Updated:
June 28, 2025
CMMC Readiness Guide
The Cybersecurity Maturity Model Certification (CMMC) is no longer optional for contractors in the Defense Industrial Base.
With over 300,000 organizations in the U.S. defense supply chain affected, the pressure to meet CMMC requirements has intensified.
In fact, a study released in October 2024 by CyberSheath and Merrill Research found that only 4% of surveyed Department of Defense (DoD) contractors believed they were ready for CMMC certification.
The stakes are high. Failing to prepare can lead to disqualification from government contracts, loss of revenue, and significant reputational damage.
At the same time, the complexity of the requirements, especially for organizations juggling IT modernization, and resource constraints, can make preparation feel overwhelming.
This guide breaks down what readiness means under CMMC 2.0, what actions to prioritize based on your desired maturity level, and how to avoid common pitfalls that delay certification.
Let’s dive right in!
A Brief Overview of CMMC 2.0
CMMC 2.0 is the Department of Defense’s updated framework for securing the Defense Industrial Base. It replaces the original five-level model with three clearer levels, each based on existing federal standards.
Level 1 applies to contractors handling only Federal Contract Information and requires 17 basic security practices. These are verified through annual self-assessments. Level 2 is for contractors working with Controlled Unclassified Information.
It requires all 110 controls from NIST SP 800-171. Some contractors at this level will self-assess, while others must pass third-party audits. Level 3 covers work involving highly sensitive information. It builds on NIST SP 800-171 with added practices from NIST SP 800-172. DoD officials will conduct assessments for this level.
CMMC 2.0 eliminates process maturity requirements and focuses strictly on technical implementation. It also reduces the burden for lower-risk contractors through self-assessment options. The rule is still in progress, and CMMC requirements will not appear in contracts until the rulemaking process finishes.
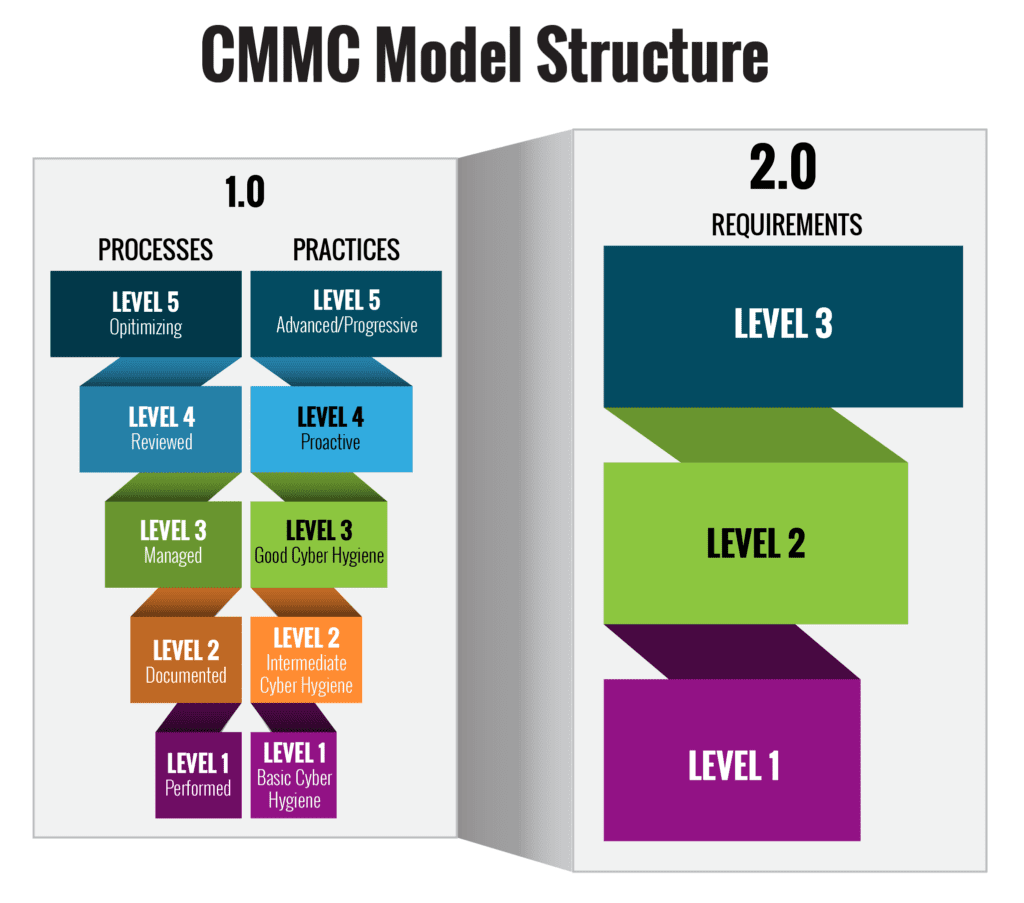
| Category | CMMC 1.0 | CMMC 2.0 |
|---|---|---|
| Model Type | Five levels with both processes and practices | Three levels based only on practices |
| Level 1 | Basic Cyber Hygiene; 17 practices (FAR 52.204-21) | Same as CMMC 1.0 Level 1 |
| Level 2 | Intermediate Cyber Hygiene; a transition step | Equivalent to CMMC 1.0 Level 3; 110 NIST SP 800-171 controls |
| Level 3 | Good Cyber Hygiene; 110 practices (NIST SP 800-171) | Equivalent to CMMC 1.0 Level 5; includes selected NIST SP 800-172 practices |
| Level 4 & 5 | Added maturity processes; focused on advanced threat protection | Removed from the model |
| Assessment Type | Third-party certification required for all levels | Mix of self-assessments and third-party audits, based on level and contract |
| Focus | Implementation and process maturity | Focused strictly on implementation |
CMMC Complicance From Bright Defense
Steps to Achieve CMMC Readiness
Here are 7 key steps that can help you achieve CMMC readiness fast:
Step 1: Understand CMMC Level 1 Requirements:
At Bright Defense, we focus our CMMC readiness audits on evaluating current cybersecurity practices, identifying gaps in compliance, and remediating the gaps until all CMMC controls are fully met. We then test the controls continuously to ensure year-round compliance.
To get started with CMMC Readiness, organizations should understand the 15 basic safeguarding requirements of FAR 52.204-21 and the 17 CMMC practices required for CMMC Level 1 compliance.
FAR 52.204-21 outlines the basic safeguarding requirements for protecting Federal Contract Information (FCI) in contractor information systems. Here’s a summarized list of the 17 CMMC practices for basic safeguarding.
17 CMMC Best Practices
- Limit Information System Access: Only authorized users can access the system.
- Authenticate Users: Verify the identity of users, processes, or devices before allowing access.
- Sanitize or Destroy Information System Media: Ensure that data is irretrievably deleted before disposal or reuse.
- Monitor and Control Communications: Control information transfers between the system and external systems or networks.
- Limit Physical Access: Restrict authorized individuals’ physical access to information systems, equipment, and operating environments.
- Escort Visitors: Monitor and escort visitors to areas where information systems operate.
- Maintain Audit Logs: Review system activity records, including network usage and user actions.
- Use Session Locks: Implement session locks for system sessions after a defined period of inactivity.
- Regularly Update System: Periodically update system, components, software, and firmware.
- Configure System Properly: Ensure the system is protected from malicious code at appropriate locations.
- Protect and Monitor Boundaries: Monitor and control communications at the system’s external and key internal boundaries.
- Use Strong and Unique Identifiers: Employ strong, unique identifiers for system users.
- Authenticate or Verify Identities: Authenticate the identity of those who receive system information.
- Protect FCI from Public Release: Prevent unauthorized public disclosure of FCI.
- Quickly Report Incidents: Report any security incidents, including potential threats, to the appropriate authorities.
- Use Strong Identifiers: Employ strong, unique identifiers for system users.
- Report Incidents: Report any security incidents to the appropriate authorities on time.
These requirements provide a foundational level of security to safeguard Federal Contract Information within contractor information systems, ensuring that sensitive data remains protected from potential threats.
Step 2: Prepare your Employees

With any cybersecurity program implementation, it’s important that the owners, board of directors, and executive leaders are fully bought into and championing the program for success. Employees are the biggest risk when it comes to cybersecurity.
It is crucial that employees follow regular and consistent Cybersecurity Awareness Training along with understanding what CMMC is, why they should care, and how to follow the new policies and procedures that will be implemented for the organization to meet compliance.
Be sure to provide employees with additional resources or point them in the right direction if they want to learn more beyond your training.
Step 3: Implement a System Security Plan (SSP)
A System Security Plan is required under CMMC and functions as your cybersecurity roadmap. It outlines your current security practices, identifies areas for improvement, and sets timelines for addressing gaps. It helps communicate your approach both internally and to the Department of Defense.
The SSP must be kept up to date and should explain how your organization meets each control in the CMMC framework. A well-maintained plan shows that your team takes cybersecurity seriously and is working consistently to improve it.
Step 4: Put Protections in Place for Controlled Unclassified Information (CUI)
To meet CMMC requirements, you need clear safeguards around all systems handling CUI. These include formal policies and procedures, physical access controls, and technical defenses such as firewalls, encryption, and intrusion detection.
Protecting your CUI environment signals that your organization takes data security seriously and is prepared to meet the expectations set by the CMMC certification process.
Step 5: Documentation and Policies

Documentation and policies play a pivotal role in CMMC readiness. They are the backbone of an organization’s cybersecurity posture, providing a clear roadmap for implementing, maintaining, and improving security practices.
Well-documented policies ensure a standardized approach to security, reducing ambiguities and inconsistencies in executing practices.
They offer a reference point for training, audits, and assessments, making demonstrating compliance during CMMC evaluations easier. Furthermore, in the event of personnel changes or system upgrades, robust documentation ensures continuity, allowing new team members or systems to align seamlessly with established security protocols.
In essence, while technical measures are crucial for cybersecurity, the documentation and policies ensure these measures are consistently and effectively applied across the organization, solidifying its CMMC readiness.
A determination statement must be linked to each objective to ensure the documentation is updated and applies to the correct policy. Policies must be reviewed annually and sent to all employees for acknowledgment.
Step 6: Seeking External Assistance
Seeking External Assistance in the journey toward CMMC readiness can be a game-changer for many organizations. As the cybersecurity landscape evolves, achieving and maintaining compliance can be daunting. Recognizing when to bring in a consultant or external expert is crucial.
These professionals offer specialized knowledge, providing insights into best practices, potential vulnerabilities, and tailored solutions that might be overlooked internally. They can help navigate the CMMC framework’s intricacies, ensuring every stone is turned on.
Moreover, third-party assessments objectively evaluate an organization’s cybersecurity posture. Such assessments validate the organization’s efforts and identify areas of improvement, ensuring a comprehensive approach to CMMC readiness. While internal efforts lay the foundation, seeking external assistance brings in the expertise and objectivity needed to elevate an organization’s cybersecurity measures to the standards demanded by the CMMC.
Step 7: Put Vendor Risk Management into Practice
When outsourcing work to third parties, you must monitor and assess whether those vendors meet CMMC requirements. Vendor risk management involves reviewing their cybersecurity policies and practices to confirm they follow current data protection standards.
This assessment should not be a one-time task. Cyber threats and technologies change quickly, so a vendor that was secure last year may no longer meet your security expectations. Ongoing evaluations are necessary to maintain protection and stay compliant with CMMC standards.
Step 8: Implementing Required Practices
When planning for the implementation of the 17 CMMC Readiness Best Practices, it’s important to consider the following:

A. Access Control and User Authentication
Central to cybersecurity is ensuring that only authorized individuals have access to your systems. This means setting up robust user authentication protocols.
Organizations can significantly reduce the risk of unauthorized access by employing strong, unique identifiers for each user and verifying the identity of users or devices before granting access.
Regularly reviewing and updating access permissions ensures that only those who need access have it, and no more than that.
B. Physical Security Measures
While digital threats are a significant concern, physical security is equally crucial. Limiting physical access to system equipment and operational environments is fundamental.
This might involve secure access mechanisms like key cards, biometric access controls, or security personnel. Monitor visitors and escort them in sensitive areas to prevent inadvertent or deliberate physical breaches.
C. System Maintenance and Protection
Regularly updating systems, components, software, and firmware is essential to protect against vulnerabilities. Staying updated as cyber threats evolve ensures your protection against known threats.
Furthermore, proactive measures, such as implementing safeguards against malicious code and using session locks after periods of inactivity, can prevent potential breaches.
D. Monitoring and Reporting
Maintaining audit logs clearly records system activity. These logs can be invaluable in identifying suspicious activities or in forensic analysis after a security incident.
Moreover, having a protocol for reporting security incidents ensures timely response and mitigation, minimizing potential damage.
E. Data Handling and Disposal
To protect FCI from unauthorized public disclosure, remain vigilant not only in how you access and use data but also in how you dispose of it.
Properly sanitizing or destroying information system media ensures that sensitive data doesn’t fall into the wrong hands even at the end of its lifecycle.
Step 9: Preparing for the CMMC Audit

One of the significant changes in CMMC 2.0 is the introduction of self-assessments for Levels 1 and 2, allowing contractors to self-certify their compliance.
However, these self-assessments are subject to random audits by the CMMC Accreditation Body. Level 3 will still require a third-party assessment by C3PAOs to ensure the highest cybersecurity standards.
Preparing for a CMMC Level 1 audit requires a strategic blend of self-assessment, documentation, and proactive measures. At this foundational level, the focus is on ensuring basic cyber hygiene practices are in place to protect Federal Contract Information (FCI).
Organizations should begin by conducting a thorough self-assessment to identify gaps in their cybersecurity practices relative to the 17 requirements of Level 1.
Document every security measure, protocol, and procedure meticulously, providing auditors with a clear trail of evidence, as the documentation process is equally crucial. This demonstrates compliance and showcases the organization’s commitment to maintaining a consistent security posture.
Additionally, engaging in mock audits or seeking guidance from external experts can be beneficial, offering a fresh perspective and highlighting potential areas of concern.
To prepare for a CMMC Level 1 audit, ensure that foundational cybersecurity practices are implemented but also verifiable, consistent, and well-documented.
Step 10: Continuous Monitoring

It is vital that organizations take a continuous monitoring approach towards CMMC Readiness. While the program’s point is to protect FCI and CUI, it’s also vital to improving the organization’s cybersecurity posture. Bright Defense offers ongoing continuous compliance services for CMMC Levels 1 and 2.
About Bright Defense:
Discover the path to CMMC compliance with Bright Defense’s CMMC readiness services. Bright Defense protects our clients from cybersecurity threats through continuous compliance. As the cybersecurity landscape becomes increasingly intricate, our team of CISSP and CISA-certified experts is here to guide you every step of the way.
From comprehensive assessments to documentation support, we ensure that your organization is prepared and primed for success in the CMMC audit. With Bright Defense by your side, you’re not just achieving compliance. You are showcasing your unwavering commitment to cybersecurity excellence. Elevate your defense contracting game and secure your future with Bright Defense’s unparalleled CMMC readiness expertise.
Get started with Bright Defense today!
Contact Us
Get In Touch