Updated:
April 17, 2026
What is Audit Readiness? A Complete Guide!
Audit readiness is the state where your organization can pass a formal audit at any time without last-minute preparation.
According to a 2025 survey of 500 IT and security decision-makers by Swimlane, only 29% of organizations say their compliance programs consistently meet internal and external standards, and 62% report that their audit evidence-gathering process is at least occasionally error-prone, which shows just how common unprepared environments remain.
In practice, audit readiness means your team does not scramble when an auditor requests proof. You already have structured documentation, mapped controls, and real-time visibility into compliance status. This reduces delays, avoids gaps, and keeps audits predictable.
This matters because most compliance failures happen due to missing evidence, unclear ownership, or inconsistent processes. Audit readiness removes those risks and turns audits into a routine validation step instead of a disruptive event.
The next sections break down what audit readiness includes, how it works in real environments, and what your team needs to maintain it continuously.
Why Do You Need To Be Audit Ready?
You need to be audit ready because it shows your security controls, policies, and evidence are already in place before an auditor asks for them. Audit readiness helps your team catch gaps early, fix control weaknesses, and keep your compliance program consistent instead of scrambling at the last minute. It has clear business value as well.
Drata reports that 41% of respondents said the lack of continuous compliance slowed their sales cycle, which shows that weak audit readiness can affect revenue, trust, and deal speed, not just audit outcomes.
Why Audit Readiness Matters For Businesses
Audit readiness matters because it shortens response time, reduces audit friction, strengthens accountability, supports year-round compliance, and surfaces issues earlier.
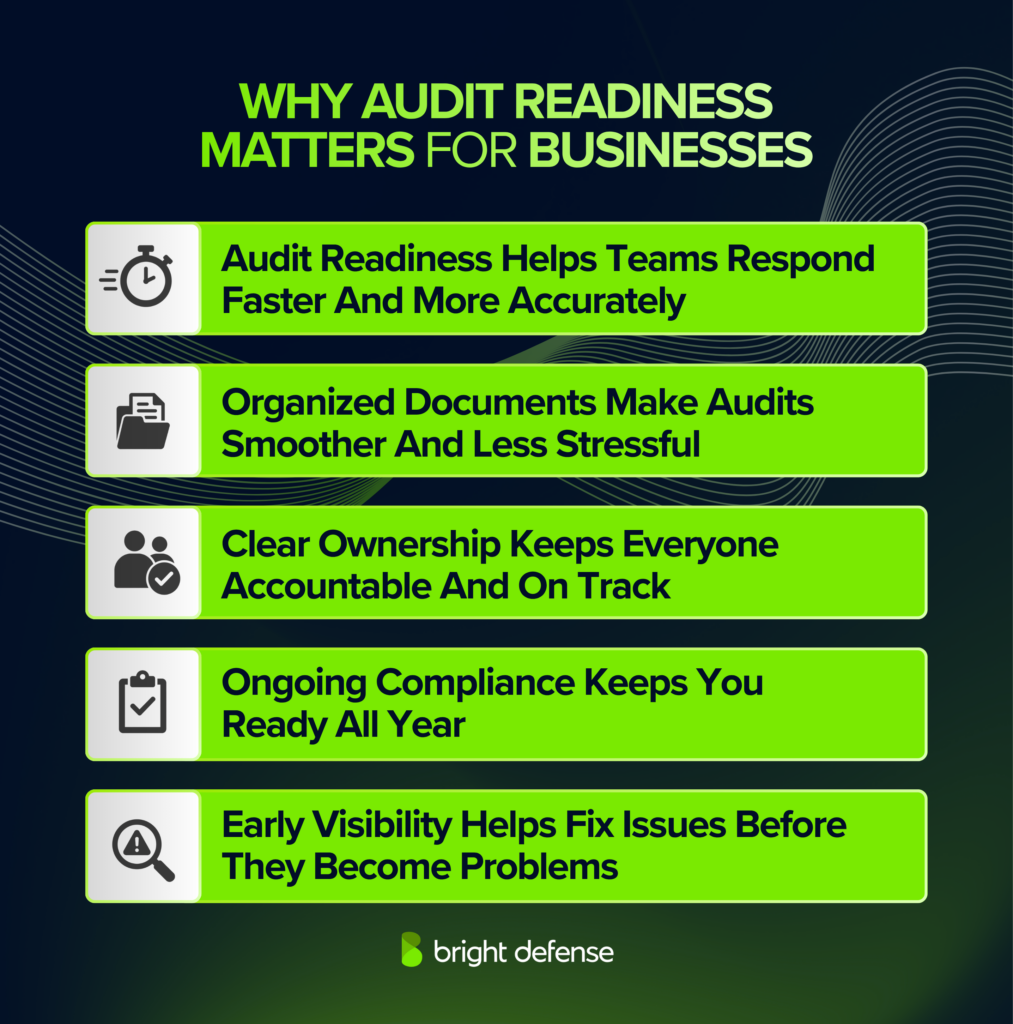
1. Audit Readiness Helps Teams Respond Faster And More Accurately
Audit readiness gives teams faster access to the right evidence, which leads to quicker responses and fewer avoidable mistakes. In PwC’s 2025 Global Compliance Survey, 53% said compliance technology improved speed of issue response, 48% reported higher-quality reporting, and 46% reported faster, more confident decision-making.
2. Organized Documents Make Audits Smoother And Less Stressful
Organized records remove much of the last-minute scramble that makes audits disruptive for operations, finance, and security teams. Thomson Reuters found 65% of risk and compliance respondents said automating manual processes would reduce complexity and cost, while 49% said standardizing frameworks across the organization would simplify the work.
3. Clear Ownership Keeps Everyone Accountable And On Track
Clear ownership keeps audit requests from stalling between teams and gives leaders a cleaner view of progress. PwC found 59% of companies reported greater confidence in compliance decision-making because of better coordination, while Thomson Reuters found 43% said breaking down silos and improving cross-department communication would reduce complexity and cost. That pattern goes to show that accountability improves when owners, deadlines, and evidence paths are clear.
4. Ongoing Compliance Keeps You Ready All Year
Ongoing compliance matters because audit pressure and regulatory change continue throughout the year, not just during audit season. Thomson Reuters found 61% of respondents named keeping up with upcoming regulatory and legislative change as a top strategic priority for the next 12 to 18 months, and PwC found 85% said compliance requirements have grown more complex over the last three years.
5. Early Visibility Helps Fix Issues Before They Become Problems
Early visibility turns audit readiness into a prevention tool instead of a cleanup exercise after a control gap has already grown. PwC found 64% of companies gained better visibility into risks and risk management activities from compliance technology. Caseware reported 21.4% use data analytics for all audits and 56.6% use it for some audits, which means 78% already rely on analytics to improve accuracy, spot anomalies, and flag high-risk areas or control deficiencies sooner.
What Does an Audit Readiness Checklist Look Like?
Audit readiness begins with scope, ownership, and evidence that are defined before fieldwork starts. A usable checklist should show what is in scope, who owns each control, and what records will support testing once the auditor begins requesting information.
1. Define The Audit Scope
The first job is to draw the boundary around the audit. That means naming the framework, the systems in scope, the data involved, the business functions touched by the review, the third parties that support those functions, and the locations that matter to the control environment.
Weak scope definition creates avoidable problems later. Teams collect the wrong evidence, owners prepare for controls that are not under review, and key systems get missed until fieldwork is already underway. A clear scope gives the audit a fixed reference point and keeps control mapping tied to the parts of the business the report will actually cover.
2. Run A Gap Assessment
A gap assessment compares the framework requirements to the controls your organization has today. Some controls will be implemented and operating as expected. Others will exist only in policy form, lack evidence, or rely on informal habits that will not hold up in testing.
This review should separate cosmetic readiness from actual readiness. A control is not ready just because a document exists or a tool is turned on. The team needs to know where ownership is missing, where evidence is weak, and where control performance has never been tested. That gives remediation work a clear order and keeps the audit from exposing issues the organization could have addressed earlier.
3. Assign Control Owners
An audit exposes ownership gaps quickly. Each control should have a named owner, a reviewer where needed, and a clear source for the evidence that supports testing. That includes policy approvals, access reviews, change records, training records, and technical outputs tied to the control.
Shared responsibility is common. Unclear responsibility is a problem. Security, IT, HR, engineering, and legal may all touch the same control set, but one person still needs to answer for execution and evidence. Without that structure, tasks slip, reviews get missed, and the team spends fieldwork sorting out who was supposed to do what.
4. Document Policies And Procedures
Policies and procedures give the control environment a written baseline. They should cover the areas the audit will test, such as access control, incident response, vendor management, risk management, and data handling, and they should reflect the way the company actually operates.
A document that is outdated, copied from a template, or disconnected from practice creates audit risk instead of reducing it. Auditors will compare the written procedure to system settings, tickets, approvals, and interviews. When those do not line up, the weakness is easy to spot. Good documentation is current, specific enough to follow, approved by the right authority, and supported by records that show the procedure is being carried out.
5. Implement And Test Key Controls
This is where audit readiness stops being a paperwork exercise and starts showing up in real operations. Your team needs the core controls in place across accounts, devices, systems, and daily workflows, then needs to confirm those controls are working the way the policy says they should.
MFA, access reviews, logging, backups, endpoint protection, and change controls matter here because weak execution is where audits start to break down. Microsoft says MFA can block more than 99% of account compromise attacks, which shows why core access controls need to be active, tested, and backed with real evidence.
6. Collect And Organize Evidence
The point is not to accumulate files. The record needs to show that the control operated during the period under review, that the activity was completed by the right person, and that any required review or approval took place. Well-organized evidence reduces follow-up requests and gives the auditor a cleaner basis for testing.
7. Continuous Monitoring And Improvement
Audit readiness starts to slip when controls stop getting checked after the initial setup is done. Continuous compliance keeps your team close to what is happening across systems, access, evidence, and everyday security work, which makes it easier to catch broken controls, stale records, missed reviews, and new risks before they turn into audit findings.
That ongoing visibility has real security value as well. IBM reported that organizations with high levels of security AI and automation identified and contained breaches an average of 98 days faster than organizations without them, which goes to show why continuous monitoring needs to stay active long after the audit prep phase ends.
What Are the Best Practices for Audit Readiness?
Audit readiness requires consistent control execution, clear ownership, and well-maintained evidence across the organization. The following are the key best practices that support effective audit readiness:
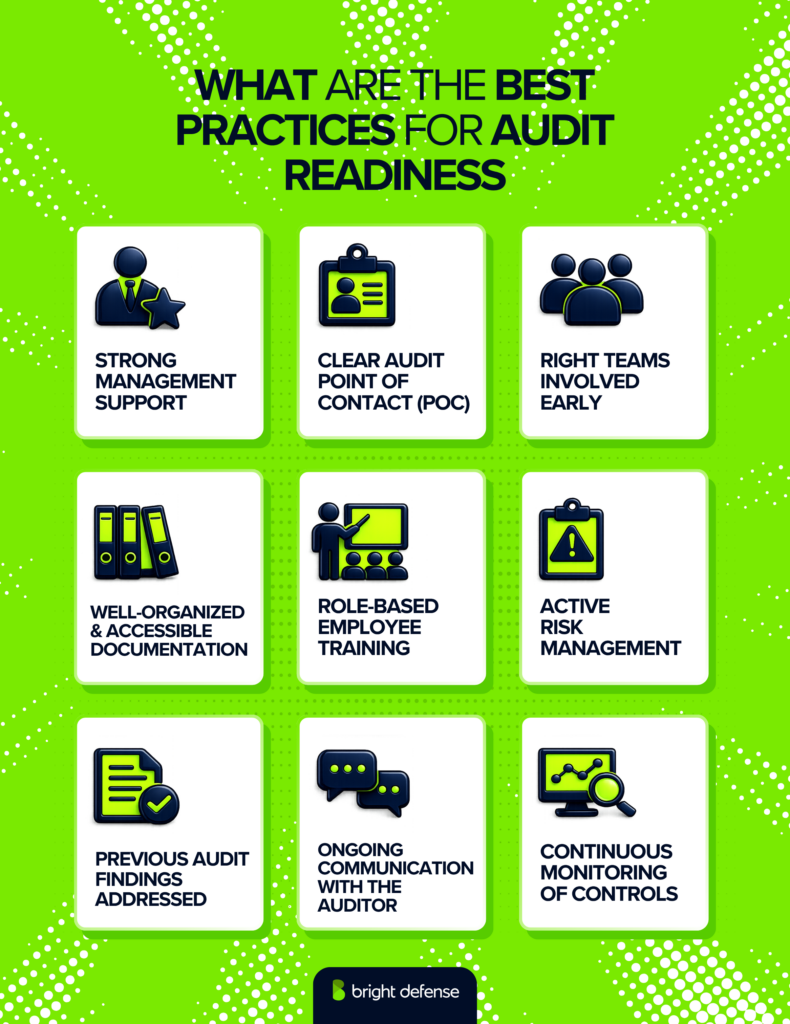
1. Strong Management Support
Audit readiness gets harder when leadership treats it as a side task. Management decides whether control owners have time on their calendars, whether remediation work gets funded, and whether control failures are escalated and resolved on schedule.
Leadership involvement changes the way the audit operates long before fieldwork starts. Teams respond to requests faster when priorities are clear, control owners complete reviews on time, and unresolved issues do not sit in a backlog waiting for approval or budget.
Evidence collection is more consistent, remediation moves earlier in the cycle, and audit meetings spend less time chasing overdue actions or explaining why the same gap is still open.
2. Clear Audit Point of Contact (POC)
A clear audit point of contact keeps requests, evidence, and scheduling under control. One person should own auditor communication, maintain the request list, route questions to the right internal teams, and track what is still outstanding.
The POC does not need to be the subject matter expert for every control. The role is to keep responses consistent, pull in the right owners at the right time, and stop the audit from fragmenting into separate conversations across security, IT, HR, and engineering.
Without that structure, duplicate requests pile up, deadlines get missed, and different teams give conflicting answers to the same question.
3. Right Teams Involved Early
Audit prep gets slower when the wrong people answer control questions or the right people join too late. Security, IT, HR, engineering, legal, and operations should be pulled in early where they own part of the process, the system, or the evidence tied to the audit.
Late involvement usually shows up in walkthroughs. Someone gives a partial answer, misses a system change, or points the auditor to the wrong record set. The meeting has to be repeated, more people get added, and fieldwork expands beyond the original request list.
4. Well-Organized & Accessible Documentation
Disorganized documentation slows fieldwork almost immediately. Policies, approvals, screenshots, logs, training records, and review evidence should sit in a single repository with a naming structure that makes each item easy to match to the control it supports.
Auditors should be able to review records before a walkthrough instead of waiting while the team searches inboxes, chat threads, and shared drives.
A well-kept repository shortens request turnaround, reduces repeat follow-ups, and gives the audit team a cleaner basis for testing.
5. Role-Based Employee Training
Employees need training that matches the decisions they make in their actual role. Someone handling customer data needs instruction on data handling and retention.
Someone with privileged access needs instruction on access control, approval requirements, and account hygiene. Staff across the company should know how to spot phishing attempts and how to report security incidents through the right process.
An auditor will look for more than a policy acknowledgment. Training records should show who completed the training, when it was assigned, when it was completed, and what topic was covered. Role-based assignments, completion logs, and periodic refreshers are stronger evidence than a generic annual session applied the same way to every employee.
6. Active Risk Management
Threats do not wait for audit season, and your risk process cannot be something you dust off once a year. A maintained risk process should identify new issues as systems change, rank them against business impact, assign owners, and track remediation through closure.
Vendors, infrastructure changes, access exceptions, and control failures all need to feed into the same process so the risk picture reflects current operations instead of a stale snapshot.
An active risk register gives the audit team something concrete to work from. It shows which risks were identified during the review period, who owned them, what action was taken, and whether any exposure remained open.
That record supports control decisions, explains why remediation work was prioritized, and gives the auditor a clearer basis for testing how the organization manages risk in practice.
7. Previous Audit Findings Addressed
Open findings from a prior audit should not roll into the next one without a documented resolution. Repeated exceptions tell the auditor that remediation stalled, ownership was unclear, or the control never operated consistently in the first place.
A clean closeout process should show what went wrong, what changed, who approved the fix, and when the issue was considered resolved.
The stronger approach is to keep a corrective action log tied to each finding. Root cause, remediation steps, owner, due date, status, and supporting evidence should all be easy to trace.
During the next audit, that record shows the issue was addressed rather than discussed and deferred.
8. Ongoing Communication With the Auditor
An audit can go off track fast when a major change comes up too late. A new cloud environment can leave part of the review period tied to evidence from a system the team no longer uses.
A retired system can remove access to logs or screenshots the auditor expected to test. Process changes and team changes can shift who performed a control, how it was reviewed, and where the record now lives.
Keeping your auditor informed throughout the year gives both sides time to deal with those changes before fieldwork starts.
The audit plan can be adjusted, evidence can be preserved before it disappears, and testing can be scoped around the way the control actually operated during the period under review. Late disclosure usually leads to rework, missing support, and longer fieldwork.
9. Continuous Monitoring of Controls
An annual audit only tests a period in time. Control performance can drift long before the next audit starts, especially when access changes pile up, evidence collection slows down, or exceptions stay open without review.
Continuous monitoring should include specific checks on a schedule, such as quarterly access reviews, monthly evidence reviews for key controls, and regular tracking of unresolved exceptions.
The point is to catch control failures while the team can still correct them inside the review period. A steady monitoring cadence produces current evidence, cleaner exception records, and fewer control gaps for the auditor to uncover during the next round of testing.
Common Audit Readiness Pitfalls to Avoid
Most audit readiness failures come from weak processes, unclear ownership, and messy documentation, not technical issues. The five pitfalls below show up often during SOC 2 fieldwork and are usually fixable before the audit starts.
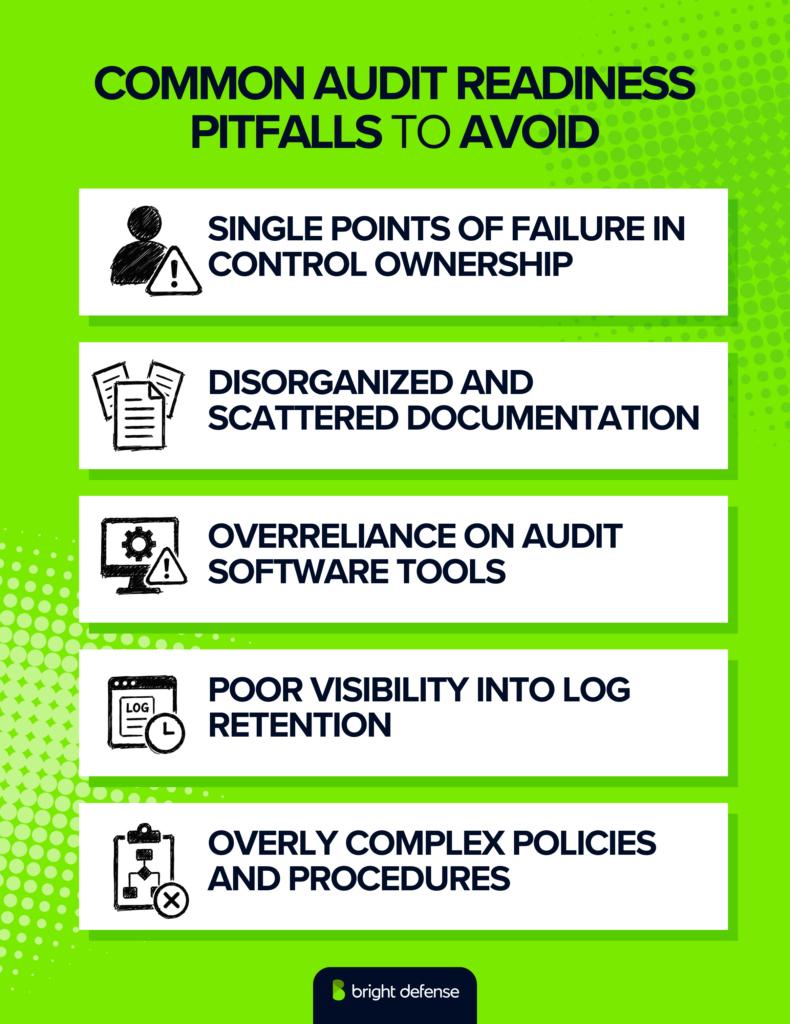
1. Single Points of Failure in Control Ownership
One person should never be the only person holding a control together. That setup looks fine until they leave, go on vacation, change roles, or simply forget where something was saved. Then the team is left saying the control probably happened but cannot prove it.
That is where audits start to get uncomfortable. Evidence needs backup ownership, clear storage, and enough continuity that the control still holds up when one person is out of the picture. Inquiry alone is not sufficient audit evidence for a control conclusion, which is exactly why memory and verbal reassurance do not save a weak process.
2. Disorganized and Scattered Documentation
Nothing drags an audit down faster than a live scavenger hunt. When teams start searching Slack threads, inboxes, and old folders during a walkthrough, the auditor sees the same problem right away: the control may exist, but the evidence process does not.
Good documentation should be easy to pull, easy to understand, and easy to match to the control it supports. That keeps requests moving, cuts repeat meetings, and gives the audit a cleaner path from start to finish.
3. Overreliance on Audit Software Tools
Audit software can speed up collection, tracking, and reporting. It cannot replace judgment. Tools only test what they are configured to test, and they only surface what the team has connected, mapped, and maintained correctly.
That is where companies get overconfident.
A dashboard can look healthy while a control is weak in practice or a key exception is sitting outside the tool’s view. The safer approach is simple: use software to reduce manual work, then use human review to catch what automation misses.
Audit standards take the same position in substance, requiring auditors to evaluate whether information used as evidence is accurate, complete, reliable, and detailed enough for the purpose.
4. Poor Visibility Into Log Retention
Log retention gaps can create audit problems long before anyone notices them. A team may think it can prove timely access removal or system activity across the full audit period, then realize halfway through fieldwork that the logs no longer go back far enough.
Google Workspace is a good example. Google says Admin log events data and User log events data are generally retained for six months, not twelve, which can leave a gap for period-of-time audits unless the company stores evidence somewhere else.
The better move is to know your retention windows early and preserve key records outside the native tool when needed.
5. Overly Complex Policies and Procedures
A policy does not help much when nobody wants to read it. Dense language, bloated steps, and overly rigid requirements tend to sit on a shelf while real work moves in a different direction. That is where inconsistency starts.
Strong policies are clear, relevant, and realistic enough that people can follow them in day-to-day work without guessing what the rule actually means. Keep them updated, keep them usable, and keep them tied to how the business really operates.
Common Cybersecurity Frameworks And Standards
Most compliance audits follow a recognized framework, and the right one depends on your industry, the data you handle, and what customers expect to see.
- SOC 2 is a common choice for cloud service providers and focuses on security, availability, processing integrity, confidentiality, and privacy. The audit is performed by a licensed CPA firm.
- ISO 27001 is an international standard for building and maintaining an information security management system. It works across many industries and is often used by companies that want a widely recognized security framework.
- HIPAA applies to healthcare organizations and any business that handles protected health information. It sets rules for protecting sensitive patient data.
- NIST frameworks give organizations a structured way to manage cybersecurity risk through defined controls and best practices.
The right framework depends on your business model, your data, and your compliance goals. A Bright Defense audit readiness assessment can help your team choose the right one and build a clear plan around it.
Continuous Compliance: Elevating Audit Readiness Through Automation
Continuous compliance moves beyond the traditional, periodic audit preparation process to a dynamic, ongoing strategy that integrates compliance into every aspect of an organization’s operations. This proactive approach ensures that a company is always audit-ready, not just when an audit is imminent.
Continuous compliance leverages automation technologies to streamline and enforce compliance processes, making it easier for organizations to stay ahead of regulatory changes and emerging cybersecurity threats. By adopting continuous compliance, companies can turn the challenge of compliance into a strategic advantage.
Advantages of Continuous Compliance
- Enhanced Security Posture: Continuous compliance means constant vigilance. By regularly monitoring and updating security measures, organizations can quickly adapt to new threats, reducing the risk of breaches and enhancing overall security.
- Reduced Compliance Costs: Automation of compliance tasks decreases the need for manual labor, cutting down on the costs associated with compliance management. It allows organizations to allocate resources more efficiently, focusing on growth and innovation.
- Streamlined Audit Preparation: With compliance processes integrated into daily operations and automated evidence collection, companies can significantly reduce the time and effort required for audit preparation. This not only eases the audit process but also minimizes disruptions to business operations.
- Improved Compliance Accuracy: Automation reduces the risk of human error in compliance tasks, leading to more accurate and reliable compliance processes. This accuracy is critical for meeting regulatory standards and avoiding penalties.
- Increased Agility: Continuous compliance enables companies to respond more swiftly to regulatory changes. Automation tools can be quickly updated to reflect new compliance requirements, ensuring the company remains in compliance without costly delays.
- Strengthened Stakeholder Trust: A commitment to continuous compliance demonstrates to customers, investors, and partners that the company prioritizes data protection and regulatory adherence. This can enhance reputation and build trust.
Bright Defense: Your Pathway to Enhanced Audit Readiness
If you are ready to begin your compliance journey, Bright Defense can help. Our monthly engagement model delivers a robust cybersecurity program designed to meet compliance frameworks including SOC 2, ISO 27001, NIST, HIPAA and CMMC. We combine our expertise with compliance automation to increase audit readiness and ensure a smooth audit.
In addition to continuous compliance, we offer vCISO services, security assessments, vulnerability management, and managed security awareness training. This makes Bright Defense the optimal partner for your entire compliance journey.
Contact Bright Defense to get started today!

FAQ
Audit readiness refers to an organization’s state of being fully prepared for a compliance audit, ensuring that all its business processes, controls, and documentation meet the required standards and best practices. It involves a proactive approach to align all aspects of the organization with the audit’s objectives.
An audit readiness assessment is a comprehensive review of your organization’s current practices against the audit objectives and requirements. This involves evaluating key processes, internal controls, and supporting documentation to identify gaps and areas for improvement. Focus on aligning your information security policy and business processes with the expected standards.
Communication is key. Regular meetings, updates, and shared resources help ensure everyone understands the audit objectives, timelines, and roles. Providing clear and concise documentation of key processes and controls can also aid in keeping the audit team and stakeholders aligned.
Risk management is a critical component of audit readiness. By identifying, assessing, and managing risks associated with your business processes and information security, you can prioritize areas that need attention and ensure that your organization is focusing on the right aspects to mitigate potential audit findings.
Prepare documents that clearly outline your internal controls, policies, and procedures. This includes your information security policy, process flowcharts, control descriptions, and evidence of controls in action (e.g., logs, reports). Make sure to review and update these documents regularly to reflect current practices.
The main difference between internal and external audits lies in their purpose and who conducts them. Internal auditors are employees of the organization, focusing on evaluating the efficiency of risk management, control, and governance processes, including accounting processes. Their goal is to identify improvements across various areas to help the organization meet its objectives. External auditors, on the other hand, are independent professionals from accounting firms, tasked with verifying the accuracy of financial statements and ensuring compliance with legal standards. While internal audits aim to enhance internal operations and controls, external audits provide stakeholders with assurance about the organization’s financial integrity.
Get In Touch