Updated:
May 7, 2026
CMMC Level 1- The First Step in Cybersecurity Maturity
If your company works with the US Department of Defense, you need to meet CMMC Level 1 requirements to handle Federal Contract Information. More than 300000 businesses are in this position.
CMMC Level 1 covers basic cyber hygiene. It includes simple but critical practices like access control and device protection to block common threats. These requirements apply to all contractors, especially small and mid-sized firms.
This article explains what CMMC Level 1 is, why it matters, how to get compliant, and what the current rollout timeline looks like. For Level 2 guidance, see our step-by-step strategy guide.
What Is CMMC?
CMMC is a set of cybersecurity requirements for companies that want to work with the US Department of Defense. If your business handles Federal Contract Information (FCI) or wants to bid on DoD contracts, you need to meet at least CMMC Level 1.
Level 1 includes basic practices to protect FCI from common threats. These are required for all prime and subcontractors who touch government data, even if they don’t handle classified material.
Overview of CMMC Level 1: Basic Cyber Hygiene
CMMC Level 1 represents the entry point within the revised three-tiered CMMC framework. It focuses specifically on the protection of FCI.
For business owners, achieving Level 1 certification is the first step towards qualifying for DoD contracts that involve handling less sensitive data. CMMC Level 1, known as “Basic Cyber Hygiene,” establishes the foundation of the comprehensive framework.
It consists of 17 practices and 14 controls. These practices are the crucial minimum measures for effectively safeguarding sensitive defense information.
As the first step in the CMMC hierarchy, Level 1 plays a vital role in foundational cybersecurity, setting the stage for more advanced measures and preparing contractors for higher CMMC levels.
It’s particularly vital for small and medium-sized businesses entering the defense supply chain, offering a manageable starting point to build a robust cybersecurity framework.
The Three Proposed Levels of CMMC
The 3 different levels of CMMC includes:
- CMMC Level 1 – Foundational: This level focuses on basic cyber hygiene practices to protect Federal Contract Information (FCI). It establishes fundamental cybersecurity controls that are essential for all contractors within the DIB.
- CMMC Level 2 – Advanced: Aimed at safeguarding Controlled Unclassified Information (CUI), this intermediate level enhances the basic cyber hygiene from Level 1 with more sophisticated cybersecurity practices and processes.
- CMMC Level 3 – Expert: Designed for organizations managing highly sensitive defense information, this highest level demands the strictest cybersecurity measures, encompassing a comprehensive and proactive cybersecurity program.
CMMC Rule Making Process and Current Timeline
The CMMC framework is currently going through the federal rule-making process. This includes a period for public comments and a finalization phase before the rules are enforced. At the time of writing, the Department of Defense is working to finalize CMMC 2.0.
Contractors should begin updating their cybersecurity practices to match the proposed requirements, even while the process is still underway. Waiting until the rules are finalized could put contracts at risk.
CMMC Timeline Highlights
- November 2021: CMMC 2.0, a revised and streamlined version of the original model, is announced with an estimated rulemaking timeframe of 9-24 months.
- March 2023: The DoD submits the proposed CMMC rule to the Office of Management and Budget (OMB) for regulatory review.
- November 2023: The regulatory review process concludes, paving the way for the rule’s publication.
- December 25, 2023: The proposed CMMC rule is published in the Federal Register, triggering a 60-day public comment period.
- Early 2024: (Tentative) The DoD addresses public comments and issues a final CMMC rule.
- Q1 2025: (Estimated) CMMC requirements begin appearing in new DoD contracts.
Next Steps
As the DoD prepares to release the proposed rule soon, stakeholders should actively analyze its specifics and prepare to offer thoughtful feedback during the public comment period.
The DoD will consider this feedback to refine the rule before issuing its final version. Once finalized, the DoD will gradually incorporate CMMC requirements into new contracts, expecting a phased implementation over several years.
To get the latest information on CMMC timelines, you can check a few key sources:
- Official CMMC Accreditation Body Website: This site often contains the most accurate and up-to-date information regarding CMMC implementation phases, training, and certification timelines.
- U.S. Department of Defense (DoD) Website: Look for press releases, updates, and official guidelines regarding CMMC on the DoD’s official website or specific pages dedicated to cybersecurity and defense contracting.
- Industry Publications and News Sites: Websites like FedScoop and Defense News often report on updates to government contracting requirements and frameworks like CMMC.
- Webinars and Conferences: Many cybersecurity and defense contracting conferences discuss CMMC. Attending these or viewing recorded sessions can provide insights into current expectations and future roadmap plans.

Detailed Analysis of CMMC Level 1
CMMC Level 1, often referred to as “Basic Cyber Hygiene,” is the foundational tier in the Cybersecurity Maturity Model Certification framework. It’s designed to safeguard Federal Contract Information (FCI) within the networks of the Defense Industrial Base (DIB). This level is crucial for establishing a baseline of cybersecurity practices that are essential for all contractors, especially those new to working with the Department of Defense (DoD).
Objectives of Level 1
- Protect FCI: The primary objective is to ensure the protection of Federal Contract Information, which is not intended for public release.
- Establish Basic Cybersecurity Hygiene: To inculcate fundamental cybersecurity practices and behaviors within the organization.
- Foundation for Higher Levels: Level 1 serves as a stepping stone for advancing to higher CMMC levels, with more stringent cybersecurity requirements.
Key Focus Areas
- Basic Cybersecurity Measures: Implementing essential security controls to protect against common cyber threats.
- User Awareness and Training: Educating employees about basic cybersecurity practices and potential cyber threats.
- Physical Security: Ensuring physical safeguards are in place to protect hardware and information systems.
What is FAR 52.204-21?
Achieving CMMC Level 1 compliance starts with implementing the 15 requirements of FAR 52.204-21, known as “Basic Safeguarding of Covered Contractor Information Systems,” is a clause within the Federal Acquisition Regulation (FAR). This clause is integral to the U.S. government’s efforts to ensure that contractors protect the confidentiality, integrity, and availability of information.
This applies directly to federal contractors and subcontractors dealing with Federal Contract Information (FCI), defined as information not meant for public release, either provided to or generated for the Government under a contract.
Key aspects of FAR 52.204-21 include:
- Scope: This clause applies to all contractors and subcontractors that process, store, or transmit Federal Contract Information. It sets out basic requirements for safeguarding that information within contractor information systems.
- Safeguarding Requirements: The clause outlines 15 specific security requirements for protecting FCI. These requirements are similar to those found in the NIST (National Institute of Standards and Technology) SP 800-171, but they are less comprehensive. They include measures for limiting information system access, ensuring secure authentication, monitoring, controlling, and protecting information transmitted or stored, and responding to incidents.
- Implementation: Contractors tasked with handling Federal Contract Information (FCI) must implement safeguards that correspond to the associated risk level. While this allows some flexibility in the application of these requirements, the key goal is to ensure adequate protection of FCI.
- Compliance: Adhering to FAR 52.204-21 is not optional but a mandatory compliance for these contractors. Often, it’s a prerequisite for securing federal contracts. Non-compliance could result in serious consequences, including penalties and potential loss of contracts.
The 15 requirements of FAR 52.204-21
The following is copied verbatim from https://www.acquisition.gov/far/52.204-21
- (i) Limit information system access to authorized users, processes acting on behalf of authorized users, or devices (including other information systems).
- (ii) Limit information system access to the types of transactions and functions that authorized users are permitted to execute.
- (iii) Verify and control/limit connections to and use of external information systems.
- (iv) Control information posted or processed on publicly accessible information systems.
- (v) Identify information system users, processes acting on behalf of users, or devices.
- (vi) Authenticate (or verify) the identities of those users, processes, or devices, as a prerequisite to allowing access to organizational information systems.
- (vii) Sanitize or destroy information system media containing Federal Contract Information before disposal or release for reuse.
- (viii) Limit physical access to organizational information systems, equipment, and the respective operating environments to authorized individuals.
- (ix) Escort visitors and monitor visitor activity; maintain audit logs of physical access; and control and manage physical access devices.
- (x) Monitor, control, and protect organizational communications (i.e., information transmitted or received by organizational information systems) at the external boundaries and key internal boundaries of the information systems.
- (xi) Implement subnetworks for publicly accessible system components that are physically or logically separated from internal networks.
- (xii) Identify, report, and correct information and information system flaws in a timely manner.
- (xiii) Provide protection from malicious code at appropriate locations within organizational information systems.
- (xiv) Update malicious code protection mechanisms when new releases are available.
- (xv) Perform periodic scans of the information system and real-time scans of files from external sources as files are downloaded, opened, or executed.

How to Prepare for CMMC Level 1?
Preparation is key to meeting CMMC Level 1 requirements without delays or surprises. The steps below will help you focus your efforts, avoid common mistakes, and move through the process with more clarity and control:
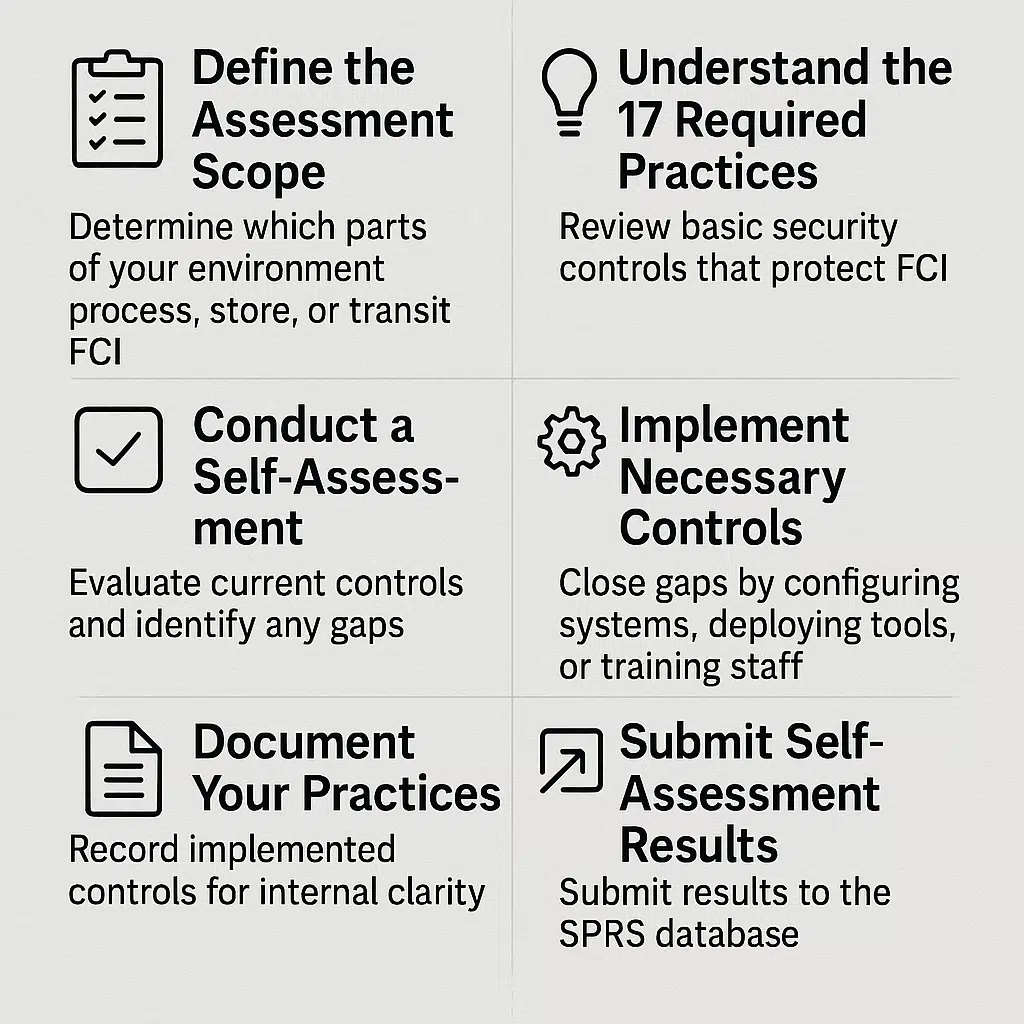
1. Define the Assessment Scope
Before doing anything else, clearly determine which parts of your environment process, store, or transmit Federal Contract Information (FCI). This step defines the “assessment boundary” and prevents unnecessary work outside the relevant systems.
- Why it matters: Scoping avoids wasted effort on non-relevant systems and helps focus security improvements where they’re needed.
- What to include: Email systems, file servers, laptops, remote access tools, subcontractor interfaces, and third-party cloud services—all should be evaluated if they touch FCI.
- Pro tip: If you’re using managed service providers (MSPs), include them in this scoping process. Their systems may also fall within the boundary if they interact with FCI.
2. Understand the 17 Required Practices
CMMC Level 1 requires adherence to 17 specific practices that align with FAR Clause 52.204-21. These are basic but critical security controls.
- Why it matters: These practices form the minimum standard for protecting FCI and demonstrate your eligibility to handle DoD contracts.
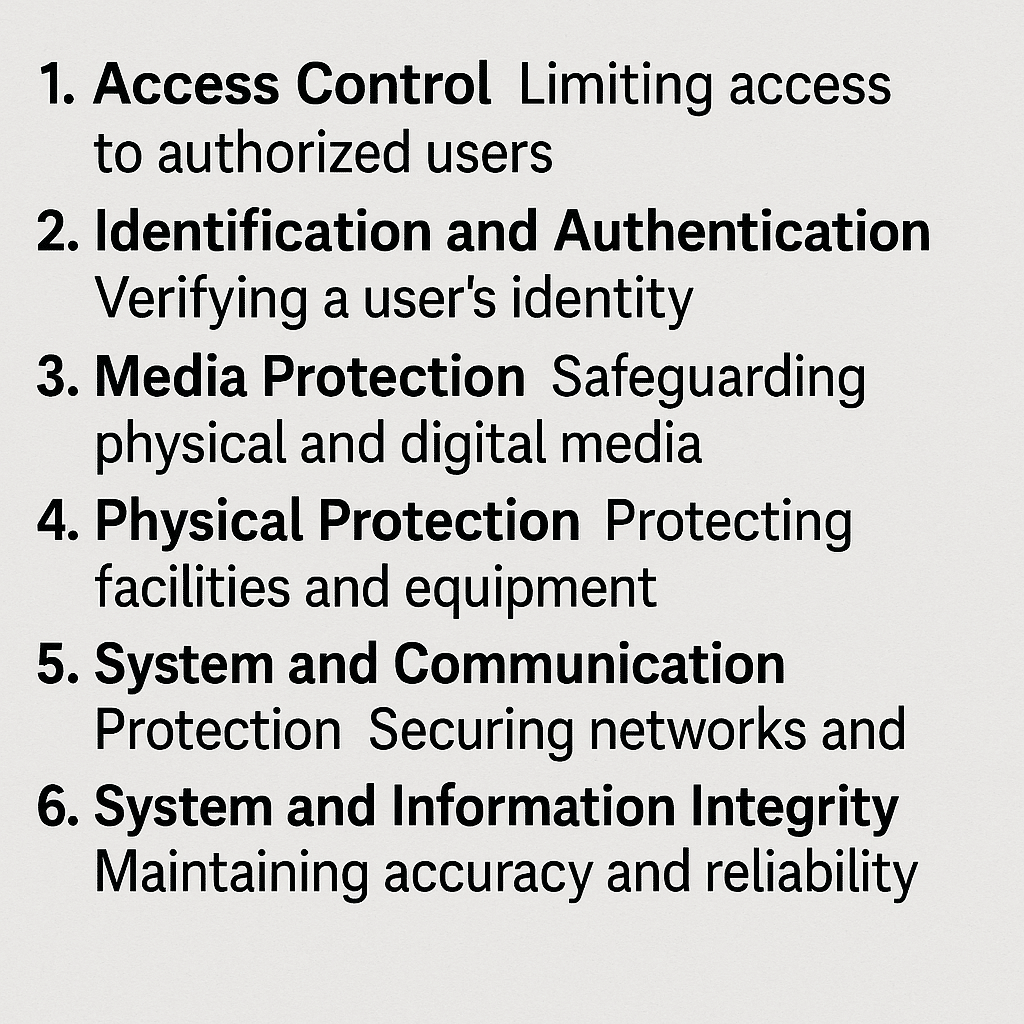
- What they cover: The practices span 6 domains, including:
- Access Control: Limit access to authorized users only.
- Identification and Authentication: Require unique IDs and enforce strong passwords.
- Media Protection: Protect removable media from unauthorized use.
- Physical Protection: Restrict physical access to systems storing FCI.
- System and Communication Protection: Monitor and protect communication channels.
- System and Information Integrity: Identify and fix vulnerabilities in software or hardware.
- Pro tip: Review each practice in plain language. Use the CMMC Level 1 Assessment Guide as your checklist.
3. Conduct a Self-Assessment
After understanding the requirements, evaluate your current controls. This is where most businesses uncover gaps between what’s required and what’s actually in place.
- Why it matters: Self-assessments give you a clear picture of your readiness before you face external verification or submit results to SPRS.
- How to do it: Use the CMMC Self-Assessment Guide and record each practice’s status as: “met,” “not met,” or “partial.” Document supporting evidence.
- Pro tip: Don’t rely on assumptions. Ask system admins, review logs, and check actual configurations.
4. Implement Necessary Controls
Close the gaps identified during your self-assessment. This step involves real action—changing configurations, deploying new tools, or training staff.
- Why it matters: Until controls are in place, your organization is technically non-compliant and may be disqualified from new contracts.
- Common tasks:
- Apply role-based access control (RBAC).
- Disable unused ports and services.
- Install endpoint protection on all devices.
- Configure auditing and alerting for suspicious activity.
- Pro tip: Keep it simple. Level 1 does not require enterprise-grade solutions—small-scale tools and built-in OS features often meet the requirement.
5. Document Your Practices
Although formal policies aren’t required at Level 1, documenting what you’ve implemented helps internal clarity and supports your self-assessment.
- Why it matters: Inconsistencies between IT practice and management assumptions can lead to missed controls. Documentation helps bridge that gap.
- What to write down:
- Password policies and enforcement settings.
- Who has admin access and why.
- Backup schedules and verification steps.
- Incident response contact list (even a basic one).
- Pro tip: Keep this information in a centralized, access-controlled location—such as a shared internal wiki or document management system.
6. Submit Self-Assessment Results
CMMC Level 1 does not require a third-party assessment. Instead, contractors submit results to the Supplier Performance Risk System (SPRS).
- Why it matters: SPRS scores are reviewed during DoD contract decisions. An outdated or missing submission may cause eligibility issues.
- How to submit:
- Create a System Security Plan (SSP) summarizing your control implementations.
- Assign a score based on the DoD scoring methodology.
- Submit the score via the Procurement Integrated Enterprise Environment (PIEE).
- Pro tip: Keep submission dates tracked annually. You’ll need to update your score if your controls change or during the annual cycle.
Remediation and POA&Ms
Remediation refers to the process of fixing gaps identified during your self-assessment. These gaps represent security practices that do not meet the CMMC Level 1 requirements.
Key Points:
- Immediate Action: Level 1 allows self-attestation, but only if all 17 practices are implemented. If you find any gaps, you must remediate them before you can claim compliance.
- Examples of remediation:
- Enabling multi-factor authentication where it was missing.
- Restricting local administrator rights.
- Updating and enforcing password policies.
- Configuring access control lists (ACLs) properly.
- Verification: Always confirm remediation through evidence—logs, screenshots, or configuration exports. These will support your claim in case of an audit or DoD inquiry.
POA&Ms at CMMC Level 1
A Plan of Action and Milestones (POA&M) is a formal document that outlines how and when an organization plans to fix known security gaps. While POA&Ms are commonly used in other compliance frameworks, their use under CMMC Level 1 is limited.
CMMC 2.0 Policy on POA&Ms
- Not accepted for Level 1: You cannot use POA&Ms to defer implementation of any Level 1 practices. All 17 controls must be fully in place at the time of your self-assessment.
- Why this matters: Even if you have a solid remediation plan, you’re not considered compliant until the practice is implemented and verifiable.
- Contrast with Level 2: POA&Ms are permitted under certain conditions for Level 2, but only for non-prioritized requirements and with strict remediation deadlines.
When to use POA&Ms internally
Even if not allowed for official compliance, POA&Ms are still useful tools internally during preparation:
- Purpose: They help organize remediation efforts, track who’s responsible for fixes, and document expected timelines.
- Structure:
- Description of the deficiency
- Planned remediation steps
- Assigned owner
- Estimated completion date
- Current status
Using POA&Ms as internal project management tools supports accountability and progress tracking without being mistaken for evidence of compliance.ation of your efforts. This preparation not only helps in achieving certification but also strengthens your cybersecurity foundation, a crucial aspect for any business working with the federal government.
Annual Assessment of Requirements
At CMMC Level 1, all contractors and subcontractors handling Federal Contract Information (FCI) must perform an annual self-assessment. This requirement comes from FAR clause 52.204.21, which outlines the basic safeguarding rules for protecting FCI.
The self-assessment is a contractor’s responsibility. It is not conducted by a third party. Once completed, the results must be submitted to the Supplier Performance Risk System (SPRS).
Details about the self-assessment process and reporting requirements are provided in CMMC rule § 170.15, with the key submission details listed under § 170.15(a)(1)(i). This section explains what information needs to be collected and how it should be reported to meet compliance obligations.

Common Misconceptions about CMMC Level 1
Understanding what CMMC Level 1 requires and what it doesn’t helps avoid delays, wasted effort, and false assumptions. Below are some of the most common misconceptions and the facts that clear them up:
A. Myths
Here are some of the common myths around CMMC Level 1:
Myth: “Level 1 is too basic to matter.”
Fact: Level 1 covers essential security practices that protect Federal Contract Information (FCI). These safeguards block common threats and form the baseline for all future cybersecurity efforts.
Myth: “Once certified, I don’t need to think about cybersecurity again.”
Fact: Certification is not a one-time event. Threats change. Systems evolve. Ongoing attention is necessary to stay compliant and secure.
Myth: “Level 1 is only for large contractors.”
Fact: Level 1 is built for organizations of all sizes, including small businesses. If you handle FCI, you fall under this requirement regardless of company size.
B. Misunderstandings
The following are the common misunderstandings surrounding CMMC Level 1:
Misunderstanding: “Level 1 certification is a long and complicated process.”
Clarification: It’s far simpler than higher levels. CMMC Level 1 involves a self-assessment against 17 basic practices. No third party audit is required.
Misunderstanding: “Compliance is optional.”
Clarification: If you handle FCI, compliance is not optional. It is required by the Department of Defense for all contractors and subcontractors.
Misunderstanding: “I need an external auditor to certify Level 1.”
Clarification: External audits are not required for Level 1. You can complete a self-assessment and submit your results in the Supplier Performance Risk System (SPRS).
Misunderstanding: “Getting compliant will cost too much.”
Clarification: Most Level 1 practices are basic and can often be met with your current tools and systems. For many businesses, costs are modest and manageable.
Misunderstanding: “Level 1 covers everything I need for cybersecurity.”
Clarification: Level 1 is a starting point. It addresses only foundational protections. Additional safeguards may be necessary depending on your systems, data, and risk exposure.he protection of sensitive information and the integrity of the defense supply chain.
Get CMMC Level 1 Ready with Bright Defense
Bright Defense helps defense contractors meet CMMC Level 1 requirements with precision and efficiency. Our team specializes in CMMC readiness and will guide you through the entire process, from scoping and self-assessment to control implementation and evidence collection.
We help you:
- Complete a detailed self-assessment based on the 17 required practices
- Identify and fix gaps in your cybersecurity controls
- Apply practical solutions tailored to your existing environment
- Maintain clear records and gather supporting evidence
- Receive a certificate of completion once all Level 1 requirements are met
Once validation is complete, you’ll have confidence that your business meets DoD cybersecurity standards and is positioned to compete for federal contracts.
Start with confidence. Stay compliant.
Contact Bright Defense today to learn how we can support your CMMC Level 1 compliance efforts.
Get In Touch