate each stage of the zero-day exploitation cycle, from reconnaissance to exploit development.
VulnCheck reported more than 14,400 exploits tied to about 10,480 unique 2025 CVEs, marking a 16.5% year-over-year increase. A large share of that growth came from AI-generated proof-of-concept code, even though much of it did not work reliably. The same technology can still strengthen defense efforts.
Security teams can use AI to detect unusual behavior, rank remediation work, and automate parts of incident response. Organizations that adopt effective AI-driven detection early will be better positioned to spot and contain zero-day attacks before they spread.
Check out more stat based researched articles:
How Bright Defense Can Help With Zero-Day Defense
Bright Defense helps organizations stay ahead of zero-day threats through continuous cybersecurity compliance. Our monthly engagement model pairs CISSP and CISA-certified experts with a compliance automation platform to keep your security posture hardened across SOC 2, ISO 27001, HIPAA, and CMMC frameworks year-round.
We focus on what actually complements penetration testing for zero-day defense: continuous monitoring through SOC/SIEM, endpoint detection and response (EDR), and ongoing compliance programs that close gaps before attackers find them. You can learn more through our Penetration Testing Services, our guide on What Penetration Testing Is, and our overview of Penetration Testing Pricing.
Frequently Asked Questions (FAQ)
A zero-day is defined here as a vulnerability maliciously exploited before a patch is publicly available.
Google Threat Intelligence Group reported 90 zero-days in 2025, compared with 100 in 2023 and 78 in 2024, with totals staying within about 60 to 100 in recent years.
Enterprise technologies accounted for 43 zero-days, or 48%, which the report describes as close to half of all tracked 2025 zero-days.
End-user platforms and products accounted for 47 zero-days, or 52%, in 2025.
Operating systems accounted for 39 zero-days, or 44% of all tracked 2025 zero-days, up from 31 in 2024 and 33 in 2023.
Mobile-related zero-days were 15 in 2025 versus 9 in 2024 and 17 in 2023, with the report noting that some exploit chains used three or more vulnerabilities.
Security and networking vulnerabilities made up about half of enterprise zero-days at 21, and the report says 14 2025 zero-days affected edge devices.
Yes, Chrome release notes state Google is aware of in-the-wild exploitation for CVE-2026-3910 reported on 2026-03-10, and for CVE-2026-3909 also reported on 2026-03-10.
Rapid patch rollout matters most, and Chrome’s security update posts provide the exploit-in-the-wild notice and the fixed stable-channel release context used for version verification.
SecurityWeek reported the CISA KEV catalog reached 1,484 entries after 245 additions in 2025, which many teams use as an exploitation-driven patch priority list.
There is no single official “biggest” zero-day exploit, but Stuxnet is widely treated as the most consequential example because it used four zero-day exploits and sabotaged industrial control systems tied to Iran’s nuclear program.
A brief FAQ answer is that they usually begin with phishing, most often through a malicious email, link, or fake webpage. CISA says more than 90% of successful cyberattacks start with a phishing email, and Cloudflare repeats the same estimate.
Examples include Stuxnet, Microsoft Outlook CVE-2023-23397, Apple WebKit CVE-2023-32435, and Palo Alto PAN-OS CVE-2024-3400. These are well-known zero-day cases documented by major vendors, security researchers, or CISA.
The 1-10-60 rule means trying to detect a threat within 1 minute, investigate it within 10 minutes, and contain or remediate it within 60 minutes. CrowdStrike uses it as a speed benchmark for incident response.
Google Threat Intelligence Group tracked 90 zero-day vulnerabilities exploited in the wild in 2025. (Google GTIG)
Annual zero-day counts have stabilized in a 60 to 100 range since 2021, far above the pre-2021 baseline. The count was 63 in 2022, 100 in 2023, 78 in 2024, and 90 in 2025. (Google GTIG)
In 2025, Microsoft led with 25 zero-days, followed by Google (11), Apple (8), Cisco (4), and Fortinet (4). (Google GTIG)
Prices vary by target. A zero-click full chain exploit for an iPhone or Android device can command up to $9 million from brokers like Crowdfense. Browser exploits range from $3 million to $3.5 million. (Crowdfense)
Mandiant found that exploitation was the initial access vector in 33% of all 2024 intrusions, making it the number one vector for the fifth straight year. (Mandiant M-Trends 2025)
VulnCheck found that 28.96% of known exploited vulnerabilities in 2025 were exploited on or before the day the CVE was published. (VulnCheck)
IBM reported the global average data breach cost reached $4.88 million in 2024, a 10% increase over the prior year. (IBM)
Zero-day exploitation is increasing. The 2025 total of 90 represents a 15% jump from 2024, and Forescout measured a 46% increase in zero-day exploitation during just the first half of 2025. (Forescout)
23. Who is exploiting zero-days the most?
In 2025, commercial surveillance vendors were attributed the most zero-day exploitation (15 zero-days), surpassing state-sponsored espionage groups (12) for the first time. Among nation-states, China-linked groups led with 10 attributed zero-days. (Google GTIG)
24. What types of products are targeted most?
Operating systems are the most exploited category (39 zero-days in 2025), followed by security and networking products (21 enterprise zero-days). Edge devices like firewalls, VPNs, and routers are especially targeted because they provide privileged network access with minimal detection coverage. (Google GTIG)
25. Can AI help defend against zero-day attacks?
Yes. IBM found that organizations extensively using AI in security operations experienced average breach costs of $3.84 million, compared to $5.72 million for those without AI. (IBM) Google GTIG expects AI to play a growing role in both attack and defense in 2026.
26. How do zero-day vulnerabilities differ from n-day vulnerabilities?
A zero-day has no known patch at the time of exploitation. An n-day vulnerability has been publicly disclosed and patched, but remains exploitable on unpatched systems. On Android, long patching timelines mean n-day vulnerabilities often function like zero-days in practice. (Google Project Zero)
27. What is the role of the zero-day market in the threat landscape?
The zero-day market encompasses white-market bug bounty programs, gray-market brokers like Crowdfense and Zerodium who sell to government clients, and black-market forums where cybercriminals trade weaponized exploits. Rising exploit prices reflect increasing difficulty in compromising hardened platforms and sustained demand from intelligence agencies and financially motivated actors.
Get In Touch