What is a POAM?
A Plan of Actions and Milestones, or POAM, can help small and medium-sized businesses make cybersecurity compliance more manageable. A POAM shows where an organization stands, what gaps still exist, and what actions need to happen next to address those issues. It works as a practical roadmap for tracking, prioritizing, and fixing security weaknesses across information systems. This article explains the role of POAMs in cybersecurity and compliance programs.
Key Takeaways
- POAM simplifies compliance for small and medium businesses and aligns security efforts with frameworks like SOC 2, ISO 27001, CMMC, HIPAA, and PCI DSS.
- Prioritizing security risks with a POAM reduces breach likelihood by 60% and ensures vulnerabilities receive timely mitigation.
- Accountability improves compliance efficiency by 40%, as POAMs assign clear responsibilities for risk management.
- A 90+ day delay in mitigation increases breach risk by 35%, emphasizing the need for prompt action.
- Automation tools (e.g., Drata, JumpCloud) improve compliance tracking and provide real-time monitoring of security postures.
- POAMs are mandatory for government contractors, especially those handling Controlled Unclassified Information (CUI).
- Regular updates (quarterly or as needed) keep cybersecurity measures effective and responsive to evolving threats.
- Security training cuts human error breaches by 50%, reinforcing employee awareness as a critical cybersecurity component.
- Beyond compliance, POAMs build customer trust, protect against financial losses, and make audits more efficient.
Let’s get started!
POAM Overview
A Plan of Actions and Milestones (POAM) is crucial for any organization looking to enhance its cybersecurity compliance posture. Businesses use a systematically structured POAM to guide them through the necessary steps for securing their systems.
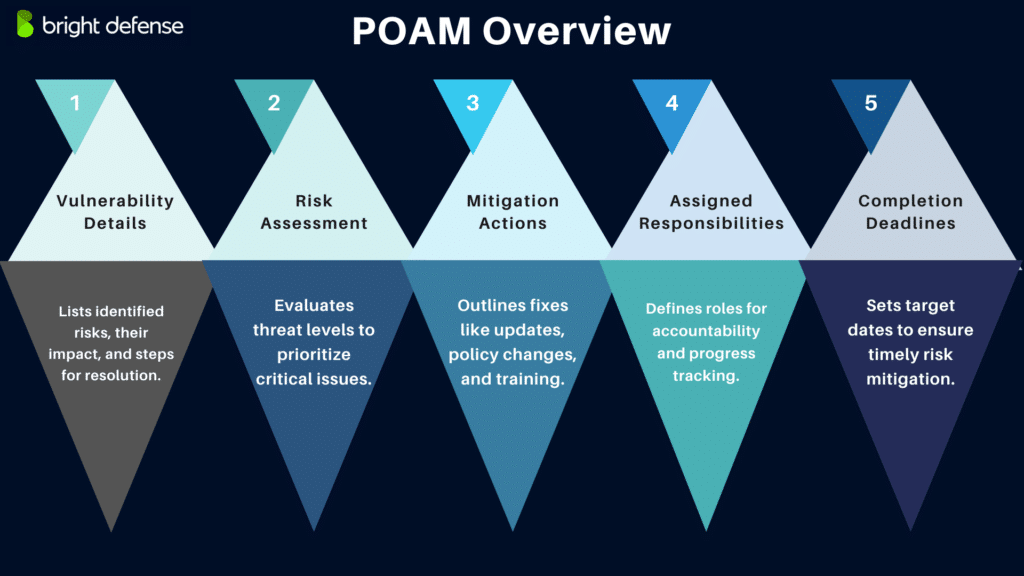
The key components of a POAM include:
- Description of Vulnerabilities: Each POAM begins with a clear description of the vulnerabilities that have been found. This section explains how each issue was identified, the possible effect on operations, and the details needed to support remediation. It also lists the tasks required to address each vulnerability, along with needed resources, milestones, and expected completion dates.
- Risk Assessment Results: This section reviews the risk tied to each identified vulnerability by examining the likelihood and possible impact of a security incident. These findings help organizations rank issues in the right order so teams can focus first on the most serious threats.
- Proposed Mitigation Actions: For each identified risk, the POAM lists specific remediation steps, such as software updates, configuration changes, policy revisions, or staff security training. These actions should match the nature and severity of the vulnerability.
- Assignment of Responsibilities: This part states which team members, departments, or system owners are responsible for each action item. Clear ownership supports accountability and makes progress easier to track.
- Target Dates for Completion: The POAM sets practical completion dates for each action based on the urgency of the issue. These deadlines help reduce exposure time and support timely remediation.

The Strategic Importance of a POAM in Cybersecurity Compliance
A POAM is instrumental in maintaining compliance with various regulatory frameworks and enhancing overall business operations. Some of the advantages include:
- Enhanced Communication and Coordination: A POAM supports clear communication and coordination among everyone involved in the compliance process. This includes internal teams, leadership, and external auditors. A well-maintained POAM keeps stakeholders informed about the status of security measures and helps each party understand its role in remediation. Clear communication also reduces duplicated effort and limits gaps in security coverage, which makes compliance work more organized and effective.
- Link to Broader Business Objectives: A POAM also supports broader business goals beyond compliance. These goals can include building customer trust, protecting brand reputation, and reducing the chance of financial loss after a security incident. When organizations address vulnerabilities methodically and document remediation efforts clearly, they show that security is an active business priority. That record can support long-term stability and growth.
- Adaptability and Continuous Improvement: Cybersecurity threats change over time, so a POAM should be updated regularly and remain flexible enough to reflect new vulnerabilities, shifting risks, or revised compliance requirements. This ongoing process helps organizations maintain stronger defenses and keep pace with changing standards.
Additionally, a POAM is important for meeting the compliance requirements of government agencies. This is especially true for contractors and subcontractors that work with the Department of Defense.
POAM Checklist
Below is a step-by-step guide for implementing your POAM, including recommended tools and best practices:
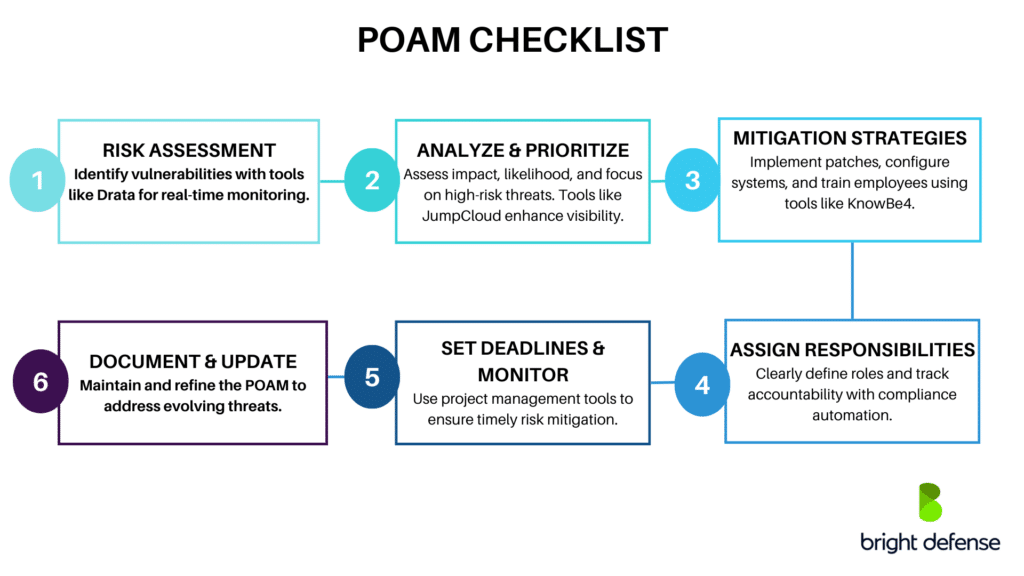
Step 1: Conduct a Thorough Risk Assessment
Begin with an initial assessment to find potential vulnerabilities across your systems. If you need help with the risk assessment process, Bright Defense’s vCISO services can provide guidance and support.
It is also worth considering compliance automation tools. Platforms such as Drata can continuously monitor your environment and collect relevant evidence, giving you current information for risk evaluation and remediation tracking. This can be especially useful for businesses working to maintain compliance with standards such as SOC 2, ISO 27001, or HIPAA.
Step 2: Analyze and Prioritize Risks
After identifying vulnerabilities, assess each one based on its potential impact and the likelihood of exploitation. These weaknesses may be uncovered through internal vulnerability assessments, external assessments, or active security incidents. It is important to document how each vulnerability was found and detected. After that, prioritize the vulnerabilities based on risk, with the highest-risk issues addressed first.
Tools like JumpCloud can support this process. JumpCloud gives organizations visibility into user activity and device security posture, which can help teams rank vulnerabilities based on potential business impact.
Step 3: Develop Mitigation Strategies
For each prioritized vulnerability, develop clear and practical mitigation strategies. This may include applying software patches, changing system configurations, or improving employee training programs. Use findings from your risk assessments to shape each strategy so the planned action directly addresses the specific vulnerability.
Employee training can also play an important role in remediation. Platforms like KnowBe4 support security awareness training that helps employees recognize common cyber threats and respond more appropriately in day-to-day work.
Step 4: Assign Responsibilities
Clearly assign responsibility for each mitigation action to a specific team member, department, or system owner. Each person involved should understand what they are responsible for and why their role matters in the broader cybersecurity effort. Compliance automation tools can also help track these assignments, document progress, and create a clear record of accountability.
Step 5: Set Deadlines and Monitor Progress
Set realistic deadlines for each action item based on its priority and level of risk. Use project management tools or built-in features within your risk and compliance platforms to track progress against those deadlines and keep remediation work on schedule. Regular check-ins and status updates also help teams adjust timelines, address delays, and keep the POAM current as conditions change.
Step 6: Document and Update the POAM Regularly
Maintain a detailed record of all actions taken and their outcomes. Update the POAM regularly so it reflects new information, completed tasks, newly identified vulnerabilities, and changing threats. The POAM should also document the resources required for each action so every remediation step is clearly defined. Regular security assessments can support these updates by revealing new issues and helping teams reprioritize tasks when needed. As a living document, the POAM should remain a central part of your cybersecurity strategy and support ongoing improvement over time.
Tips on Prioritizing Actions Based on Risk Assessment:
- Focus on Impact and Probability: Allocate resources first to the risks that are most likely to occur or would cause the most serious harm if exploited.
- Consider Business Impact: Prioritize mitigation actions that protect your most critical business functions, systems, and sensitive data.
- Regulatory Requirements: Address compliance-related vulnerabilities promptly so you can reduce exposure to penalties, failed audits, or contractual issues.

How To Ensure Compliance with a POAM?
Ensuring compliance with a POAM requires consistent execution, regular review, and clear accountability across the organization.
- Strict Adherence to Timelines: Follow the assigned timelines for each task closely. Delays can leave known vulnerabilities open longer than necessary and increase organizational risk. Timely remediation helps reduce exposure and keeps the POAM on track.
- Regular Audits and Reviews: Conduct regular audits and internal reviews to confirm that planned actions are completed and working as intended. These reviews should also check that the POAM remains accurate, complete, and current.
- Training and Awareness: Train all relevant personnel on their responsibilities within the POAM and the importance of sound security practices. Ongoing awareness helps teams respond more effectively to security issues and maintain steady progress.
- Resource Allocation: Assign enough staff, time, and technology to support POAM execution. Limited resources often slow remediation efforts and make compliance harder to maintain.
- Management Involvement: Active management support is important for keeping the POAM a real operational priority. Leadership attention helps secure resources, remove blockers, and reinforce accountability across teams.
How to Write a POA&M (Plan of Action & Milestones)
A Plan of Action & Milestones, or POA&M, is a structured document used to track and manage security weaknesses, compliance gaps, or operational risks within an organization. It explains the issue, the steps needed for remediation, the people responsible, and the timeline for completion. POA&Ms are commonly used in cybersecurity, government compliance, and risk management programs.
Step 1: Identify the Weakness or Issue
Start by clearly stating the security weakness or compliance gap. This entry should include a short description of the issue, such as missing security patches, outdated software, or policy non-compliance. It should also note how the issue was identified, whether through an audit, penetration test, vulnerability scan, or another review process. Finally, assign a risk level, such as high, medium, or low, so the issue can be prioritized appropriately.
Step 2: Assign Responsibility
Identify the person, team, or system owner responsible for addressing the issue. Clear ownership supports accountability, reduces confusion, and helps keep remediation efforts moving on schedule.
Step 3: Define Corrective Actions
List the specific steps required to fix the issue. Keep each action clear, specific, and easy to follow. For example, this may include updating system software to the latest version, implementing multi-factor authentication, or revising a company security policy to reflect current compliance requirements.
Step 4: Set Milestones and Deadlines
Break each corrective action into clear milestones with target dates. This makes progress easier to track and helps teams complete remediation work in an organized way. For example, one milestone may be installing security updates by a set date, followed by a later milestone to verify the updates through a system audit or validation review.
Step 5: Identify Required Resources
Determine the tools, budget, personnel, or approvals needed to complete each corrective action. Documenting these requirements helps teams plan properly, avoid delays, and confirm that the necessary support is in place before remediation begins.
Step 6: Track Progress and Update the POA&M
Regularly update the POA&M with the status of each action:
- Open: Issue is identified but not yet addressed
- In Progress: Remediation is underway
- Completed: The corrective action is finished and verified
- Deferred: Action is postponed due to valid reasons, such as awaiting funding
Step 7: Document Any Residual Risks
If an issue cannot be fully resolved, document any remaining risk along with the controls or mitigation steps that are still in place. This gives decision-makers a clear view of the remaining exposure and helps them plan next steps, exceptions, or risk acceptance more effectively.
Final Thoughts
The implementation of a Plan of Actions and Milestones (POAM) is crucial in achieving and maintaining compliance. By assessing and addressing vulnerabilities, a POAM helps secure an organization’s data assets and infrastructure from emerging threats. It also demonstrates a commitment to proactive security management.
We encourage all businesses, particularly small and medium-sized enterprises, to adopt this practice as a core component of their broader cybersecurity measures. Integrating a POAM into your cybersecurity strategy helps in complying with legal and regulatory requirements. It also builds trust with clients and stakeholders by showing a dedication to maintaining robust security protocols.
Stay Secure with Bright Defense!
If you are looking to improve your cybersecurity posture, Bright Defense can help. Our team of CISSP and CISA-certified security experts will develop and execute a plan of action to meet compliance frameworks, including SOC 2, ISO 27001, CMMC, and HIPAA. Our monthly engagement model combines our vCISO expertise with compliance automation to simplify and streamline your compliance journey.
Bright Defense also offer risk assessments, business continuity planning, penetration tests, endpoint protection, and managed security awareness training. Contact us today to get started!
Sample POAM Template
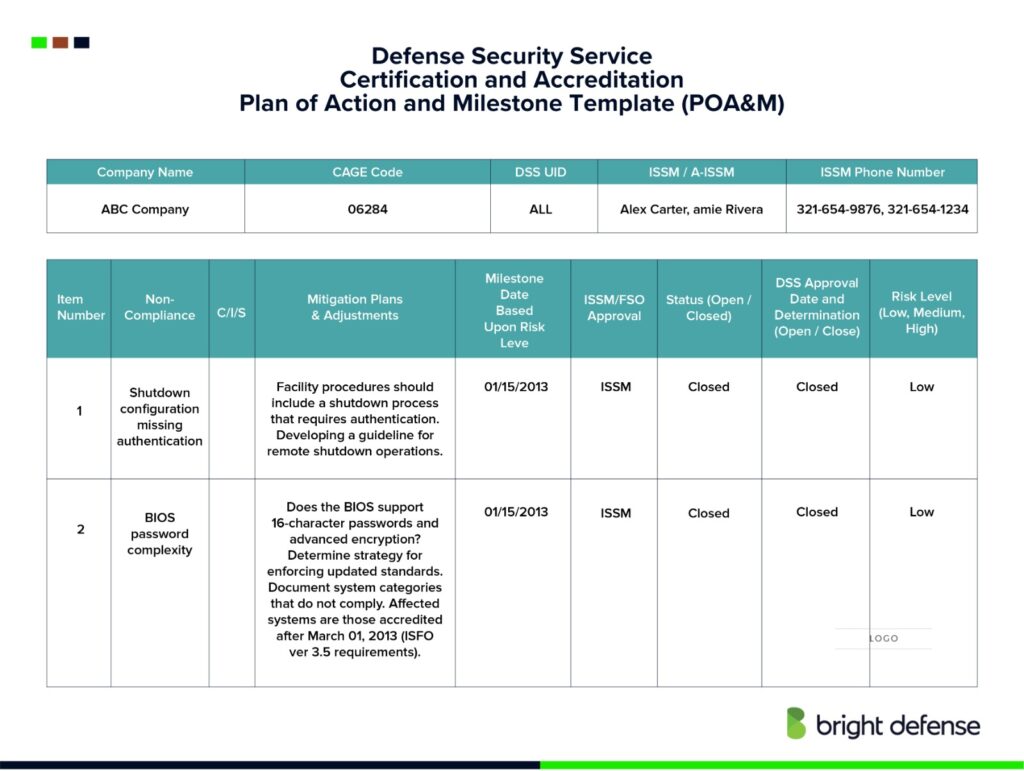
1. Header Information
- Company Name
- CAGE Code
- DSS UID
- ISSM / A-ISSM Names
- ISSM Phone Numbers
2. POA&M Action Items Table
- Item Number
- Non-Compliance Description
- The specific issue or vulnerability (example: shutdown configuration missing authentication).
- C/W/S
- Control reference or category where the issue falls.
- Mitigation Plans & Adjustments
- Detailed plan on how to correct the issue.
- Can include procedural changes, technical fixes, or future upgrades.
- Milestone Date (Based Upon Risk Level)
- The planned date when mitigation will be completed.
- ISSM/FSO Approval
- Indicates whether ISSM/FSO has reviewed and approved the action.
- Status (Open/Closed)
- Current state of the action item.
- DSS Approval Date and Determination (Open/Closed)
- DSS review and final determination status.
- Risk Level (Low/Medium/High)
- The severity level assigned to the finding.
Frequently Asked Questions (FAQ)
A Plan of Actions and Milestones (POAM full form) is a document that outlines specific steps an organization intends to take to address and mitigate security vulnerabilities within its systems. It serves as a roadmap for implementing security improvements and is crucial for tracking progress toward compliance with cybersecurity standards.
You should regularly update a POAM to reflect the progress of mitigation actions, the emergence of new vulnerabilities, changes in business processes, or shifts in compliance requirements. We typically recommend updating a POAM quarterly. However, the frequency can increase depending on the dynamic nature of the organization’s environment and the severity of the vulnerabilities. Regular updates ensure that the POAM remains relevant and that the organization can adapt to new threats and changes effectively.
A System Security Plan (SSP) is a formal document that details the security controls in place for an organization’s system. It describes the system environment, system responsibilities, and the security policies and controls designed to protect the system.
For organizations seeking CMMC (Cybersecurity Maturity Model Certification) compliance, a POAM helps document corrective actions for meeting the required security controls and practices. It is especially crucial for DoD contractors who must meet specific cybersecurity requirements to maintain eligibility for government contracts.
POAMs are critical for government contracts because they demonstrate an organization’s commitment to meeting the stringent security requirements mandated by federal agencies. Handling Controlled Unclassified Information (CUI) often requires them. They are crucial for ensuring the protection of sensitive government data. Additionally, POAMs help ensure the protection of sensitive information, addressing the needs of DoD contractors to safeguard data beyond classified levels, in compliance with the highest cybersecurity standards governed by CMMC Level 3, including DFARS 252.204-7012 rules and measures against APTs.
A corrective action plan within a POAM should include a detailed account of vulnerabilities, the measures planned to address these vulnerabilities, timelines for implementing these measures, and the assignment of responsibilities to ensure accountability. Additionally, third-party assessment organizations (3PAO) play a crucial role in evaluating the effectiveness of these corrective actions, particularly in verifying mitigation efforts and certifying compliance with standards such as CMMC.
Organizations should document their progress by updating the POAM with completed tasks, newly identified vulnerabilities, and revisions to the mitigation strategies as necessary. This ongoing documentation helps maintain operational transparency and compliance with security requirements.
Implementing a POAM typically requires both human and technological resources. Human resources involve personnel responsible for executing tasks and overseeing the process, while technological resources may include security tools and systems for monitoring and enforcing security controls.
Milestones in a POAM indicate key points of achievement within the plan. They gauge progress toward the ultimate goal of mitigating all identified vulnerabilities and play a crucial role in ensuring that corrective actions are completed on schedule.
Get In Touch