John Minnix - Compliance Strategist
June 30, 2025
SOC 2 Compliance Requirements: Your Essential 2024 Guide
Are you seeking clarity on SOC 2 compliance requirements? Our SOC 2 compliance requirements overview will break down the key elements you need to know for 2024. SOC 2 is a critical framework for protecting customer data and demonstrating your organization’s commitment to information security. Whether you’re in finance, healthcare, education, or technology, understanding and implementing SOC 2’s five Trust Services Criteria is an essential step towards building trust and building a robust security culture.
Let’s get started!
Key Takeaways
- SOC 2 compliance is a customizable approach to data security that demonstrates an organization’s commitment to protecting customer data. It is key for building trust and avoiding security breaches.
- The SOC 2 framework is based on five Trust Services Criteria—Security, Availability, Confidentiality, Processing Integrity, and Privacy—with Security being the only required criterion for all audits.
- Organizations seeking SOC 2 compliance must undertake a thorough preparation process. This includes self-audits, and readiness assessments. They also must select relevant Trust Services Criteria.
- Continuous monitoring is critical for maintaining compliance and preparing for annual audits.
- Bright Defense can help you achieve SOC 2 compliance.
Understanding SOC 2 Compliance
For service organizations, SOC 2 compliance represents a significant achievement. It showcases their commitment to information security. It also demonstrates their ability to manage and protect client data effectively. SOC 2 stands out for its adaptable, risk-based approach. Flexibility distinguishes SOC 2 from more rigid, prescriptive frameworks like ISO 27001.
This flexibility enables organizations to tailor their security controls and audit processes to meet their unique business needs and challenges. By doing so, companies can implement a cybersecurity strategy that aligns precisely with their operational requirements and risk profile. This ensures effective and efficient protection of sensitive data.
Why is SOC 2 compliance important?
By adhering to SOC 2 standards, organizations can enhance their security controls, ensuring that sensitive data is handled securely and responsibly. This is crucial for protecting against data loss and theft, and for maintaining operational integrity and resilience.
Furthermore, achieving SOC 2 is a powerful tool for building trust with clients and stakeholders. It provides a transparent validation from an independent third party that an organization is committed to maintaining a high standard of data security. This is particularly important when dealing with clients who are entrusting their sensitive information to your company.
Who needs SOC 2 compliance?
SOC 2 compliance is essential for a broad range of industries, especially those that manage or process sensitive customer data. Its importance transcends specific sectors, making it relevant to any organization focused on safeguarding data integrity and privacy. Particularly critical are sectors such as:
- Finance: Banks, investment firms, and insurance companies, which deal with highly sensitive financial data and are often under strict regulatory scrutiny.
- Healthcare: Healthcare providers, insurers, and related services that handle protected health information (PHI) and must comply with privacy regulations such as HIPAA and SOC 2.
- Education: Educational institutions that store student data, from personal information to academic records, which are protected under laws like FERPA.
- Technology: This sector includes companies providing Software as a Service (SaaS), cloud computing, data hosting, and other IT services.
The need for SOC 2 compliance is particularly pronounced among technology companies, such as SaaS and cloud services providers. This is due to the inherent risks of digital data storage and transfer.

Key Components of SOC 2 Compliance
The five Trust Services Criteria (Security, Availability, Confidentiality, Processing Integrity, and Privacy) are at the core of SOC 2 compliance. These criteria form the foundation for assessing a service organization’s controls. These criteria form the pillars that uphold the structure of SOC 2 compliance, with each pillar addressing a specific aspect of information security. While security is the only criterion that is compulsory for all organizations undergoing a SOC 2 audit, the other criteria can be just as crucial, depending on the organization’s specific operations and risk exposure.
To meet the requirements of these criteria, organizations are guided by the certified public accountants. These points serve as a roadmap for designing suitable controls that satisfy the specific requirements under each Trust Services Criteria. This ensures a comprehensive evaluation during the SOC 2 compliance process.
Let’s examine each of these criteria in greater detail.
Security
Security is the cornerstone and the only mandatory criterion of a SOC 2 audit, highlighting the essential role of security measures in safeguarding client data. In an era where cyber threats are escalating, implementing strong security controls such as access controls, firewalls, and operational protocols to block unauthorized access has become increasingly vital.
However, aligning with SOC 2 compliance isn’t a one-time effort. It requires ongoing adaptation of security measures to combat emerging threats. This adaptation includes implementing advanced protections like two-factor authentication and encryption to enhance security against unauthorized access.
But what about the need for systems to remain continuously operational to handle incoming data?
Availability
The Availability principle ensures that systems, operations, and services are accessible to authorized users as stipulated by agreements with customers or business partners. It underscores the importance of resource availability for authorized use. In today’s fast-paced environment, where even minimal downtime can incur substantial losses, maintaining high standards for operational uptime and performance is crucial for SOC 2 compliance.
SOC 2’s availability controls extend beyond minimizing downtime. They emphasize the importance of business continuity, disaster recovery planning and testing, data backups, and replication, along with infrastructure and capacity monitoring. These controls are designed to prevent, detect, and rectify interruptions in service availability, including system maintenance, capacity planning, incident response, and business continuity strategies. System availability levels are typically defined through mutual agreements between the service provider and the client, aligning expectations and operational requirements.
However, how does one ensure the confidentiality of sensitive data to protect customer information?
Confidentiality
The Confidentiality principle is critical in restricting access to sensitive data to authorized personnel only. It involves stringent controls over both logical and physical access to prevent unauthorized disclosure and to detect and respond to data breaches.
Protecting sensitive financial data and internal documents, such as business plans, requires robust mechanisms like firewalls and rigorous access controls. Encryption is particularly crucial in securing data during transmission and limiting access to designated individuals or groups.
But how do we ensure the integrity of data being processed?
Processing Integrity
Processing Integrity is fundamental to SOC 2 compliance, ensuring that the systems used to store, process, and retrieve data function effectively and as intended. Its goal is to maintain data integrity by ensuring that information is accurate, complete, timely, and authorized.
Consider a financial services company that processes online payments. Processing Integrity is vital to ensure that every transaction is processed accurately and securely. This includes verifying that funds are deducted correctly from the payer’s account and credited accurately to the payee’s account, without any errors or delays. Furthermore, the system must be capable of generating reliable and timely confirmations and receipts that reflect the transaction details precisely as intended. Regular reviews of security controls must include verifications of Processing Integrity to ensure that outputs are accurate and that data is processed correctly within the system’s workflow.
And how is personal information handled to ensure privacy?
Privacy
The Privacy principle in SOC 2 compliance focuses on the handling of personal information, ensuring it aligns with the organization’s privacy notice and accepted privacy practices, distinct from confidentiality, which covers various types of sensitive data.
SOC 2 privacy measures are designed to protect Personally Identifiable Information (PII), including any data that can identify an individual. To adhere to SOC 2 privacy criteria, organizations must:
- Inform customers about data collection practices
- Obtain consent for data processing
- Enable individuals to request the deletion of their data
- Protect customer information from breaches
- Clearly outline customers’ privacy rights
With a comprehensive understanding of the key components of SOC 2 compliance, let’s explore the types of SOC 2 reports.

The Two Types of SOC 2 Reports
SOC 2 compliance offers two distinct types of reports—Type 1 and Type 2—each providing critical insights into the controls and processes of a service organization tailored to different purposes. A SOC 2 Type 1 report evaluates the suitability and design of an organization’s controls at a specific point in time. Type 1 is beneficial for organizations that must demonstrate their system’s capabilities to meet the Trust Services Criteria in a short timeframe.
In contrast, a SOC 2 Type 2 report goes a step further. It assesses the operational effectiveness of these controls over a more extended period, typically a minimum of six months. This extended evaluation period provides a more comprehensive view of how effectively the controls are managed and maintained over time. It offers greater assurance to clients and stakeholders about the ongoing security and reliability of the service provider’s operations.
Deciding on the best type for your organization involves considering the organization’s objectives for compliance, the expectations of its clients, and the regulatory requirements it faces. The more comprehensive Type 2 report is often favored by those seeking to establish or reinforce trust with clients over time.
Preparing for SOC 2 Compliance: A Step-by-Step Guide
While preparing for SOC 2 compliance might appear intimidating, it certainly doesn’t have to be so. The journey starts with a self-audit to pinpoint weaknesses in controls. This is followed by a SOC 2 readiness assessment conducted by an experienced auditor to estimate compliance and fill any identified gaps. Selecting relevant Trust Services Criteria based on the organization’s specific operations and risk exposure is crucial to effectively align the audit with the company’s needs and manage the budget.
Organizations must review and adjust their security controls, including internal controls, following SOC 2 requirements. This involves implementing key control activities governed by the chosen Trust Services Criteria and properly documenting these activities for audit purposes in a service organization control report.
The SOC 2 framework involves a cycle that includes readiness and preparation, conducting an internal assessment, and engaging with a CPA firm to conduct an audit.
Perform a self-audit
A SOC 2 self-audit is a critical first step in the compliance journey. It involves:
- Defining the audit scope
- Mapping compliance requirements to current controls
- Identifying gaps
- Creating remediation plans
By conducting internal SOC 2 self-audits, organizations can prepare for the formal audit by mapping their security controls to the selected Trust Services Criteria.
The self-audit process involves:
- Documenting an evidence collection spreadsheet to clearly identify gaps in compliance
- Formulating an action plan for those gaps, including responsibilities and timelines for implementation
- Reviewing current practices and controls against SOC 2 requirements to identify areas needing improvement before the formal audit.
Choose relevant TSCs for audit
Choosing the relevant Trust Services Criteria for a SOC 2 audit is a crucial step in the compliance journey. This choice should be based on the organization’s specific operations and the expectations of their enterprise clients. The decision process includes evaluating service guarantees like uptime and considering customer expectations.
The selection process for Trust Services Criteria typically begins with security criteria. Depending on customer requirements, it may include others like confidentiality or privacy. But how do one ensure that the security controls align with SOC 2 requirements?
Review and adjust security controls
To align with SOC 2 requirements, each organization must tailor its security controls based on its own specific business practices. Reviews of an organization’s security controls should result in necessary updates and documentation to meet evolving SOC 2 compliance standards.
Organizations with SOC 2 Type 2 certification must ensure that their software development and application creation adhere to the established and audited controls. Automation of SOC 2 compliance processes aids in preparing for audits by enabling:
- Continuous monitoring
- Streamlining tasks such as evidence collection
- Control scanning and testing
- Risk assessment
Evidence is a crucial component during SOC 2 audits. It must be compiled and presented to demonstrate adherence to the selected controls.
Complete a final readiness assessment
After updating security controls, a final readiness assessment is crucial to verify that an organization is prepared for the SOC 2 compliance audit. Conducting a final readiness assessment involves testing and reviewing updated security controls to ensure they meet SOC 2 requirements.
This final readiness assessment serves as a critical step for organizations to iron out any discrepancies before facing an independent auditor’s review. But how does one maintain SOC 2 compliance after achieving it?

Maintaining SOC 2 Compliance
Rather than being a one-time achievement, maintaining SOC 2 compliance is an ongoing process. Automation tools in SOC 2 compliance can continuously monitor systems to ensure all compliance controls remain operational, assisting organizations to stay ready for future audits. Compliance automation for SOC 2 extends beyond the initial audit, offering capabilities such as continuous monitoring and effective risk management to support organizations in maintaining their compliance.
Organizations must undergo annual audits to maintain SOC 2 compliance, which includes proving the continued effectiveness of security controls. For continued SOC 2 compliance, companies are advised to:
- Monitor compliance controls
- Maintain security evidence for future audits
- Set proper administrative policies
- Ensure ongoing adherence to technical security controls
- Communicate the results of self-audits and remediation plans to stakeholders
This is crucial in building a strong security culture and preparing for SOC 2 compliance.
However, how does SOC 2 compliance fare compared to other audits conducted by a third-party auditor?
Comparing SOC 1 and SOC 2 Audits
SOC 1 and SOC 2 audits serve different purposes and cater to different audiences. SOC 1 audits are conducted in accordance with the SSAE 18 AT-C 320 standards, focusing on the controls at a service organization that are relevant to their clients’ financial reporting. On the other hand, SOC 2 audits comply with SSAE 18 AT-C 105 and SSAE 21 AT-C 205 standards, evaluating operational and compliance controls based on the AICPA’s Trust Services Criteria.
While SOC 1 reports target an audience interested in the control of financial reporting, such as auditors and financial executives, SOC 2 reports cater to a wider target audience. This includes:
- Compliance officers
- IT executives
- Regulators
- Business partners concerned with operational and compliance controls
Some service organizations may need to undergo both SOC 1 and SOC 2 audits, particularly if they deal with services that affect both their clients’ financial reporting and their own operational and compliance protocols.
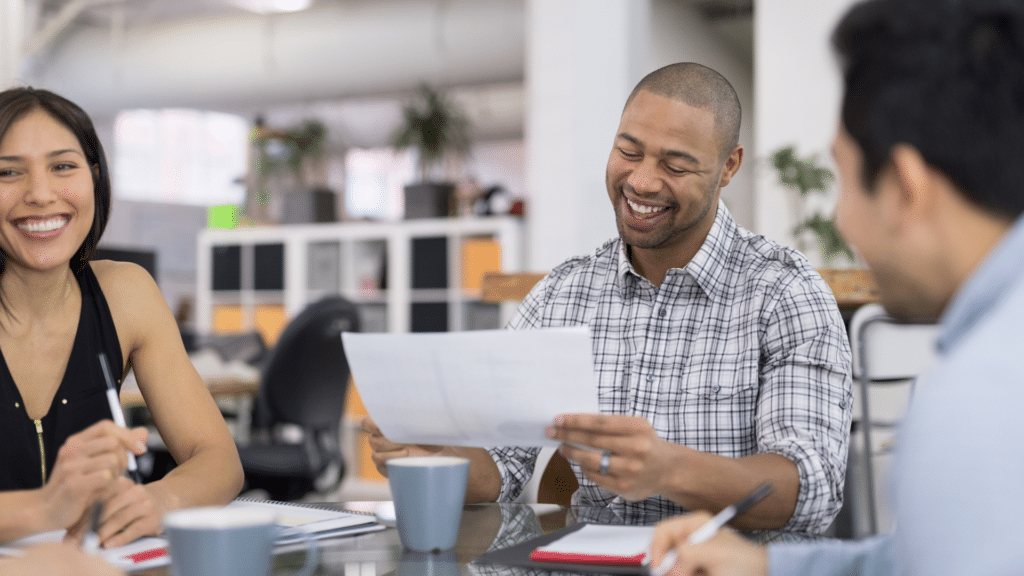
Engaging a SOC 2 Consultant
For many organizations, the path to SOC 2 compliance is daunting. This is particularly true for those lacking in-house expertise. A SOC 2 consultant, like Bright Defense, proves invaluable here. These experts specialize in navigating the complexities of SOC 2 compliance. They provide tailored support that simplifies the entire process.
Benefits of Working with a SOC 2 Consultant
Expert Guidance: A SOC 2 consultant offers a wealth of knowledge and experience. They help demystify the compliance process. Insights into best practices and common pitfalls ensure organizations start on the right track.
Customized Compliance Strategy: Consultants like Bright Defense work closely with clients. They understand each organization’s specific needs and context. They help choose relevant Trust Services Criteria. Their strategies align with each organization’s unique risks and objectives.
Efficiency and Effectiveness: Consultants streamline the compliance process efficiently. They help define the audit scope and map compliance requirements to controls. Identifying gaps and creating remediation plans not only saves time but focuses efforts effectively.
Preparation for Audits: SOC 2 consultants assist in audit preparations. They help document control activities and gather necessary evidence. This ensures everything is ready for a smooth audit process.
Continuous Compliance Support: Beyond initial compliance, consultants help maintain SOC 2 standards over time. They adapt security controls and processes as business needs and threats evolve. This support is crucial for those aiming for SOC 2 Type 2 certification, which requires sustained compliance evidence.

Leveraging Technology for SOC 2 Compliance
Adopting innovative SOC 2 compliance software can offer an organization a competitive edge in a regulated industry, providing benefits such as automated platforms, smart workflows, and expert guidance. Platforms like Drata, Vanta, and Secureframe leverage smart workflows to automate up to 90% of compliance tasks, facilitating evidence collection and control documentation for SOC 2 compliance.
Security for SOC 2 compliance can be enhanced through the use of technological solutions. This includes network and web application firewalls, two-factor authentication, and intrusion detection systems, which provide an additional layer of protection for sensitive data.
Let’s now conclude and recapitulate the key points we’ve learned.
Summary
Navigating the path to SOC 2 compliance may seem daunting, but with a clear understanding of the steps involved, the journey can be a rewarding one. From understanding the importance of SOC 2 compliance to choosing the relevant Trust Services Criteria for audit, we’ve outlined various aspects of SOC 2 compliance. We’ve detailed the key components, explored the two types of SOC 2 reports, and discussed how to prepare for and maintain SOC 2 compliance.
While the road to SOC 2 compliance demands commitment and diligence, the rewards are worth the effort. Achieving and maintaining SOC 2 compliance is a testament to an organization’s commitment to robust information security practices. It’s about building trust with customers and stakeholders, meeting legal obligations, and upholding a reputation in a data-driven marketplace. With the right approach and the right tools, SOC 2 compliance is a goal well within reach.
Bright Defense Delivers SOC 2 Compliance Solutions!
If you are ready to meet SOC 2 compliance requirements for your organization, Bright Defense is here to help. Our monthly engagement model delivers a robust cybersecurity program to meet compliance frameworks including SOC 2, ISO 27001, HIPAA, NIST, and PCI. Once compliance standards are reached, we constantly enhance your security program to keep up with the evolving threat landscape and compliance standards.
All of our continuous compliance plans include automation software. This increases efficiency and lowers the cost of compliance. Get started on your compliance journey today with Bright Defense!

Frequently Asked Questions
What is SOC 2 compliance?
SOC 2 compliance is a voluntary certification that shows a service organization’s commitment to information security and dedication to protecting customer data.
Who needs SOC 2 compliance?
Companies in sectors such as finance, healthcare, education, and technology that handle sensitive customer data need SOC 2 compliance to ensure the security of the data they manage.
What is the difference between SOC 2 Type 1 and Type 2 reports?
The main difference is that a SOC 2 Type 1 report assesses security controls at a specific point in time, while a Type 2 report evaluates control effectiveness over an extended period. This distinction is important for understanding the scope and depth of the assessments.
How can an organization prepare for SOC 2 compliance?
To prepare for SOC 2 compliance, an organization should perform a self-audit, select relevant Trust Services Criteria (TSCs), review and adjust security controls, and complete a final readiness assessment. These steps are crucial for ensuring compliance with SOC 2 standards.
How can technology aid in SOC 2 compliance?
Implementing innovative software and automating compliance tasks can greatly aid in SOC 2 compliance. Additionally, utilizing technology such as network and web application firewalls, two-factor authentication, and intrusion detection systems can enhance security.
Get In Touch