Why Penetration Testing is Important for Your Business in 2026
Data breaches occur more frequently and cost more every year. The global average cost per breach has hit $4.44 million, and in the United States, that number jumps past $10+ million. Nearly 20% of breaches happen through known security vulnerabilities and stolen credentials, up 34% from the previous year. Most of these are gaps that can be fixed before they become a problem.
Penetration testing finds those weak spots before someone else does. Running regular pen tests alongside vulnerability assessments helps you identify vulnerabilities across your websites, apps, and other web-facing systems. This article breaks down the benefits of penetration testing and how it keeps breach costs off your balance sheet.
The global penetration testing market is valued at $1.98 billion in 2025 and is projected to reach $4.39 billion by 2031, growing at a compound annual growth rate of 14.2%. That growth reflects rising cyber attacks, stricter regulatory requirements, and the expanding complexity of cloud, mobile, and API-driven environments across industries.
You should perform a penetration test when you:
- Deploy new applications, security infrastructure, or software updates
- Migrate to cloud or shift to remote/hybrid work
- Recover from a ransomware or malware attack
- Onboard third-party vendors with access to your organization’s network
- Prepare for a compliance audit under PCI DSS, HIPAA, SOC 2, or similar frameworks
Penetration testing helps protect more than the organization itself. Regular testing safeguards customer data, reduces financial exposure, satisfies stakeholder and insurer requirements, and preserves brand reputation.
The motivation behind testing has shifted. The Fortra 2024 Penetration Testing Report found that 82% of organizations now cite risk assessment and vulnerability prioritization as their primary pen testing objective, up 12 points from the prior year.
Regulatory compliance ranked second at 72%. Organizations that started conducting penetration testing for regulatory reasons quickly realized the practice delivers far more than a checked box.
Without further ado, here are the key factors that make penetration testing crucial for organizations in 2026:

1. Pen Test Finds Exploitable Vulnerabilities Before Attackers Do
Penetration testing shows you exactly where an attacker would break in. An ethical hacker simulates real attack methods against your systems, networks, and applications to find the specific security weaknesses that lead to actual compromise.
Every major cybersecurity framework describes the same core function: confirming which vulnerabilities are exploitable in practice, not just flagging them in theory.
The window between disclosure and exploitation is getting shorter. Attackers now weaponize new vulnerabilities in an average of 5 days, down from 32 days just one year earlier. That data comes from Mandiant's 2023 analysis, and the window has almost certainly shrunk further since.
Industry-wide penetration testing data shows at least one exploitable vulnerability in 84% of all engagements. These numbers all point to the same takeaway: exploitable weaknesses exist in nearly every environment, and catching them early costs measurably less than responding after a breach.
2. AI Powered Cyberattacks Increase The Need For Penetration Testing
Artificial intelligence has significantly increased the scale and realism of cyberattacks, which makes penetration testing an essential security practice in 2026.
Attackers now use AI tools to automate phishing campaigns, generate impersonation content, and test vulnerabilities at massive scale, which increases the likelihood of successful breaches across organizations.
Security research highlights the rapid growth of AI driven attack activity:
- 62% of organizations encountered deepfake attacks involving AI generated voice or video impersonation used in fraud and social engineering.
- 13% of organizations reported breaches involving AI models or AI driven applications.
- 82.6% of phishing emails now contain AI generated language, which increases message realism and social engineering success rates.
The scale of automated attacks means organizations face constant exposure to phishing, impersonation fraud, and vulnerability exploitation.
Penetration testing provides a practical defense because it simulates the same attack techniques used in real incidents and exposes weaknesses before attackers exploit them. Regular testing keeps web applications, systems, and digital assets prepared for AI generated attack campaigns.
3. Checks Whether Security Controls Actually Work Under Attack Pressure
Firewalls, endpoint protection, intrusion detection systems, and access controls all look functional on a dashboard. Penetration testing puts them under real attack pressure to find out whether they actually stop an attacker.
A pen tester chains together techniques the same way a threat actor would, testing whether your security measures hold up when someone actively tries to bypass them.
The average enterprise runs roughly 75 security solutions, yet 67% of U.S. organizations still reported a breach in recent surveys.
A test might reveal that a web application firewall blocks known attack signatures but fails against slightly modified payloads, or that multi-factor authentication protects the front door while a misconfigured API grants the same access without any authentication at all.
Pen testers go entirely undetected in roughly 61% of engagements, meaning the security operations team never triggers an alert during the simulated attack. That single metric tells an organization more about its defensive readiness than months of log reviews or compliance checklists.
4. Reduces Breach Risk & Protects Sensitive Data
Penetration testing directly lowers the probability of a successful breach by identifying and eliminating the attack paths an intruder would use to reach sensitive data.
A pen test maps out exactly how an initial foothold turns into full access to customer records, financial information, intellectual property, and employee credentials, and gives your team the specifics needed for risk mitigation before those paths are used.
IBM's 2025 Cost of a Data Breach Report puts the global average breach cost at $4.44 million, with U.S. organizations hitting a record $10.22 million. Healthcare remains the costliest sector at $7.42 million per incident. Breaches contained within 200 days cost $3.87 million, while those that lingered longer averaged $5.01 million.
Organizations using AI and automation extensively in their security operations saved an average of $1.9 million per breach and shortened the breach lifecycle by 80 days. The average annual pen testing budget of $164,000 to $187,000 represents a fraction of a single breach's total cost.
Penetration testing reduces operational exposure by catching exploitable weaknesses during a controlled engagement rather than during an active incident that triggers downtime, forensic investigations, legal response, and regulatory notifications.
5. Meets Compliance And Policy Requirements
Penetration testing is a stated requirement across most major regulatory frameworks and industry standards. PCI DSS v4.0, mandatory since March 2025, requires both internal and external penetration tests at least annually under Requirement 11.4. NIST SP 800-53 Rev. 5 mandates pen testing for all high-baseline federal systems through Control CA-8. HIPAA, SOC 2, ISO 27001, GLBA, and FedRAMP all include penetration testing as part of their security validation expectations.
Most frameworks require that all exploitable findings are remediated and retested to confirm the fix. PCI DSS specifically mandates this cycle, and CISA's Cybersecurity Performance Goals carry the same expectation. A penetration test that produces documented findings, remediation records, and retest confirmation gives your compliance team a clean audit trail that satisfies multiple frameworks at once.
Card brands and acquiring banks impose PCI non-compliance penalties that can reach up to $100,000 per month. Organizations that suffer a breach while non-compliant face steeper fines, increased legal liability, and potential loss of the ability to process card payments. Regular penetration testing keeps your organization ahead of audit cycles, and the resulting documentation serves as ongoing evidence of due diligence.
6. Prioritizes Remediation Based On Real Exploitability
Penetration testing tells your team which vulnerabilities to fix first and why. Automated scanners generate long lists ranked by severity scores, but those scores do not account for your specific environment, business context, or whether a vulnerability is actually reachable from the outside.
Roughly 60% of all vulnerabilities receive a high or critical CVSS rating, yet only about 3% result in meaningful exposure when tested against real-world conditions.
Penetration testing reorders that list by actual exploitability, showing which findings grant an attacker real access and which ones exist only on paper.
Context matters just as much as technical severity. A medium-severity vulnerability on a server that handles payment processing carries far more consequence than a critical-severity finding on an isolated test system.
Pen testers factor in what data is at stake, what systems connect downstream, and how much operational damage a successful exploit would cause. That context turns a raw vulnerability report into a remediation plan ranked by what matters most to the business.
7. Improves Reporting Quality And Fix Validation
A penetration test produces a detailed report that goes far beyond what automated tools deliver. Each finding includes proof of exploitation, the exact steps taken to reach the vulnerability, the systems and data affected, and a risk rating tied to real-world impact.
That reporting quality directly addresses incomplete remediation, one of the biggest problems in vulnerability management. Industry data shows that less than 48% of pen test findings are actually resolved, and among high and critical severity issues, roughly 31% remain unpatched. A well-structured pen test report closes that gap with clear reproduction steps, ranked severity based on demonstrated impact, and specific remediation guidance.
Retesting confirms whether each remediation effort actually eliminated the vulnerability or simply masked it. The median time to resolve all pen test findings sits at roughly 67 days, nearly five times longer than most organizations target. Retesting catches fixes that fall short, prevents the same weaknesses from reappearing, and gives leadership a verified record that identified risks have been fully addressed.
Types of Penetration Testing
Penetration testing takes many forms, each targeting a different part of your environment. Some focus on network security and infrastructure, others on web application testing and mobile apps, and a few test physical security and human behavior.
Here are the 10 most common types and what each one covers.
- Network Penetration Testing — Tests your internal and external network infrastructure (servers, firewalls, routers, switches) for weaknesses an attacker could use to break in or move laterally across the organization's network.
- Web Application Penetration Testing — Simulates attacks on websites, portals, and web app tools to find security flaws like SQL injection, cross-site scripting, broken authentication, and insecure access controls.
- Client-Side Penetration Testing — Targets software employees use every day (browsers, email clients, document viewers, plugins) to see if attackers could exploit vulnerabilities through phishing or malicious files.
- Wireless Penetration Testing — Checks your Wi-Fi networks for weak encryption, rogue access points, default credentials, and signal leakage that could let an attacker connect from outside the building.
- Social Engineering Penetration Testing — Tests how employees respond to social engineering attacks like phishing emails, phone scams (vishing), fake text messages (smishing), and in-person impersonation. Results help build security awareness across the organization.
- Physical Penetration Testing — Attempts to bypass real-world physical security (locks, badge readers, cameras, security guards) to access restricted areas, steal equipment, or plant rogue devices.
- API Penetration Testing — Probes your API endpoints for complex vulnerabilities in authentication, authorization, input validation, and business logic that automated scanners typically miss.
- Mobile Application Penetration Testing — Simulates attacks on iOS and Android apps to find issues in data storage, encryption, session handling, and communication with backend servers.
- Cloud Penetration Testing — Tests the parts of your cloud environment you control (IAM roles, storage settings, APIs, workload configurations) for misconfigurations, exposed endpoints, and overly broad permissions.
- IoT Penetration Testing — Assesses connected devices (sensors, cameras, controllers) across hardware, firmware, wireless protocols, cloud APIs, and companion apps to find security weaknesses standard audits miss.
What's the Difference Between Penetration Testing vs. Vulnerability Scanning
Penetration testing and vulnerability scanning both find security weaknesses in networks, systems, and applications. The two methods serve different purposes and produce different results.
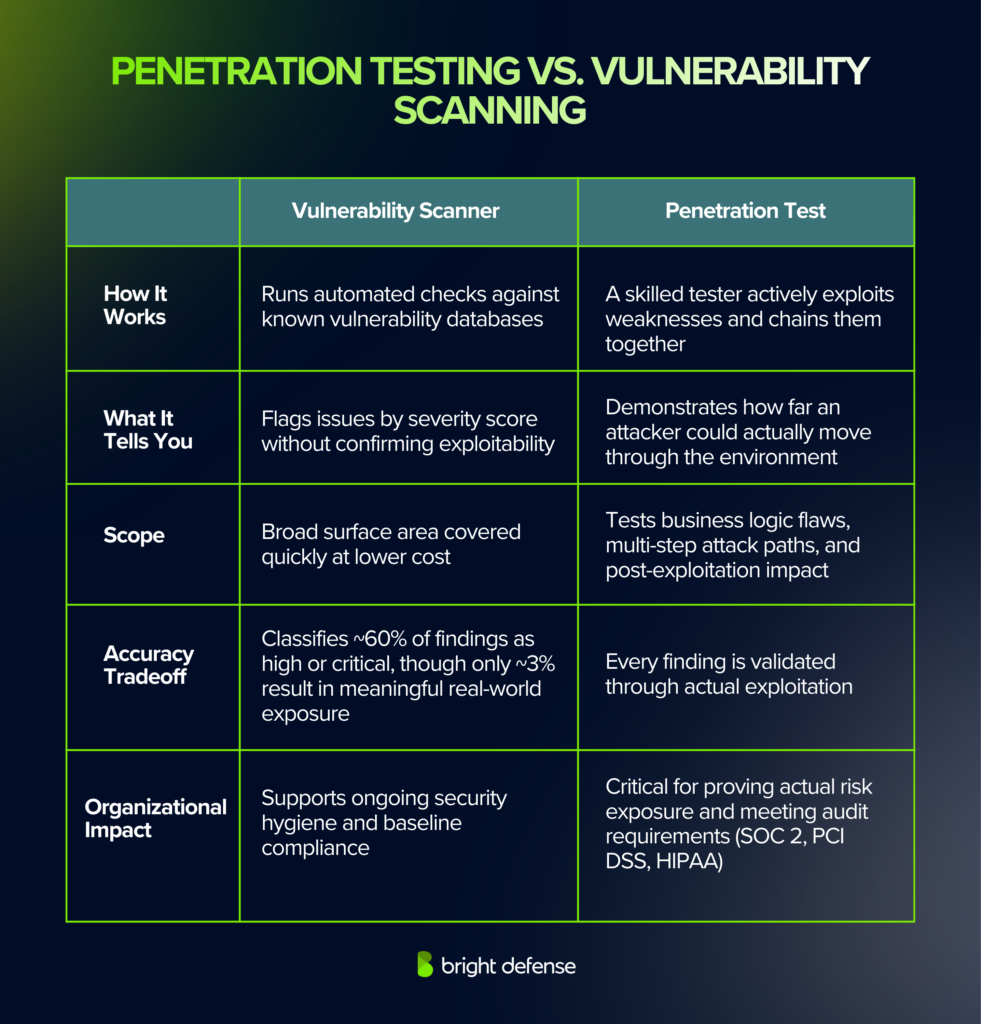
Vulnerability scanners:
- Run automated checks against known vulnerability databases
- Flag issues based on severity scores without confirming exploitability
- Cover broad surface area quickly at lower cost
- Classify roughly 60% of all vulnerabilities as high or critical, even though only 3% result in meaningful real-world exposure
Penetration testing:
- Uses a skilled tester to actively exploit weaknesses and chain them together
- Demonstrates how far an attacker could move through the environment
- Tests business logic flaws, multi-step attack paths, and post-exploitation impact
- Produces findings with proof of exploitation, root cause analysis, and prioritized remediation steps
The OWASP Web Security Testing Guide states that automated tools alone are insufficient for in-depth security assessments. Manual tests uncover chained attack paths, business-logic flaws, and context-dependent risks that scanners structurally cannot detect.
The Fortra 2024 Penetration Testing Report found that 86% of organizations run both methods together, treating scanning as necessary but not sufficient on its own.
How a Penetration Test Works: Process, Best Practices, and Testing Types
A penetration test combines manual and automated techniques carried out by trained security professionals familiar with the systems they are testing. Industry frameworks from NIST SP 800-115, OWASP, and PTES define the process to keep results consistent, repeatable, and audit-ready.
Here's what the entire pentest process looks like:

1. Scoping and Pre-Engagement
The process starts with a written agreement that defines what gets tested, which methods the testers can use, and what stays off-limits. Both sides sign off before any testing begins.
This gives the testing team legal authorization and gives your team full visibility into the timeline and approach. The scope determines whether the engagement covers a single computer system, an entire network segment, or a combination of both.
2. Reconnaissance and Discovery
The testing team gathers information about the target system from internal and external sources using the same methods a real attacker would. This phase maps out your attack surface to find entry points and exposed services.
Activities include collecting publicly available data from DNS records and domain registrations, scanning for open ports and running services, identifying known vulnerabilities tied to your technology stack, and reviewing organizational details for social engineering paths.
3. Exploitation and Penetration Attempt
With the attack surface mapped, testers begin the penetration attempt to break into the environment. The goal is to show exactly what a real attacker could do with each weakness.
This may include gaining unauthorized access to systems or databases, escalating from a basic user account to admin-level access, moving across your network to reach internal systems, extracting or modifying data, and bypassing security controls like firewalls, MFA, and intrusion detection.
Testers document every step, tool, and technique along the way. How individual weaknesses connect into a full attack path often matters more than any single finding on its own.
4. Reporting and Analysis
The testing team delivers a report covering every finding with proof of exploitation, affected systems, risk severity, and specific steps to fix the issue. The report includes an executive summary with business risk context, technical details with reproduction steps and evidence, risk ratings based on real-world exploitability, prioritized fix recommendations, and a record of which security controls detected the tester and which did not.
5. Remediation and Retesting
Your team fixes each issue based on the priority ranking in the report. After fixes go in, the pen testing team retests those specific vulnerabilities to confirm full resolution.
This step is critical because incomplete fixes are common. The median time to resolve all pen test findings is 67 days, and 31% of serious issues remain unpatched even after reporting. PCI DSS v4.0 specifically mandates this fix-and-retest cycle.
Three Types of Penetration Tests
- Black box testing gives the tester little to no prior knowledge of the infrastructure. This approach simulates a real-world cyberattack from an outsider and functions as a covert pen test where defenders may not know testing is underway.
- White box testing provides the tester with full knowledge of the source code, architecture, and environment. This allows for a deeper, more thorough examination of internal weaknesses and is common for internal penetration testing engagements.
- Gray box testing gives the tester partial knowledge of the internal network or application. This simulates an attack from a user with some level of access, such as a compromised employee account or third-party vendor.
An internal pen test focuses on what an attacker could do after gaining a foothold inside the network, while an external pen test targets internet-facing assets to determine whether an outsider can breach the perimeter.
Most organizations that perform both as part of a holistic security strategy get the clearest picture of their overall exposure.
Best Practices for Getting the Most From a Penetration Test
A penetration test delivers the most value when both sides prepare for it.
The following practices help IT and security professionals get clearer findings, faster remediation, and stronger results from every engagement:
- Define clear objectives and scope before the test begins. Specify which systems, applications, and networks are in scope and what business risks you want the test to address.
- Select qualified testers with relevant certifications and experience. Outsource the engagement when internal teams lack the expertise or independence required for an objective assessment.
- Set communication guidelines so relevant personnel know when the test will occur. Establish a process for escalating critical findings during the engagement and reviewing results afterward.
- Test after significant changes to your environment, including new deployments, cloud migrations, infrastructure updates, and post-incident recovery.
- Treat retesting as mandatory. Confirm that every remediated finding has been fully resolved before closing the engagement.
- Implement efficient security measures based on the pen test findings. Use the prioritized remediation guidance to allocate resources toward the potential vulnerabilities that carry the highest business risk.
- Set testing frequency based on your risk profile. An organization that performs pen tests annually meets most compliance minimums, but those facing elevated cyber threats or rapid infrastructure changes should test more often.
Bright Defense Finds Your Vulnerabilities Before Attackers Do
Bright Defense's penetration testing team works the same way real attackers do, probing your networks, applications, and cloud environments to find the specific weaknesses that lead to compromise.
The difference is you get a detailed report with proof of exploitation, prioritized remediation steps, and retesting to confirm every fix holds.
Our approach covers the full scope of what modern organizations need tested, from web application penetration testing and network penetration testing assessments to cloud security reviews and social engineering simulations.
Every engagement follows industry-accepted methodologies aligned with NIST, OWASP, and PCI DSS v4.0, so your results serve both your security posture and your compliance requirements.
Whether you need a first-time assessment, annual testing for SOC 2 or PCI DSS compliance, or retesting after a major infrastructure change, Bright Defense delivers clear findings and actionable remediation guidance your team can act on immediately.
Schedule your penetration test and get a clear picture of your risk before an attacker does.
Frequently Asked Questions on Why Penetration Testing is Important
Penetration testing finds exploitable weaknesses before attackers do, validates whether security controls actually work under pressure, supports compliance with frameworks like PCI DSS and HIPAA, and produces prioritized remediation steps tied to real business impact. Organizations with proactive security testing save an average of $1.9 million per breach compared to those without.
Penetration testing validates practical attack paths and impact, which turns potential vulnerabilities into proven, actionable security risks that teams can fix and retest. This process supports risk mitigation by showing exactly where defenses break down. NIST SP 800-115
Penetration testing can uncover chained attack paths, business-logic issues, complex vulnerabilities, and access-control failures that automated penetration testing tools often do not confirm or cannot safely exploit. Manual tests by skilled penetration testers catch context-dependent issues that scanners structurally miss. OWASP Web Security Testing Guide
No. Vulnerability scanning focuses on detecting potential weaknesses and security flaws across broad surface areas. Penetration testing focuses on confirming exploitability and real-world impact by attempting to exploit vulnerabilities the way a real attacker would. PCI SSC Penetration Testing Guidance v1.1
Most programs follow at least annual testing plus testing after significant changes to security infrastructure. PCI DSS guidance states testing must occur at least annually and after significant changes. Organizations facing frequent cyber attacks or operating under strict regulatory requirements should increase their testing frequency. PCI SSC Penetration Testing Guidance v1.1
A well-scoped test uses written rules of engagement, safety constraints, and coordination to reduce operational risk. Effective penetration testing balances thoroughness with caution, but any active testing can create some risk in production environments. NIST SP 800-115
Confirm scope, test windows, points of contact, escalation rules for critical findings, and clear written authorization so the test stays controlled and legal. Defining which network security components and applications are in scope helps the testing team identify vulnerabilities efficiently. NIST SP 800-115
A typical outcome includes documented findings, evidence, affected assets, risk context, and remediation guidance. The report details every security vulnerability discovered, the steps taken to exploit it, and specific recommendations for implementing efficient security measures. NIST SP 800-115
Look for clear methodology, strong scoping discipline, safe testing practices, and reporting quality. Confirm the team includes experienced ethical hacking professionals who can test the exact tech stack and environment you run, including social engineering attacks when needed. A provider that performs pen tests across network, application, and cloud environments gives you the broadest coverage. Bright Defense Penetration Testing · CISA Penetration Testing service overview
Fix the highest-impact items first, validate fixes with retesting, and keep the report plus remediation evidence for customer reviews and regulatory compliance needs. Penetration testing helps close the loop only when remediation is verified and documented. PCI SSC Penetration Testing Guidance v1.1
11. Why is penetration testing important?
Penetration testing is important because it shows whether security measures can be defeated under real-world constraints. It produces actionable findings on security weaknesses that matter for risk and policy requirements, helping organizations find security weaknesses and address them before a security incident occurs. NIST Computer Security Resource Center
12. What are the 4 types of security?
Four commonly referenced security control groupings are management (administrative) controls, operational controls, technical controls, and physical and environmental controls. Together they form the foundation of an organization's security infrastructure. NIST Computer Security Resource Center
13. What are the 7 stages of penetration testing?
A commonly used 7-stage model (PTES-style) is pre-engagement interactions, intelligence gathering, threat modeling, vulnerability analysis, exploitation, post-exploitation, and reporting. These stages help identify potential vulnerabilities systematically and produce results that support both remediation and compliance. KirkpatrickPrice
14. What is the significance of the penetration test?
A penetration test is significant because it provides evidence of practical attack paths and impact. It supports remediation planning plus security assessment and compliance verification, giving organizations a clear basis for strengthening security measures against real-world cyber threats. NIST Computer Security Resource Center
15. What is penetration testing?
Penetration testing is an authorized security test where an ethical hacker uses attacker-style methods to find and exploit vulnerabilities in systems, networks, or applications. The goal is to identify security weaknesses in a computer system or network before real attackers do. NIST SP 800-115
Get In Touch