Updated:
March 1, 2026
What is Red Team vs. Blue Team in Cybersecurity
Cyberattacks continue to affect businesses across every sector, with incidents growing more complex and expensive.
Estimates suggest that cybercrime losses may reach close to $10 trillion worldwide in 2025. This growing pressure has led many organizations to focus more on testing and strengthening their internal security teams.
One approach involves using red teams and blue teams. Red teams act as adversaries, simulating attacks to find weak points.
Blue teams take the defensive role, monitoring systems, detecting threats, and responding to breaches. Both teams play different parts but work toward the same goal: improving security.
Regular training helps security staff stay prepared. Instead of relying only on checklists or policy updates, teams often run red team vs. blue team exercises to test real-world readiness.
This blog covers how these teams operate, how they differ, and why both are important for maintaining strong security.
Key Takeaways
- Red teams simulate attacks to reveal weak points, while blue teams defend systems, detect threats, and respond to incidents.
- Red vs blue team exercises help organizations test actual defenses rather than relying on policies or assumptions.
- Offensive teams use tactics and tools like Metasploit or phishing, while defenders rely on detection systems and incident response protocols.
- When red and blue teams share insights, the combined effort leads to stronger defenses and faster response.
- Ongoing exercises allow teams to address emerging threats, spot recurring flaws, and support continuous improvement in cyber readiness.
What Is a Red Team?
A red team is a group of security professionals assigned to simulate real-world attacks against an organization’s systems, networks, and staff. Their role is to test how well defenses hold up under pressure and reveal areas that need improvement.
Red team members include ethical hackers, system specialists, and forensic analysts who carry out controlled attack simulations. These exercises often resemble actual threat scenarios, allowing organizations to see how they might respond in a real incident. The red team adopts the mindset of a threat actor to find technical flaws, human errors, and process gaps. Their work helps build a clearer understanding of where the organization is most exposed.
Each role on the red team serves a specific purpose:
- Penetration testers: Launch targeted attacks to find weaknesses in infrastructure and applications.
- Ethical hackers: Use offensive techniques responsibly to identify risk areas.
- Threat analysts: Examine trends in attacker behavior and design realistic test scenarios.
- Social engineers: Attempt to trick employees into revealing access or bypassing protections.
- Vulnerability analysts: Examine systems for unpatched issues or misconfigurations.
- Security auditors: Review security controls for gaps in implementation or adherence.
- Red team leaders: Oversee operations and coordinate full-scope assessments across different systems and teams.
What Is a Blue Team?
A blue team is a group of cybersecurity professionals responsible for protecting an organization’s systems and data. Their work focuses on prevention, detection, and response. One of the critical factors they monitor is breakout time. This refers to the period between an initial system compromise and the moment an attacker begins moving across the network. Reducing this window helps limit potential damage.

While red teams simulate attacks, blue teams build and maintain defensive capabilities. They monitor network activity, investigate suspicious behavior, contain incidents, and apply security measures that reduce exposure. Their role is continuous, with a strong focus on system hardening and fast response. In organizations where the yellow team supports tool integration or automation, they may assist the blue team by improving data flow and detection efficiency.
Common blue team roles include:
- Security analysts: Monitor systems and review logs to detect threats.
- Incident responders: Investigate breaches and contain attacks to restore normal operations.
- Threat hunters: Search for hidden threats that evade automated tools.
- System administrators: Enforce access controls and apply security patches.
- Vulnerability managers: Track known issues and coordinate timely remediation.
- Security engineers: Build and maintain defensive tools and configurations.
- Cybersecurity evaluators: Test existing protections to identify weak areas and verify how threats may impact the company’s network.
Key Differences Between Red and Blue Team
Red and blue teams serve opposite roles in security. One attacks, the other defends. The sections below break down their key differences across purpose, methods, and mindset.
| Aspect | Red Team | Blue Team |
| Primary Role | Offensive: Simulate attacks to identify vulnerabilities | Defensive: Protect systems and respond to threats |
| Objective | Identify security gaps through simulated attacks | Detect and mitigate real-world threats |
| Approach | Mimic real-world adversaries using various tactics | Monitor, detect, and respond to security incidents |
| Activities | Penetration testing, social engineering, exploit development | Threat detection, incident response, system hardening |
| Mindset | Think like an attacker to uncover weaknesses | Focus on protecting and securing critical assets |
| Tools & Techniques | Custom scripts, red team frameworks (e.g., Cobalt Strike, Metasploit) | SIEM, IDS/IPS, firewalls, endpoint monitoring tools |
| Outcome | Reveals security gaps and blind spots | Enhances detection and response capabilities |
| Visibility | Operates covertly to avoid detection | Maintains visibility across systems and logs |
| Reporting Focus | Documents methods of compromise and provides recommendations | Reports incidents, metrics, and long-term security improvements |
| Team Composition | Ethical hackers, penetration testers, threat analysts | Security analysts, incident responders, system administrators |
| Cost Implication | Higher due to specialized skills and offensive tools | Generally lower, focusing on defense and prevention |
| Collaboration | Provides insights to improve defensive strategies | Implements improvements based on red team findings |
1. Objective
The core difference in purpose lies in how each team views the system. One side looks for flaws while the other works to keep everything secure. Red teams are tasked with challenging existing defenses by simulating how a real attacker would gain unauthorized access.
Blue team members focus on protecting assets and maintaining business continuity. Both are critical, but their missions sit on opposite ends. One disrupts, the blue team defends.
2. Approach
Red teams take an offensive approach and actively try to break into systems using tactics modeled after real world adversaries. They might exploit vulnerabilities, craft phishing emails, or attempt to bypass access controls.
In contrast, defensive security professionals rely on strategies rooted in detection and containment. Their efforts go into prevention, monitoring, and response. They continuously assess whether the environment is secure and react when something suspicious happens.
3. Primary Activities
The red team spends most of its time on activities like penetration testing, vulnerability scanning, or conducting phishing campaigns. Their job is to simulate attack chains and evaluate how far they can go without being detected.
Meanwhile, the security personnel on the blue team focus on tasks like monitoring network logs, responding to alerts, and improving configurations. They may build detection rules or rehearse event management procedures to stay ready.
4. Mindset
Mindset plays a significant role in how each team operates. Red teams think like attackers. They try to find creative and unconventional ways to access protected environments, including exploiting human error or overlooked configurations.
Blue teams take the opposite perspective. Their mindset is centered around protection and focuses on how to limit exposure, anticipate risks, and reduce damage if something slips through, especially when dealing with new and emerging threats.
5. Tools and Techniques
There is a clear divide in the tools both teams use. Red teams often rely on offensive security tools like Metasploit or Cobalt Strike. They may write custom scripts to bypass mechanisms or mimic known threat actors.
On the other hand, blue teams use detection and analysis systems such as SIEM platforms, intrusion detection, and endpoint protection. Their setups include monitoring security software to stop anything that resembles a real attack on the internal network.
6. Outcome
When a red team finishes an engagement, they provide a detailed report of how they gained access, which defenses they bypassed, and where improvements are needed. Their work red teams identify weaknesses that need fixing.
Blue teams, in response, take these findings and implement fixes. They refine policies, reconfigure systems, and apply updated threat detection logic. Together, this process strengthens the organization’s defenses and improves the overall security posture.
7. Visibility
Red team operations are often stealthy by design. They try to stay hidden to truly test how well the organization can detect and respond under pressure.
The blue team, meanwhile, works toward maximum visibility. Their goal is to maintain a clear picture of what is happening in the environment at all times using logs and security tools to gain awareness of activity targeting the organization’s critical assets.
8. Reporting Focus
When it comes to reporting, red teams typically focus on detailing how attacks were executed, which paths were used, and what went undetected.
This helps shape cyber security priorities. Blue teams write reports that cover what was observed, how incidents were handled, and how the organization’s security posture can be improved. The feedback loop between the two teams leads to consistent advancement in defensive strength.
9. Team Composition
The structure of each team also differs. Red teams often include offensive security professionals like penetration testers, independent ethical hackers, and specialists in areas like social engineering or post exploitation.
Blue teams bring together analysts, responders, and engineers who manage detection systems and respond to cyber threats. Some may be cross trained to understand both perspectives in a red or blue team environment.
10. Cost Implication
From a cost perspective, red team exercises tend to be more expensive in the short term because they require specialized skills and careful scoping.
However, they are run periodically. Blue team functions are ongoing, which means the cost is spread out across daily operations and often involves more consistent investment in staff and infrastructure for organization’s security defense.
11. Collaboration
Although they serve different functions, the relationship between red and blue teams is not adversarial. In well run organizations, they collaborate.
Insights from offensive simulations guide defensive adjustments. At the same time, red teams learn what tactics are less useful as the blue side adapts. This ongoing cycle improves the cyber security strategy as a whole.
Benefits of Conducting Red and Blue Team Exercises
A 2021 report from the SANS Institute found that 14 percent of organizations took between one and six months to detect a breach. In many cases, attackers remain undetected long enough to move across networks, steal data, or disrupt operations. Security teams often face budget and staffing limitations that prevent them from identifying weaknesses early. Running structured red and blue team exercises creates a safe environment for testing, analysis, and improvement.
Here are the key advantages of conducting these exercises:
1. Finding Vulnerabilities
Red team exercises simulate how a real attacker might approach a target, which helps uncover flaws in systems, applications, and access controls. These flaws may include unpatched software, weak authentication mechanisms, poor segmentation, and overlooked misconfigurations. Many of these weaknesses are difficult to spot with automated scanners alone. Simulated adversary tactics give organizations a clearer picture of where defenses can fail under pressure.
This process also exposes process-level issues such as gaps in change management or excessive user privileges. Once vulnerabilities are identified, blue teams can validate the risks and prioritize remediation based on real-world impact.
2. Stronger Defenses
After reviewing red team actions, blue teams can make targeted improvements to their detection logic, alert thresholds, and system hardening practices. Red teams often reveal blind spots in monitoring tools and show which attacker behaviors go unnoticed. Blue teams use this information to improve their response strategies, deploy more effective alerts, and close visibility gaps.
These exercises may also reveal the need for better endpoint logging, stronger access controls, or faster patch cycles. As blue teams apply these changes, the overall environment becomes more resilient to attacks.
3. Improved Incident Response
Red and blue team simulations allow defenders to test how well their response plans function under stress. These tests highlight where processes break down, such as unclear ownership, delays in containment, or communication issues between departments. Practicing in a live setting gives responders a chance to sharpen their skills and build muscle memory, which helps them act faster during real events.
Repeated drills provide better insight into how long it takes to detect, respond to, and recover from various types of attacks. This leads to refined playbooks, more effective escalation paths, and stronger coordination across teams.
4. Promoting Collaboration
While red and blue teams focus on different objectives, these exercises create an opportunity for closer collaboration. When red teams explain how they breached defenses and blue teams share their detection process, both sides gain valuable insight.
This type of debriefing builds trust and helps eliminate friction between offensive and defensive teams. Shared understanding improves coordination and leads to more informed decisions about future defenses.
5. Strengthening Security Posture
These exercises help leadership gain a more accurate understanding of the organization’s real-world security readiness. Results from red team simulations highlight where controls break down under pressure, and blue team observations indicate where detection and response succeed or fail.
Ongoing testing allows teams to spot recurring weaknesses or slow detection paths. With that knowledge, decision-makers can set clearer priorities for tooling, staffing, and policy adjustments.
6. Raising Awareness and Training
Security depends on more than technology. These exercises can serve as an educational opportunity for non-technical staff as well. Phishing simulations or physical breach attempts help expose risky behaviors like weak passwords, careless access sharing, or poor badge security.
By involving other departments in post-exercise reviews, organizations can reinforce the importance of policies and protocols. Employees become more engaged in the security process and are more likely to report suspicious activity.
7. Continuous Improvement
Each red and blue team exercise creates a chance to measure progress and apply what was learned. Over time, teams move from reacting to specific threats to building processes that anticipate and resist a wider range of attacks.
Lessons from previous tests inform the next round of planning. This creates a structured feedback loop that helps improve controls, fine-tune alerting, and refine overall strategy.
8. Staying Current with Threat Intelligence
Red teams frequently incorporate tactics based on the latest threat reports. These methods may mirror ransomware deployment, supply chain compromise, or credential abuse. When these are tested in a safe setting, blue teams can assess whether existing defenses detect and contain those actions effectively.
This kind of hands-on exposure allows defenders to apply intelligence practically, adjust detection rules, and expand internal threat hunting efforts. Keeping up with how attackers operate helps security teams remain proactive rather than reactive.
What is a Purple Team?
A purple team brings red and blue teams together. Instead of working separately, they coordinate directly, sharing tactics, observations, and goals. The purpose is not to form a third unit but to tighten the feedback loop between offense and defense.
In a purple team setup, red teams show how attacks unfold while blue teams monitor and respond in real time. This back and forth leads to faster detection improvements, clearer fixes, and fewer blind spots. It turns testing into a focused effort to raise response speed, reduce risk, and strengthen overall security.
How Can Red and Blue Teams Collaborate?
Collaboration between red and blue teams strengthens the security posture of any organization. When both sides work together, they uncover weaknesses more effectively and apply targeted improvements. This model, often referred to as purple teaming, allows both offensive and defensive teams to coordinate their efforts and achieve results that isolated testing cannot produce.
Instead of viewing the two sides as working against each other, organizations can create a shared process where both contribute to detection, analysis, and response enhancements. Red teams reveal attack paths and bypass methods. Blue teams review those paths and apply defensive updates, all within the same engagement cycle.
To support this collaboration, teams can follow these practices:
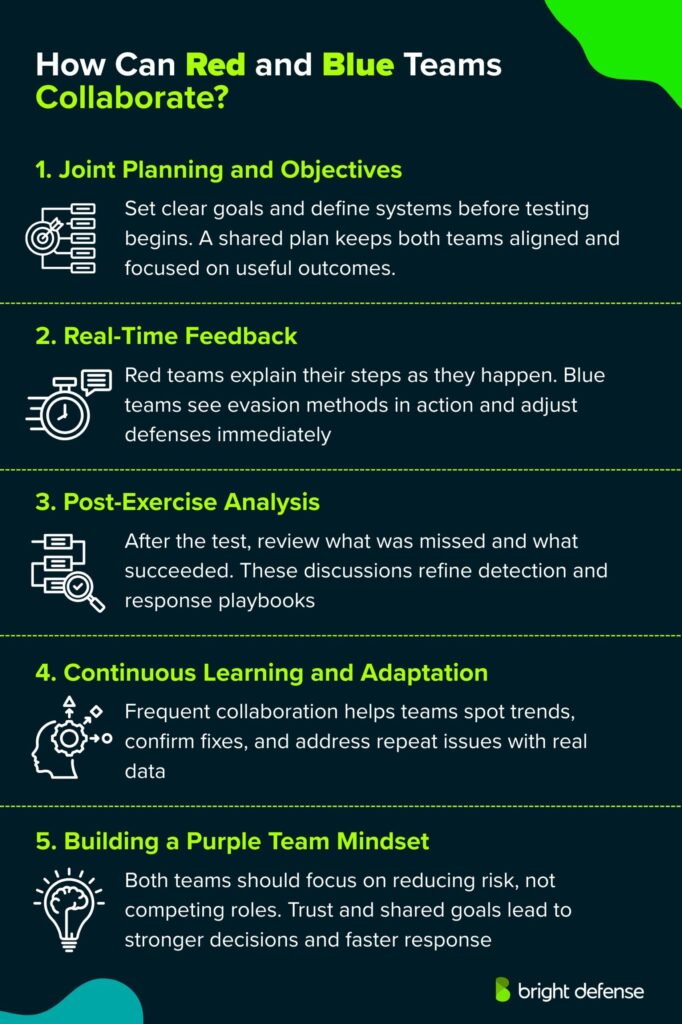
1. Joint Planning and Objectives
Before launching any exercise, red and blue teams should define clear goals and identify the systems involved. Shared planning gives both sides a common direction and ensures that test results align with operational priorities. When objectives are aligned from the start, exercises stay focused and produce more relevant insights.
2. Real-Time Feedback
During engagements, red teams can explain their actions while the test unfolds. Blue teams gain visibility into the methods used to avoid detection or trigger alerts. This immediate exchange helps defenders understand what their tools are missing and allows for fast adjustments during the same session. Real-time feedback supports quicker adaptation and sharper detection logic.
3. Post-Exercise Analysis
After the simulation ends, teams should meet to review each phase of the test. Discussions can cover gaps in detection, missed alerts, and areas where defensive actions fell short. This type of debriefing brings valuable insights that improve response playbooks and detection coverage. Reviewing actual attack sequences helps shape future priorities for security operations.
4. Continuous Learning and Adaptation
Maintaining consistent collaboration helps teams stay sharp and improve over time. Regular testing cycles reveal progress, expose recurring blind spots, and confirm whether previous fixes are still effective. This approach replaces guesswork with measured improvements that follow a clear track record.
5. Building a Purple Team Mindset
Strong collaboration starts with a shared mindset. Red and blue teams should operate with mutual trust and a joint focus on reducing risk. When both sides prioritize outcomes instead of competing roles, their combined efforts create stronger visibility, faster containment, and more informed security decisions. Encouraging this mindset across the team leads to better cooperation, clearer roles, and long-term security gains.
Frequently Asked Questions
A Red Team is a group authorized to emulate a potential adversary’s attack capabilities against an organization’s security posture so defenders can see real attack impact in operational conditions.
A Blue Team is a group that evaluates operational network security, finds threats and risks in the environment, and works with the customer on mitigation techniques and readiness.
A Red Team vs. Blue Team approach pairs offensive emulation with defensive operations so the organization can observe which defenses work and which gaps matter under realistic attack conditions.
A White Team referees the exercise, enforces rules, handles requests for information, and prevents testing from causing operational problems for the defender’s mission.
A penetration test is a planned technical security test with defined phases such as planning, discovery, attack, and reporting, while Red Teaming is typically objective-driven adversary emulation focused on showing real-world attack impact and defensive performance.
MITRE ATT&CK provides a shared language that Red Teams use for adversary emulation planning and that Blue Teams use to map detections and validate coverage against known techniques.
Your team should set scope, objectives, rules of engagement, logging expectations, and reporting requirements because NIST guidance treats the assessment plan and rules of engagement as core planning artifacts.
You should verify payment and purchase requests with a known secondary channel such as a phone call, and you should separately confirm any change in account number or payment procedures with the requester.
A SOC is aligned with the blue team because it centralizes defensive work such as continuous threat detection and response operations.
Get In Touch