Updated:
April 14, 2026
SOC 2 vs. NIST: Choosing the Right Compliance Framework
Choosing the right compliance framework for your business can be complicated. SOC 2 vs. NIST is a common framework comparison. Both frameworks aim to protect your data, but they take different routes. SOC 2 is focused on trust and security in handling customer data, especially for service organizations. On the other hand, NIST provides a broad set of guidelines to help organizations of all sizes improve their cybersecurity.
In this article, we’ll break down SOC 2 and NIST in simple terms and compare their approaches to data security and compliance. By the end of this guide, you’ll have a clearer picture of which framework suits your business needs, helping you make a well-informed decision on the path to robust data security.
Key Takeaways
- SOC 2 is designed for service providers to prove they protect customer data through controls around security, availability, integrity, confidentiality, and privacy.
- NIST offers flexible but detailed cybersecurity guidelines used across sectors, especially for those handling sensitive government-related data.
- SOC 2 requires independent audits that result in formal reports, while NIST frameworks rely on internal assessments or outside evaluations tied to federal programs like CMMC.
- Organizations can choose one framework or apply both, depending on client expectations, industry requirements, and the need for regulatory compliance.
- Maintaining continuous compliance through regular monitoring, documentation, and staff involvement is essential for both SOC 2 and NIST.
What is SOC 2?
SOC 2, short for Service Organization Control 2. It is a framework designed for service providers storing customer data. It was developed by the American Institute of CPAs (AICPA). SOC 2 is not just a one-time checklist but a set of criteria for managing customer data. It is based on five trust service principles: Security, Availability, Processing Integrity, Confidentiality, and Privacy.
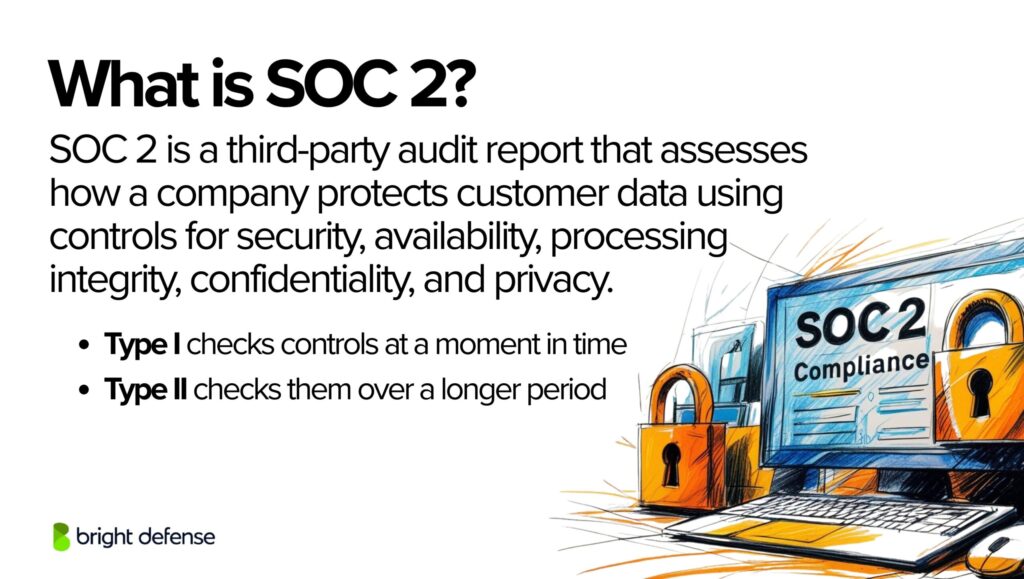
- Security ensures that systems are protected against unauthorized access.
- Availability refers to the system’s accessibility for operation and use, as agreed.
- Processing Integrity means system processing is complete, valid, accurate, timely, and authorized.
- Confidentiality involves protecting any confidential information as promised or agreed.
- Privacy addresses the system’s collection, use, retention, disclosure, and disposal of personal information in conformity with the organization’s privacy notice.
Two types of SOC 2 reports are Type I and Type II. Type I describes the vendor’s systems and whether their design meets relevant trust principles. Type II details the operational effectiveness of these systems. SOC 2 is highly flexible and can be tailored to each organization’s unique needs. It is not prescriptive but requires companies to establish and follow strict information security policies and procedures.
What is NIST?
NIST refers to following a structured set of security and privacy guidelines developed by the National Institute of Standards and Technology. These guidelines are not a fixed checklist but a flexible framework used to protect information systems and sensitive data. One of the most widely used frameworks is the NIST Cybersecurity Framework (CSF), which includes five core functions:
- Identify
- Protect
- Detect
- Respond
- Recover
The National Institute of Standards and Technology (NIST) is an influential body under the U.S. Department of Commerce, focusing on developing standards and technology to improve security, efficiency, and competitiveness in various sectors. NIST is recognized for its comprehensive frameworks, which guide organizations in managing and reducing cybersecurity risks. While NIST has developed numerous frameworks and standards, three stand out for their widespread applicability and robustness: the NIST Cybersecurity Framework (CSF), NIST 800-53, and NIST 800-171.
- NIST Cybersecurity Framework (CSF) is a flexible guide designed to help organizations of all sizes and sectors manage and mitigate cybersecurity risks. It is built around five core functions: Identify, Protect, Detect, Respond, and Recover. These functions provide a high-level, strategic perspective on the lifecycle of managing and reducing cybersecurity risks.
- NIST 800-53 offers a catalog of security and privacy controls for all U.S. federal information systems, except those related to national security. It is known for being comprehensive, prescriptive, and widely used by government agencies and contractors to align with federal requirements.
- NIST 800-171 is specifically tailored for non-federal organizations that handle Controlled Unclassified Information (CUI). It aims to protect sensitive federal information in non-federal systems and organizations. NIST 800-171 is critical for contractors and entities working directly with the federal government. It ensures they maintain a robust security posture to safeguard sensitive data.
NIST frameworks are celebrated for their thoroughness and adaptability, offering a structured yet flexible approach to cybersecurity. Unlike prescriptive regulations, NIST provides guidelines and best practices. This allows organizations to tailor their implementation strategies to their needs, size, and industry sector.
Organizations can better navigate their compliance journey by exploring the benefits and intent of SOC 2 and NIST. This aligns their operations and security measures with the framework best fitting their business model and objectives. The next sections will delve into the distinctions between SOC 2 and NIST and provide insights into choosing the most suitable framework for your organization.
Key Differences Between SOC 2 and NIST
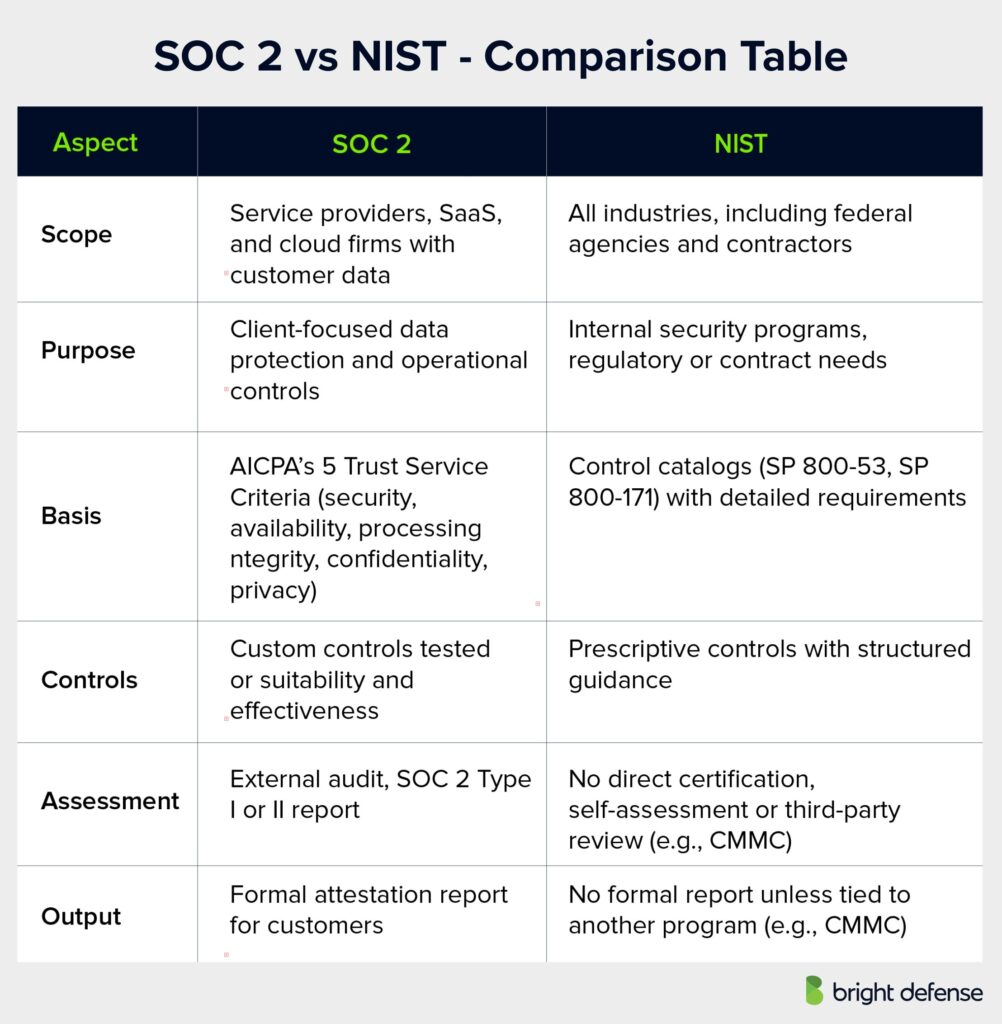
Understanding the distinctions between SOC 2 and NIST frameworks is crucial for organizations choosing the right path for their compliance strategy.
| Category | SOC 2 | NIST |
|---|---|---|
| Scope | Focused on service providers, especially SaaS and cloud-based firms handling customer data. | Applies across industries, including federal agencies, contractors, and private organizations. |
| Purpose | Addresses client expectations for data protection and operational controls. | Supports internal security programs and fulfills regulatory or contractual obligations. |
| Framework Basis | AICPA’s 5 Trust Service Criteria: security, availability, processing integrity, confidentiality, privacy. | Detailed control catalogs (e.g., SP 800-53, SP 800-171) with specific requirements. |
| Control Approach | Organizations define controls; auditors test for suitability and effectiveness. | Prescriptive controls with structured implementation guidance. |
| Assessment Method | External audit by licensed firms; results in SOC 2 Type I or Type II report. | No direct certification; self-assessment or third-party review under programs like CMMC. |
| Output | Formal attestation report used to demonstrate security posture to customers. | No formal report unless tied to another compliance program (e.g., CMMC for defense contractors). |
1. Differences in Scope and Applicability
SOC 2 applies to service organizations that handle customer data, especially cloud-based providers and SaaS companies. NIST frameworks apply broadly across sectors, including federal agencies, contractors, and private companies. SOC 2 is driven by client assurance. NIST serves both internal security goals and regulatory requirements.
2. Control Frameworks and Requirements
SOC 2 is based on 5 AICPA’s Trust Service Criteria: security, availability, processing integrity, confidentiality, and privacy. Organizations define their own controls, and auditors assess whether those controls meet the criteria.
NIST frameworks, such as SP 800-53 and SP 800-171, provide detailed, predefined controls. They are more prescriptive and often required for government-related work, especially when handling Controlled Unclassified Information (CUI).
3. Assessment and Certification Process
SOC 2 audits are performed by independent firms, resulting in a formal Type I or Type II report. These are widely used to demonstrate third-party security posture.
NIST does not offer certification. Organizations self-assess or follow program-specific audits (e.g., CMMC) that reference NIST standards. Compliance with NIST is often regulatory or contractual rather than market-driven.

Why Choose SOC 2?
Choosing SOC 2 is particularly beneficial for service-oriented businesses that must demonstrate high security and privacy controls to their clients.
- Client Assurance: SOC 2 is widely recognized in the industry, especially in the United States and Canada. A SOC 2 certification can significantly boost your organization’s credibility, showing your commitment to protecting client data.
- Market Demand: Many businesses require their service providers to be SOC 2 compliant, especially when handling sensitive or critical information.
- Customizable Framework: SOC 2 allows organizations to tailor their controls to specific business practices, providing flexibility in implementing security measures.
Why Choose NIST?
NIST frameworks are ideal for organizations looking for a comprehensive and structured approach to managing cybersecurity risks. NIST is especially relevant to companies working with the federal government or handling sensitive information.
- Broad Applicability and Recognition: NIST standards are globally recognized and provide a trusted benchmark for cybersecurity. This makes them beneficial for a wide range of industries.
- Compliance with Federal Requirements: For organizations working with the U.S. government or handling CUI, compliance with NIST 800-171 is mandatory. Adherence to NIST standards can open doors to federal contracts and partnerships.
- Integration with CMMC: The Cybersecurity Maturity Model Certification (CMMC) is a unifying standard for implementing cybersecurity across the defense industrial base. NIST 800-171 is the foundation for CMMC Level 3. Adhering to NIST standards can help organizations prepare for CMMC assessments, which are crucial for contractors in the defense sector.
Pursuing Both SOC 2 and NIST
In some cases, organizations may find it advantageous or necessary to align with both SOC 2 and NIST frameworks. This dual approach can maximize data protection and compliance, especially for companies that operate in diverse sectors or offer a wide range of services.
- Enhanced Trust and Security: By adhering to both frameworks, organizations can demonstrate a high level of commitment to data security and privacy. This may appeal to a broader client base.
- Comprehensive Compliance Strategy: Some industries may require compliance with both standards due to their specific regulatory landscape or business model. For instance, a cloud service provider working with government agencies might need SOC 2 for general business purposes and NIST compliance for federal contracts.
- Leveraging Synergies: While SOC 2 and NIST have distinct focuses, there are overlaps in their controls and processes. Organizations can streamline their compliance efforts by identifying and leveraging these synergies, reducing redundancy, and optimizing resource allocation.
However, pursuing dual compliance requires careful planning and resource management. Organizations should conduct a thorough gap analysis, assess the cost-benefit ratio, and develop a strategic plan that addresses the unique demands of each framework while capitalizing on their commonalities.

The Role of Continuous Compliance in SOC 2 and NIST Frameworks
Continuous compliance is an ongoing process of ensuring that an organization adheres to the required standards and regulations at all times, not just during annual audits or assessments. In the context of SOC 2 and NIST frameworks, continuous compliance plays a pivotal role.
Continuous Monitoring and Improvement
- SOC 2: Given that SOC 2 is more than a one-time assessment, organizations need to continuously monitor their controls related to the five trust service principles. This involves regular reviews of security measures, updates to policies as per the changing technology landscape, and consistent employee training to ensure that everyone is aligned with the organization’s security protocols.
- NIST: NIST frameworks, particularly the Cybersecurity Framework (CSF), emphasize continuous monitoring and improvement as part of their core functions. Organizations are encouraged to regularly identify and assess cybersecurity risks, protect their assets through ongoing maintenance of security controls, detect anomalies promptly, and constantly refine their response and recovery strategies.
Automation and Integration
- Integrating compliance activities into daily operations can significantly reduce the burden of maintaining continuous compliance. Automation tools can help in regular data monitoring, timely reporting of compliance metrics, and swift detection and mitigation of potential issues.
- For both SOC 2 and NIST frameworks, leveraging technology to streamline compliance processes ensures that the organization remains compliant and can quickly adapt to new threats or changes in regulations.
Culture of Compliance
- Building a culture of compliance is vital. This means fostering an environment where data security and adherence to standards are ingrained in the daily activities of all team members.
- Regular training, clear communication of policies, and a top-down emphasis on the importance of compliance are crucial. When employees understand their role in maintaining SOC 2 and NIST standards, they become active participants in the organization’s security posture.
Documentation and Evidence
- Continuous compliance requires meticulous documentation. For SOC 2, this means keeping detailed records of policies, procedures, and control activities. For NIST, it involves maintaining comprehensive documentation of the implementation of controls and ongoing risk management activities.
- Regularly updated documentation supports compliance and streamlines the audit process. This provides clear evidence of the organization’s commitment to maintaining high security and privacy standards.
Vendor and Third-Party Management
- As organizations often rely on third-party vendors, ensuring that these partners also adhere to SOC 2 and NIST standards is part of continuous compliance. This involves regular assessments of vendor security practices, contractual agreements on compliance standards, and continuous monitoring of third-party risks.
In conclusion, continuous compliance with SOC 2 and NIST is an integral part of an organization’s operations. It demands ongoing vigilance, a culture that prioritizes security and privacy, and the effective use of technology to automate and integrate compliance activities. By embracing continuous compliance, organizations strengthen their reputation, ensuring lasting trust with clients and partners.

Final Thoughts
Choosing SOC 2, NIST, or both depends on an organization’s operational, market, and regulatory needs. SOC 2 offers a flexible trust standard suited for service providers that want to show strong security and privacy practices. NIST delivers structured guidance for a wide range of industries, including those working with federal agencies or handling controlled unclassified information.
Some teams may benefit from using both frameworks to meet varied client and regulatory expectations. Successful compliance requires a clear view of each framework, an honest assessment of internal needs, and a practical implementation plan. A thoughtful choice gives organizations a path that fits industry requirements and supports long term business goals.
Bright Defense Delivers SOC 2 and NIST Compliance Solutions
Bright Defense supports SOC 2 and NIST readiness with a mission focused on reducing cybersecurity risk through continuous compliance. Our team strengthens security posture and lowers breach exposure.
Our monthly service gives you CISSP and CISA guidance, a practical cybersecurity plan, and controls that fit standards such as SOC 2, NIST, CMMC, HIPAA, and ISO 27001. The service includes a compliance automation platform that cuts cost and improves efficiency.
We also offer vulnerability management, security awareness training, phishing tests, and vCISO support. Start your compliance program with Bright Defense today.
Frequently Asked Questions
1. What is cybersecurity risk management and how do SOC 2 and NIST frameworks assist in it?
Cybersecurity risk management means identifying threats, assessing impact, and applying controls to reduce risk. SOC 2 helps by setting requirements for security, availability, processing integrity, confidentiality, and privacy. NIST provides broader guidance (like NIST CSF and 800-53) for identifying, protecting, detecting, responding to, and recovering from threats.
2. How do SOC 2 and NIST address access control to protect sensitive data?
Both require strict access controls. SOC 2 enforces rules so only authorized users can access systems. NIST applies least privilege and separation of duties, requiring limits on who can access what and why.
3. Why is it important for certified public accountants (CPAs) to understand SOC 2?
SOC 2 was developed by the AICPA, and CPAs conduct its audits. They assess whether a company’s controls meet trust principles. Their reports help organizations prove data security and build stakeholder confidence.
4. How can organizations implement controls to manage cybersecurity risk effectively?
They can follow SOC 2 or NIST. First, identify risks. Then apply policies, procedures, and technology to reduce those risks. Include incident response, access management, and regular reviews to keep controls effective.
5. What role does the cybersecurity framework play in helping organizations protect data?
The NIST CSF gives a clear structure: Identify, Protect, Detect, Respond, and Recover. It helps businesses build a consistent, ongoing approach to defend against cyber threats and protect data.
6. How can businesses demonstrate compliance with information security and compliance requirements?
They can use SOC 2 and NIST. Regular audits, strong documentation, and control testing show regulators and clients that data is handled securely and that compliance rules are followed.
7. Why is it important for organizations to stay updated with the current regulatory environment and compliance framework?
Laws and standards change often. Staying current helps avoid penalties, keeps systems secure, and protects the organization’s reputation.
8. How can organizations ensure that their cybersecurity program aligns with the NIST framework?
Start with a gap analysis. Compare current practices to NIST guidance. Then apply missing controls, train staff, and monitor the program regularly to keep everything aligned and effective.
9. What are the main differences between SOC 2 and the NIST Cybersecurity Framework?
SOC 2 focuses on how well a service provider meets trust service criteria—security, availability, processing integrity, confidentiality, and privacy. It results in an attestation report from a CPA. NIST CSF, on the other hand, is a voluntary guideline that helps organizations assess and improve cybersecurity practices. SOC 2 is commonly used for customer assurance, while NIST is often used internally for building or maturing a security program.
10. Can an organization use both SOC 2 and NIST at the same time?
Yes. Many organizations use both. NIST provides detailed guidance for building controls, while SOC 2 provides a way to report on those controls. Mapping NIST controls to SOC 2 criteria helps companies design a strong security posture and then validate it through an audit.
11. How long does it take to complete a SOC 2 audit?
A SOC 2 Type I audit can take a few weeks to a couple of months, depending on the readiness of the organization. A SOC 2 Type II audit usually requires a review period of 3 to 12 months, followed by the audit itself. Time depends on scope, resources, and maturity of existing controls.
12. What types of organizations typically need SOC 2 compliance?
SOC 2 is especially relevant for SaaS providers, cloud service companies, data processors, and any third-party vendor that stores or processes client data. These organizations often need SOC 2 reports to meet client expectations and enter into contracts with regulated businesses.
13. How do NIST and SOC 2 help with third-party risk management?
NIST offers specific guidance for managing risks from vendors and partners (e.g., NIST 800-161 and NIST CSF supply chain considerations). SOC 2 reports give assurance that a vendor’s controls meet industry expectations. Using both helps organizations evaluate, select, and monitor vendors more effectively.
14. What is included in a SOC 2 report?
A SOC 2 report includes a description of the organization’s systems, the trust service criteria selected, the controls in place to meet those criteria, and the auditor’s opinion on whether the controls were suitably designed and operating effectively. Type I covers design at a point in time, while Type II also assesses effectiveness over a set period.
15. How does NIST support incident response planning?
NIST provides detailed guidance on incident response through publications like NIST SP 800-61. It outlines how to prepare for, detect, analyze, contain, eradicate, and recover from security incidents. This helps organizations respond quickly and reduce the impact of breaches or disruptions.
A 2024 survey by the Cloud Security Alliance found that 58% of SaaS providers pursue SOC 2 compliance, primarily due to customer demand, while 42% implement NIST-based controls (e.g., NIST CSF or NIST 800-53). Many companies adopt both, but SOC 2 adoption tends to be higher in customer-facing businesses, whereas NIST dominates in government and critical infrastructure sectors.
SOC 2 Trust Services Criteria map to approximately 61 controls across security, availability, processing integrity, confidentiality, and privacy. In contrast, NIST 800-53 Rev. 5 contains over 1,100 controls, including optional enhancements. This means NIST can be up to 18x more granular, especially for federal compliance and high-security environments.
A SOC 2 Type 2 audit typically takes 3–12 months to complete, depending on readiness and scope. NIST-based compliance (like NIST 800-171 or 800-53) often requires 12–24 months due to broader control implementation and required documentation, particularly for defense contractors under CMMC.
SOC 2 audit costs typically range from $20,000 to $80,000 for mid-sized companies, including readiness assessments and auditor fees. NIST compliance efforts (especially 800-53) often exceed $200,000–$500,000 due to deeper control implementations, continuous monitoring, and federal compliance requirements.
Mapping studies show that SOC 2 and NIST 800-53 share 60–70% control overlap, primarily in access management, incident response, and risk assessment. This allows organizations that already meet NIST to achieve SOC 2 with 30–40% incremental effort, and vice versa.
Get In Touch