Tim Mektrakarn - CISSP | CISA | ISO 27001
June 28, 2025
The Benefits of a Cybersecurity Gap Assessment
Cybersecurity is an essential consideration for Small and Medium-sized Businesses (SMBs). As SMBs increasingly rely on technology for operations, customer engagement, and financial transactions, the urgency to secure digital assets becomes a top priority. Cybersecurity is a formidable defense, protecting these businesses from the advanced threats of hackers and cyber adversaries.
For an SMB, where resources might be limited but the value of data is immense, robust cybersecurity measures are not just a technical necessity but a core business imperative. Adopting a solid cybersecurity framework safeguards an SMB’s critical data and instills confidence among its clients and partners. SMBs can thus navigate the digital landscape with the assurance that comprehensive cybersecurity protocols shield their operations.

What is a Cybersecurity Gap Assessment?
A cybersecurity gap assessment is a specialized evaluation that focuses on identifying discrepancies between an organization’s current cybersecurity practices and the desired or industry-standard security measures. In the digital age, where threats are ever-evolving and the consequences of breaches can be severe, understanding and addressing these gaps is crucial. This assessment dives deep into an organization’s security infrastructure, policies, procedures, and practices, comparing them against best practices or regulatory standards. The identified “gaps” represent vulnerabilities or areas of improvement in the cybersecurity framework. For businesses, especially SMBs with limited resources, understanding these gaps is the first step in fortifying their digital defenses, ensuring not only the protection of sensitive data but also maintaining trust with stakeholders and clients. In essence, a cybersecurity gap assessment provides a roadmap for enhancing security measures in the face of growing cyber threats.
In the realm of cybersecurity, both gap assessment and risk assessment play pivotal roles in shaping an organization’s security posture. However, they address different facets of cybersecurity and serve distinct purposes:
Cybersecurity Gap Assessment: This evaluation process identifies discrepancies between an organization’s current cybersecurity measures and the desired or industry-standard practices. The primary focus is on understanding the “gaps” or shortcomings in the existing security infrastructure, policies, and procedures. By comparing the current state of cybersecurity practices against best practices, regulatory standards, or specific benchmarks, organizations can pinpoint areas that need enhancement or overhaul. The outcome is a clearer understanding of where the organization stands and what improvements are needed to reach a more secure state.
Cybersecurity Risk Assessment: This process is dedicated to identifying, analyzing, and evaluating potential cyber threats and vulnerabilities that an organization might face. It delves into the various risks associated with data breaches, malware attacks, phishing attempts, and other cyber threats. By assessing these risks, organizations can prioritize them based on their potential impact and the likelihood of occurrence. The primary goal is to develop strategies and controls to mitigate, manage, or eliminate these identified risks, ensuring that the organization is prepared for potential cyber threats.
While a cybersecurity gap assessment is about understanding and addressing the discrepancies in current security practices, a cybersecurity risk assessment is about recognizing and preparing for potential threats. Both assessments are integral to building a robust cybersecurity framework and ensuring an organization’s digital assets are well-protected.
Why is a Gap Assessment Crucial?
In today’s interconnected digital world, the importance of a gap assessment in cybersecurity cannot be overstated. Here’s why:
- The Increasing Threats in the Cyber Landscape: Every day, new vulnerabilities, malware, and sophisticated attack methods emerge, targeting businesses of all sizes. These threats are not static; they evolve, becoming more advanced and harder to detect. A cyber security gap assessment helps organizations stay ahead of these threats by identifying areas of weakness in their cybersecurity infrastructure. By understanding where the vulnerabilities lie, organizations can proactively address them, ensuring they are not easy targets for cyber adversaries.
- The Cost of Data Breaches and Cyberattacks: Beyond the immediate financial implications, data breaches can have long-lasting effects on a company’s reputation, customer trust, and market position. The average cost of a data breach has been steadily rising, with businesses facing not only direct financial losses but also potential loss of clientele, reduced market share, and a tarnished brand image. A cyber security gap assessment acts as a preventive measure, highlighting areas that, if left unaddressed, could result in costly breaches.
- Legal and Regulatory Implications of Inadequate Cybersecurity: Regulatory bodies worldwide are recognizing the importance of cybersecurity, leading to stringent laws and regulations. Non-compliance can result in hefty fines, legal actions, and further damage to a company’s reputation. A gap assessment ensures that organizations are not just meeting the minimum required standards but are striving for best practices in cybersecurity. By identifying and addressing gaps, businesses can ensure they remain compliant, avoiding legal repercussions and demonstrating their commitment to safeguarding user data.
A gap assessment is not just a tool for improvement but a necessity in the modern cyber landscape. It provides a clear roadmap for organizations to fortify their defenses, mitigate potential risks, and navigate the complex world of cybersecurity with confidence.
Key Components of a Cybersecurity Gap Assessment
A comprehensive cybersecurity gap assessment is a multi-faceted process that delves deep into an organization’s security posture. Here are the key components that form the backbone of this assessment:
- Asset Identification: At the heart of any cybersecurity strategy is a clear understanding of what needs protection. This involves cataloging all digital assets, from hardware devices like servers and workstations to software applications and data repositories. By identifying these assets, organizations can prioritize their protection efforts, ensuring that the most critical and sensitive data and systems receive the highest level of security.
- Threat Analysis: Once assets are identified, the next step is to understand the potential threats they might face. This involves analyzing the cyber landscape to identify the types of attacks, threat actors, and methods that could target the organization’s assets. Whether it’s ransomware, phishing campaigns, or advanced persistent threats, understanding these dangers is crucial to developing effective defense strategies.
- Vulnerability Assessment: With a clear picture of potential threats, organizations can then focus on identifying weaknesses within their systems. This involves scanning and testing the infrastructure to pinpoint vulnerabilities that could be exploited by cyber adversaries. These vulnerabilities could range from outdated software patches to misconfigured servers or weak password policies.
- Control Analysis: This component evaluates the current security measures in place. Are the existing controls effective in mitigating the identified vulnerabilities? Are there redundant or outdated security measures that need revisiting? By assessing the effectiveness of current controls, organizations can determine where enhancements or changes are required to bolster their security posture.
- Risk Evaluation: The culmination of the gap assessment process is the risk evaluation. By combining the insights from asset identification, threat analysis, vulnerability assessment, and control analysis, organizations can determine the potential impact of the identified risks. This evaluation helps in prioritizing remediation efforts, ensuring that the most significant risks are addressed first and resources are allocated effectively.

The Gap Assessment Process
Navigating the complexities of cybersecurity requires a structured and systematic approach. The gap assessment process serves as a blueprint for organizations to evaluate their current security measures and identify areas of improvement. Here’s a breakdown of the process:
- Preparation: Before diving into the assessment, it’s essential to set clear objectives. What does the organization aim to achieve with this assessment? Are there specific regulations or standards they need to adhere to? Once the goals are defined, gather the necessary resources. This might include assembling a team of cybersecurity experts, procuring assessment tools, or engaging third-party consultants. Proper preparation ensures that the assessment is thorough and aligned with the organization’s needs.
- Data Collection: With the groundwork laid, the next step is to collect data on the organization’s current security posture. This involves cataloging assets, understanding existing security protocols, and gathering information on previous security incidents or breaches. Data collection provides a snapshot of the organization’s current state, serving as a baseline for the subsequent stages of the assessment.
- Analysis: Armed with the collected data, the team then compares the organization’s current security posture against industry best practices, regulatory standards, or specific benchmarks. This comparative analysis helps in identifying gaps or discrepancies in the existing security measures. It’s a critical phase where vulnerabilities, weaknesses, and areas of non-compliance come to light.
- Report Generation: After the analysis, a comprehensive report is generated. This document captures the findings of the assessment, detailing the identified gaps, vulnerabilities, and areas of improvement. The report also provides insights into the potential risks associated with these gaps, offering a clear picture of the organization’s security landscape.
- Action Plan Development: The final and perhaps most crucial step is developing an action plan. Based on the findings from the report, this plan outlines the strategies and steps required to address the identified gaps. It provides a roadmap for enhancing the organization’s security measures, prioritizing actions based on risk levels, and allocating resources effectively. The action plan serves as a guide for the organization to navigate its journey towards a more secure and compliant state.
The gap assessment process is a holistic approach to understanding, evaluating, and enhancing an organization’s cybersecurity measures. By following this structured process, businesses can ensure they are well-prepared to face the challenges of the modern cyber landscape.
Benefits of Conducting a Gap Assessment
In the realm of cybersecurity and business operations, conducting a gap assessment offers a multitude of advantages. Here’s a closer look at the key benefits:
- Enhanced Security Posture: One of the primary benefits of a gap assessment is the strengthening of an organization’s security measures. By identifying vulnerabilities and weaknesses in the existing infrastructure, businesses can take targeted actions to fortify their defenses. This not only reduces the likelihood of breaches but also ensures that the organization is better equipped to handle evolving cyber threats.
- Compliance with Industry Regulations and Standards: As the digital landscape grows, so does the regulatory environment. Many industries now have stringent cybersecurity standards and regulations in place. A gap assessment helps organizations identify areas of non-compliance, ensuring they meet or exceed industry benchmarks. This not only prevents potential legal repercussions and fines but also positions the organization as a responsible and compliant entity in its sector.
- Improved Stakeholder Trust and Confidence: In today’s data-driven world, stakeholders, be it customers, partners, or investors, place immense value on data security. By conducting a gap assessment and proactively addressing security concerns, organizations can demonstrate their commitment to safeguarding sensitive information. This boosts trust and confidence among stakeholders, leading to stronger business relationships and enhanced brand reputation.
- Proactive Approach to Threat Management: Rather than reacting to security incidents after they occur, a gap assessment promotes a proactive stance. Organizations can anticipate potential threats, understand their risk landscape, and implement preventive measures. This forward-thinking approach not only mitigates risks but also ensures that the organization is always a step ahead in its cybersecurity strategy.
A gap assessment is more than just an evaluative tool—it’s a strategic instrument that drives tangible benefits for organizations. By understanding and addressing their cybersecurity shortcomings, businesses can navigate the digital world with greater assurance, resilience, and credibility.

Common Challenges and How to Overcome Them
Embarking on a gap assessment, especially in the realm of cybersecurity, can present a set of challenges. Recognizing these obstacles and devising strategies to address them is crucial for the success of the assessment. Here’s a look at some common challenges and ways to overcome them:
- Resistance from Stakeholders: Often, stakeholders might resist changes or interventions, especially if they perceive them as disruptive to existing workflows or costly endeavors.
- Solution: Communication is key. Engage stakeholders early in the process, educating them about the importance of the gap assessment and its long-term benefits. Highlight potential risks of inaction and demonstrate how the assessment aligns with the organization’s broader goals. When stakeholders understand the value and necessity of the assessment, resistance is likely to diminish.
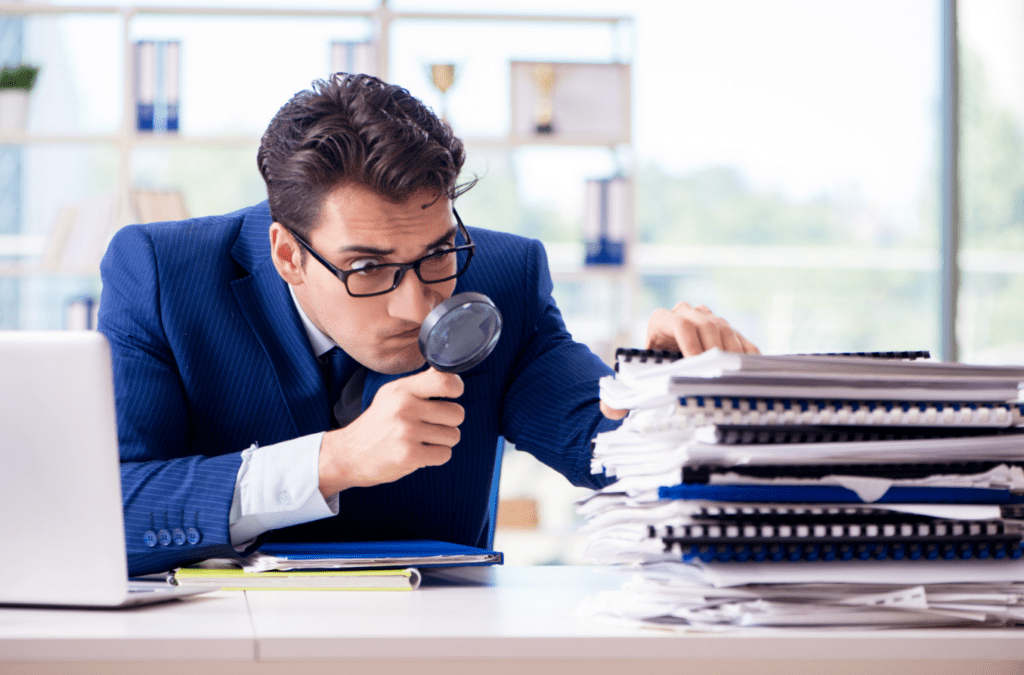
- Lack of Technical Expertise: Conducting a thorough gap assessment requires specialized knowledge, and not all organizations have the requisite technical expertise in-house.
- Solution: Engaging third-party experts can be invaluable. These experts bring a wealth of experience and can provide an unbiased perspective on the organization’s security posture. Additionally, they can introduce best practices and methodologies that might not be familiar to the internal team.
- Resource Constraints: Many organizations, especially SMBs, might face constraints in terms of budget, time, or manpower, making it challenging to conduct a comprehensive assessment.
- Solution: Prioritizing is essential. Start by focusing on the most critical gaps or vulnerabilities that pose the highest risk. Over time, as resources become available, the scope of the assessment can be expanded. Additionally, consider leveraging automated tools or platforms that can expedite the assessment process without significant manual intervention.
- Solutions for Continuous Improvement: The cybersecurity landscape is dynamic, and organizations need to adapt continuously.
- Solution: Invest in continuous training for the internal team, ensuring they stay updated with the latest threats, technologies, and best practices. Regularly revisit and update the gap assessment to reflect changes in the organization’s infrastructure, goals, or the broader cyber environment.
While challenges in conducting a gap assessment are inevitable, they are not insurmountable. With a proactive approach, clear communication, and the right resources, organizations can navigate these challenges and ensure a successful and impactful assessment.
Conclusion
As we’ve delved into the intricacies of gap assessments, it’s evident that these evaluations are not mere optional exercises but essential tools for organizations, especially SMBs, to navigate the complex world of cyber threats. Regular gap assessments offer a clear lens to view discrepancies in current security practices, providing actionable insights to fortify defenses. Beyond just identifying vulnerabilities, these assessments serve as a roadmap, guiding organizations towards a more secure and compliant state. In this age, where the cost of inaction can be monumental—ranging from financial losses to tarnished reputations—it’s imperative for organizations to adopt a proactive stance. By prioritizing cybersecurity, regularly conducting gap assessments, and taking informed actions based on their findings, organizations not only safeguard their digital assets but also instill trust among stakeholders, ensuring sustainable growth in an interconnected world.
About Bright Defense
Bright Defense stands as a global shield against cybersecurity threats, championing continuous compliance. Our monthly services, led by CISSP and CISA professionals, craft and execute a cybersecurity strategy aligned with standards like SOC 2, HIPAA, ISO 27001, NIST, and CMMC.
We streamline your compliance process with our integrated automation platform, ensuring real-time monitoring of your adherence status. Additionally, we provide managed training for security awareness and conduct phishing tests.
Embark on your SaaS compliance voyage with Bright Defense today!
FAQ on Cybersecurity Gap Assessments
- What is a cybersecurity gap assessment?
- A cybersecurity gap assessment is a specialized evaluation that identifies discrepancies between an organization’s current cybersecurity practices and desired or industry-standard security measures. It provides a roadmap for enhancing security measures against growing cyber threats.
- How do gap assessments differ from risk assessments in cybersecurity?
- While a cybersecurity gap assessment focuses on identifying discrepancies in current security practices, a cybersecurity risk assessment is about recognizing and preparing for potential threats. Both are essential for a robust cybersecurity framework.
- Why is conducting a gap assessment crucial?
- A gap assessment is vital due to the increasing threats in the cyber landscape, the rising costs of data breaches and cyberattacks, and the legal and regulatory implications of inadequate cybersecurity.
- What are the key components of a cybersecurity gap assessment?
- The main components include asset identification, threat analysis, vulnerability assessment, control analysis, and risk evaluation.
- What is the process of a gap assessment?
- The process involves preparation, data collection, analysis, report generation, and action plan development.
- What benefits can organizations expect from a gap assessment?
- Benefits include an enhanced security posture, compliance with industry regulations and standards, improved stakeholder trust, and a proactive approach to threat management.
- What challenges might organizations face during a gap assessment?
- Common challenges include resistance from stakeholders, lack of technical expertise, resource constraints, and the need for continuous improvement in the dynamic cybersecurity landscape.
- How can organizations overcome resistance from stakeholders during a gap assessment?
- Engaging stakeholders early, educating them about the importance of the assessment, and highlighting potential risks of inaction can help diminish resistance.
- How can SMBs with limited resources conduct a comprehensive gap assessment?
- Prioritizing critical gaps or vulnerabilities and leveraging automated tools or platforms can help SMBs conduct effective assessments even with resource constraints.
- How can organizations ensure continuous improvement in their cybersecurity measures?
-
- Investing in continuous training for the internal team and regularly updating the gap assessment to reflect changes in the organization’s environment can ensure ongoing improvement.
Get In Touch