Updated:
June 28, 2025
CMMC Controls for SMB Owners: A Guide to the 14 Controls
CMMC is moving closer to finalization, but many SMBs in the defense sector still face uncertainty about what steps to take and which controls to implement. If you work with the Department of Defense, you’re expected to meet specific cybersecurity standards that protect sensitive information across your systems.
CMMC defines multiple maturity levels, each with clear security requirements. These range from basic hygiene to advanced practices, depending on the risk level of the work you perform. The goal is simple: reduce the chances of cyber attacks and data breaches across the defense supply chain.
At the core of CMMC is NIST 800-171, a set of security requirements designed for non-federal systems that handle Controlled Unclassified Information (CUI). These guidelines form the foundation for many CMMC controls, especially at the higher levels. Understanding and applying them is essential for compliance.
This guide breaks down what you need to know about the 14 CMMC control families, focusing on what matters most for SMBs aiming to protect sensitive data and meet DoD requirements.
Understanding CMMC and NIST 800-171
The Cybersecurity Maturity Model Certification (CMMC) and NIST 800-171 are crucial frameworks in the defense industry, each playing a pivotal role in shaping the landscape of cybersecurity.
Explanation of CMMC
Here’s a breif explanation of the Cybersecurity Maturity Model Certification:
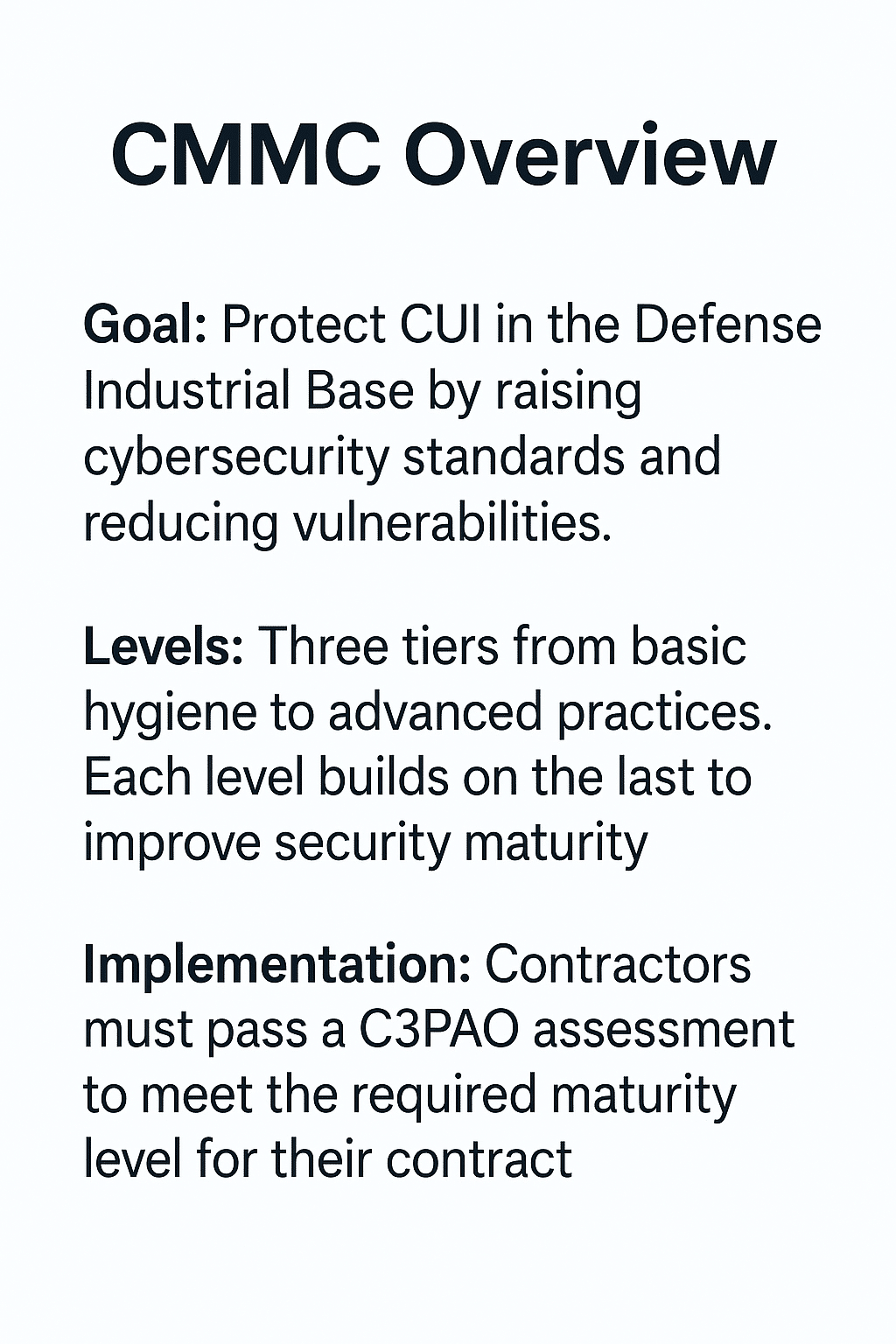
- Goals: The primary goal of CMMC is to enhance the protection of Controlled Unclassified Information (CUI) residing in the Defense Industrial Base (DIB). This is achieved by standardizing and elevating cybersecurity practices across the supply chain. CMMC aims to reduce vulnerabilities, making it more challenging for adversaries to compromise sensitive defense information.
- Levels: CMMC is structured across three maturity levels, each representing a step up in cybersecurity sophistication and robustness. Level 1 focuses on basic cyber hygiene, while Level 3 involves advanced and progressive cybersecurity practices. Each level comprises specific practices and processes that range from basic cyber hygiene to optimizing and standardizing these processes across the organization.
- Implementation: To comply with CMMC, defense contractors must undergo an assessment by a CMMC Third Party Assessment Organization (C3PAO). This ensures that the required level of cybersecurity maturity is met. The specific level required depends on the nature of the contract and the sensitivity of the information handled by the contractor.

Overview of NIST 800-171
A brief overview of NIST 800-171 is given below:
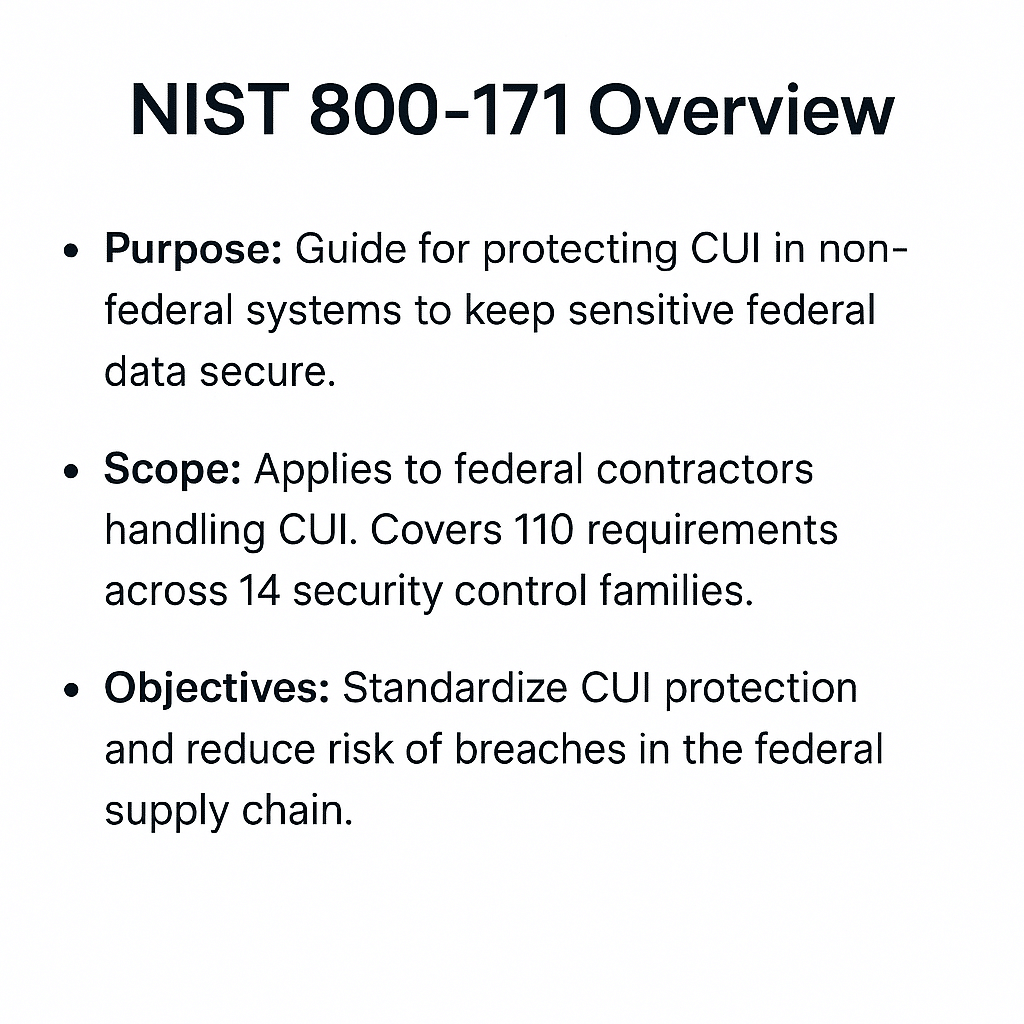
- Purpose: NIST 800-171 provides guidelines on protecting CUI in non-federal systems and organizations. Its main purpose is to safeguard sensitive federal information that is processed, stored, and transmitted in non-federal information systems and environments.
- Scope: The scope of NIST 800-171 is primarily focused on contractors and subcontractors working with the federal government who handle CUI. It outlines 110 security requirements spread across 14 families of security controls, including access control, incident response, and risk assessment.
- Objectives: The objectives of NIST 800-171 are to standardize the protection of CUI and improve the overall security posture of federal supply chains. It aims to reduce the risk of data breaches and cyber-attacks through comprehensive and consistent security measures.
Integration of NIST 800-171 into CMMC Framework
NIST 800-171 is intricately woven into the fabric of the CMMC framework. The practices and processes outlined in NIST 800-171 form the basis for many of the requirements in the CMMC controls, particularly at Levels 2 and 3, where protecting CUI is paramount.
This integration ensures a harmonized approach to cybersecurity, making it easier for defense contractors to understand and implement the necessary security controls. In essence, adhering to NIST 800-171 is not just about compliance; it’s about building a foundation upon which CMMC certification can be achieved, ensuring a comprehensive and robust cybersecurity posture.
Key CMMC Controls Derived from NIST 800-171
The NIST 800-171 standard, titled “Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations,” comprises 110 security requirements spread across 14 families of controls.
These controls are designed to protect Controlled Unclassified Information (CUI) in non-federal information systems and organizations. Here’s a brief overview of each control family and its purpose:
14 CMMC Controls from NIST 800-171
Implementing the NIST 800-171 controls effectively requires a thorough understanding of each control and adopting best practices tailored to your organization’s needs. Here’s a detailed look at the first five controls and strategies for their implementation:
Access Control – CMMC Control 1
- Details: Access control is about ensuring that users and devices have access only to the network and data necessary for their roles. This includes managing permissions, controlling remote access, and enforcing restrictions on the use of portable storage devices.
- Best Practices:
- Implement Role-Based Access Control (RBAC) to define roles and assign access rights accordingly.
- Utilize strong authentication methods, like multi-factor authentication (MFA), to verify user identities.
- Regularly review and update access permissions, especially when employees change roles or leave the organization.
- Use encryption for data in transit and at rest to protect sensitive information.
Awareness and Training – CMMC Control 2
- Details: This control emphasizes the importance of training staff to recognize and respond to security threats. Awareness programs should cover policy and procedure education, threat identification, and safe computing practices.
- Best Practices:
- Develop comprehensive training programs that are updated regularly to reflect the latest security threats and best practices.
- Conduct regular security awareness sessions and phishing simulation exercises.
- Include cybersecurity training as part of the onboarding process for new employees.
- Keep records of training sessions and ensure all employees, including contractors, participate.
Audit and Accountability – CMMC Control 3
- Details: This involves creating and maintaining records of system activity and enabling the tracking of user actions. It’s crucial for detecting anomalies, investigating incidents, and enforcing accountability.
- Best Practices:
- Implement a robust log management system that collects, monitors, and analyzes audit logs.
- Define clear audit log retention policies based on legal and business requirements.
- Regularly review and analyze logs for suspicious activities.
- Ensure that the logs are secure, tamper-proof, and only accessible to authorized personnel.
Configuration Management – CMMC Control 4
- Details: Configuration management requires the establishment and maintenance of baselines for system configurations that enhance security. This includes controlling changes and documenting configurations.
- Best Practices:
- Develop and maintain a secure baseline configuration for all systems.
- Use configuration management tools to track changes and ensure systems are consistently configured.
- Regularly update systems and software to patch vulnerabilities.
- Conduct periodic security assessments to ensure configurations are still in compliance with policy.
Identification and Authentication – CMMC Control 5
- Details: This control mandates the verification of user, process, or device identities before granting access to organizational systems.
- Best Practices:
- Implement strong, unique passwords along with MFA for an additional layer of security.
- Use digital certificates or biometric authentication for critical systems.
- Regularly audit user accounts and authentication systems to detect any anomalies.
- Ensure session controls are in place to automatically log users out after periods of inactivity.
Incident Response – CMMC Control 6
- Details: This control requires organizations to establish and follow a formal incident response process, including preparation, detection, analysis, containment, recovery, and post-incident activities.
- Best Practices:
- Develop and document an incident response plan that includes roles, responsibilities, and procedures.
- Train staff to recognize and respond to security incidents effectively.
- Regularly test and update the incident response plan to ensure its effectiveness.
- Implement an incident tracking system to document and manage incident details.
Maintenance – CMMC Control 7
- Details: This control focuses on regular maintenance of systems to ensure continued security and operational integrity.
- Best Practices:
- Schedule regular maintenance activities and ensure they are performed by authorized personnel.
- Document all maintenance activities, including changes or updates made.
- Ensure maintenance tools are examined for malicious code before use.
- Monitor system performance post-maintenance to ensure no security features have been compromised.
Media Protection – CMMC Control 8
- Details: This involves protecting both digital and non-digital media (e.g., paper records, USB drives) that contain CUI.
- Best Practices:
- Implement access controls to restrict media access to authorized individuals.
- Use encryption to protect data on portable media.
- Establish procedures for secure media storage, transport, and disposal.
- Conduct regular audits to account for all media containing CUI.
Personnel Security – CMMC Control 9
- Details: This control ensures that individuals who have access to CUI are reliable and meet security criteria.
- Best Practices:
- Conduct background checks as part of the hiring process.
- Provide ongoing security awareness and training.
- Implement a process to revoke access when an individual’s employment is terminated or when changes in their role no longer require access to CUI.
Physical Protection – CMMC Control 10
- Details: This control focuses on protecting physical premises and equipment from unauthorized access and environmental hazards.
- Best Practices:
- Implement physical access controls (like keycards or biometric scanners) to limit access to facilities.
- Use surveillance equipment and alarm systems for monitoring.
- Ensure critical equipment is located in secure areas with environmental controls.
- Develop procedures for responding to physical security incidents
Risk Assessment – CMMC Control 11
- Details: Requires conducting regular risk assessments to identify vulnerabilities in organizational operations and assets.
- Best Practices:
- Conduct periodic risk assessments to identify and evaluate risks.
- Use the results to update security policies, procedures, and controls.
- Involve stakeholders from different departments in the risk assessment process.
- Keep a documented record of all risk assessment activities and findings.
Security Assessment – CMMC Control 12
- Details: Involves regularly assessing security controls to determine their effectiveness.
- Best Practices:
- Develop and implement a security control assessment plan.
- Conduct assessments at planned intervals or when significant changes occur.
- Use the results to address any deficiencies and improve security controls.
- Document all assessment processes and results for accountability.
System and Communications Protection – CMMC Control 13
- Details: Requires implementing measures to protect information systems and ensure the security of data in transit and at rest.
- Best Practices:
- Use firewalls, intrusion detection/prevention systems, and encryption to protect networked communications.
- Implement secure communication protocols like HTTPS, SSH, or VPNs.
- Regularly update and patch network devices and systems.
- Monitor network traffic for unusual activity.
System and Information Integrity – CMMC Control 14
- Details: Focuses on protecting systems from malware and unauthorized changes, and ensuring data integrity.
- Best Practices:
- Implement and regularly update anti-malware software.
- Use file integrity monitoring tools to detect unauthorized changes.
- Implement error detection and correction methods for data.
- Regularly conduct system scans and reviews to detect anomalies.
Implementing these controls requires a combination of technology, processes, and people. It’s important to continuously monitor, review, and update your security practices to adapt to new threats and changes in the environment.
Tools and Resources CMMC Controls Implementation
The implementation of Cybersecurity Maturity Model Certification (CMMC) controls in organizations, especially those involved in defense contracting, is a critical step towards ensuring compliance and enhancing cybersecurity posture. Here’s an overview of the best practices and tools necessary for effective implementation:

Tools and Resources for Effective Implementation
- Automated Compliance Software: Tools like compliance management platforms can automate the tracking of your compliance status and help manage documentation and reporting.
- Cybersecurity Frameworks and Checklists: Utilize frameworks like NIST’s Cybersecurity Framework and CMMC checklists to guide your implementation process.
- Security Information and Event Management (SIEM) Systems: SIEM systems provide real-time analysis and reporting of security alerts generated by applications and network hardware.
- Vulnerability Assessment Tools: Regularly use these tools to scan your systems for vulnerabilities. Addressing these vulnerabilities promptly is essential for maintaining security.
- Data Encryption Solutions: Encrypt sensitive data both at rest and in transit to protect it from unauthorized access.
- Incident Response Management Tools: These tools help in effectively managing and responding to cybersecurity incidents, thereby reducing the impact of any breaches.
- Engage a CMMC Registered Practitioner: These experts are trained and certified by CyberAB to help SMBs implement the controls required by CMMC from Level 1 to Level 2.
Implementing CMMC controls requires a strategic approach, commitment from all levels of the organization, and the right set of tools and practices. By following these best practices and utilizing effective tools, organizations can not only achieve compliance but also significantly enhance their overall cybersecurity resilience.
Conclusion: Emphasizing the Critical Role of CMMC and NIST 800-171
As we conclude, it’s imperative to revisit and underscore the vital importance of the Cybersecurity Maturity Model Certification (CMMC) and NIST 800-171 in the landscape of modern cybersecurity, particularly within the defense sector.
Recap of the Importance of CMMC and NIST 800-171
The CMMC framework serves as a cornerstone in safeguarding the defense industrial base, mandating a standardized level of cybersecurity across all defense contractors. This certification ensures that sensitive information, integral to national security, is protected against increasingly sophisticated cyber threats.
NIST 800-171 complements CMMC by providing detailed guidelines for the protection of Controlled Unclassified Information (CUI) in non-federal systems and organizations. Its incorporation into the CMMC model harmonizes efforts to secure data and fortify cybersecurity infrastructures.
Final Thoughts on the Role of These Frameworks in Enhancing Cybersecurity
Together, CMMC and NIST 800-171 form a robust framework that not only elevates the cybersecurity standards but also instills a culture of continuous security improvement and vigilance. They address both technical and procedural aspects of cybersecurity, ensuring a comprehensive approach to data protection.
For defense contractors, compliance with these frameworks is not just about adhering to regulations; it’s a strategic investment in their cybersecurity resilience. This commitment significantly reduces vulnerabilities, thereby safeguarding not just their own interests but also those of the national defense ecosystem.
Bright Defense Provides CMMC Consulting and Advisory Services
- It’s crucial for organizations, especially those within the defense sector, to take proactive steps in assessing their current cybersecurity posture in relation to CMMC and NIST 800-171 standards.
- Engage in a thorough gap analysis to identify areas of improvement, and develop a strategic plan to address any deficiencies. This may involve updating policies, investing in new technologies, or enhancing employee training programs.
- Consider partnering with cybersecurity experts like Bright Defense and utilizing compliance software tools such as Drata to streamline the process and ensure a thorough and accurate assessment.
- Remember, achieving and maintaining compliance is an ongoing process. Regular reviews and updates to your cybersecurity practices are essential to stay aligned with the evolving nature of cyber threats and regulatory requirements, that is why Bright Defense offers Continuous Compliance services to help SMB owners achieve this.
Get In Touch