Updated:
February 25, 2026
What is a SOC 3 Compliance Report?
A SOC 3 report is a public-facing audit report on a service organization’s controls.
It provides a summary of a service auditor’s opinion on how a company’s systems meet the five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy.
If you’re a potential customer, a business partner, or just curious about how companies protect your data, you’ve come to the right place.
In this blog, we’ll break down everything you need to know about SOC 3 reports: what they cover, who issues them, and why they’re such a big deal for both businesses and their clients.
What is a SOC 3 Report?
A SOC 3 report is a publicly shareable assurance report issued under the System and Organization Controls (SOC) framework created by the American Institute of Certified Public Accountants (AICPA). It is based on the same Trust Services Criteria as a SOC 2 report, which include security, availability, processing integrity, confidentiality, and privacy, but it is written for a general audience.
Unlike a SOC 2 report, which contains detailed descriptions of systems and auditor test results (and is restricted to customers, regulators, or partners under a non-disclosure agreement), a SOC 3 report provides only a high-level summary of the service auditor’s opinion. It avoids sensitive details and technical depth, making it safe to publish on a company’s website or share with anyone who wants reassurance about the company’s security posture.
In short:
- Purpose: Demonstrates that an independent auditor has validated the effectiveness of controls without disclosing confidential evidence.
- Audience: Customers, prospects, and the public.
- Use case: Marketing and trust building, showing that the organization takes security and compliance seriously.
Who Typically Needs a SOC 3
A SOC 3 report is not required for every organization, but it becomes valuable when a company wants to demonstrate trust and security processes to a broad, non-technical audience. Unlike a SOC 2 report, which is meant for customers and regulators under NDA, a SOC 3 is meant to be public.
Here are some of the potential areas where SOC 3 can be a requirement:
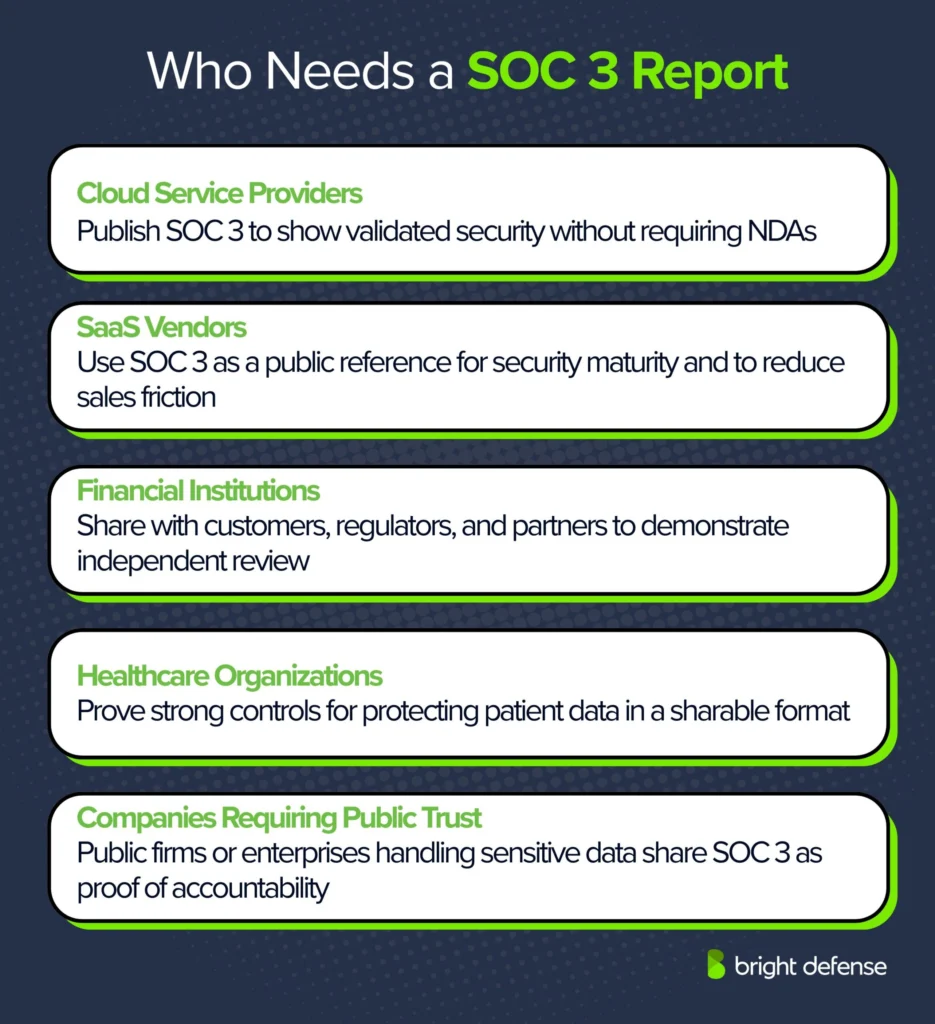
1. Cloud Service Providers
Companies that deliver cloud platforms or hosting services publish SOC 3 reports so prospects and prospective customers can review validated security protocols without signing a non disclosure agreement. This transparency helps them stand out in a competitive market and builds trust with businesses that may have strict vendor due diligence requirements.
2. SaaS Vendors
Software-as-a-Service providers use SOC 3 reports to give potential clients a public reference point for their organization’s commitment to security maturity. Since these reports can be accessed freely, they reduce friction in sales cycles and provide prospects with confidence before they commit to deeper evaluations such as SOC 2 reviews.
3. Financial Institutions
Banks, payment processors, and fintech organizations face heavy regulatory oversight. Publishing a SOC 3 gives them an accessible way to show customers, regulators, and partners that their systems have been reviewed independently against security and availability standards. This serves as a visible commitment to protecting sensitive financial data.
In fact, 41% of organizations now require vendors to show compliance with specific security frameworks even at the initial evaluation stage– having a SOC 3 ready can accelerate this vetting process. (MSSPAlert)
4. Healthcare Organizations
Hospitals, insurance companies, and health technology providers rely on SOC 3 reports to demonstrate that strong controls are in place for safeguarding patient records. The public format of the report makes it easy to share with patients, regulators, and business partners, supporting compliance obligations such as HIPAA.
5. Any Company With a Public Trust Requirement
Organizations outside finance and healthcare also benefit from SOC 3 reports if they need to reassure a wide audience about security practices. Public companies, firms with investor scrutiny, and enterprises handling sensitive transactions can share SOC 3 reports openly as proof of accountability. This makes them valuable tools for maintaining trust at scale.
Why do they need it
- To demonstrate accountability without exposing sensitive details.
- To increase customer confidence during sales and partnership discussions.
- To differentiate from competitors who may only provide private SOC 2 reports.
Why SOC 3 Compliance Is Important
A SOC 3 report provides external assurance that an organization’s risk management program based on the AICPA’s Trust Services Criteria (TSC) has been reviewed.
Unlike SOC 2, which contains detailed systems testing and control descriptions intended for auditors and security professionals, SOC 3 is written for a public audience.
It confirms that the organization’s systems have been examined by a qualified service auditor without revealing confidential information.
From a compliance and risk management perspective, SOC 3 plays a key role in bridging the gap between internal security controls assurance and public accountability.
Here are some of the key reasons that make it crucial:

1. Public Assurance Without Exposing Internal Details
SOC 2 reports, while essential for vendor assessments and regulatory oversight, contain information such as control design, testing procedures, and exceptions noted during the audit. Publishing these can unintentionally give threat actors insight into potential weaknesses.
SOC 3 addresses this by presenting the audit’s outcome in a summarized, high-level format. This approach allows organizations to demonstrate compliance with AT-C section 105 and 205 (standards from the AICPA), while keeping critical details restricted to trusted parties.
2. Demonstrates Alignment With Trust Service Principles
SOC 3 reports still map to the five Trust Services Criteria—security, availability, processing integrity, confidentiality, and privacy. These principles are grounded in the COSO framework and widely recognized across multiple industries.
Publicly presenting a SOC 3 provides assurance that the organization maintains systems designed to meet these criteria, which is particularly valuable for vendor risk management programs that reference NIST SP 800-53 or ISO/IEC 27001 as comparative benchmarks.
3. Builds Confidence Among Customers and Partners
From a buyer’s perspective, third-party validation provides peace of mind. Instead of just taking a vendor’s word for it, they have a CPA’s attestation. In fact, recent industry research revealed that 63% of enterprise buyers now require detailed security and compliance information before even engaging with a vendor.
This means having a SOC 3 available early can significantly reduce uncertainty for prospects. It’s an easily shareable trust signal that can reassure customers and partners that your systems are secure, even before NDAs are signed or deeper security reviews occur.
4. Supports Regulatory and Due Diligence Requirements
Many regulators and standards bodies, including the Office of the Comptroller of the Currency (OCC) in banking and HIPAA’s Security Rule in healthcare, require organizations to validate the company’s security posture of critical vendors.
SOC 3 reports provide a public-facing artifact that satisfies initial due diligence questions, especially in procurement processes, RFP submissions, or investor audits. While SOC 2 may be required for final validation, SOC 3 reduces friction by making the organization’s audit status immediately visible.
5. Strengthens Brand Reputation
Demonstrating trustworthiness can directly impact your brand’s value. Independent attestation reports like SOC 3 are one of the strongest signals of maturity in an organization’s governance, risk, and compliance (GRC) program.
Publishing a SOC 3 annually shows a commitment to ongoing independent oversight, not just internal policies. Public stakeholders notice this too. In fact, 79% of consumers say that protecting their personal data is very important to earning their trust in a company.
Sharing a SOC 3, a company visibly commits to security and privacy best practices, which can translate into higher customer and investor trust. (This aligns with guidance in frameworks like NIST CSF, which emphasize demonstrating a “Govern” function through external assurance.)
6. Provides a Competitive Edge in Crowded Markets
In industries like SaaS, cloud hosting, and fintech, many providers compete with nearly identical service features. Decision-makers often use security risks as the differentiating factor.
According to ISACA’s 2023 State of Cybersecurity report, 62 percent of enterprises rank third-party audit transparency as a deciding influence during vendor selection. A SOC 3 allows companies to stand out against competitors who cannot show the same external validation.
7. Communicates Assurance in Plain Language
SOC 2 is technical in nature, often spanning hundreds of pages of control tests and auditor opinions. SOC 3, in contrast, is designed for executives, investors, and the general public.
Its simplified narrative makes it suitable for corporate websites, investor relations pages, or annual reports. This aligns with the AICPA’s stated intent for SOC 3: to make assurance accessible beyond compliance specialists while maintaining a standards-based, CPA-verified foundation.
What Is The Difference Between Soc 2 And Soc 3?
While both SOC 2 and SOC 3 audits follow the AICPA’s Trust Services Criteria, they differ in scope, audience, and level of detail. SOC 2 provides the technical depth needed for auditors, regulators, and customers performing due diligence, while SOC 3 serves as a publicly accessible summary designed to demonstrate assurance without disclosing sensitive control information.
| Aspect | SOC 2 | SOC 3 |
|---|---|---|
| Purpose | Provides detailed assurance about controls for customers, partners, and regulators | Provides a high-level summary of controls for public distribution |
| Audience | Restricted to specific parties under NDA (e.g., auditors, customers, regulators) | General public, prospects, and anyone interested |
| Detail Level | In-depth descriptions of systems, controls, and test results | Auditor’s opinion and summary only, without confidential details |
| Format | Technical and compliance-focused, often 100+ pages | Concise report, usually just a few pages |
| Use Cases | Customer due diligence, regulatory reviews, vendor assessments | Marketing, public trust, website publication |
| Availability | Shared under NDA due to sensitive information | Freely shareable and often posted online |
| Type | Type I (design of controls at a point in time) and Type II (operating effectiveness over a period) | Always Type II (covers operating effectiveness over time) |
In short, SOC 2 proves the details, SOC 3 promotes the assurance. Organizations typically complete a SOC 2 audit first, then request a SOC 3 to share audit results more openly with prospects, investors, and the general public.
Components of a SOC 3 Report
A SOC 3 report provides a simplified version of a SOC 2 examination. It follows a consistent structure defined by the American Institute of Certified Public Accountants (AICPA) under the Trust Services Criteria (TSC), offering public assurance without exposing confidential data.
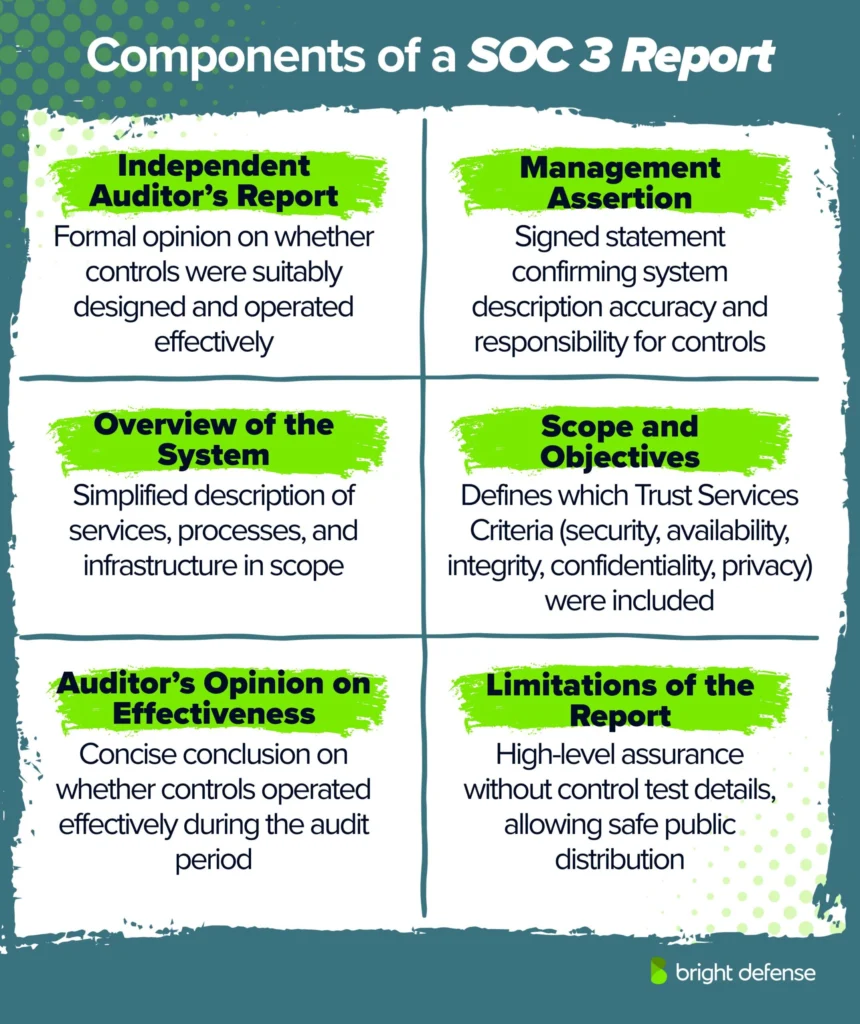
1. Independent Auditor’s Report
The opening section contains the auditor’s formal opinion, issued under ATC Section 205, Examination Engagements. This opinion addresses whether the organization’s control objectives were suitably designed and operated effectively to meet the selected TSC categories.
The opinion can be unqualified (clean), qualified (with exceptions noted), or adverse (significant deficiencies). This section is the foundation of trust within the final report.
2. Management Assertion
Management provides a signed statement confirming responsibility for the system description, scope, and control environment.
The assertion declares that the system description is accurate and that controls were designed and are operating effectively during the audit period. This accountability is critical because service organization’s management, not the auditor, defines the system boundaries and scope.
3. Overview of the System
The report includes a simplified description of the services, processes, and infrastructure in scope. Unlike SOC 2, this section does not contain sensitive details such as control testing or exception listings.
However, it must clearly define system boundaries such as applications, hosting environments, and data centers so that readers understand which parts of the organization were covered by the audit.
4. Scope and Objectives
This section specifies which of the five Trust Services Criteria, security, availability, processing integrity, confidentiality, and privacy, were evaluated. Organizations can select the principles most relevant to their services.
For example, a SaaS provider may include security and availability while omitting privacy if personal data is not processed. This flexibility makes SOC 3 reports adaptable to different industries and use cases.
5. Auditor’s Opinion on Effectiveness
In addition to the formal opinion at the beginning, the report includes a concise summary of the auditor’s conclusion on whether controls operated effectively during the specified period.
The clarity and brevity of this section make it suitable for audiences who are not compliance specialists but need assurance of effectiveness.
6. Limitations of the Report
SOC 3 reports are designed for general use. They do not include descriptions of control tests, results, or exceptions. Instead, they provide a high-level assurance that an independent CPA firm has performed the audit in line with AICPA standards.
The limitation is intentional because it allows organizations to share SOC 3 reports publicly without disclosing operational details that could aid an attacker or compromise confidentiality.
Is a SOC 3 Report Mandatory?
No, a SOC 3 report is not mandatory. It is an optional report that organizations choose to pursue when they want a public-facing summary of their SOC 2 audit.
Regulators, user auditors, or enterprise customers will typically request a SOC 2 report because it contains the detailed evidence they need for due diligence and regulatory compliance. SOC 3, on the other hand, exists mainly as a trust-building marketing tool for a wider audience.
When a SOC 3 is Pursued
- A company wants to publish security assurance publicly on its website or marketing materials.
- A business wants to shorten sales cycles by giving prospective customers an immediate, high-level validation of its security program.
- An organization in industries like SaaS, cloud services, finance, or healthcare wants to signal credibility to the public without disclosing sensitive details.
Key Takeaway
- SOC 2 may be required by customers or regulators.
- SOC 3 is voluntary and serves as an additional way to communicate compliance more broadly..
SOC 3 Audit Process
A SOC 3 report is derived from a SOC 2 audit. Organizations do not go through a separate SOC 3 engagement; instead, they undergo a SOC 2 audit first, and then request a SOC 3 summary report from the same auditor. The process usually follows these steps:
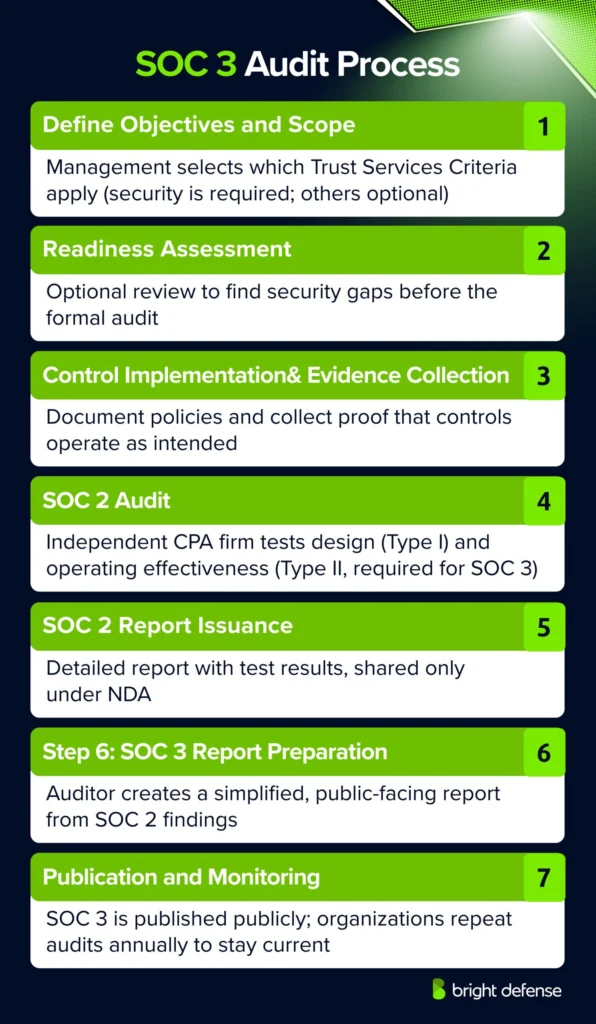
- Step 1: Define Objectives and Scope: Management determines which Trust Services Criteria will be covered (security is mandatory, while availability, processing integrity, confidentiality, and privacy are optional). These choices map directly to the organization’s service commitments and control objectives.
- Step 2: Readiness Assessment: Optional but recommended: Many organizations begin with a readiness review to identify gaps in their security processes before the formal audit. This step helps avoid delays or failures during the real examination.
- Step 3: Control Implementation and Evidence Collection: The organization documents processes, policies, and other internal controls, and collects evidence showing that these controls are in place and functioning.
- Step 4: SOC 2 Audit by Independent Auditor: A licensed CPA firm or accredited assessor evaluates the design (Type I) and operational effectiveness (Type II) of the controls. Since SOC 3 is always type ii reports, the auditor must test operating effectiveness over a defined period, typically 6 to 12 months.
- Step 5: Issuance of SOC 2 Report: The auditor prepares the detailed SOC 2 report, including test results and findings. This report is restricted to customers, regulators, and other stakeholders under NDA.
- Step 6: Preparation of SOC 3 Report: Using the SOC 2 findings, the auditor drafts a simplified, public-facing SOC 3 report. This includes the auditor’s opinion, management assertion, system overview, and scope, but excludes sensitive control details.
- Step 7: Publication and Ongoing Monitoring: The SOC 3 report can be published on the organization’s website or shared openly with prospects. To maintain credibility, the company must repeat the audit annually and update the report accordingly.
How Bright Defense Can Help You
At Bright Defense, we guide organizations through every stage of the SOC journey, from preparation to certification. Our approach is hands-on and practical, designed to take away the complexity that often surrounds SOC reporting.
We start with readiness assessments to pinpoint gaps in your current controls, then work with your team to build the policies and internal security controls that match the Trust Services Criteria.
When it comes time for the audit, we stand beside you. We help collect evidence, prepare your staff for what to expect, and coordinate directly with auditors to keep the process moving smoothly. After the SOC 2 audit is complete, we assist in securing and publishing a SOC 3 report that you can confidently share with prospective customers.
Our work does not end there. Compliance is an ongoing responsibility, and we provide continued support through monitoring, reviews, and performance monitoring so that your organization stays audit-ready year after year.
With Bright Defense, you gain more than an audit partner, you gain a long-term ally in building trust with customers, partners, and the wider public.
FAQs
A SOC 3 report is a general use report for service organizations that addresses controls relevant to the Trust Services Criteria and is meant for broad sharing with users who want assurance but do not need the full SOC 2 detail.
A SOC 3 report is a shorter, public-facing summary and does not provide the same level of detail as a SOC 2 report, while SOC 2 is the more detailed report used for deeper review.
A SOC 3 report uses the AICPA Trust Services Criteria, which cover security, availability, processing integrity, confidentiality, and privacy, based on the applicable criteria in scope.
Yes. SOC 3 reports are general use reports and can be freely distributed, which is one reason companies use them for broad customer and public trust communication.
No. SOC 3 reports give a higher level summary and not the same detailed testing information found in SOC 2 reports.
Yes, if you want a public report that many prospects can read without NDA handling. AWS, for example, states its SOC 3 report is publicly available, while SOC 1 and SOC 2 access requires an NDA.
No, not for most higher risk reviews. A SOC 3 report is useful for a quick public assurance check, but teams often need the fuller SOC 2 report when they need more detail for vendor risk assessment.
Start with the reporting period, the services or systems covered, the Trust Services Criteria in scope, and the auditor’s opinion, because those items tell you what was reviewed, when it was reviewed, and what assurance the report actually gives.
Yes, in a limited sense. SOC 3 is based on the same Trust Services Criteria topics as SOC 2, but it does not replace SOC 2 for vendor due diligence because SOC 2 includes much more detail on controls and testing results.
Get In Touch