Updated:
May 7, 2026
SOC 2 Controls List for 2026
Starting a SOC 2 program means creating controls that fit your company’s goals, risks, and systems. These controls will vary depending on how your organization operates, the data you handle, and what your customers expect.
SOC 2 is based on five Trust Services Criteria, each tied to a specific type of risk. Knowing which controls apply helps you prepare for audits, handle vendor reviews, and keep your security practices in order.
This post outlines the main types of SOC 2 controls, how they connect to the criteria, and where to begin when building your list.
Download SOC 2 Controls List PDF
What Are SOC 2 Controls?
SOC 2 controls are the policies, procedures, and technical measures used to protect systems and data. They help reduce the risk of security risks, mistakes, or unauthorized access.

These controls are based on the SOC 2 Trust Services Criteria, which auditors use as a guide when assessing your organization.
Common examples include password rules, multi-factor authentication, logical access security measures, access permissions, and steps for onboarding and offboarding employees.
Each control supports your overall security program and helps meet the expectations of customers and service organizations.
SOC 2 Controls List
The SOC 2 controls framework is built around five Trust Services Criteria (TSC): Security, Availability, Processing Integrity, Confidentiality, and Privacy. These controls guide how a company protects systems and data and form the core of what auditors evaluate during a SOC 2 examination.

1. Security Controls
Security is the foundation of SOC 2. This category focuses on strong operational practices and defenses against both digital and physical threats. Controls in this section often include multi-factor authentication, web application firewalls, physical and virtual measures, and physical safeguards at server facilities.
Auditors also review indirect controls, such as hiring policies for security roles, to assess whether the organization has established the right environment for protecting confidential information.
Security is the foundation of SOC 2. These controls protect against both digital and physical threats.

Examples include:
- Multi-factor authentication
- Web application firewalls
- Detection and monitoring procedures for unauthorized activity
- Physical safeguards for server rooms
- Hiring and background checks for staff in sensitive roles
- Security awareness training for all employees
2. Privacy Controls
Privacy controls apply to any customer data a company handles. Organizations must clearly communicate their privacy policies to individuals whose data they store.

These controls typically require organizations to:
- Obtain consent before collecting data
- Limit data collection to what is necessary
- Collect data through lawful methods
- Use data only for the purpose stated
- Dispose of data once it is no longer needed, following internal compliance process requirements
- Maintain documentation as part of internal control responsibilities
3. Confidentiality Controls
Confidential data often needs to be shared with trusted parties, for example, health information shared across hospitals and pharmacies. The goal here is not to block access entirely but to manage secure sharing with vetted business partners.
Controls focus on identifying confidential data, limiting unauthorized access, and securely disposing of it after a defined retention period. These safeguards help maintain trust services principles and support compliance efforts.
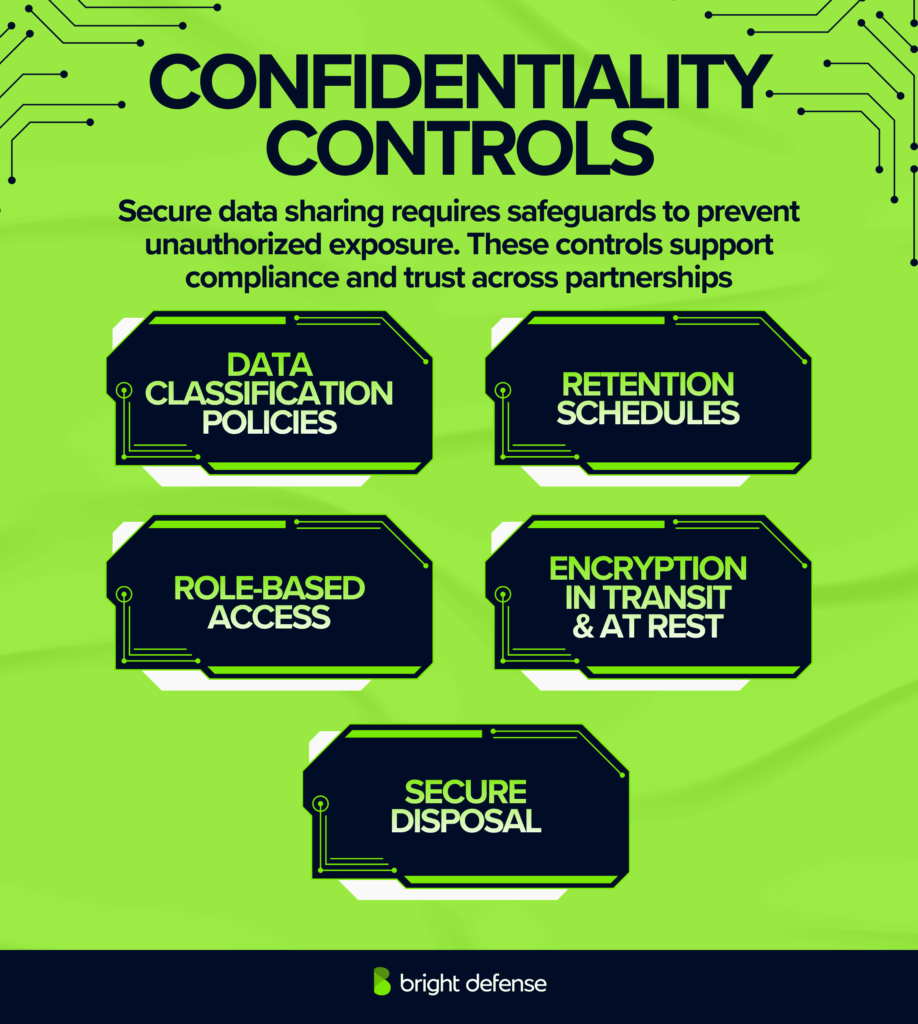
The goal of confidentiality controls is to allow secure sharing without exposing unauthorized users to that data.
Typical controls:
- Data classification policies
- Role-based access permissions
- Use of encryption at rest and in transit
- Secure disposal processes for confidential information
- Retention schedules for confidential data

4. Processing Integrity Controls
These controls address whether systems perform as intended. They focus on the accuracy, completeness, and reliability of system processing, especially when large volumes of data are ingested, processed, and exported. Effective controls help confirm that inputs and outputs align and that no data is lost or altered during processing.
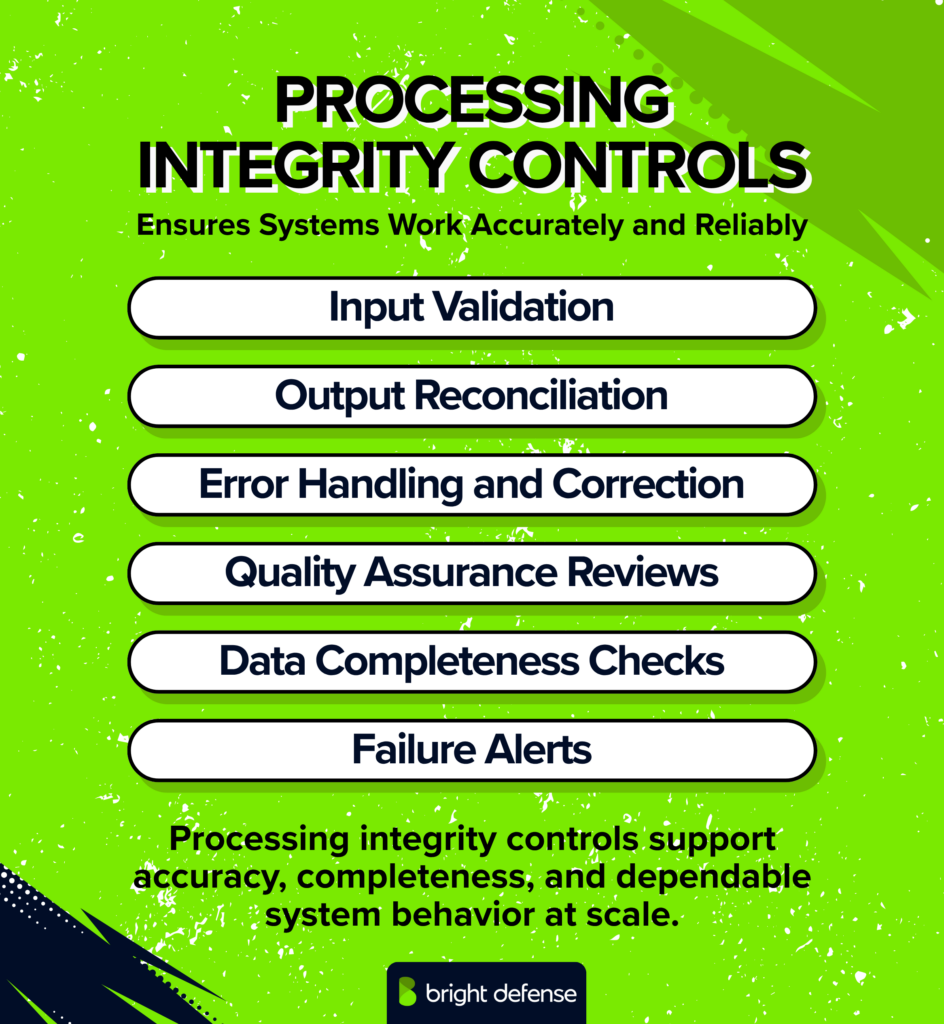
SOC 2 Processing Integrity Controls
Examples include:
- Timely error detection and correction during periods of high processing demand
- Input validation and sanity checks
- Monitoring data pipelines to verify inputs and outputs match expected results
- Reconciling processed data through automated checks and reporting
- Controls that prevent unauthorized system components’ logic changes
- Automated alerts for processing failures
5. Availability Controls
Availability controls aim to reduce downtime and maintain reliable service delivery. These are critical for SaaS platforms and cloud providers. This category also involves input from senior management when defining acceptable recovery objectives and allocating resources.
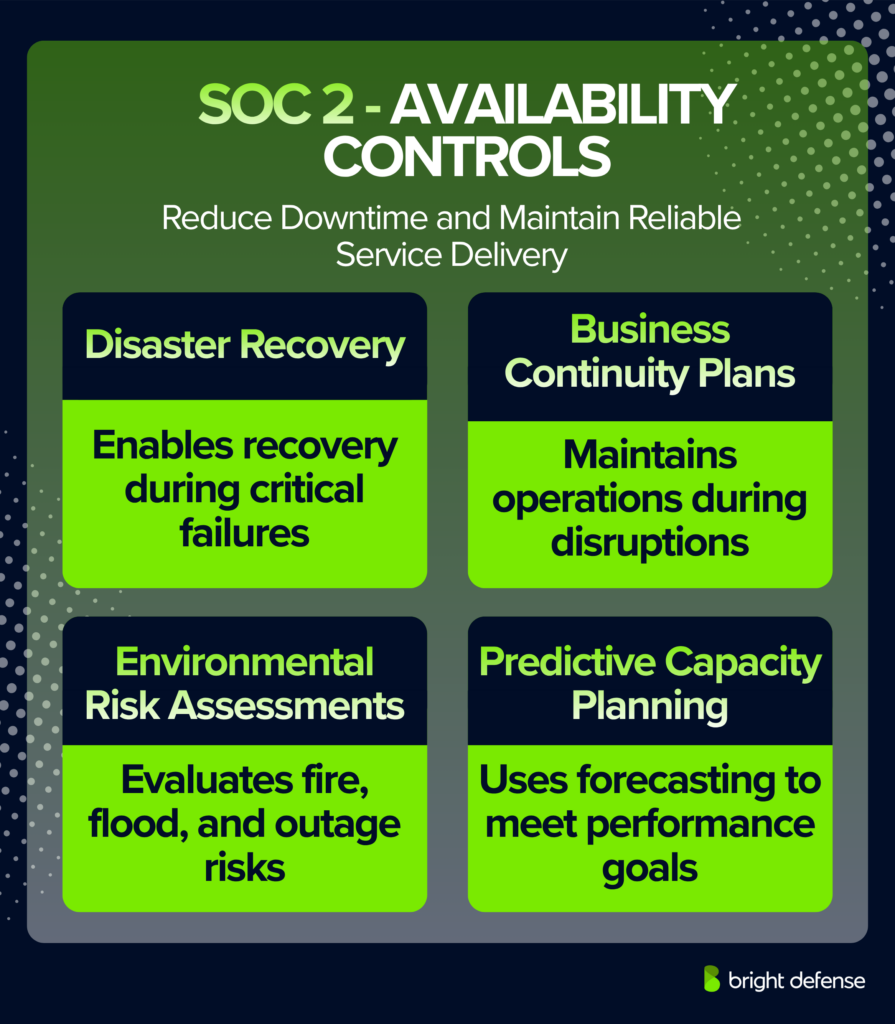
Typical controls include:
- Secure backup procedures
- Disaster recovery plans
- Business continuity plans
- Environmental risk management assessments
- Predictive capacity planning as part of a formal readiness assessment
Control Categories in SOC 2
SOC 2 controls are also grouped into functional categories that support the five TSCs. These include:
1. Control Environment
- Encourages ethical behavior and integrity
- Involves senior leadership and the board in oversight
- Assigns clear responsibilities for controls
2. Communication and Information (CC2)
- Documents policies and procedures clearly
- Communicates data-handling expectations to staff and third parties
- Ensures timely sharing of incident updates and risk alerts
3. Risk Assessment (CC3)
- Regularly evaluates new risks to security and compliance
- Identifies internal and external threats
- Considers the impact of system changes or new services
4. Monitoring Activities
- Tracks control performance over time
- Flags control failures or policy violations
- Shares findings with stakeholders
5. Logical and Physical Access Controls
- Manages user credentials and system permissions
- Uses strong authentication methods
- Restricts physical access to hardware
6. System and Operations Controls
- Logs security events and monitors for anomalies
- Responds to system incidents
- Maintains change logs and version control
7. Change Management Controls
- Requires documented approvals for all code or system changes
- Tests updates in a staging environment
- Tracks who made changes and when
8. Risk Mitigation Controls
- Supports recovery from business disruptions
- Maintains vendor risk assessment practices
- Includes monitoring and contract terms for third-party vendors
Common Criteria (CC-Series)
The Security category includes nine Common Criteria (CC1–CC9), which apply across all TSCs.
- CC1: Control Environment
- CC2: Communication and Information
- CC3: Risk Assessment
- CC4: Monitoring Activities
- CC5: Control Activities
- CC6: Logical and Physical Access Controls
- CC7: System Operations
- CC8: Change Management
- CC9: Risk Mitigation
Each criterion represents a layer of control maturity and helps shape an auditor’s opinion on whether your environment meets SOC 2 standards.

Which SOC 2 Controls Are Hardest To Automate?
The hardest SOC 2 controls to automate are the ones that depend on human judgment, documented review decisions, approvals, or live exercises instead of a simple system-state check. SOC 2 is risk-based rather than checklist-based, and many controls still require uploaded evidence rather than continuous monitoring, which limits full automation.
The controls below usually create the most manual work.
Risk Assessment Controls
These controls require a completed risk assessment, a treatment plan, assigned owners, remediation tracking, and periodic review. Drata highlights that risk outputs directly determine control scope, which ties this process to human evaluation rather than automated signals.
Periodic User Access Reviews
These reviews depend on human validation of access rights, role appropriateness, and remediation decisions. Vanta notes that quarterly reviews remain time-intensive for most teams, and evidence typically includes reviewer comments and completed access changes.
Vendor Management And Third-Party Reviews
AICPA’s How to Perform Proper Vendor Management paper lists governance, policy, third-party risk assessment reviews, due diligence procedures, evaluation of vendor controls, and ongoing monitoring as core parts of the process. Drata adds that organizations should keep a current vendor inventory with risk ratings and review compliance reports or similar evidence for critical vendors at least annually
Incident Response And Business Continuity Testing
These controls require real exercises and documented outcomes rather than passive monitoring. Evidence typically includes test scenarios, participant records, results, and lessons learned, which ties compliance to executed scenarios rather than system data.
Change Management Approvals
Automation can capture commits and deployments, yet approval workflows, testing validation, and exception handling still rely on human decisions. Change management as requires authorization, tracking, and approval across the lifecycle, which keeps this control dependent on documented review rather than automated checks.
Governance And People Controls
These controls depend on policy review, employee acknowledgment, hiring records, and performance evaluations. Policies need to be formally reviewed and accepted, which ties compliance to organizational processes instead of system telemetry.
A practical rule is that SOC 2 controls are hardest to automate when the auditor needs to see who made a decision, what they reviewed, why they approved it, and what happened next. Even the best SOC 2 compliance software cannot remove the human steps tied to these controls.
How Many Controls Are In SOC 2?
SOC 2 does not define a fixed number of controls because it is based on the Trust Services Criteria rather than a standardized checklist. The framework includes about 64 common criteria (CC1 through CC9), and each organization maps its own controls to those criteria based on its systems, risks, and scope.
The total number of controls varies across organizations:
| Scope Type | Typical Number of Controls |
|---|---|
| Small startup | 40 to 70 controls |
| Mid-size SaaS | 70 to 120 controls |
| Enterprise | 120 to 200+ controls |
The final count depends on several factors:
- The Trust Services Categories selected, such as Security, Availability, Confidentiality, Processing Integrity, and Privacy.
- The complexity of systems and infrastructure.
- The level of risk and regulatory exposure.
- Auditor expectations and control granularity.
Most SOC 2 reports focus on the Security category, which contains the core common criteria, and additional categories increase the total control count.
How Bright Defense Cybersecurity Compliance Can Help With SOC 2
Bright Defense Cybersecurity Compliance helps organizations achieve SOC 2 compliance through a structured support model that covers readiness, control implementation, and audit preparation. The team conducts a SOC 2 gap assessment to identify control deficiencies, develops security controls aligned with SOC 2 criteria, and prepares complete audit documentation with organized evidence.
We guide clients through each phase, including scope definition, policy development, evidence collection, and auditor coordination, which creates a clear and manageable compliance path. CISSP and CISA certified experts provide continuous monitoring, risk assessments, and policy updates so compliance remains active after certification. This approach keeps security practices consistent across operations and supports long term audit success through practical execution and direct support.
FAQs
A SOC 2 controls list is the set of controls your organization operates and tests as evidence for the Trust Services Criteria in scope, typically organized in a controls matrix that links each criterion to one or more controls and evidence sources.
No. SOC 2 uses control criteria (the Trust Services Criteria) rather than a single universal checklist, so the SOC 2 requirements depend on scope, system boundaries, and your service commitments.
The Common Criteria (CC1–CC9) are the baseline criteria under the Security category that form the foundation of a SOC 2 examination, and they apply alongside any additional category criteria you include.
These category-specific criteria extend CC1–CC9 and are scoped when the organization makes commitments around uptime, processing accuracy, confidentiality of information, or privacy of personal data.
A workable matrix ties each in-scope criterion to a control statement, an owner, an evidence source, and a test cadence so the auditor can test control design and, for Type II, operating effectiveness over the report period.
Share the SOC 2 report (or permitted sections under NDA), since it typically contains management’s assertion, the system description, the auditor’s report, and the tests of controls and results rather than a standalone “controls list” document.
Start with a clear system scope when working toward becoming SOC 2 compliant, then map CC1–CC9 to your current controls and write down the evidence source and owner for each control so collection work starts early and stays consistent across the audit window.
Check the system and services in scope, the Trust Services Criteria included, the audit period, and the complementary user entity controls (CUECs) section, since CUECs describe controls the customer is expected to operate for the report’s assurance to hold.
SOC 2 security controls are the controls an organization designs and operates to meet the SOC 2 Security criteria, which cover Common Criteria areas such as control environment (CC1), communication and information (CC2), risk assessment (CC3), monitoring (CC4), control activities (CC5), logical and physical access controls (CC6), system operations (CC7), change management (CC8), and risk mitigation (CC9), and Security is defined as protecting information and systems against unauthorized access, unauthorized disclosure, and damage.
SOC 2 has no fixed number of controls because AICPA publishes criteria, and each organization designs its own controls to meet the criteria for the categories in scope; for Security, the Common Criteria are the complete set of criteria, while other categories add extra criteria series.
A widely used “basic” set is the five NIST Cybersecurity Framework functions: Identify, Protect, Detect, Respond, Recover, and CSF 2.0 adds Govern as an additional function.
The COSO Internal Control—Integrated Framework describes five components of internal control: Control Environment, Risk Assessment, Control Activities, Information and Communication, Monitoring Activities.
Get In Touch