Updated:
May 7, 2026
List Of Recent Compliance News in 2026
Cybersecurity compliance continues to evolve in 2026 as regulators introduce stricter security requirements, faster incident reporting rules, and tougher enforcement actions. Businesses across every industry are adapting to new privacy laws, AI governance standards, and growing third-party risk expectations.
This blog covers the latest compliance news in 2026, including major regulatory updates, enforcement trends, and the cybersecurity requirements shaping modern compliance programs.
Let’s begin!
Key Compliance News From April 2026
1. OCR Slaps 4 Firms With $1.165M In Fines
Date: 23 Apr, 2026
HHS OCR announced $1.165 million in HIPAA ransomware settlements on 23 Apr, 2026, turning four breach investigations into a clear compliance warning for healthcare providers, plans, and business associates. The cases involved Regional Women’s Health Group, Assured Imaging, Consociate Health, and Star Group’s health plan, with ransomware incidents affecting more than 427,000 individuals. OCR tied the penalties to Security Rule failures, especially missing or weak risk analysis, impermissible PHI disclosure, delayed breach notice, and inadequate ePHI safeguards. Each organization accepted a two-year corrective action plan, which means the real cost goes beyond the penalty and into monitored compliance repair.
Bright Defense can help healthcare organizations validate HIPAA controls and test ransomware exposure before OCR investigations turn security gaps into costly compliance findings.
Source: HHS OCR.
2. CMMC Phase 2 Locks In C3PAO Certs
Date: 10 Nov, 2026

CMMC Phase 2 turns third-party certification into a contract eligibility issue for many DoD contractors starting 10 Nov, 2026. Under 32 CFR Part 170, Phase 2 begins one calendar year after Phase 1 and allows DoD to require Level 2 C3PAO status for applicable solicitations and contracts as a condition of award. Contractors handling FCI or CUI cannot treat self-assessment as the safe default anymore, because Level 2 C3PAO certification, SPRS entries, annual affirmation, evidence retention, and POA&M closeout now affect bid readiness. Conditional Level 2 status can expire after 180 days, which makes early assessment planning critical.
Bright Defense can help DoD contractors prepare for CMMC Level 2 readiness through cybersecurity compliance support and penetration testing before C3PAO findings delay contract awards.
Source: eCFR
3. Self-Funded Plan Pays $245K After Ransomware
Date: 23 Apr, 2026

Star Group, L.P. Health Benefits Plan agreed to pay $245,000 after HHS OCR investigated a ransomware incident affecting 9,316 individuals. The self-funded employee benefits plan reported the breach on 22 Oct, 2021, after an unauthorized actor deployed ransomware against its information system and exposed names, addresses, dates of birth, SSNs, and health insurance information. OCR said the plan impermissibly disclosed PHI and failed to complete an accurate, thorough risk analysis for ePHI confidentiality, integrity, and availability. The settlement includes a corrective action plan, making this a direct warning that employer-sponsored health plans face HIPAA Security Rule enforcement, not just hospitals and clinics.
Bright Defense can help self-funded health plans test ransomware exposure and close HIPAA Security Rule gaps before OCR review turns missing risk analysis into a costly settlement.
Source: HHS OCR
4. CISA Adds 7 KEV Entries Hitting Microsoft And Adobe
Date: 13 Apr, 2026
CISA added seven vulnerabilities to KEV on 13 Apr, 2026, making them required remediation priorities for federal civilian agencies under BOD 22-01 and a practical patch benchmark for private sector compliance teams. The batch includedfour Microsoft flaws, CVE-2012-1854, CVE-2023-21529, CVE-2023-36424, and CVE-2025-60710, plus two Adobe Acrobat or Reader flaws, CVE-2020-9715 and CVE-2026-34621, with one Fortinet flaw in the same action. CISA said each entry had evidence of active exploitation, and FCEB agencies received a 27 Apr, 2026 deadline for the Microsoft and Adobe items. The compliance takeaway is simple: KEV entries should control patch SLAs, exception tracking, and audit evidence. (CISA)
Bright Defense can help organizations validate KEV exposure and test Microsoft, Adobe, and document-processing attack paths before known exploited CVEs become audit failures or breach entry points.
Source: CISA
5. SEC Cyber Disclosures Pass 2025 Pace
Date: 06 May, 2026
SEC cyber disclosures are tracking above the 2025 pace as public companies continue using Form 8-K to report material and voluntary cybersecurity incidents through EDGAR. The compliance issue is not just filing volume; it is whether disclosure committees can prove when materiality was evaluated, what facts were known, and why the company chose Item 1.05 or another Form 8-K item. The SEC rule requires material cyber incidents to be disclosed within four business days after materiality is determined, which puts pressure on legal, finance, security, and board reporting workflows. For public companies, the control evidence now matters as much as the incident narrative.
Bright Defense can help public companies test incident response, disclosure readiness, and cyber controls before SEC reporting timelines expose gaps in governance and evidence.
Source: SEC EDGAR
Key Compliance News From March 2026
1. MMG Fusion Pays $10K Over 15M PHI Leak
Date: 05 Mar, 2026

HHS OCR announced on 05 Mar, 2026 that MMG Fusion, LLC agreed to pay $10,000 to settle a HIPAA investigation tied to an unreported cyber incident affecting about 15 million individuals. OCR opened the case inMarch 2023 after a complaint reported PHI on the dark web. Investigators found that an unauthorized actor infiltrated MMG’s systems in December 2020, exposing names, phone numbers, mailing addresses, emails, birth dates, and appointment dates. OCR tied the case to impermissible PHI disclosure, failure to conduct an accurate risk analysis, and failure to notify covered entities. MMG entered a three-year corrective action plan.
Bright Defense can help healthcare business associates test HIPAA safeguards and breach notification readiness before dark web exposure becomes an OCR enforcement case.
Source: HHS OCR
2. Delve Whistleblower Alleges 493 Fake SOC 2 Reports
Date: 31 Mar, 2026
A whistleblower writing as DeepDelver alleged that Delve generated fabricated SOC 2 and ISO 27001 evidence, turning fast compliance automation into a vendor risk warning for companies that relied on those reports. IANS reported that textual analysis found nearly identical boilerplate in 493 of 494 SOC 2 reports, including repeated grammatical errors, while all 259 SOC 2 Type II reports allegedly carried identical auditor conclusions. Delve denied the claims, saying it does not issue compliance reports and that independent auditors provide final opinions. The compliance takeaway is direct: SOC 2 buyers must verify auditor independence, report scope, test evidence, and control operation before treating any attestation as trust proof. (IANS)
Bright Defense can help SaaS companies and buyers validate SOC 2 evidence, audit readiness, and vendor security claims before weak attestations create contract, privacy, or regulatory exposure.
Source: IANS.
Key Compliance News From February 2026
1. Top of the World Ranch Pays $103K Over 1,980 Records
Date: 19 Feb, 2026
HHS OCR announced on 19 Feb, 2026 that Top of the World Ranch Treatment Center agreed to pay $103,000 after a March 2023phishing breach exposed ePHI for 1,980 patients. OCR said the Illinois substance use disorder treatment provider filed the breach report after an unauthorized third party accessed data through a workforce member’s email account. The agency found that the provider failed to conduct an accurate and thorough HIPAA Security Rule risk analysis for ePHI confidentiality, integrity, and availability. The settlement became OCR’s 11th Risk Analysis Initiative enforcement action and requires a two-year corrective action plan covering risk analysis, risk management, policies, procedures, and workforce training.
Bright Defense can help healthcare providers test phishing exposure and HIPAA risk analysis gaps before one compromised mailbox turns into OCR enforcement.
Source: HHS OCR
2. FTC Sends 2nd Ransomware Report To Congress
Date: 06 Feb, 2026
The FTC issued its second ransomware report to Congress on 06 Feb, 2026, updating lawmakers on its work against ransomware and other cyberattacks under the RANSOMWARE Act. The report frames ransomware as a consumer protection and data security issue, not just an incident response problem. The FTC highlighted its data security enforcement program, public and business education, action against tech support scam actors, and international cyber coordination tied to China, Russia, North Korea, and Iran. The agency said it has brought more than 90 data security enforcement actions with favorable outcomes, including matters involving GoDaddy and Illuminate Education.
Bright Defense can help organizations test ransomware readiness and data security controls before FTC scrutiny turns weak safeguards into a compliance and consumer protection issue.
Source: FTC
Key Compliance News From January 2026
1. California DROP Opens For Data Broker Deletion
Date: 01 Jan, 2026
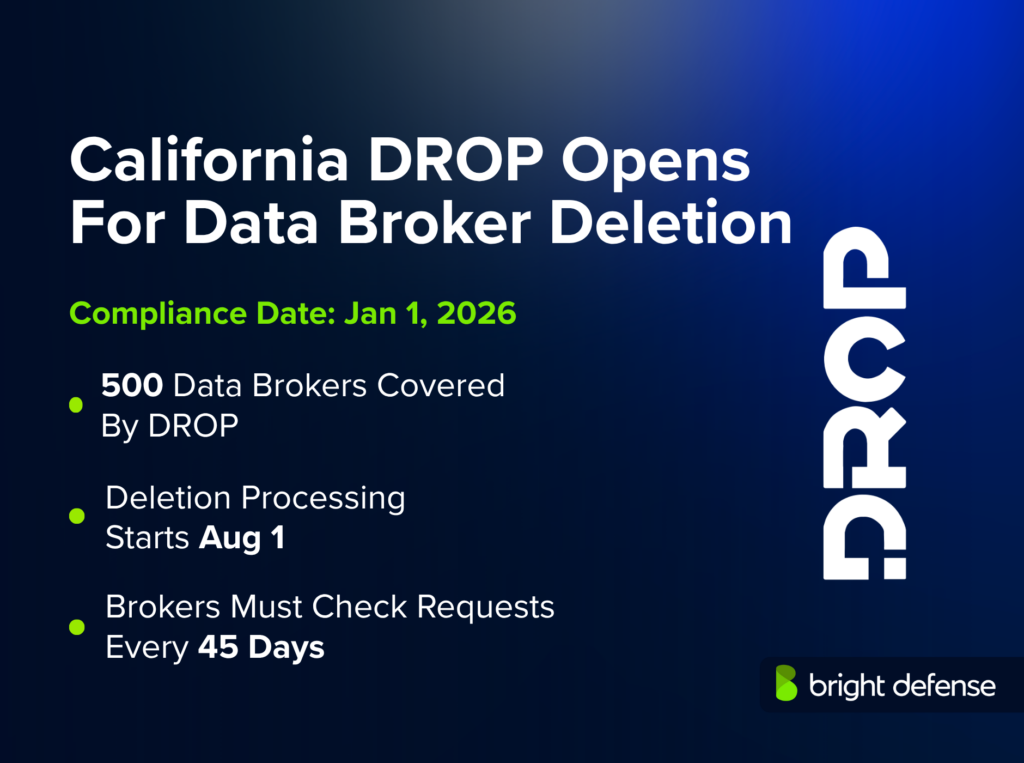
California’s DROP platform went live on 01 Jan, 2026, giving residents one state-run channel to request deletion and opt-out from more than 500 registered data brokers. The California Privacy Protection Agency says consumers verify California residency, create a profile, and submit a single DROP request instead of contacting brokers one at a time. The compliance clock now shifts to data brokers: processing starts on 01 Aug, 2026, requests must be checked every 45 days, and matching personal data must be deleted within 90 days unless a legal exemption applies. This turns deletion intake, identity matching, vendor coordination, and status reporting into auditable privacy obligations.
Bright Defense can help privacy-regulated businesses test deletion workflows, vendor data flows, and security controls before consumer privacy requests expose operational compliance gaps.
Source: California Privacy Protection Agency
2. Indiana Privacy Law Hits 100K Threshold
Date: 01 Jan, 2026

Indiana’s Consumer Data Protection Act took effect on 01 Jan, 2026, adding another state privacy law for companies that collect or use resident data. The law applies to businesses operating in Indiana or targeting Indiana residents that control or process personal data of at least 100,000 Indiana consumers in a calendar year. A second trigger covers businesses processing data of at least 25,000 Indiana consumers and earning more than 50% of gross revenue from selling personal data. The compliance takeaway is direct: privacy notices, consent for sensitive data, consumer rights workflows, processor contracts, and data protection assessments now need Indiana coverage.
Bright Defense can help organizations test privacy, security, and vendor controls before new state privacy thresholds turn data handling gaps into regulatory exposure.
Source: Indiana General Assembly
Key Compliance News From December 2025
1. FTC Locks Illuminate Into 10-Year Order
Date: 01 Dec, 2025
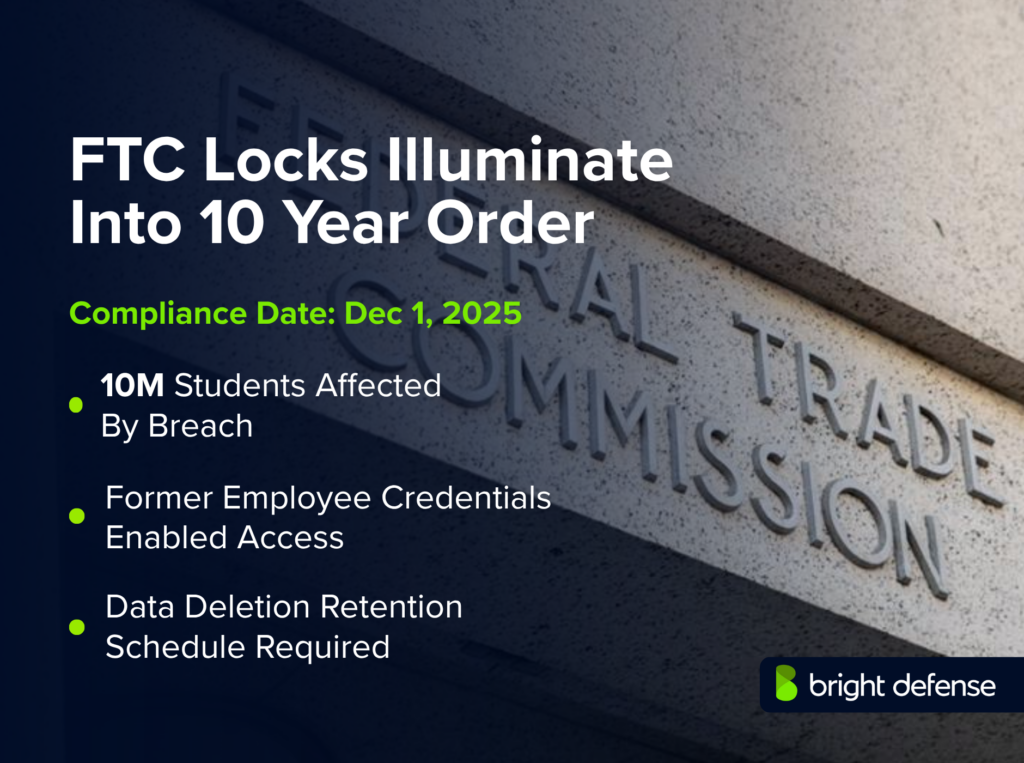
The FTC announced on 01 Dec, 2025 that Illuminate Education would be required to implement a security program and delete unnecessary student data after a breach exposed personal data for more than 10 million students. The FTC alleged that a hacker used credentials from a former employee who had left three and a half years earlier to access cloud databases in late December 2021. Exposed data included addresses, birth dates, student records, and health-related information. The proposed order bars misleading security claims, requires data deletion, mandates a written retention schedule, and forces breach reporting to the FTC. The compliance lesson is clear: edtech vendors must treat student data retention, access controls, and offboarding as board-level security evidence.
Bright Defense can help education vendors test cloud access controls and data retention practices before weak safeguards turn student records into FTC enforcement exposure.
Source: FTC
2. FTC Hits Nomad With 10-Year Order After $186M Heist
Date: 16 Dec, 2025

The FTC announced on16 Dec, 2025 that Illusory Systems, doing business as Nomad, would face a proposed 10-year order after hackers exploited weak software development practices and stole $186 million from consumers. The agency alleged Nomad marketed itself as “security-first,” yet pushed inadequately tested code in June 2022 that introduced a major token bridge flaw exploited just over a month later. Consumers still lost abou t$100 million after partial recovery. The proposed order requires a written security program, third-party assessments, truthful security claims, annual certification, and return of recovered assets. The compliance message is clear: security claims, code review, incident response, and loss controls must match actual engineering evidence.
Bright Defense can help fintech and Web3 companies test software security controls and compliance evidence before one code defect becomes an enforcement action.
Source: FTC
Get In Touch